Which API must an engineer use to change a netmask on a Cisco IOS XE device?
A file that already exists in a local repository is updated. Which command must be executed to ensure that the changes in the file are included in the next Git commit?
A developer is trying to retrieve data over a REST API. The API server responds with an HTTP client error response code. After investigating the response the developer realizes the realizes the response has a Retry-After header. What is the root cause of this error?
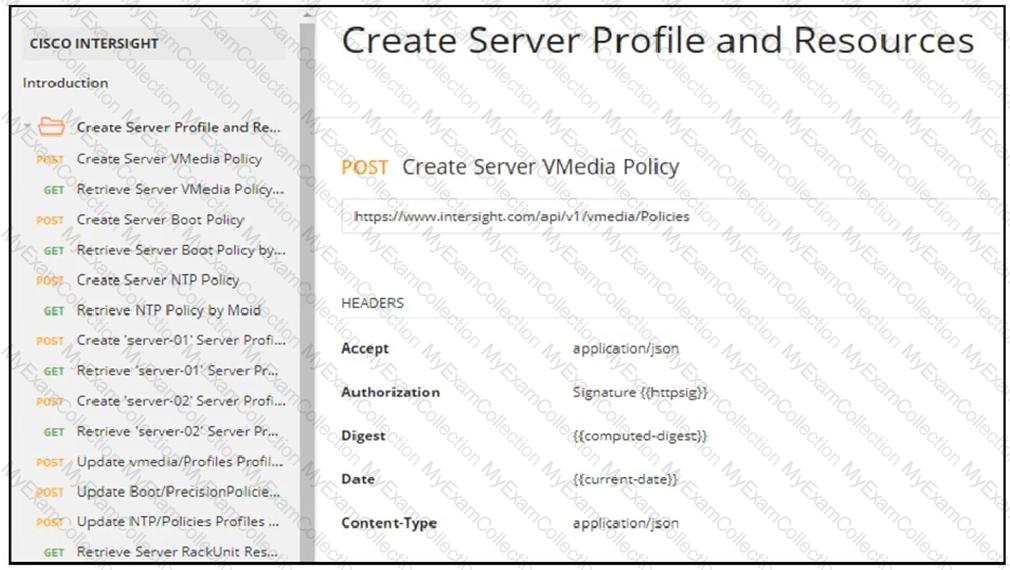
Refer to the exhibit.
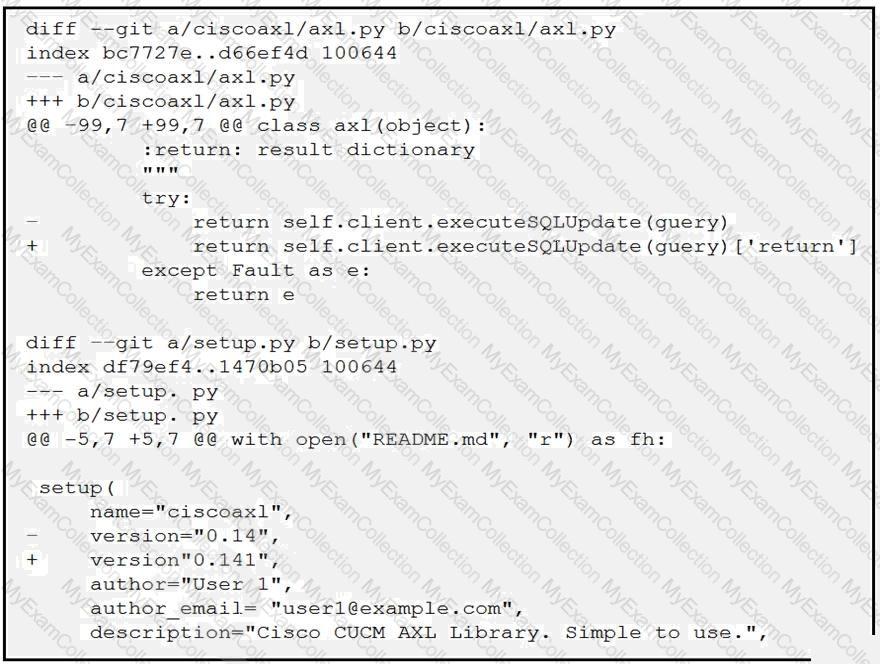
Which two files are being edited in the unified diff? (Choose two.)
What are two functions of a routing table on a network device? (Choose two.)
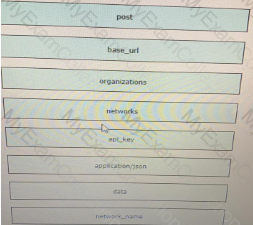
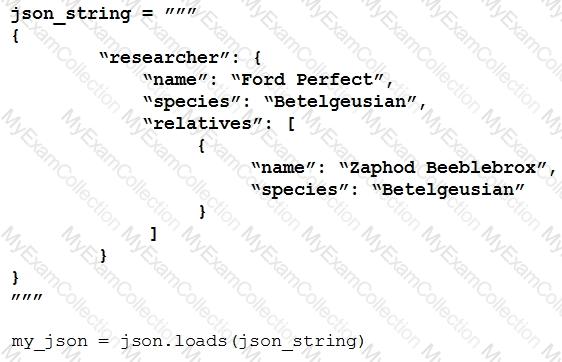
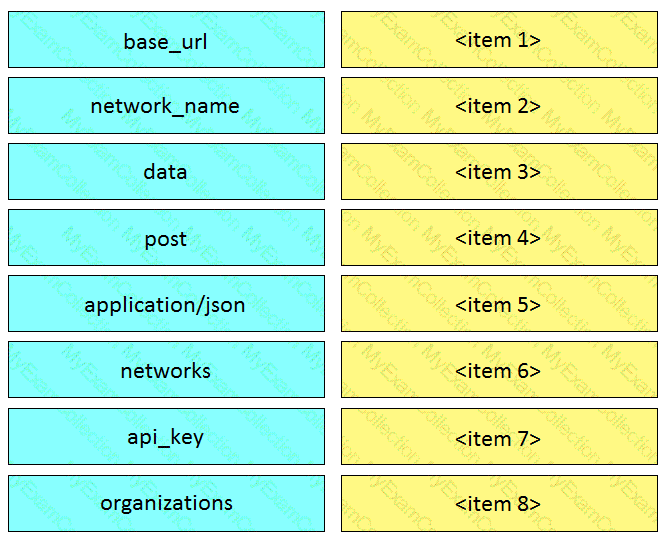
Refer to the exhibit.

A developer must integrate a bot with an internal communication app. The developer wants to replace the webexbot package with the teamsbot package by using Ansible and prepares a playbook In the first two tasks, the playbook stops the webexbot and verifies that the teamsbot is installed. What is accomplished in the last task of the workflow when the developer runs the Ansible playbook?
Refer to the exhibit.
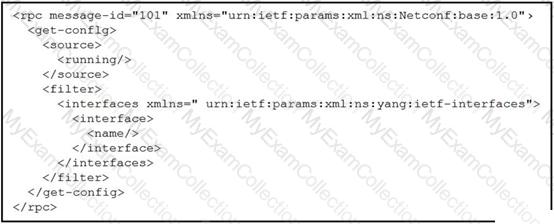
A network engineer uses model-driven programmability to monitor and perform changes on the network. The network engineer decides to use the NETCONF RPC message to complete one of their tasks. What is accomplished by sending the RPC message?
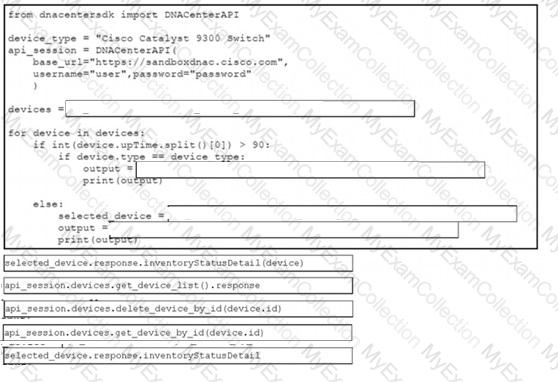
Refer to the exhibit.
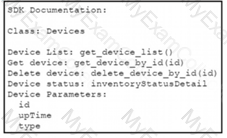
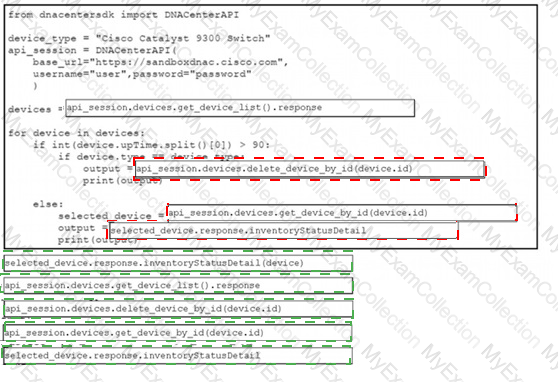
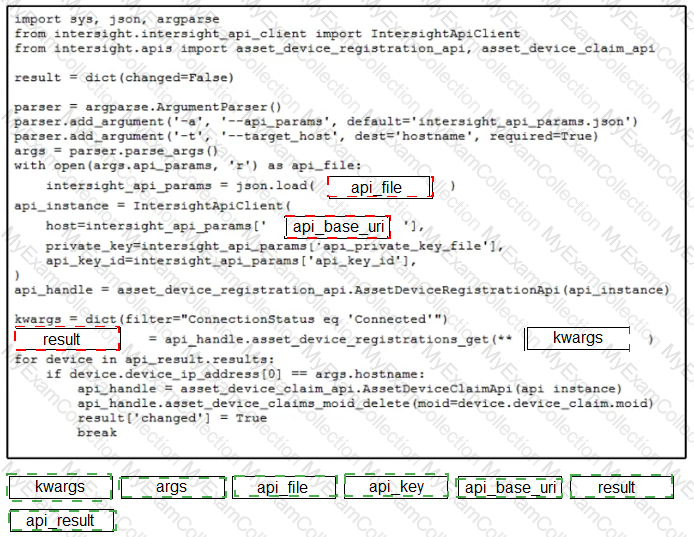
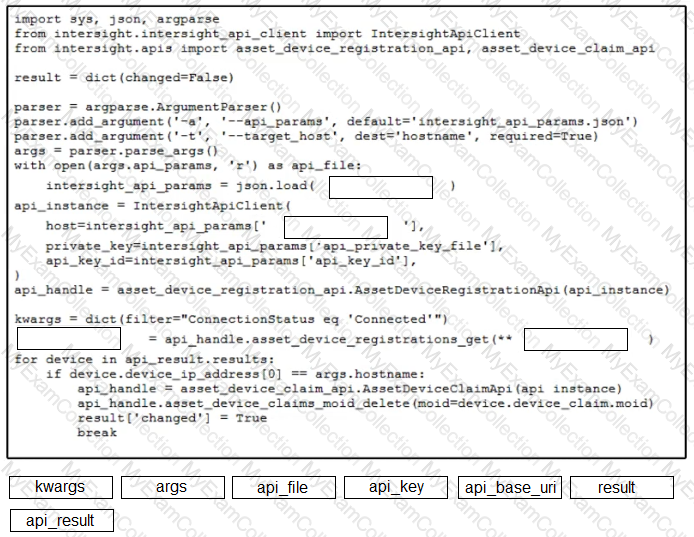
A Python script must delete all Cisco Catayst 9300 Series switches that have an uptime that is greater than 90 days The script must also query for the status of all the other devices Drag and drop the code from the bottom onto the bottom box the code is missing to complete the script Not at options are used
A local Docker alpine image has been created with an image ID of a391665405fe and tagged as “latestâ€. Which command creates a running container based on the tagged image, with the container port 8080 bound to port 80 on the host?
Refer to the exhibit.
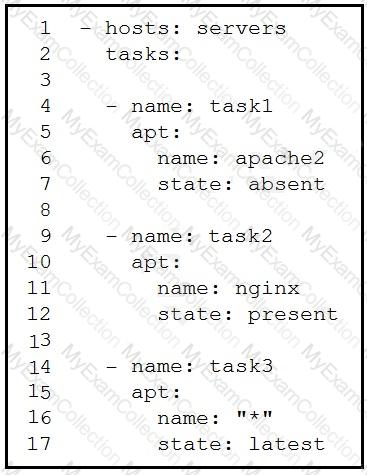
A developer must check packages on web load balancers that use nginx packages. The developer updates the servers as required in Ansible inventory and prepares an Ansible playbook to automate this workflow on related servers. Which process is being automated by the Ansible playbook?
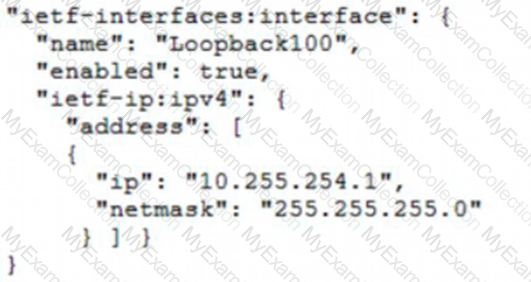
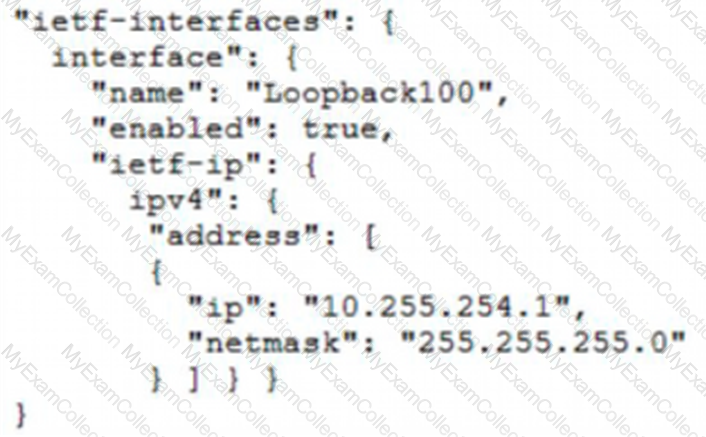
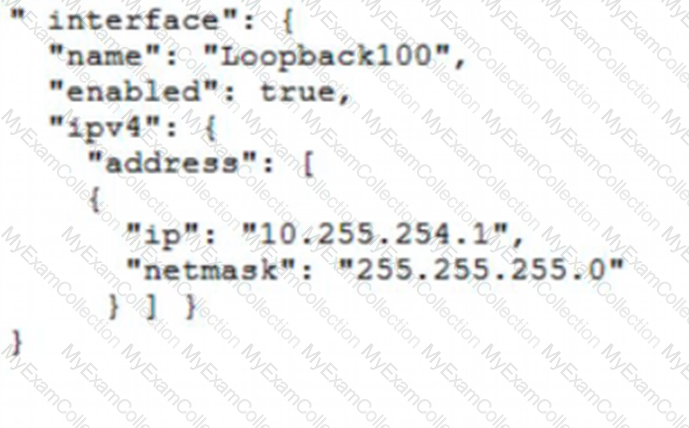
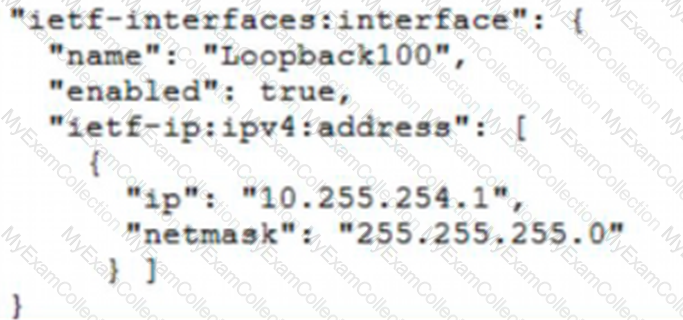
Refer to the exhibit.
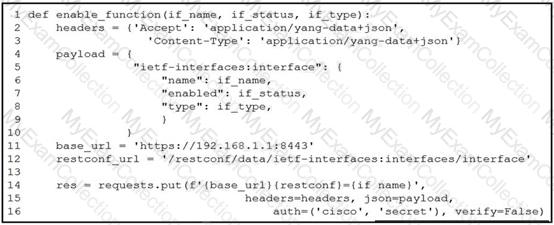
A network engineer wants to automate the port enable/disable process on specific Cisco switches. The engineer creates a script to send a request through RESTCONF and uses ietf as the YANG model and JSON as payload. Which command enables an interface named Loopback1?
A developer needs a list of clients connected to a specific device in a Meraki network. After making a REST API call, the developer receives an unfamiliar response code. Which Cisco DevNet resource should be used to identify the meaning of the response code?
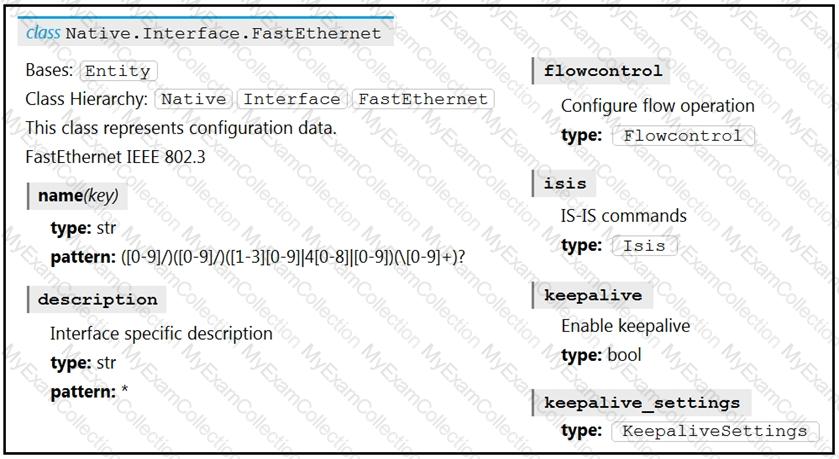
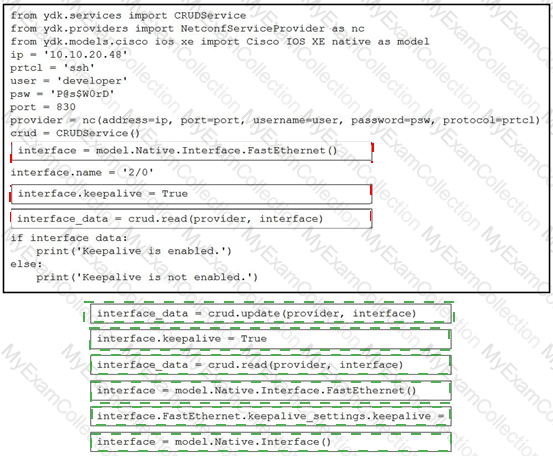
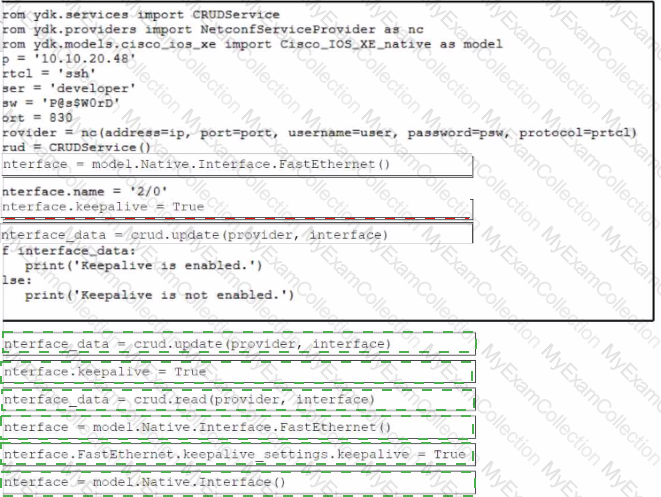
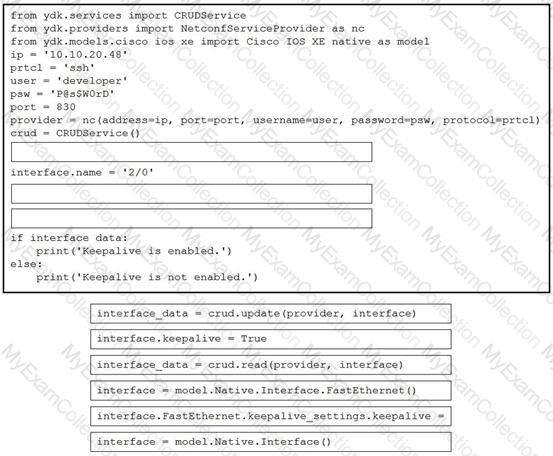
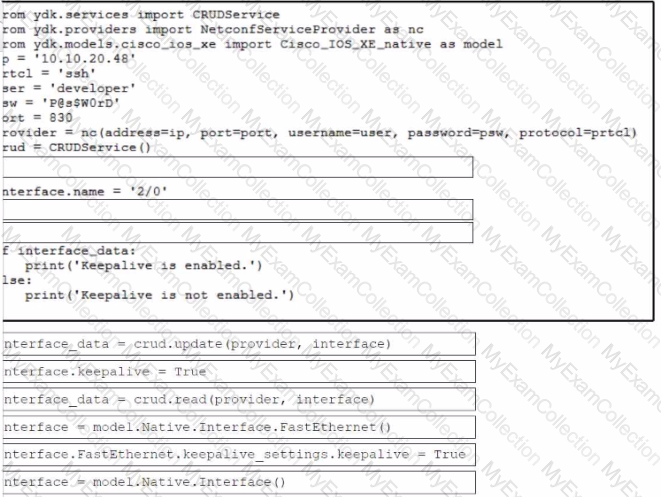
Refer to the exhibit. Drag and drop the code snippets from the bottom to the blanks in the code to enable keepalive for the FastEthernet 2/0 interface. Not all options are used.
Refer to the exhibit.
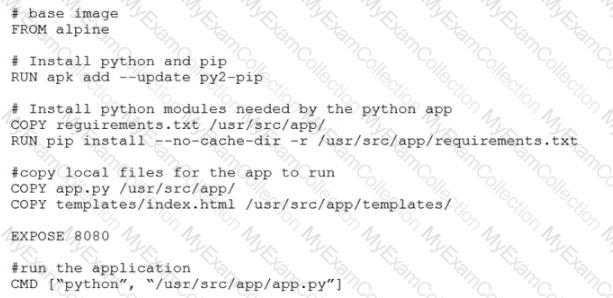
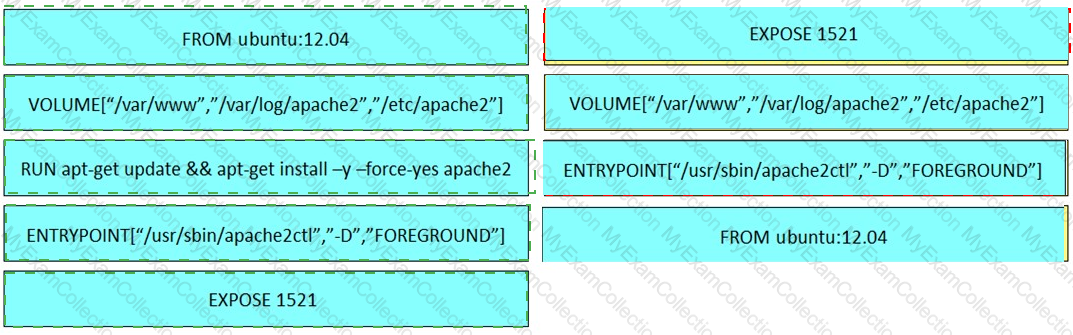
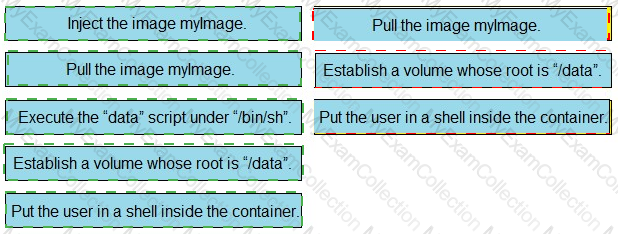
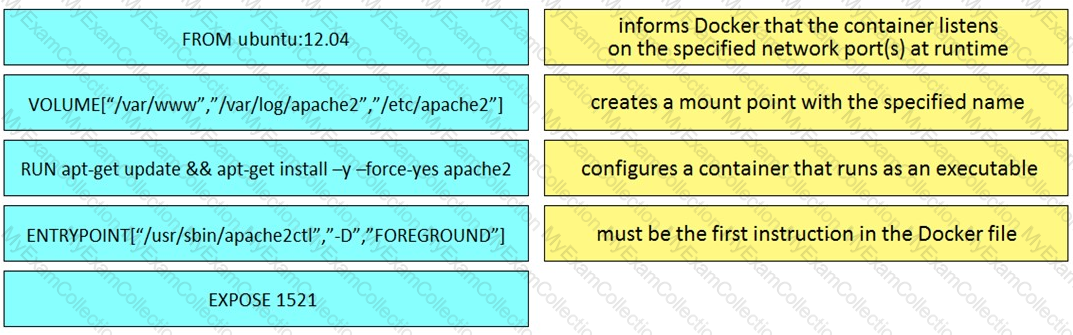
Which function does the EXPOSE line perform when building an image from this Dockerfile?
Refer to the exhibit.
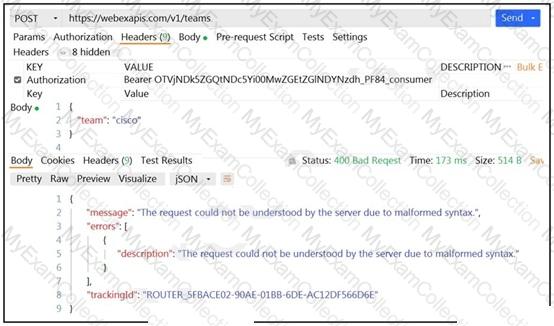
A developer wants to create a room named cisco through Webex API. The developer prepares the request by putting an API token inside the authorization header; however, the given HTTP call returns error code 400. How must the call parameters be changed to ensure a valid response?
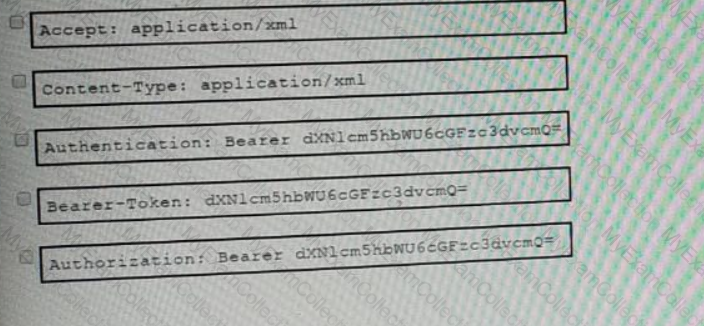
Refer to the exhibit.
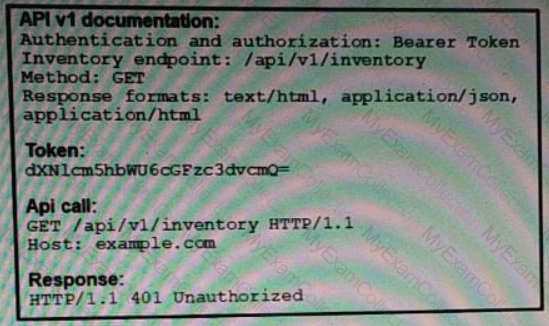
An API call is constructed to retrieve the inventory in XML format by using the API. The response to the call is 401 Unauthorized. Which two headers must be added to the API call? (Choose two.)
In test-driven development, what are two of the green bar patterns? (Choose two.)
Refer to the exhibit.
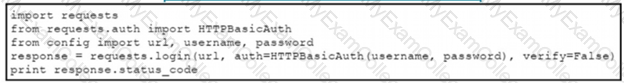
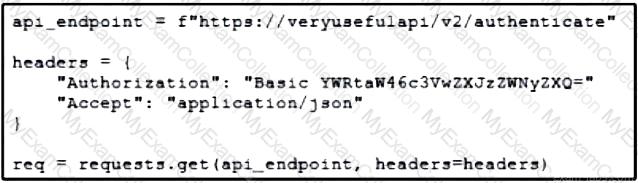
The script returns an output of 401. To use the supplied URL. an HTTP GET request must Be sent with an Authorization header. The header value is a BaseG4 encoded concatenation of the username and password. Which action must be taken to return an output of 200?
A developer is working on a feature for a new application. The changes in the existing branch named 'feat00304' must be integrated into a single commit with the current working primary branch named 'prodapp411926287'. Which git command must be used?
Refer to the exhibit.

A network engineer works on a Cisco DevNet application that is available for download on the Cisco DevNet website. The engineer prepares a bash script to automate operations that relate to the application. Which workflow is being automated in the bash script?
Drag and drop the Dockerfile instructions from the left onto the descriptions on the right. Not at options are used.
Into which type of Python data structure should common data formats be parsed?
Refer to the exhibit.
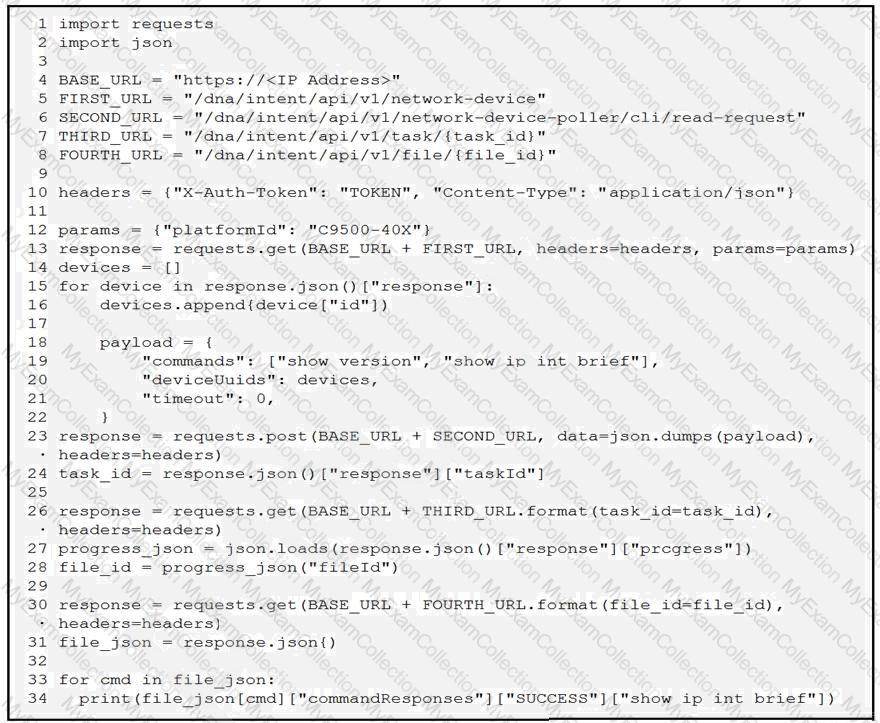
A network engineer must collect information from the network using Cisco DNA Center APIs. The script must query for the devices with 'platformId' 'C9540-x' and then send commands to be executed. Which process is automated by the Python script?
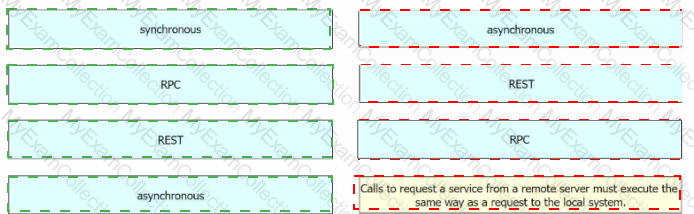
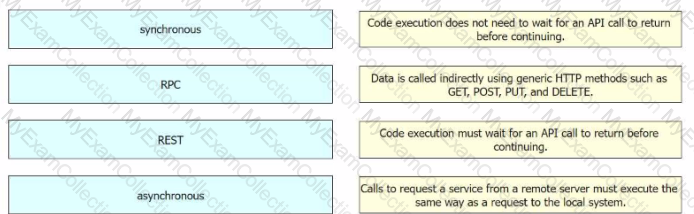
How does a synchronous API request differ from an asynchronous API request?
Refer to the exhibit.
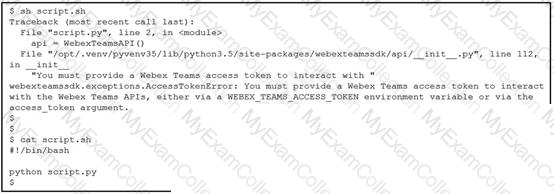
Which line must be included in the Bash script for the Python code to succeed?
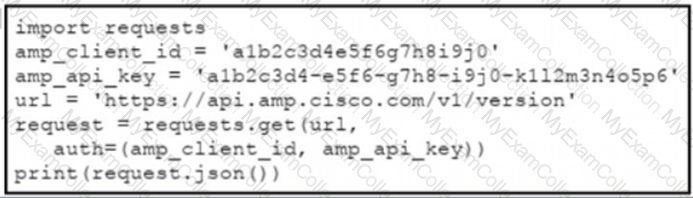
Refer to the exhibit.
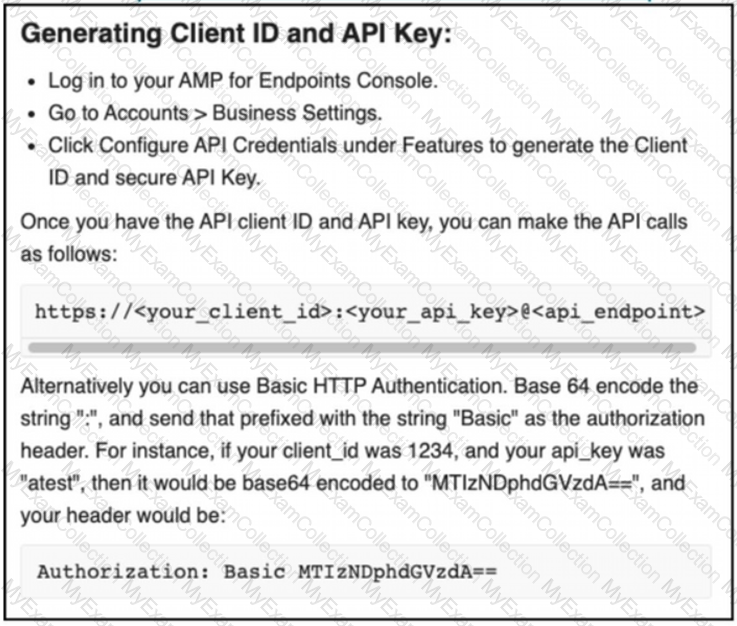
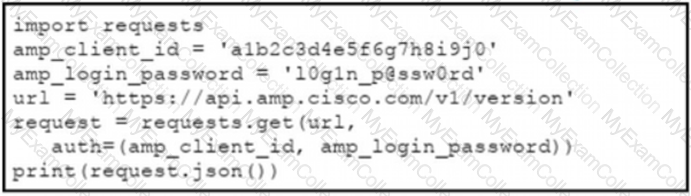
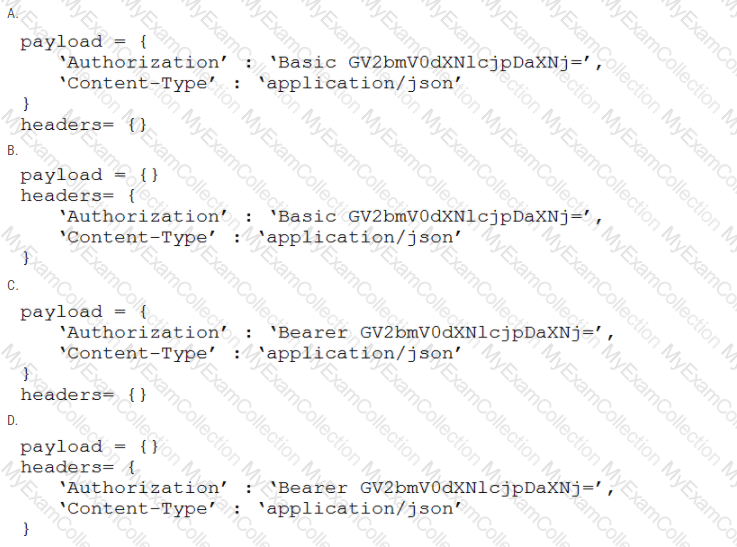
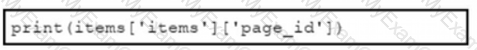
The documentation outlines how to use credentials for the AMP API Which script successfully performs an API call using basic authentication?
A)
B)
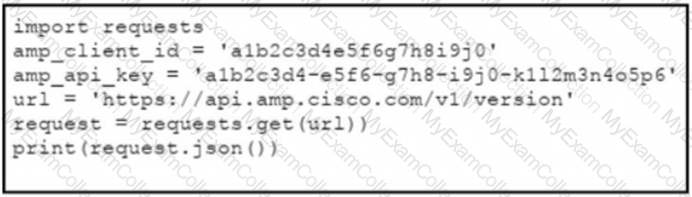
C)
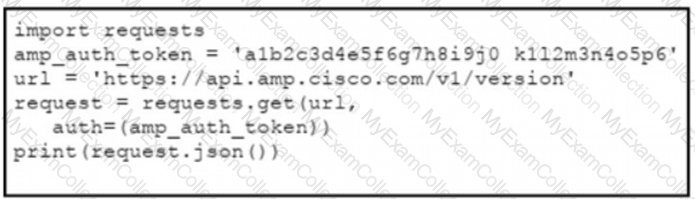
D)
Refer to the exhibit.
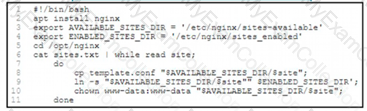
An engineer must configure a load balancer server. The engineer prepares a script to automate workflow by using Bash. The script install the nginx package, moves to the /optAtginx directory, and reads the sites M We (or further processing Based on the script workflow, which process is being automated within the loop by using the information mi sites txt?
What are two considerations when selecting the "best route" for a network device to reach its destination? (Choose two.)
Which application should be used to externally access all applications deployed in the same host machine with a single public IP address and port, when each application listens on different local ports?
Refer to the exhibit.
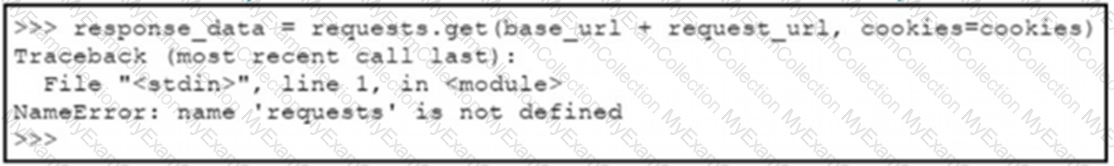
A Python code has been written to query a device. The executed code results in the error shown. Which action resolves the problem?
Refer to the exhibit.
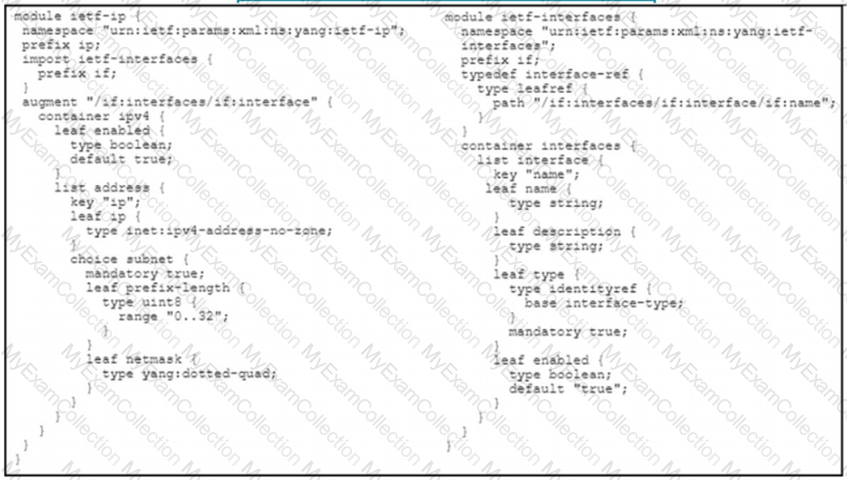
Which JSON snippet configures a new interface according to YANG model?
A)
B)
C)
D)
A developer has created a new image to use in a Docker build and has added a tag for the image by using the command:
$ docker tag 84fe411926287 local/app:0.4
Which command must be executed next to build the Docker image using the tag?
A developer is creating a script to interact with a REST API service which requires basic authentication. The credentials are "devnet:391665405" and the Base64 encoding of the credentials is "GV2bmV0dXNlcjpDaXNj=". Which payload and header combination must be used for authentication?
What is a benefit of a model-driven approach for infrastructure automation?
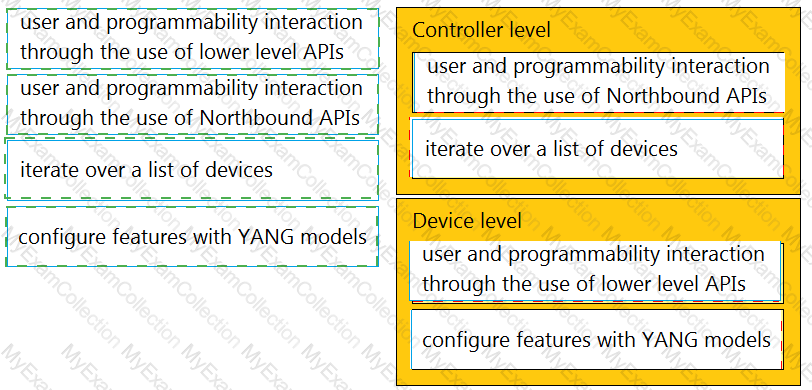
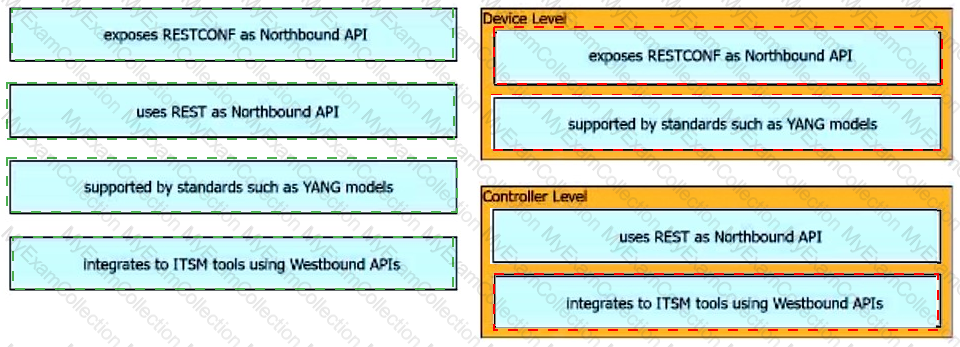
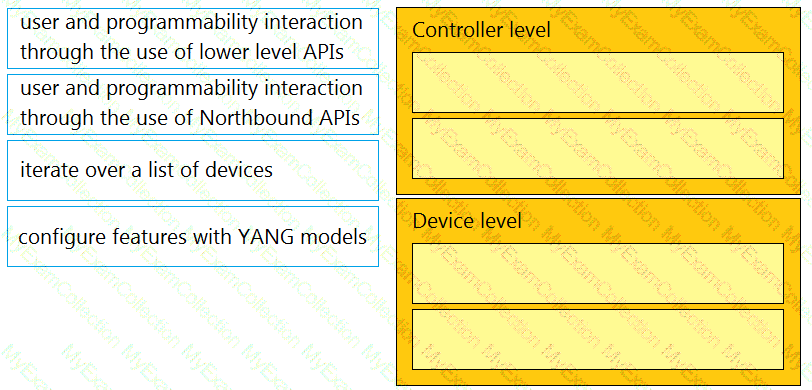
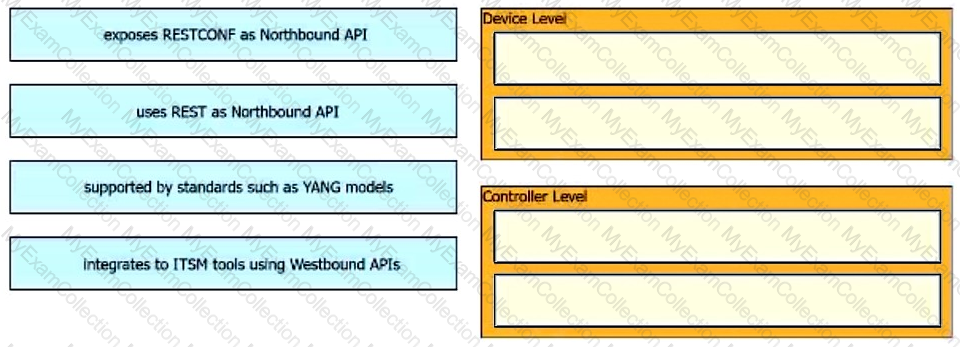
Drag and drop the types of management from the left onto the levels at which they are performed on the right.
Access to the management interface of devices must be restricted by using SSH and HTTPS. Which two ports must be included in the ACLs for the protocols to work? (Choose two.)
Refer to the exhibit.
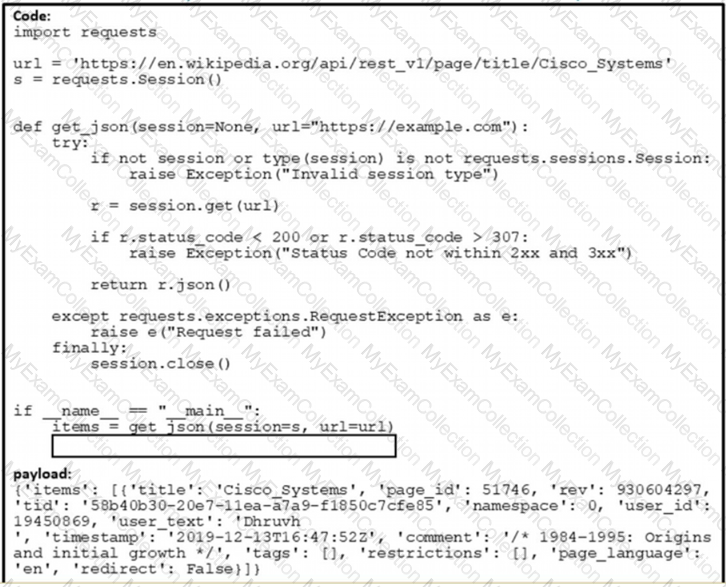
Which command needs to be placed on the box where the code is missing to output the value of page_jd in the Python 3.7 script?
A)
B)
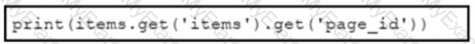
C)
D)
An engineer must review and clean up a code repository. During the review, the engineer finds a file named config.json that contains API URLs, shared keys, and other application configurations. Which two methods, according to best practice, must be used to protect secrets? (Choose two.)
Which Cisco platform is used to manage data center infrastructure through third-party tools and system integrations?
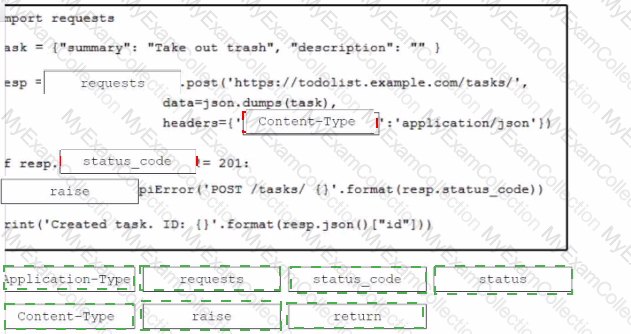
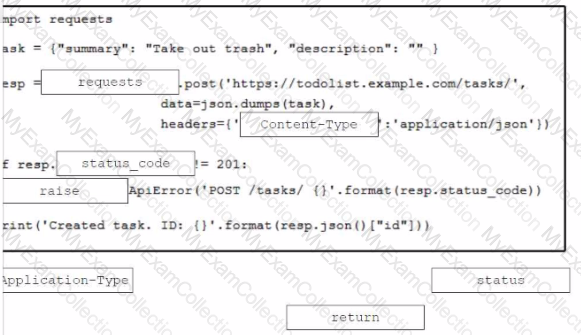
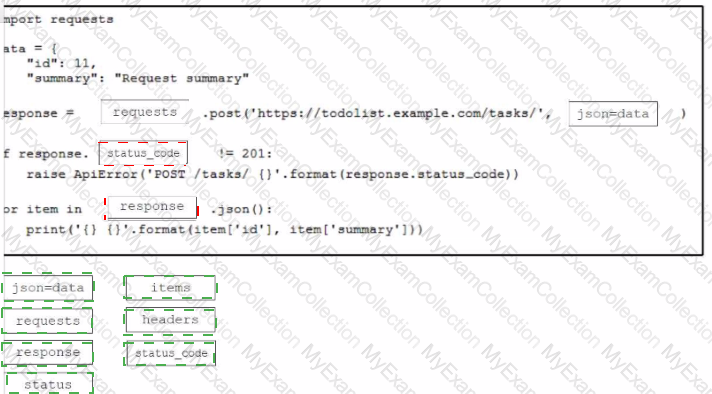
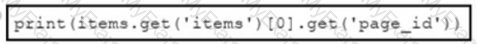
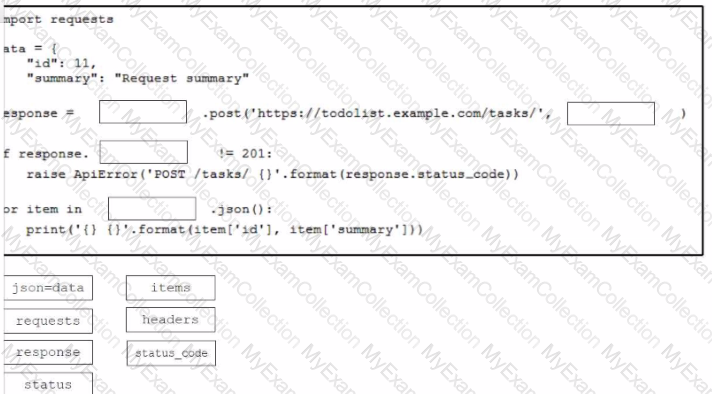
Drag and drop the code from the bottom onto the box where the code is missing to construct a Python script that calls a REST API request. Not all options are used.
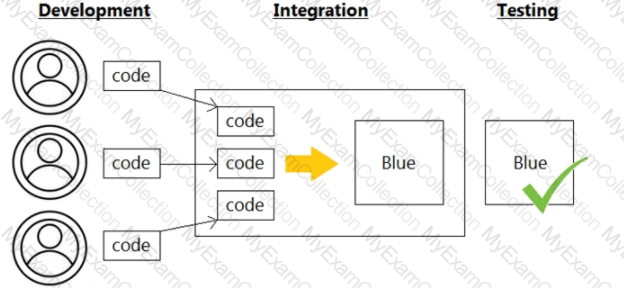
A team of developers is responsible for a network orchestration application in the company. The responsibilities also include:
developing and improving the application in a continuous manner
deployment of the application and management of CI/CD frameworks
monitoring the usage and problems and managing the performance improvements
Which principle best describes this DevOps practice?
A customer's cloud services must:
Migrate services to another data center on demand.
Save the operational state of the machine on demand.
Support Windows and Linux GUIs.
Maximize hardware utilization.
Which type of deployment meets these requirements?
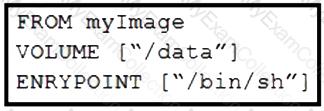
Refer to the exhibit. Drag and drop the actions from the left that the contents of this Dockerfile accomplish onto the right. Not all options are used.
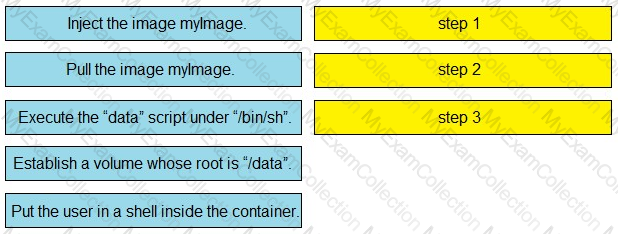
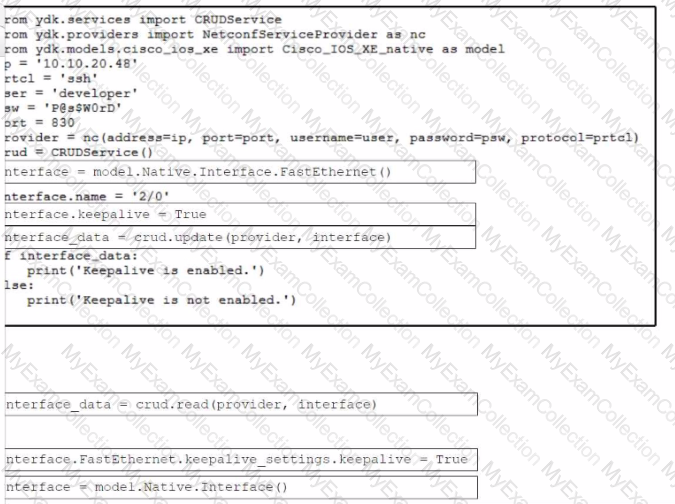
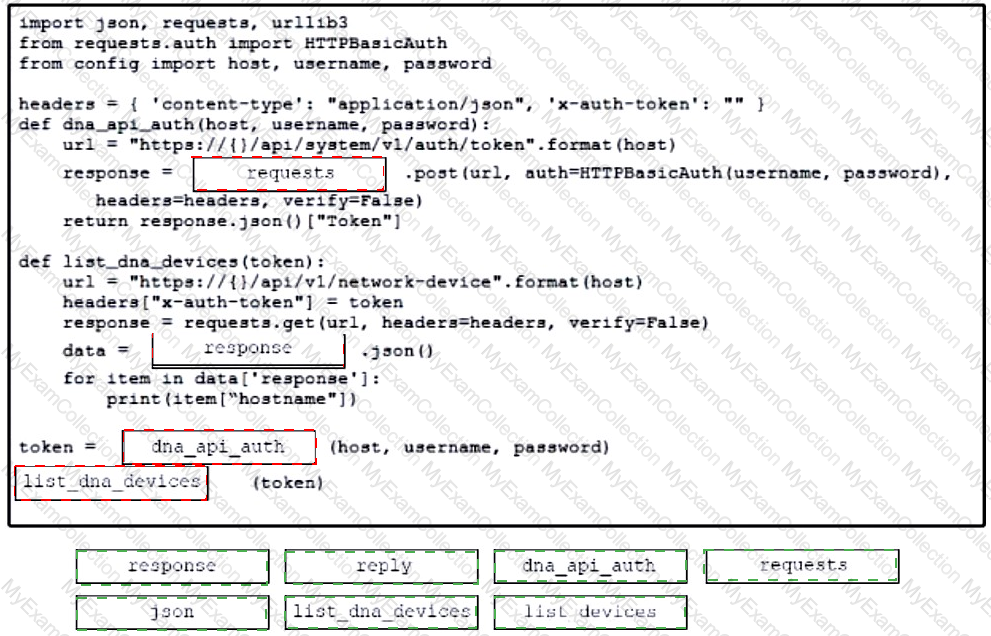
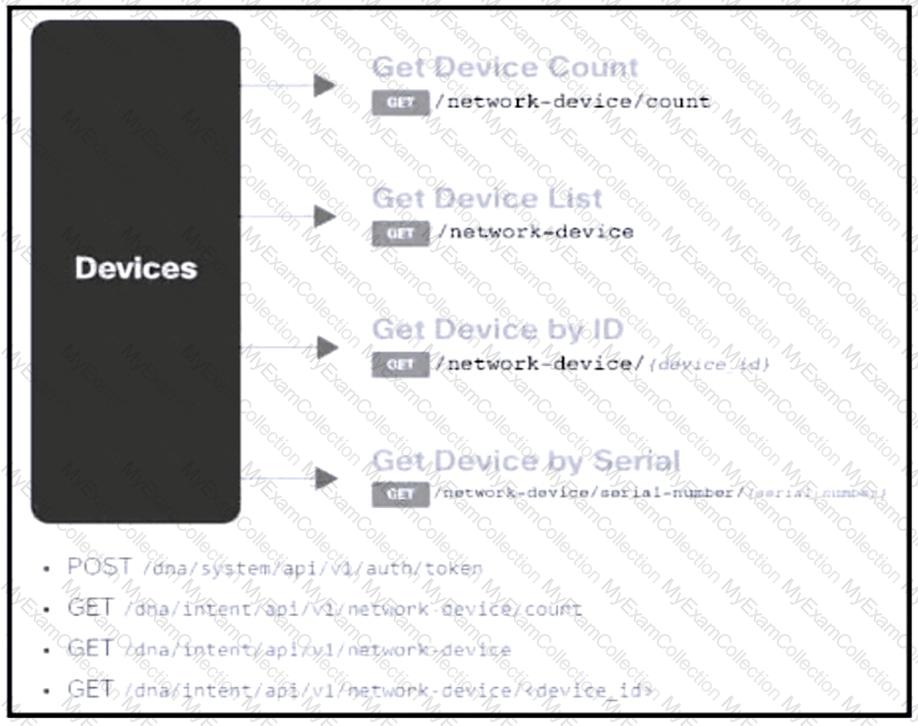
Refer to the exhibit. An engineer prepares a script to automate workflow by using Cisco DNA Center APIs to display:
total count of devices
list of the network devices
information of one device with a hostname filter
What is displayed in the final step after the Python script is executed?

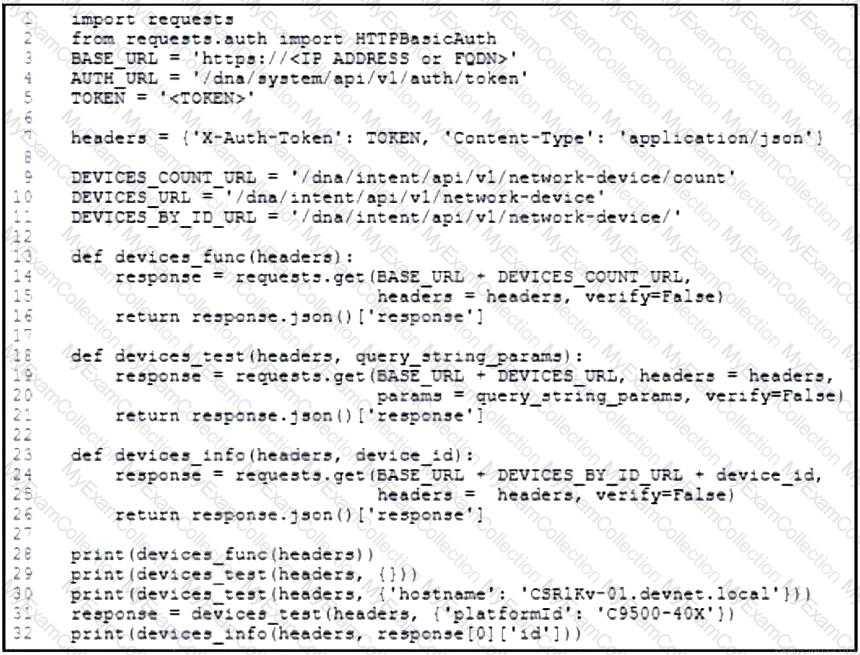
Refer to the exhibit. Drag and drop the code snippets from the bottom to the blanks in the code to enable keepalive for the FastEthernet 2/0 interface. Not all options are used.
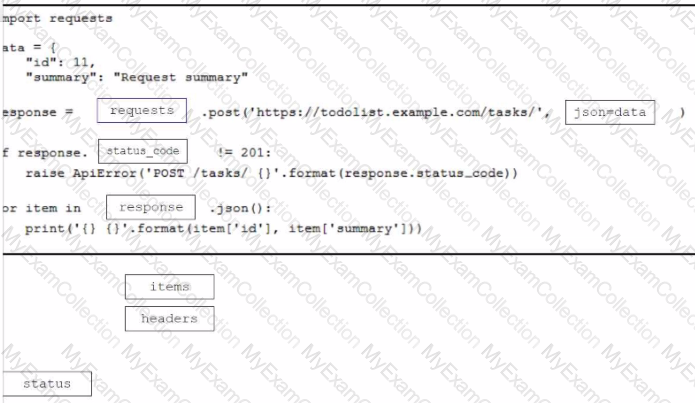
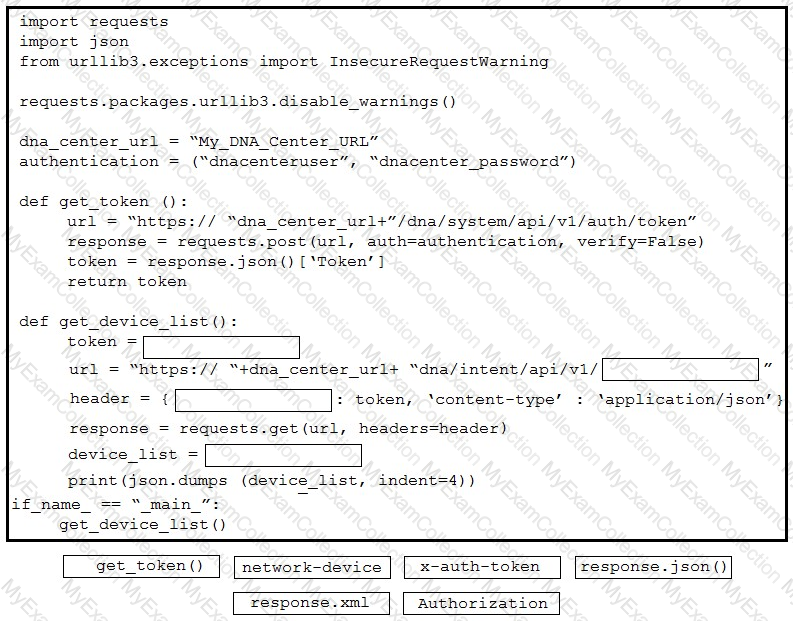
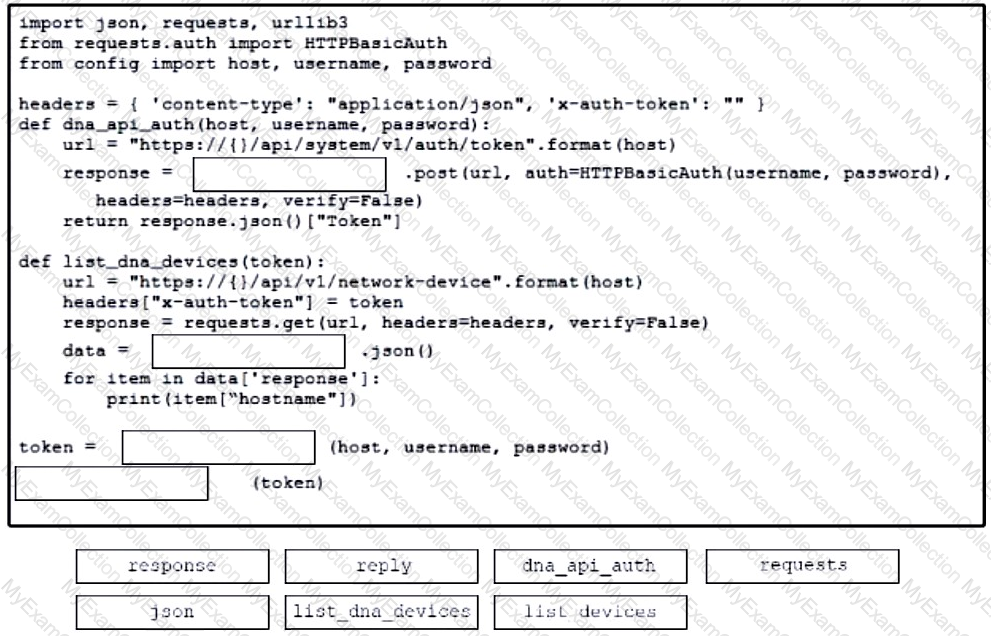
Refer to the exhibit. Drag and drop the code snippets from the bottom onto the blanks in the Python script to retrieve a list of network devices from Cisco DNA Center. Not all options are used.
A developer is developing a web application that uses username and password to authenticate to the next service. The user credentials must be available at any time in the application. The developer must choose and implement a secure method of storing the authentication credentials that are used in the automation code. Which password handling method must be used to minimize the security risk?
Refer to the exhibit.
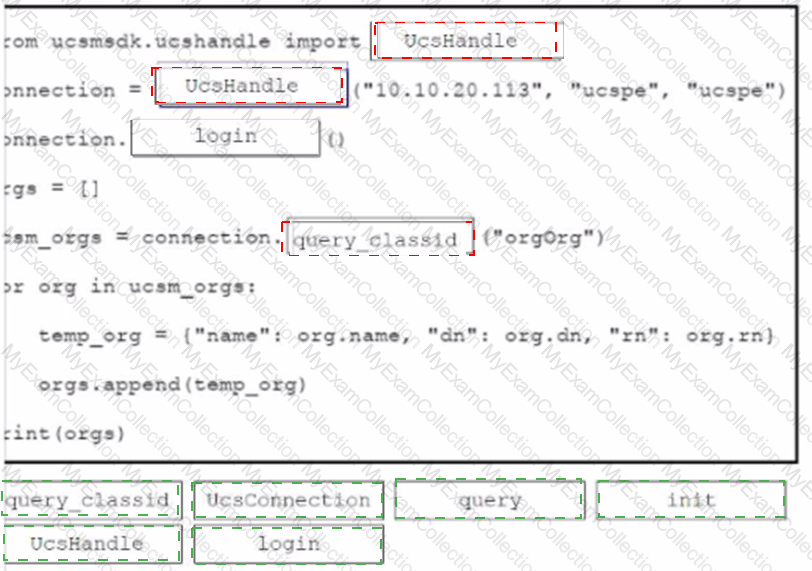
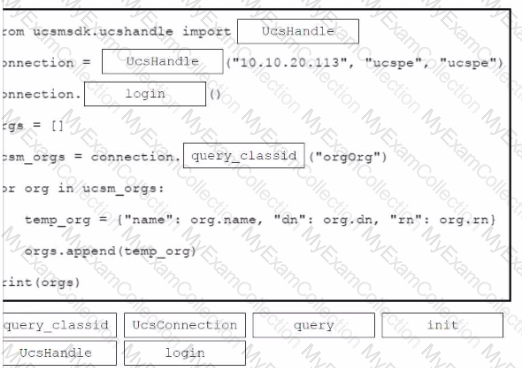
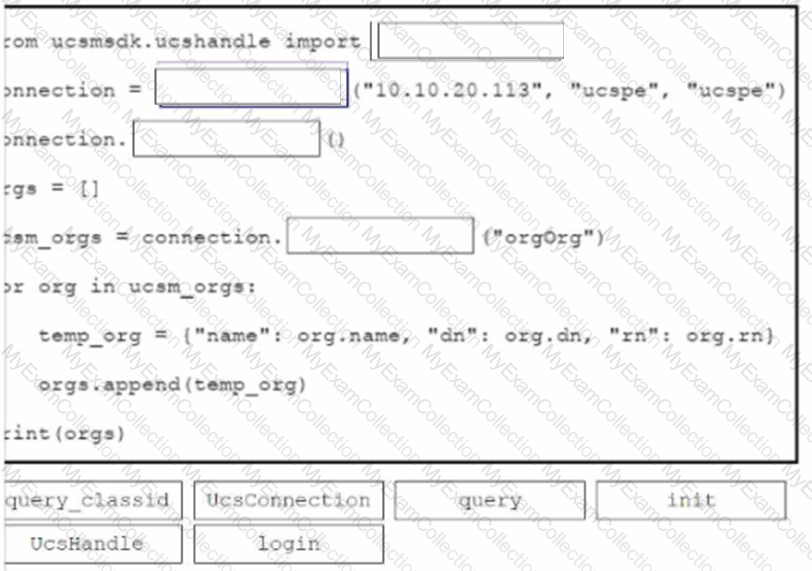
An engineer needs to retrieve all the organizations in a Cisco UCS Manager deployment. Drag and drop the code snippets from the bottom onto the blanks in.. Python script to print the information to standard output. Some options may be used more than once. Not all options are used.
A developer creates a new application, but the application must be tested before being released to a customer. When a mobile phone that uses 4G is used to access the application, the request fails. Why does the connection to the application fail?
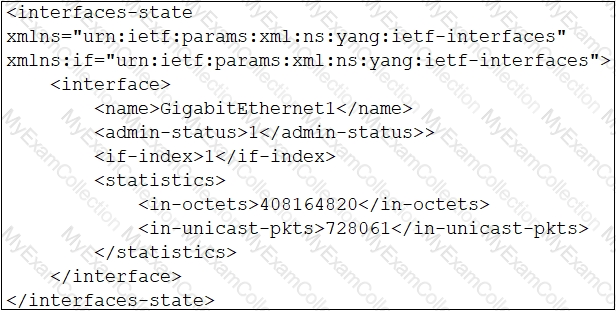
Refer to the exhibit.
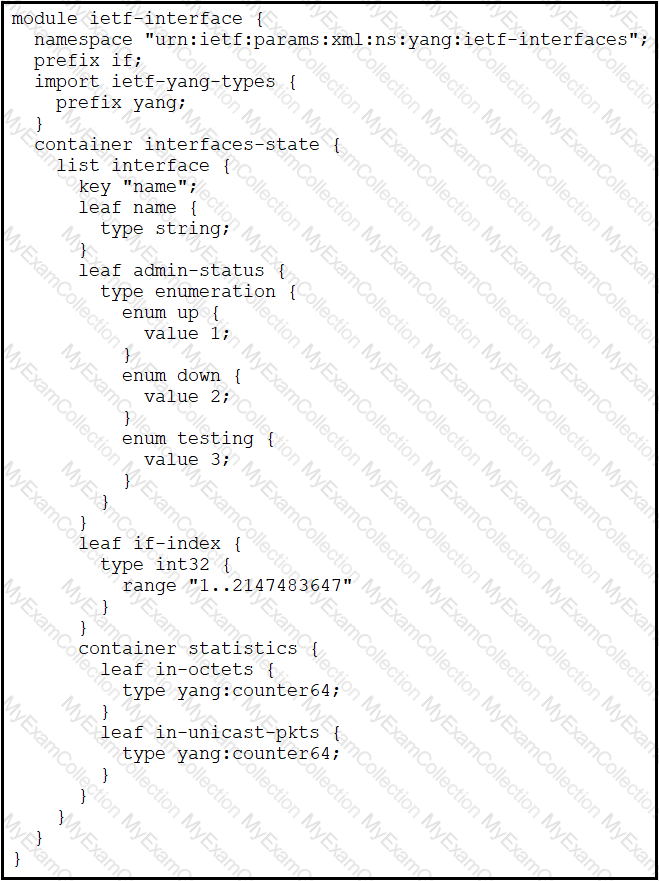
Which XML snippet has interface information that conforms to the YANG model?
A)
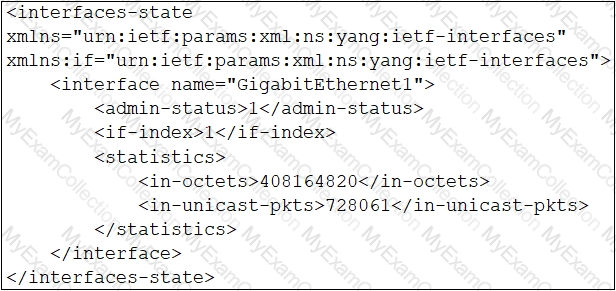
B)
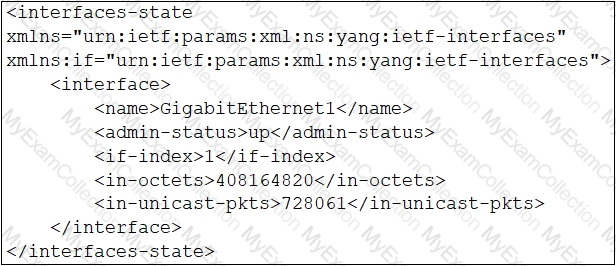
C)
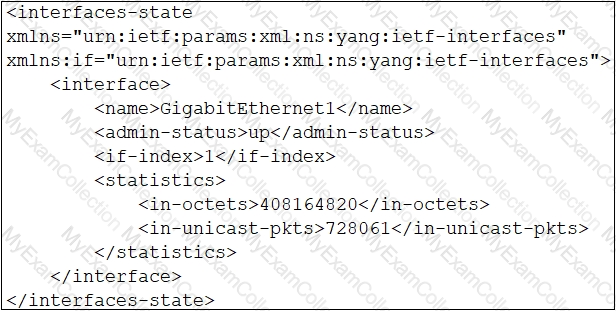
D)
Refer to the exhibit.
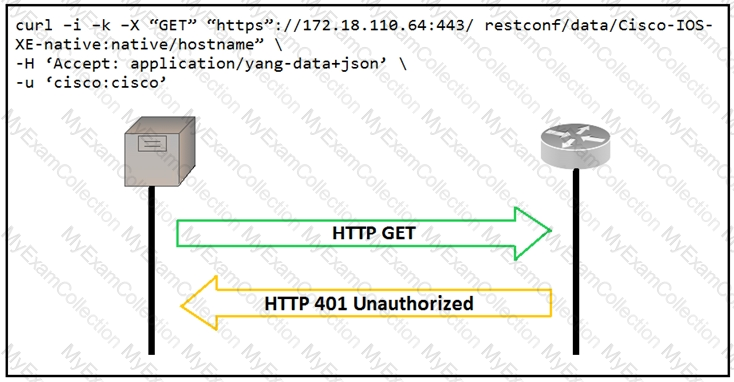
An administrator attempts to perform a GET operation by using the Cisco IOS XE RESTCONF API to return the hostname of a device. The sequence diagram in the exhibit illustrates the HTTP messages observed. Which change to the API request resolves the issue?
Which two commands download and execute an Apache web server container in Docker with a port binding 8080 in the container to 80 on the host? (Choose two.)
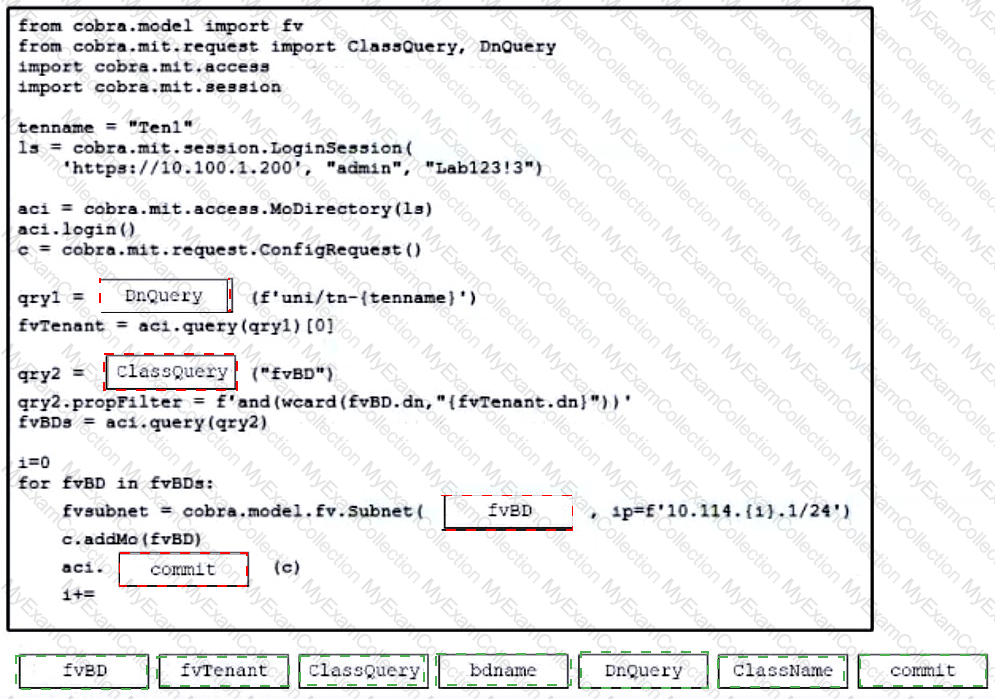
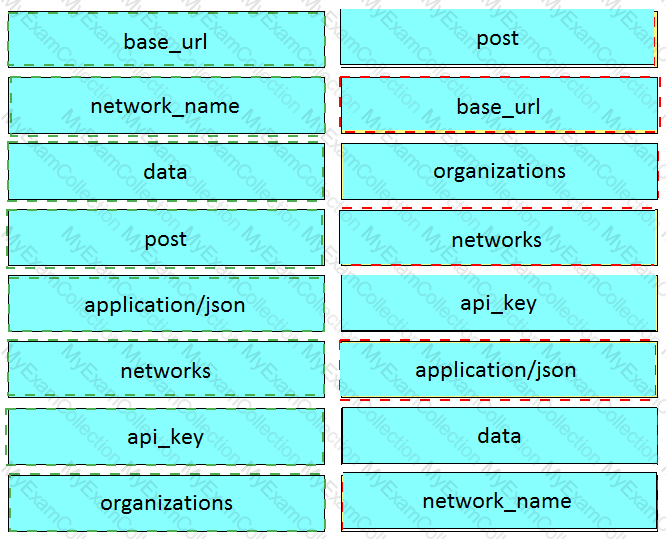
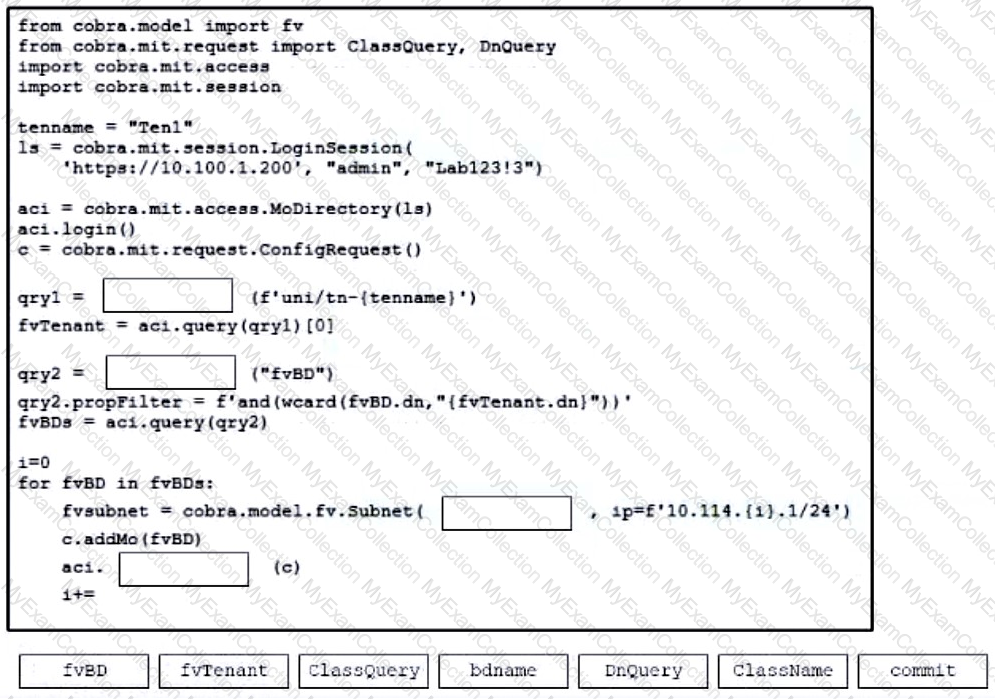
Refer to the exhibit. Drag and drop the code from the bottom onto the box where the code is missing to add a subnet to each bridge domain in the Ten1 tenant. Not all options are used.
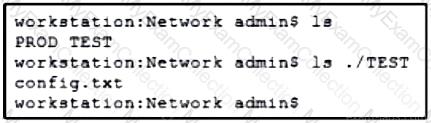
Refer to the exhibit. A network engineer must copy the “config.txt†file from directory TEST to directory PROD. The copied file must also be renamed into “current.txtâ€. Which command must be used to accomplish these tasks?
Refer to the exhibit. A developer is part of a team that is working on an open-source project in which source code is hosted in a public GitHub repository. While the application was built, security concerns were addressed by encrypting the credentials on the server. After a few months, the developer realized that a hacker managed to gain access to the account. The exhibit contains part of the source code for the login process. Why was the attacker able to access the developer's account?
When a Cisco IOS XE networking device is configured by using RESTCONF, what is the default data encoding method?
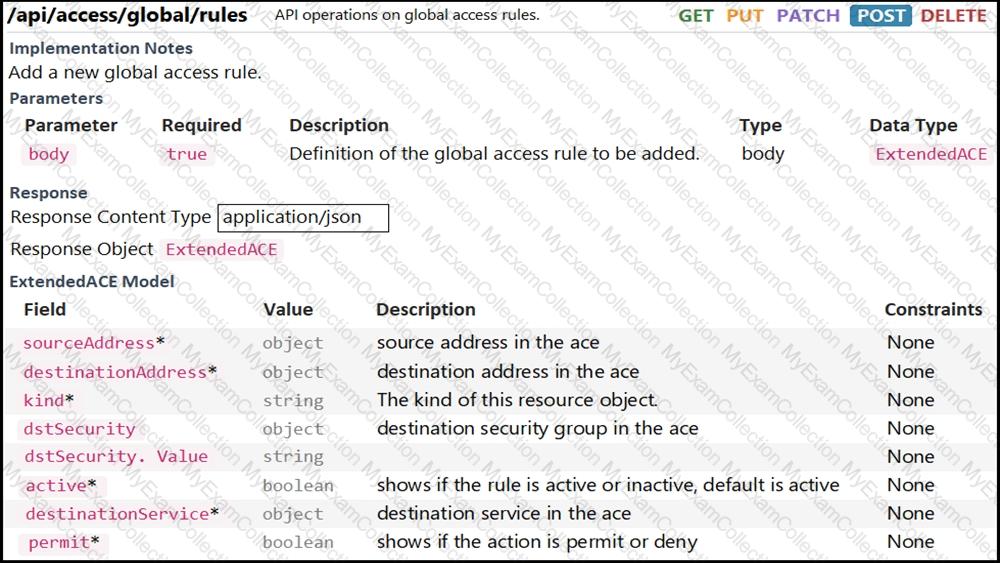
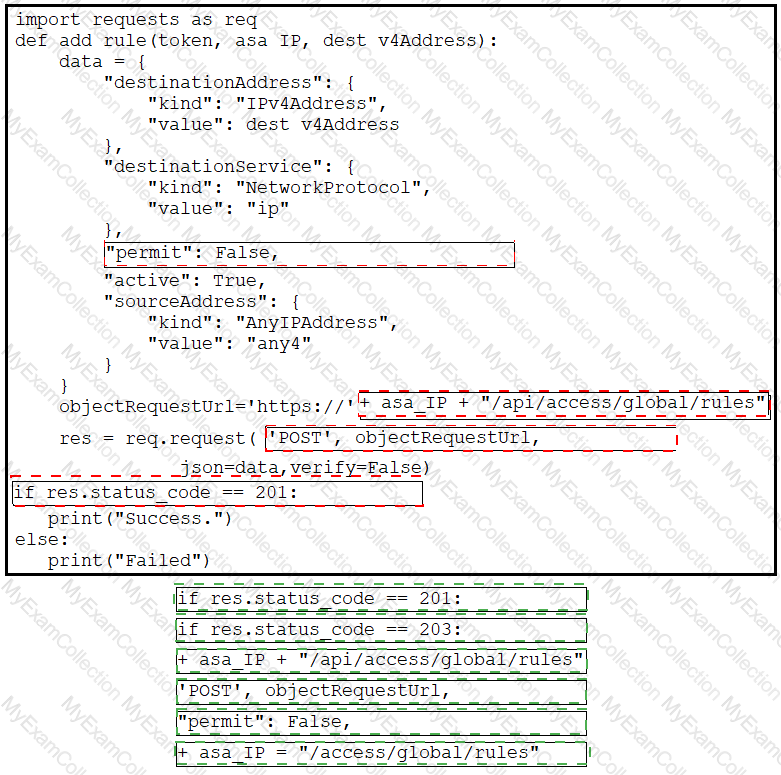
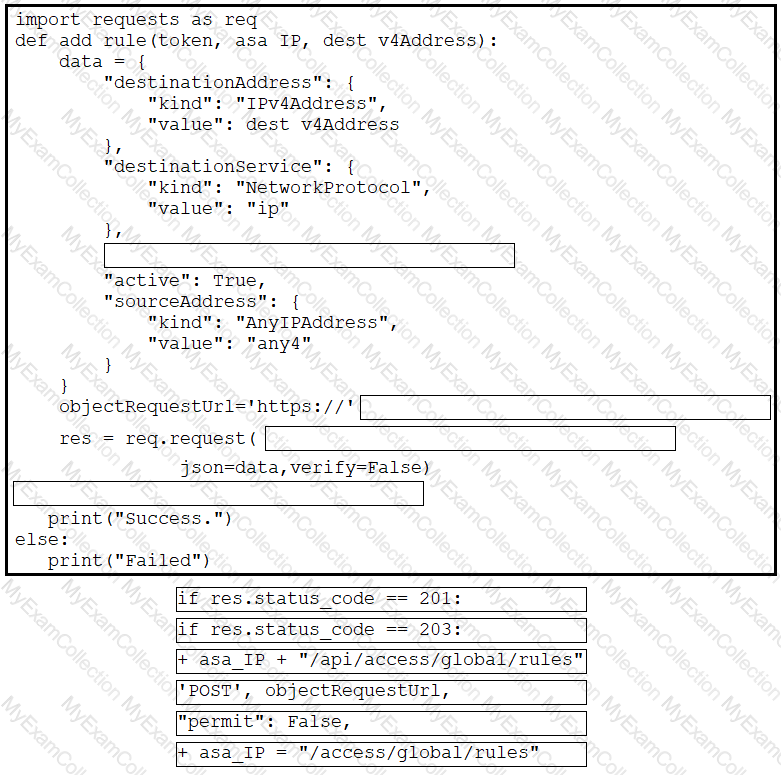
Refer to the exhibit. Drag and drop the code from the bottom onto the box where the code is missing to complete the function that adds a new global access rule that denies traffic using the Cisco ASA REST API. Not all options are used.
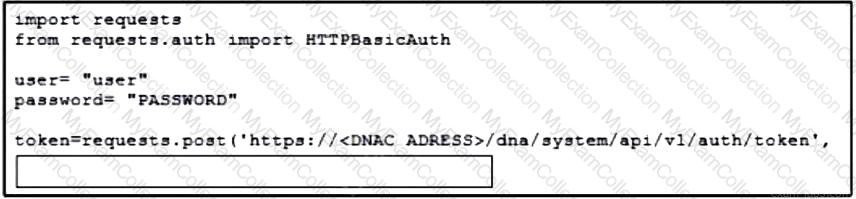
Refer to the exhibit. A developer must use a token to collect data from Cisco DNA Center API and prepares a Python script to send requests. Which line of code needs to be placed on the snippet where the code is missing to obtain a token from the Cisco DNA Center API?
Developer is working on a new feature and made changes on a branch named ‘branch-413667549a-new’. When merging the branch to production, conflicts occurred. Which Git command must the developer use to recreate the pre-merge state?
Which type of OWASP threat forges a malicious HTTP request into an application?
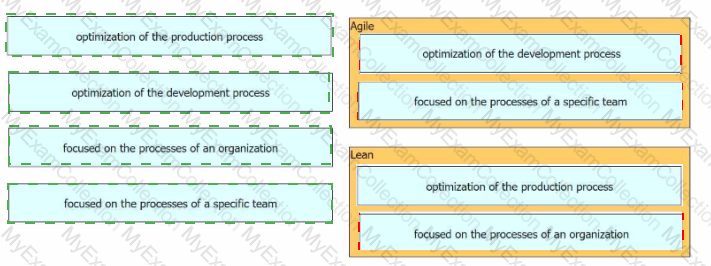
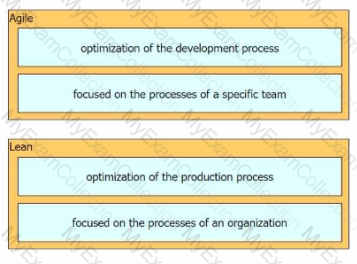
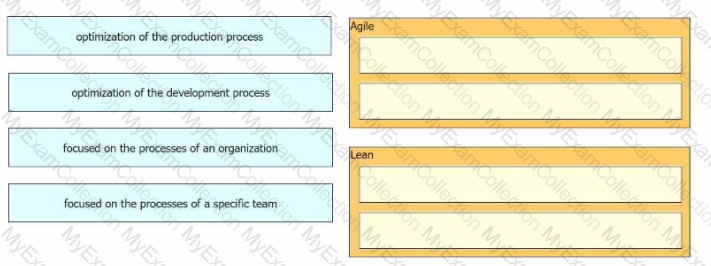
Drag and drop characteristics from the left onto the infrastructure management methodologies on the right.
Drag and drop the code from the bottom onto the box where the code is missing to construct a Python script that calls a REST API request. Not all options are used.
Refer to the exhibit.
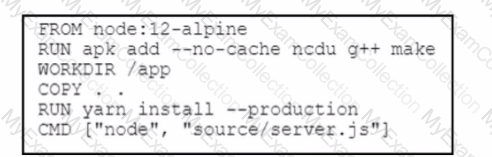
The server.js Node.js script runs after the Dockerfile creates its container. What is the working directory of the application inside the container?
A developer plans to deploy a new application that will use an API to implement automated data collection from Webex with these requirements:
The application was created by using the request library.
Requires HTTP basic authentication.
Provides data in JSON or XML formats.
Which Cisco DevNet resource helps the developer with how to use the API?
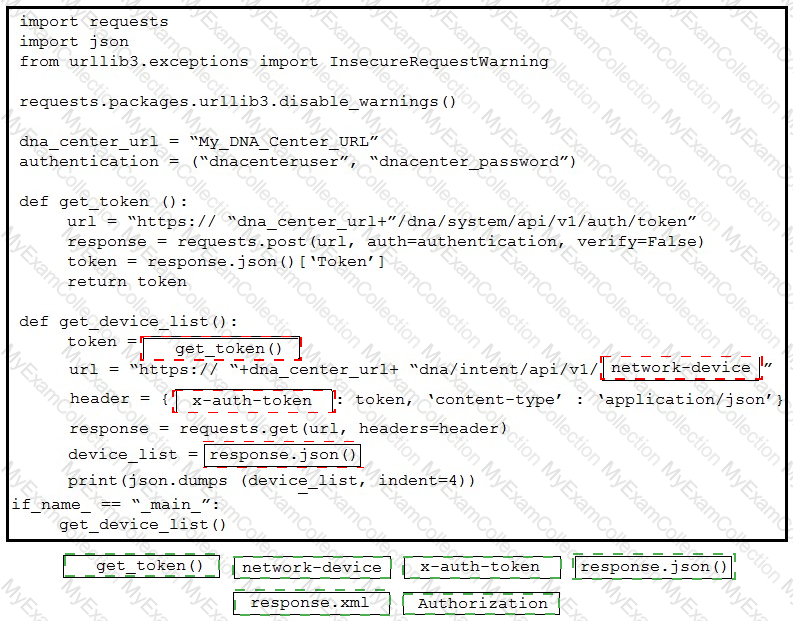
Refer to the exhibit. Drag and drop the code from the bottom onto the box where the code is missing to construct a request that generates a security token and gets a list of network devices. Not all options are used.
Which RFC 1918 address space includes a subnet of 172.16.0.0 that uses a mask of 255.255.0.0?
Drag and drop the characteristics from the left onto the software development methodologies on the right.
What is the purpose of running tests before writing code in test-driven development?
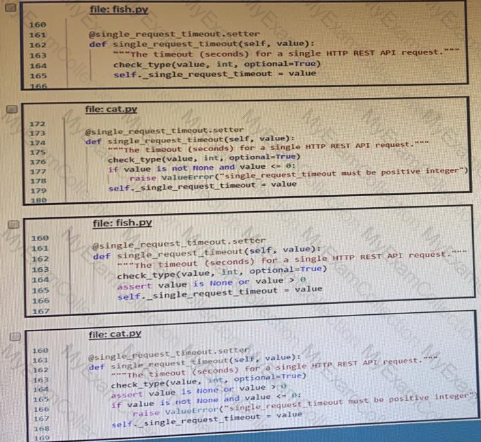
Refer to the exhibit.
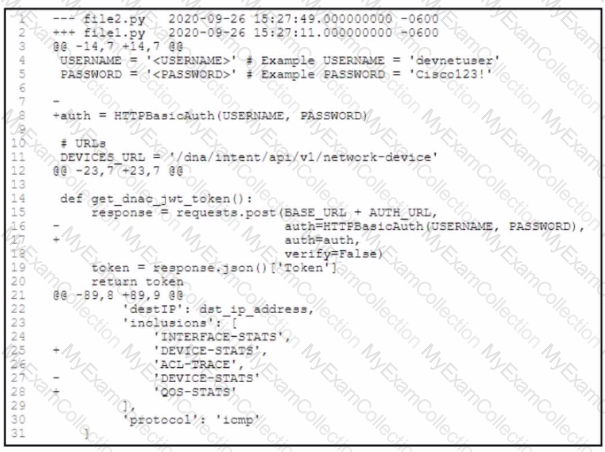
An engineer is comparing two tiles by using the unified cliff format What is determined by the content in the file2.py file?
Drag and drop the common API styles from the left onto the requirement on the right.
Refer to the exhibit. Drag and drop the code from the bottom onto the box where the code is missing to construct a Python script by using the Cisco SDK. Not all options are used.
An engineer must investigate the problems on a web application and address them to related teams. The engineer verifies the application reachability from the single public IP
dress with port and discovers that HTTPS access works to three servers of a network farm with IP 172.16.50.1 .2 and .4. but HTTPS access to the server with IP 172.16.50.3 does : work. Which problem type must be addressed as the cause for the case?
Which REST architectural constraint indicates that no client context should be stored on the server between requests?
Refer to the exhibit.
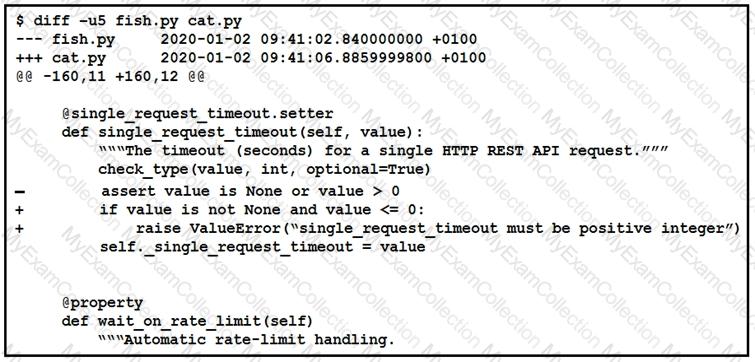
The output of a unified diff when comparing two versions of a python script is shown. Which two “single_request _timeout ()â€
Which principle is a value from the manifesto for Agile software development?
Refer to the exhibit.
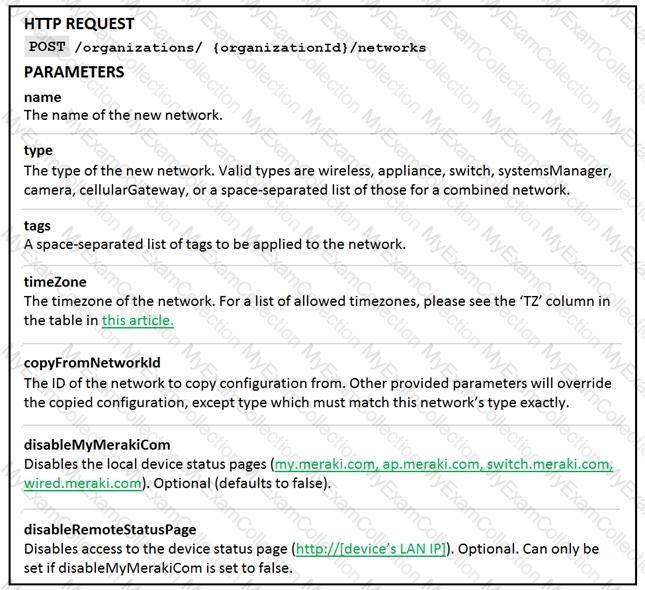
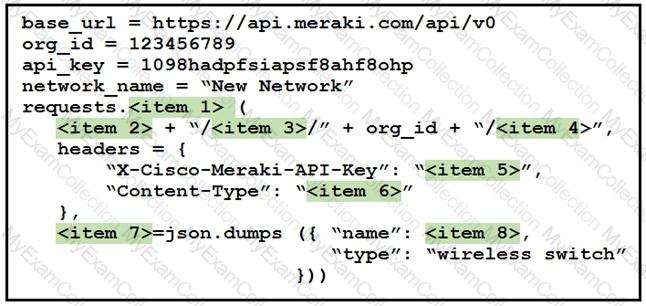
Drag and drop the code from the left onto the item numbers on the right to complete to Meraki python script shown in the exhibit.
Which network device monitors incoming and outgoing traffic and decides whether to allow or block specific traffic based on a defined set of rules?
What is used in Layer 2 switches to direct packet transmission to the intended recipient?
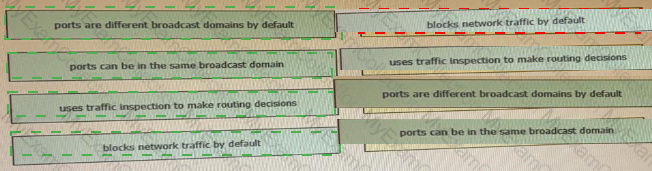
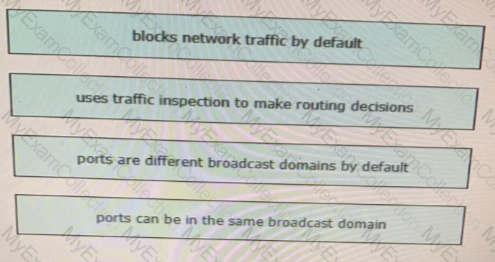
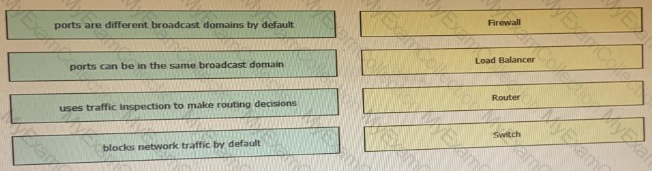
Drag and drop the functionalities from the left onto correct networking devices on the right.
A company has written a script that creates a log bundle from the Cisco DNA Center every day. The script runs without error and the bundles are produced. However, when the script is run during business hours, report poor voice quality of phones calls. What explains this behavior?
Which Cisco DevNet resource allows access to products in a development lab to explore, learn, and build application that use Cisco APLs?
A small company has 5 servers and 50 clients. What are two reasons an engineer should spilt this network into separate client and server subnets? (Choose two)
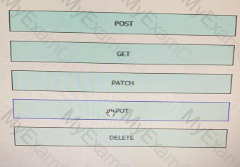
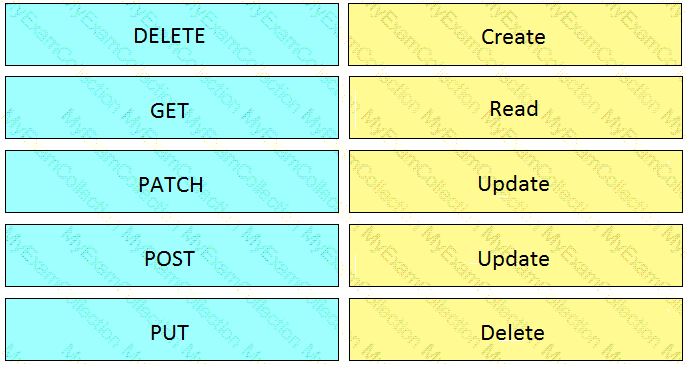
: 19 DRAG DROP
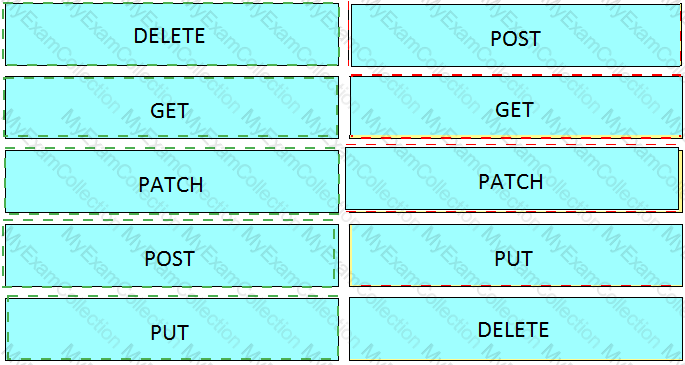
Drag and drop the HTTP methods from the left onto their generally accepted corresponding create, read, update, and delete operations on the right.
What is the outcome of executing this command?
git clone ssh://john@exmaple.com/path/to/my-project_git
Refer to the exhibit.
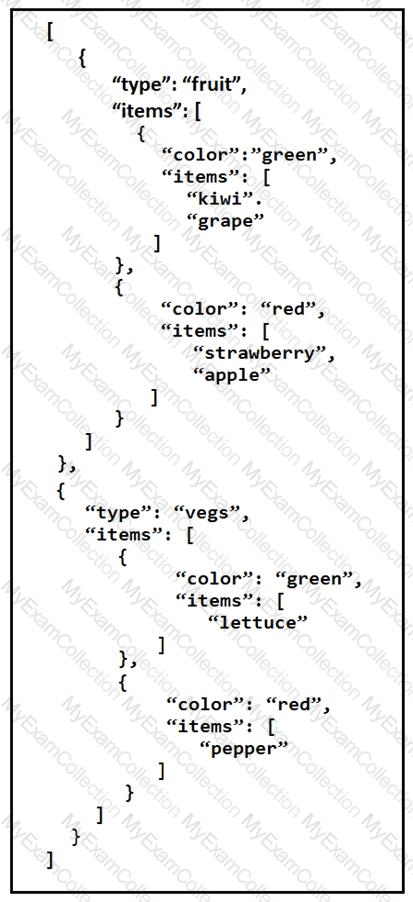
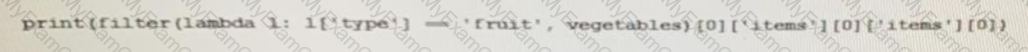
A REST API retune this JSON output for a GET HTTP request, Which has assigned to a variable called “vegetables†Using python, which output is the result of this command?
A 401 HTTP response code is returned when calling a REST API. What is the error state identified by this response code?
Which task is performed because the test-driven development approach is being used?
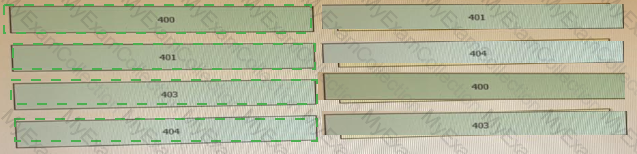
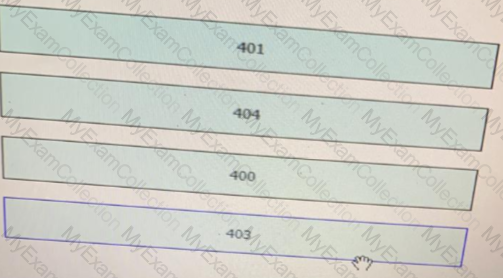
Drag and drop the HTTP status codes from the left onto the correct descriptions on the right.

Which type of threat occur when an attacker can send hostile data to an interpreter within an application?
What operation is performed with YANG model-driven programmability in NX-OS?
Refer to the exhibit.
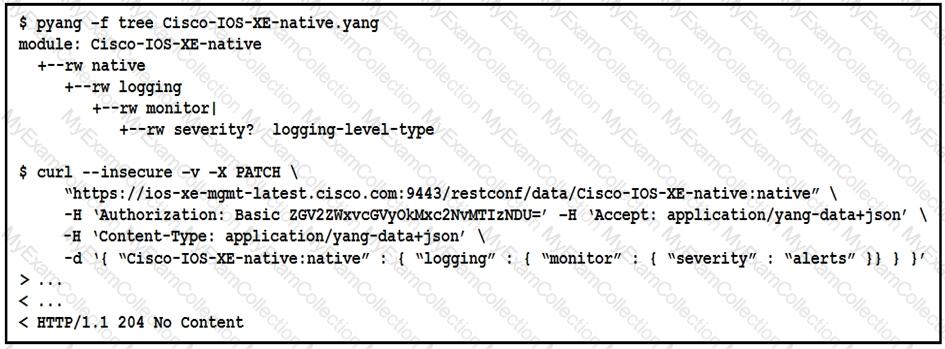
The definition of the YANG module and a RESTCONF query sent to a Cisco IOc XE device is shown. Which statement is correct if the RESTCONF interface responds with a 204 status code?
What are two advantages of YANG-based approaches for infrastructure automation? (Choose two.)
Which platform has an API that be used to obtain a list of vulnerable software on user devices?
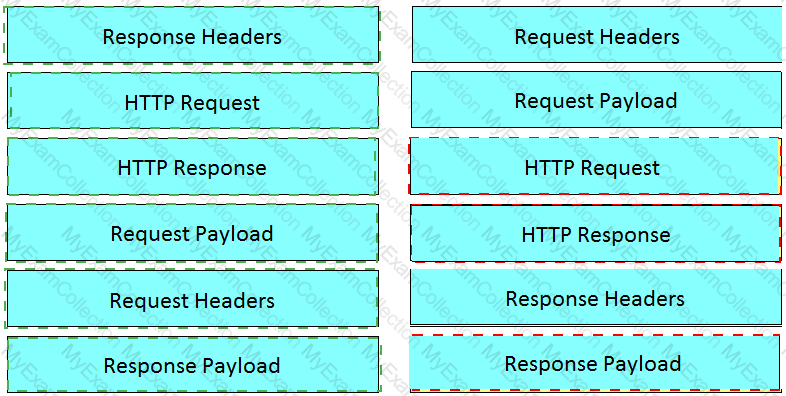
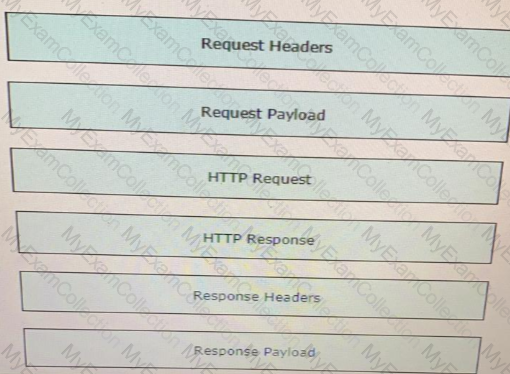
Refer to the exhibit.
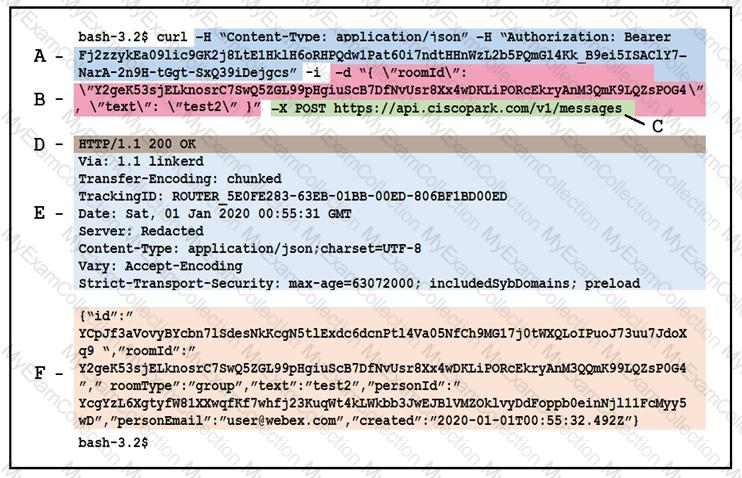
Drag and drop the descriptors from the left onto the correct parts of the API request and response on the right.
A REST API service requires authentication based on the username and password. The user “john†has the password “384279060†and the Base64 encoding of those credentials is “am9objowMTIzNDU2Nzg=â€. Which method completes an authentication request?
Which response status code is used by a RESTful interface to indicate successful execution of a request?
Fill in the blanks to complete the statement.
Cisco DNA provide the capability to send an HTTP _______________ request to the API endpoint https://DNA-c_API_ADDRESS/api/vi/network-device/ and receive the network __________ list in __________ format.
What are two roles of an artifact repository in a CI/CD pipeline? (Choose two.)
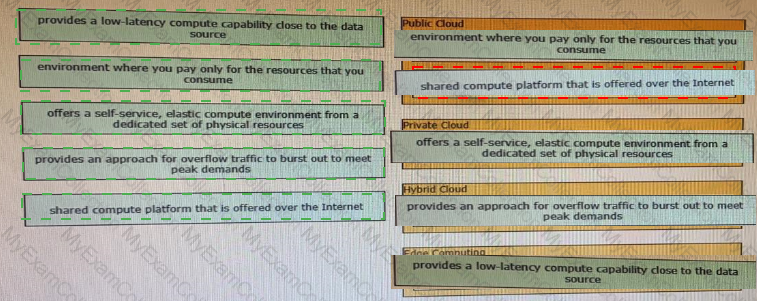
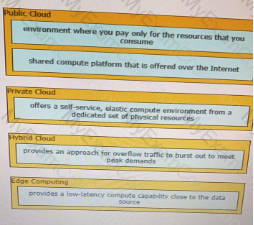
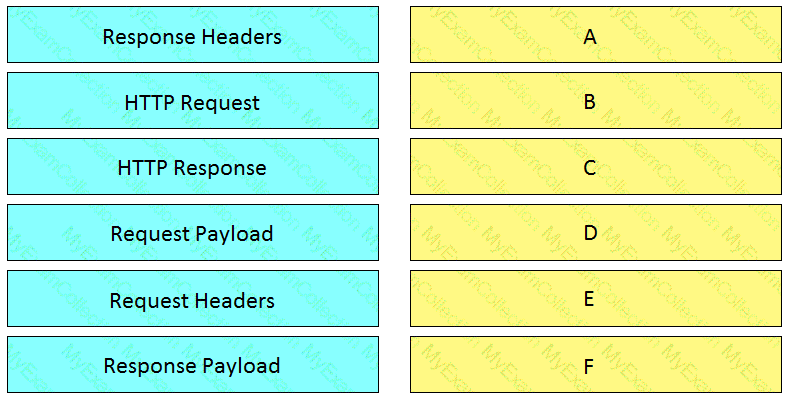
Drag and drop the descriptions from the left onto correct application deployment models on the right.
An application calls a REST API and expects a result set of more than 550 records, but each time the call is made, only 25 are returned. Which feature limits the amount of data that is returned by the API?
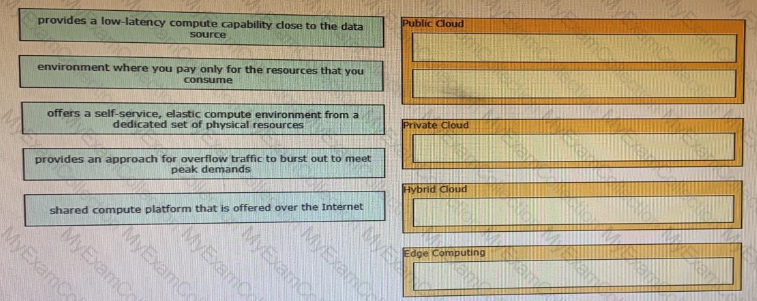
Refer to the exhibit.
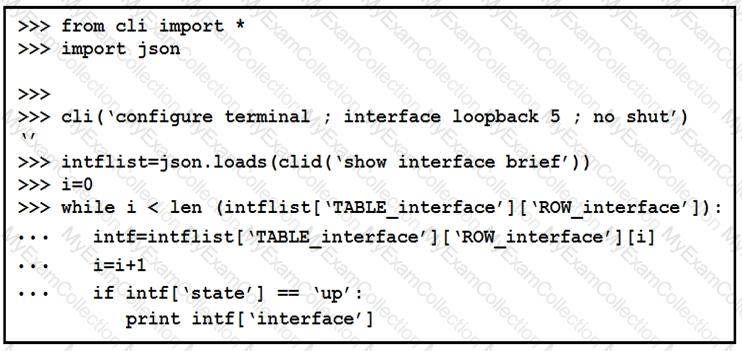
The python interpreter and the Cisco python SDK are available by default in the Cisco NX-OS software. The SDK documentation shows how the cild() API can be used when working with working with JSON and XML. What are two effect of running the script? (Choose two.)
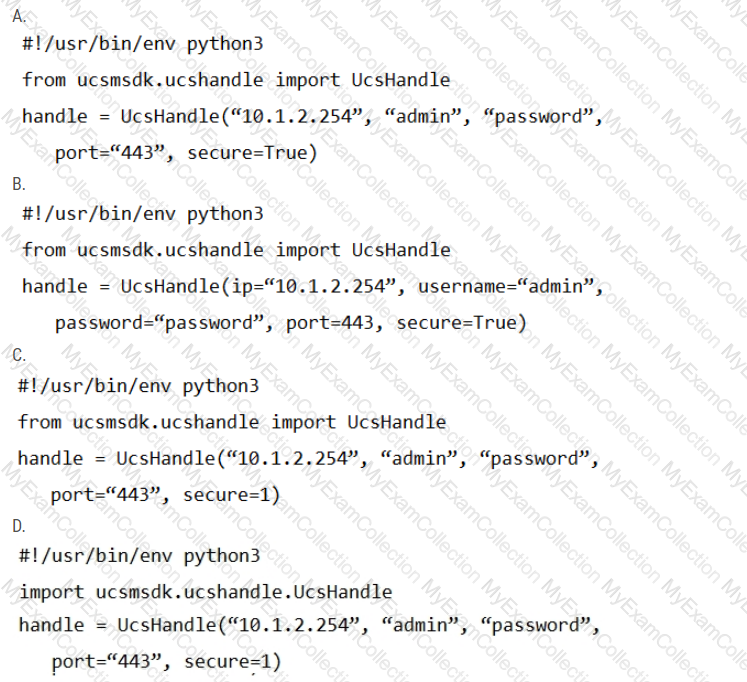
Refer to the exhibit.
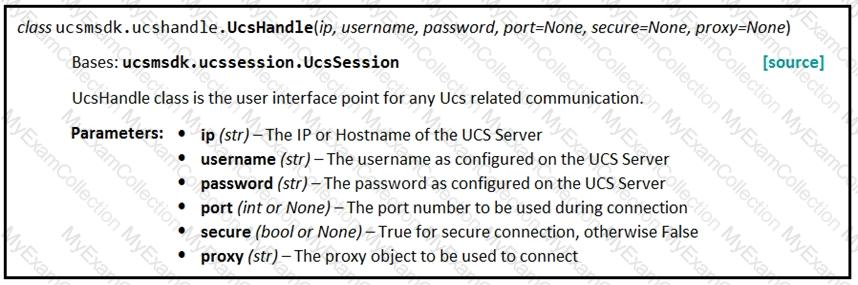
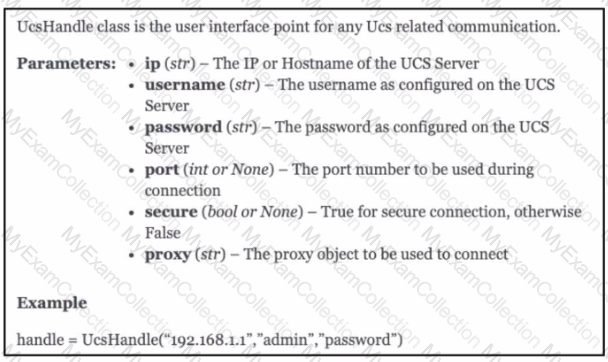
Given the API documentation for the UCS SDK python class, UcsHandle, which code snippet creates a handle instance?
Which statement about authentication a RESTCONF API session with a router that runs Cisco IOS XE software is true?