You have a Microsoft 365 subscription that uses Microsoft Defender for Cloud Apps and has Cloud Discovery enabled.
You need to enrich the Cloud Discovery data. The solution must ensure that usernames in the Cloud Discovery traffic logs are associated with the user principal name (UPN) of the corresponding Microsoft Entra ID user accounts.
What should you do first?
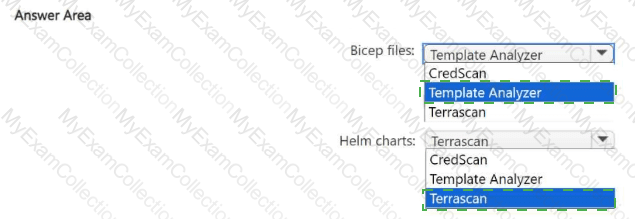
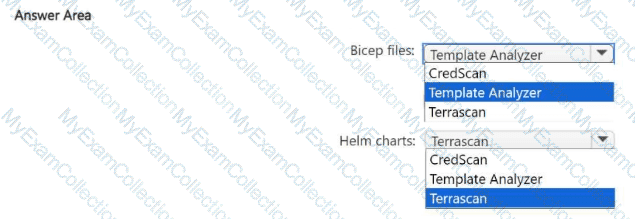
You have an Azure DevOps organization that contains an Azure Repos respository named Repo1 and is onboarded to Microsoft Defender for DevOps.
You create infrastructure as code (laC) files and store them in Repo1. The laC files are formatted as Bicep files and Helm charts.
You need to configure Defender for DevOps to identify misconfigurations in the laC files.
Which scanning tool should you use for each type of files? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You are configuring Azure Sentinel.
You need to create an incident in Azure Sentinel when a sign-in to an Azure virtual machine from a malicious IP address is detected.
Solution: You create a Microsoft incident creation rule for a data connector.
Does this meet the goal?
You have an Azure subscription that contains a user named User1 and a Microsoft Sentinel workspace named WS1. WS1 uses Microsoft Defender for Cloud.
You have the Microsoft security analytics rules shown in the following table.
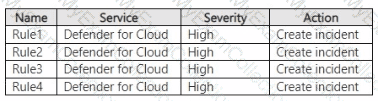
User1 performs an action that matches Rule1, Rule2, Rule3, and Rule4. How many incidents will be created in WS1?
You need to ensure that the Group1 members can meet the Microsoft Sentinel requirements.
Which role should you assign to Group1?
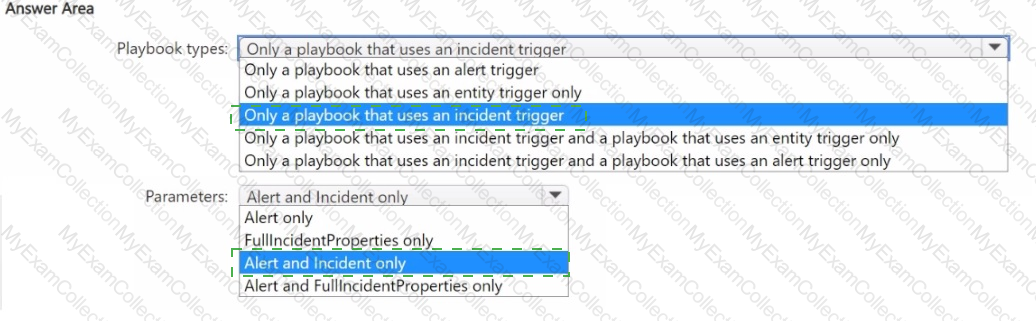
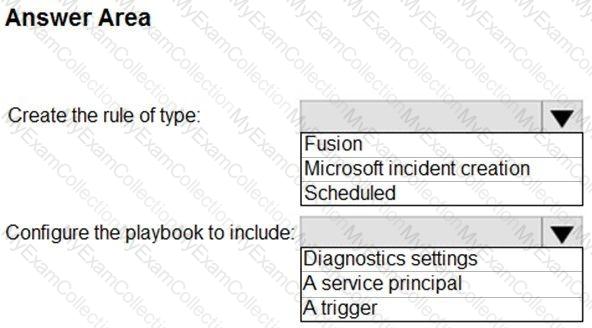
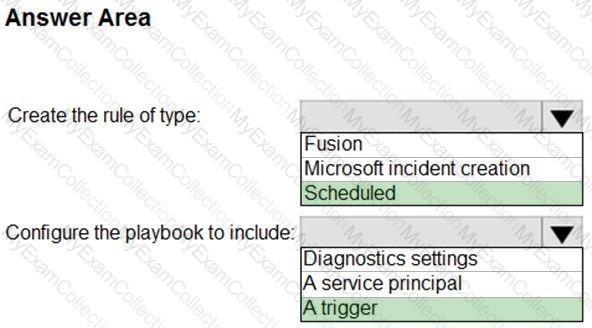
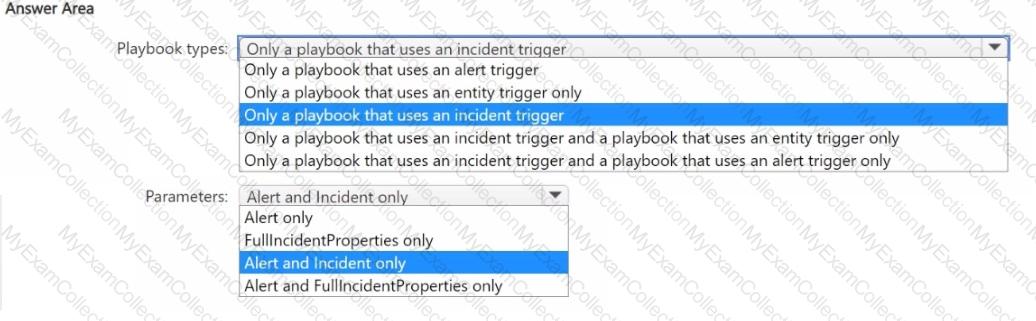
You have a Microsoft Sentinel workspace.
You need to create playbooks that meet the following requirements:
• Use an automation rule to trigger actions on an entity.
• Call the Entities - Get Hosts action.
Which types of playbooks should you use, and which parameters should you specify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to configure event monitoring for Server1. The solution must meet the Microsoft Sentinel requirements. What should you create first?
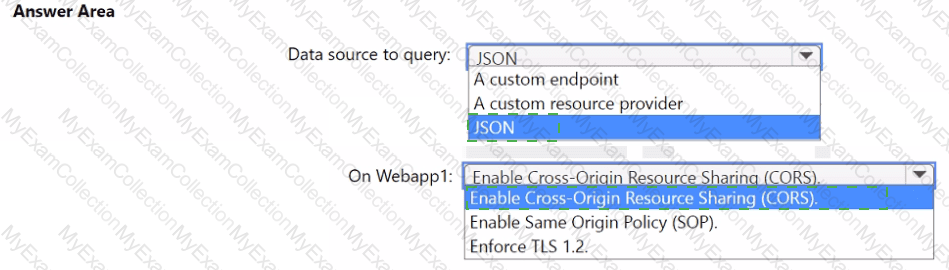
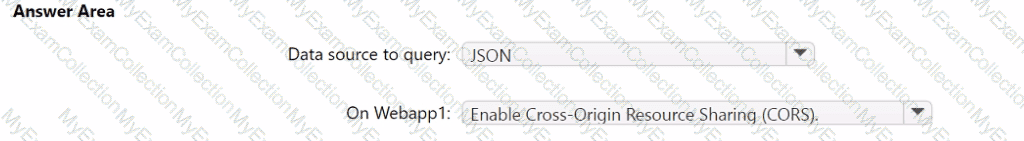
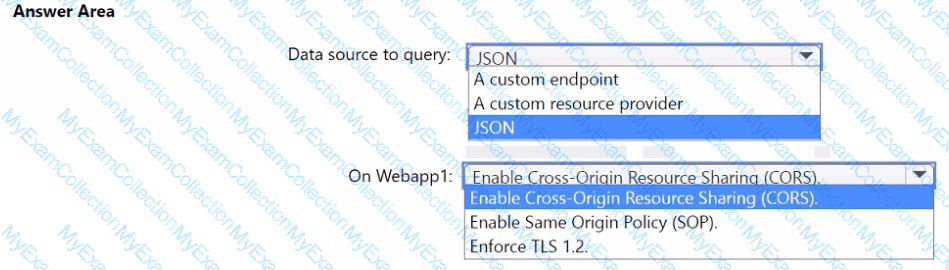
You need to implement the query for Workbook1 and Webapp1. The solution must meet the Microsoft Sentinel requirements. How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to ensure that the processing of incidents generated by rulequery1 meets the Microsoft Sentinel requirements.
What should you create first?
You need to implement the Defender for Cloud requirements.
What should you configure for Server2?
You need to implement the scheduled rule for incident generation based on rulequery1.
What should you configure first?
You need to implement the Defender for Cloud requirements.
Which subscription-level role should you assign to Group1?
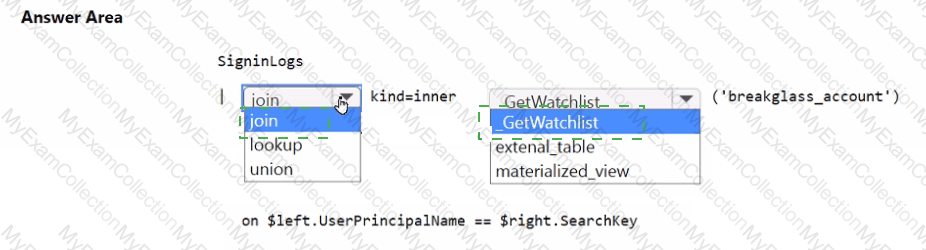
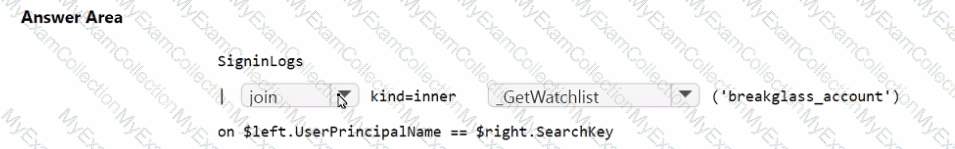
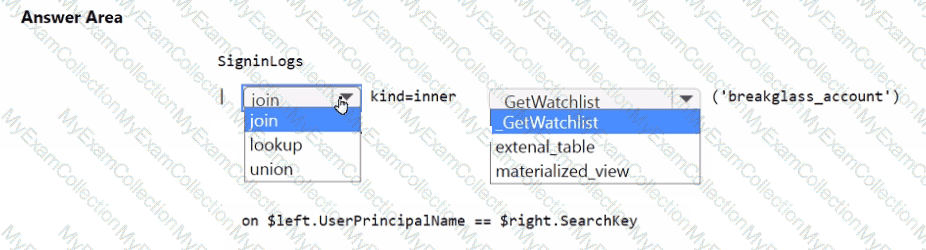
You need to implement the Microsoft Sentinel NRT rule for monitoring the designated break glass account. The solution must meet the Microsoft Sentinel requirements.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
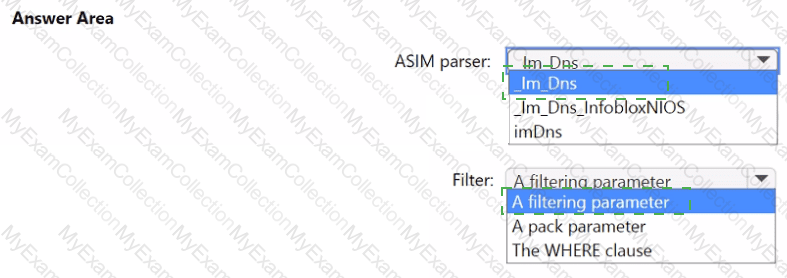
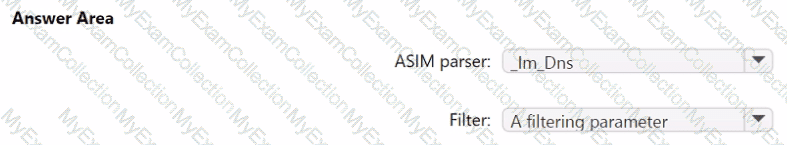
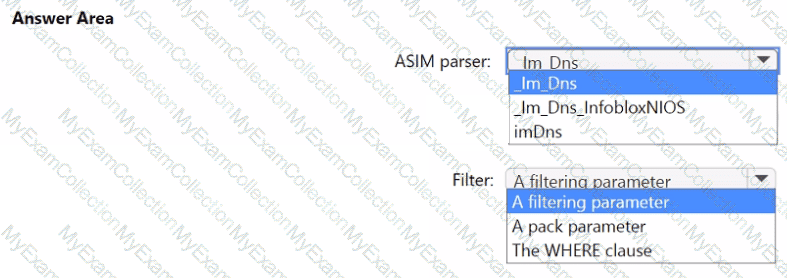
You need to implement the ASIM query for DNS requests. The solution must meet the Microsoft Sentinel requirements. How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
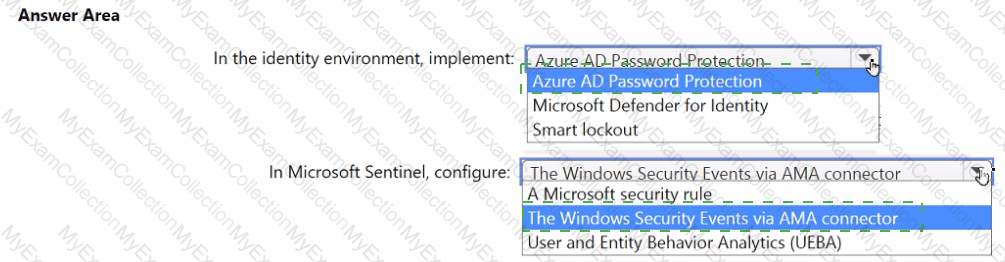
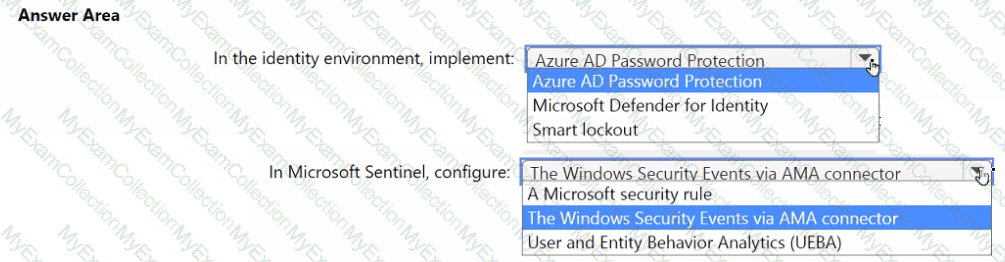
You need to monitor the password resets. The solution must meet the Microsoft Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to ensure that the configuration of HuntingQuery1 meets the Microsoft Sentinel requirements.
What should you do?
You have a Microsoft 365 subscription that uses Microsoft Defender XDR. Microsoft Purview, and Exchange Online.
You have a partner company named Contoso, Ltd.
You need to review all the emails that contain PDF attachments and were received from Contoso during the past month. The solution must minimize administrative effort.
What should you use?
You have an Azure subscription that contains a Log Analytics workspace named Workspace1.
You configure Azure activity logs and Microsoft Entra ID logs to be forwarded to Workspace1.
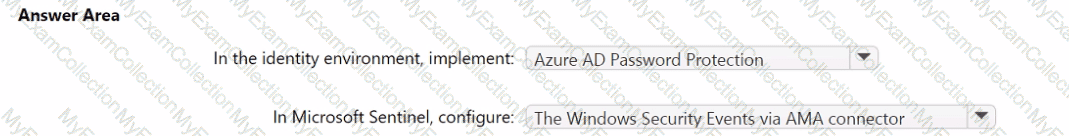
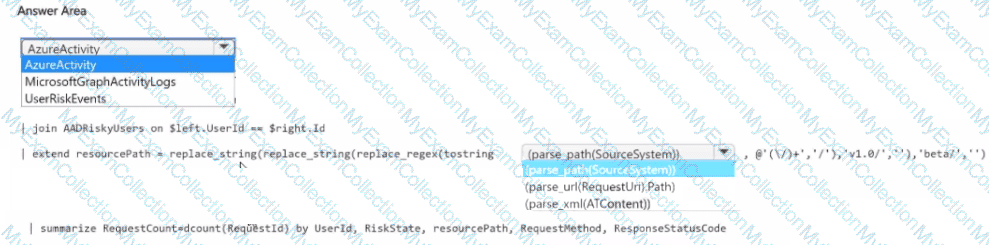
You need to identify which Azure resources have been queried or modified by risky users.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
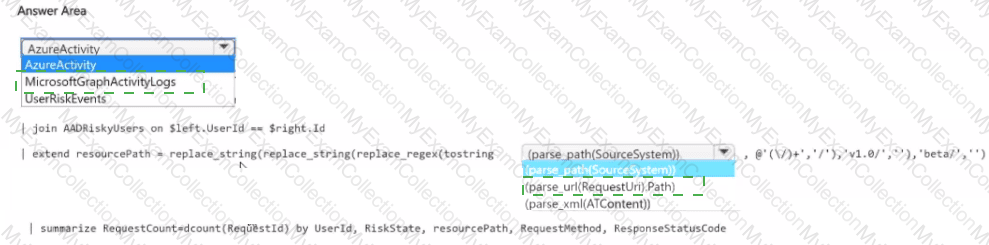
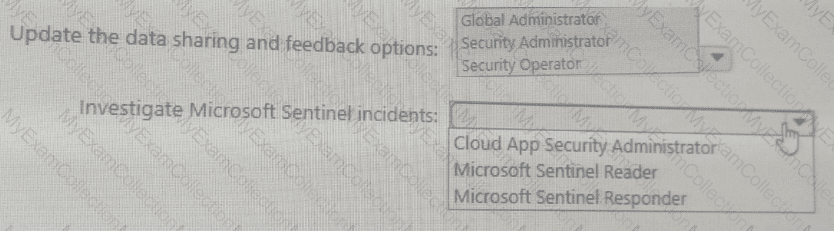
You have an Azure subscription named Sub1 that is linked to a Microsoft Entra tenant named contoso.com. Contoso.com contains a user named User1. Sub1 contains a Microsoft Sentinel workspace.
You provision a Microsoft Copilot for Security capacity.
You need to ensure that User1 can use Copilot for Security to perform the following tasks:
. Update the data sharing and feedback options.
. Investigate Microsoft Sentinel incidents.
The solution must follow the principle of least privilege.
Which role should you assign to User1 for each task? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point
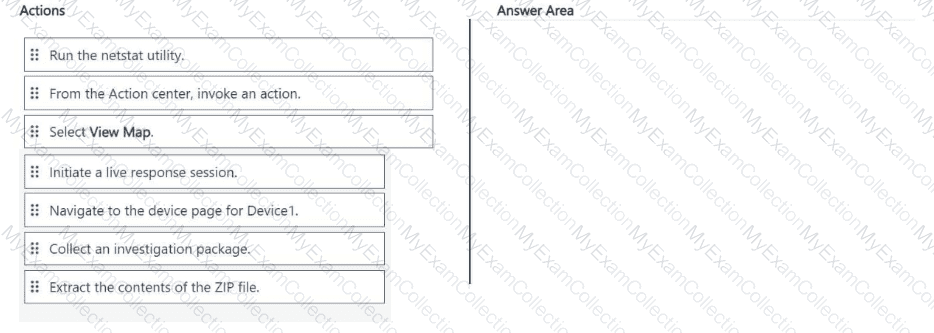
You have an on-premises Windows 11 Pro device named Device1 that is onboarded to Microsoft Defender for Endpoint
You have a Microsoft 365 subscription.
You need to identify the processes running on Device1 and which network connections the processes have open. The solution must minimize administrative effort.
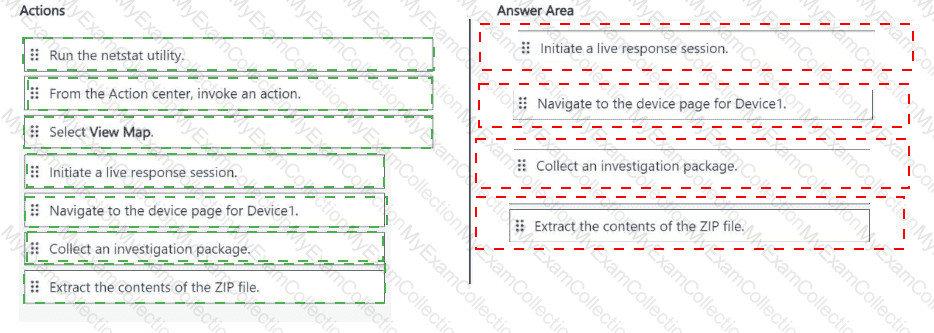
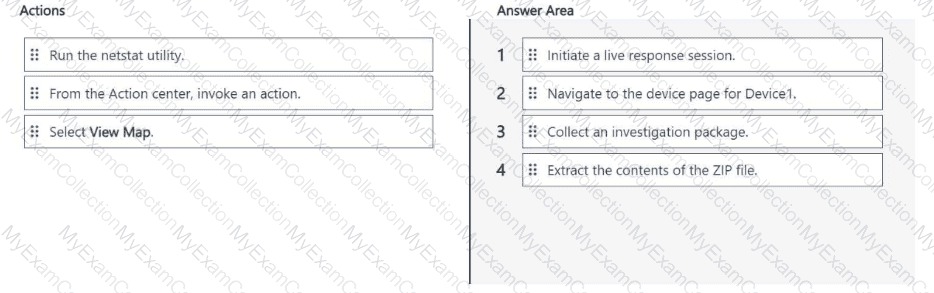
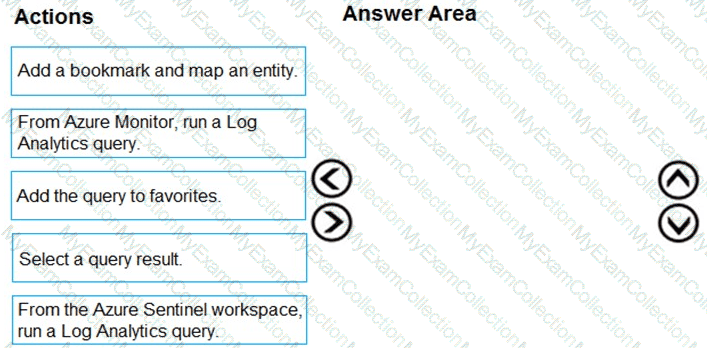
Which four actions should you perform in the Microsoft Defender portal in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
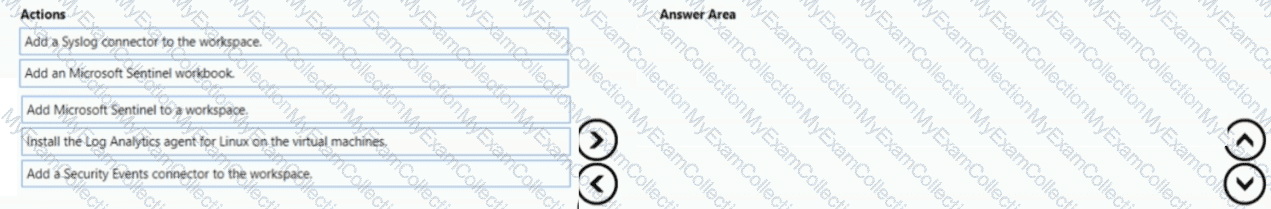
You have an Azure subscription that contains 100 Linux virtual machines.
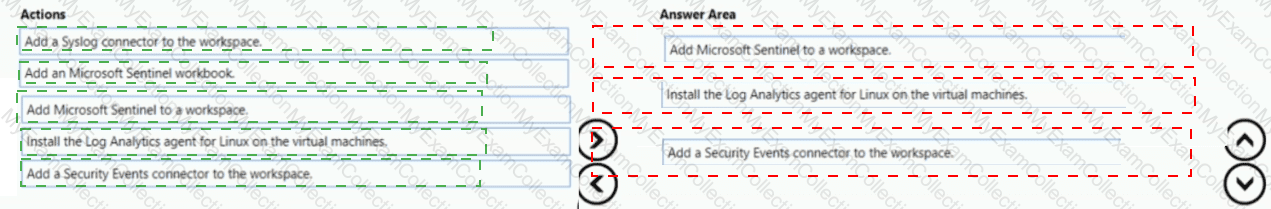
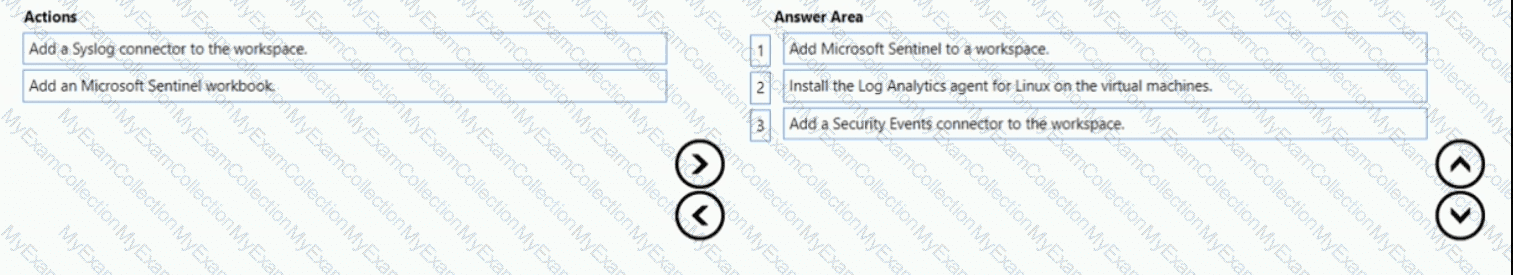
You need to configure Microsoft Sentinel to collect event logs from the virtual machines.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
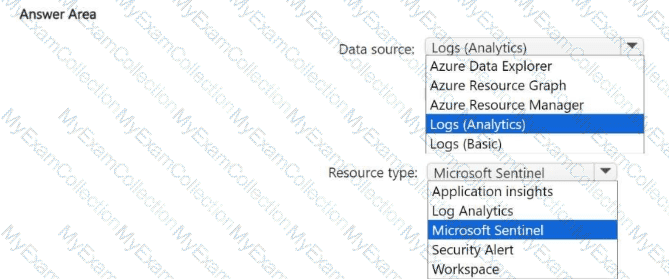
You have a Microsoft Sentinel workspace.
You have a KQL query. The query returns Microsoft Sentinel incidents that are stored in the Securitylncident table and occurred during the last 90 days.
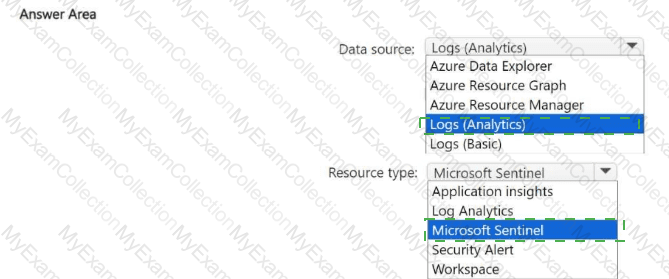
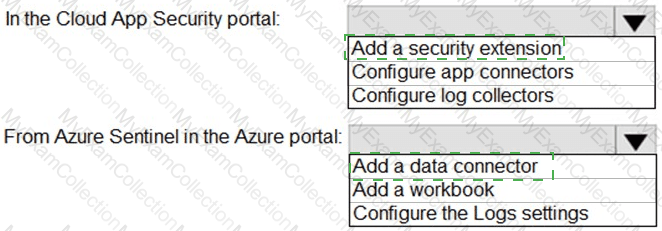
You need to create a Microsoft Sentinel workbook that will include a visualization of the query.
To what should you set Data source and Resource type for the workbook? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription that uses Microsoft 365 Defender.
You plan to create a hunting query from Microsoft Defender.
You need to create a custom tracked query that will be used to assess the threat status of the subscription.
From the Microsoft 365 Defender portal, which page should you use to create the query?
You have an on-premises network.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Identity.
From the Microsoft Defender portal, you investigate an incident on a device named Device1 of a user named User1. The incident contains the following Defender for Identity alert.
Suspected identity theft (pass-the-ticket) (external ID 2018)
You need to contain the incident without affecting users and devices. The solution must minimize administrative effort.
What should you do?
You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint Plan 2 and contains a Windows device named Device!.
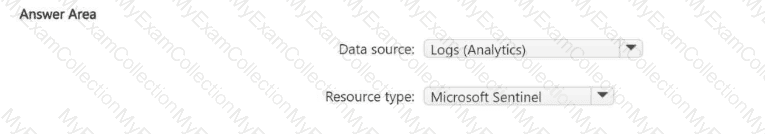
You initiated a live response session on Device1.
You need to run a command that will download a 250-MB file named File! .exe from the live response library to Device1. The solution must ensure that Filel.exe is downloaded as a background process.
How should you complete the live response command? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

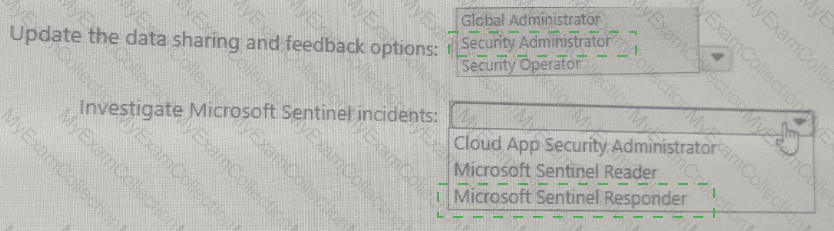
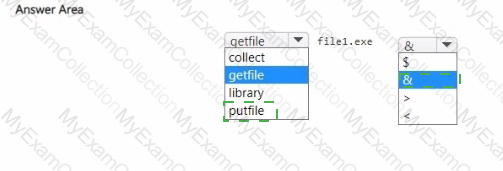
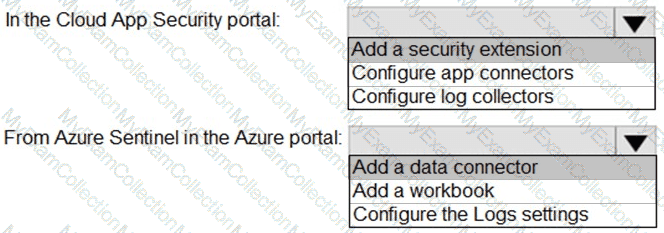
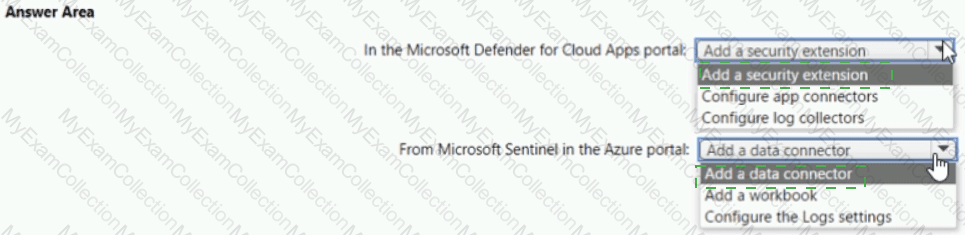
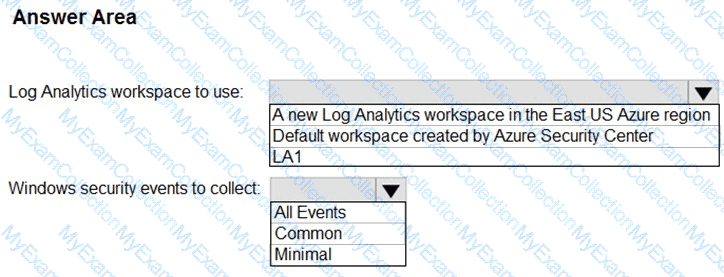
You need to configure the Azure Sentinel integration to meet the Azure Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
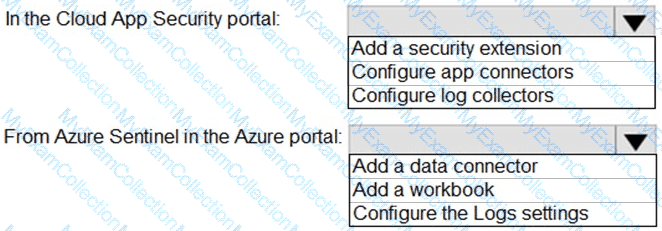
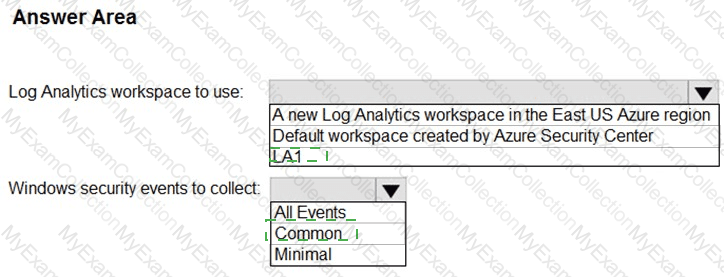
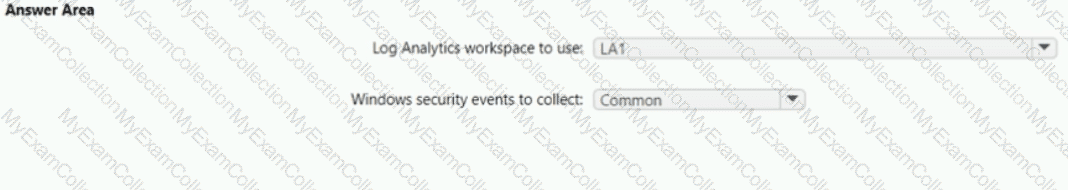
You need to configure the Microsoft Sentinel integration to meet the Microsoft Sentinel requirements. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
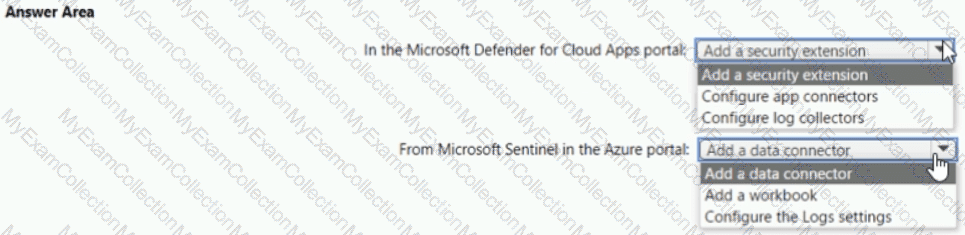
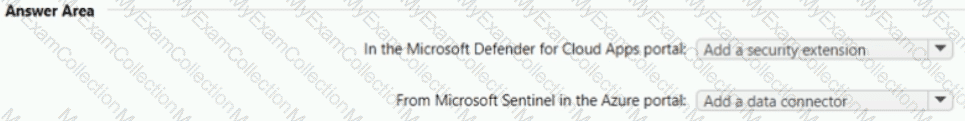
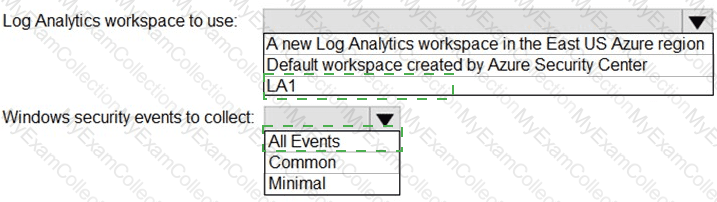
You need to implement Azure Defender to meet the Azure Defender requirements and the business requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to modify the anomaly detection policy settings to meet the Cloud App Security requirements. Which policy should you modify?
You need to create the test rule to meet the Azure Sentinel requirements. What should you do when you create the rule?
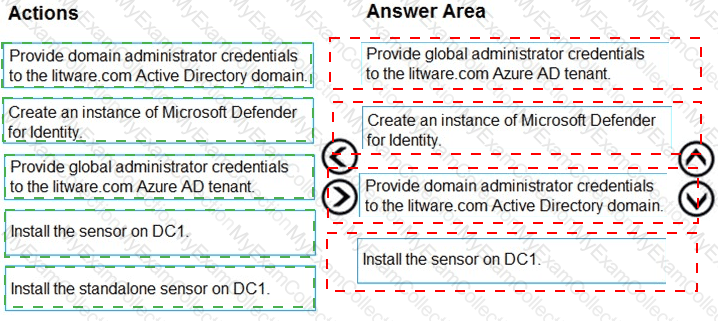
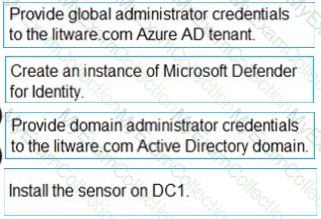
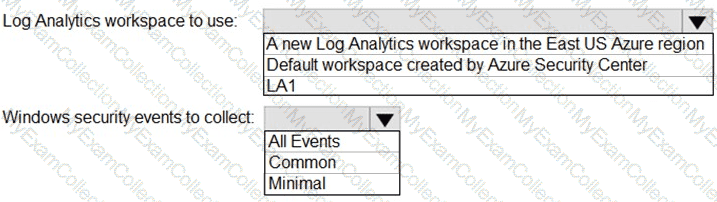
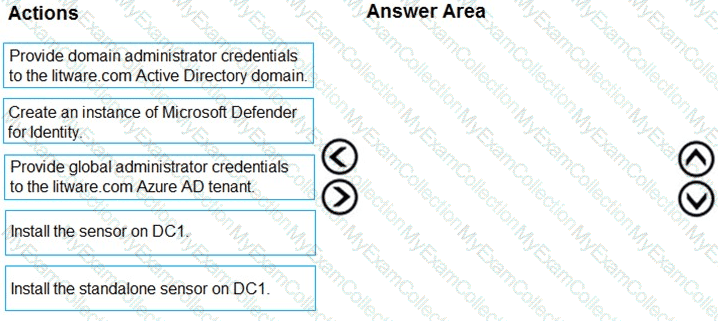
You need to configure DC1 to meet the business requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to restrict cloud apps running on CUENT1 to meet the Microsoft Defender for Endpoint requirements. Which two configurations should you modify? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
You need to implement the Azure Information Protection requirements. What should you configure first?
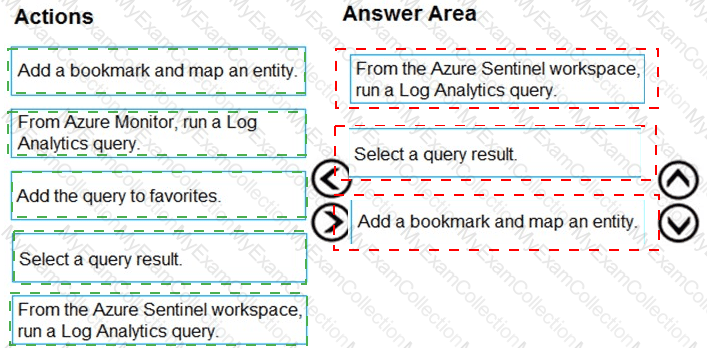
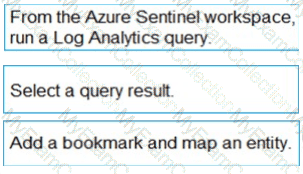
You need to add notes to the events to meet the Azure Sentinel requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of action to the answer area and arrange them in the correct order.
You need to assign a role-based access control (RBAC) role to admin1 to meet the Azure Sentinel requirements and the business requirements.
Which role should you assign?
You need to modify the anomaly detection policy settings to meet the Microsoft Defender for Cloud Apps requirements and resolve the reported problem.
Which policy should you modify?
You need to implement Microsoft Defender for Cloud to meet the Microsoft Defender for Cloud requirements and the business requirements. What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to restrict cloud apps running on CLIENT1 to meet the Microsoft Defender for Endpoint requirements.
Which two configurations should you modify? Each correct answer present part of the solution.
NOTE: Each correct selection is worth one point.
Which rule setting should you configure to meet the Microsoft Sentinel requirements?
The issue for which team can be resolved by using Microsoft Defender for Endpoint?
You need to complete the query for failed sign-ins to meet the technical requirements.
Where can you find the column name to complete the where clause?
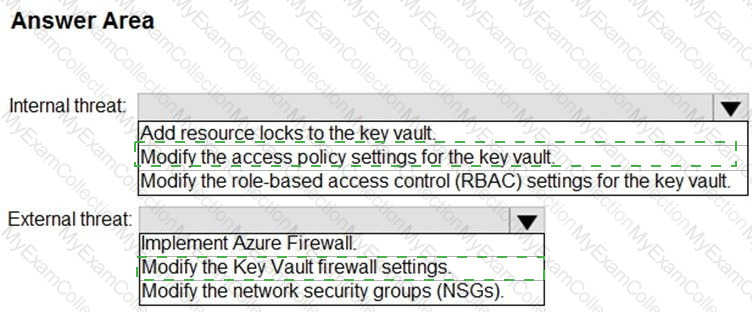
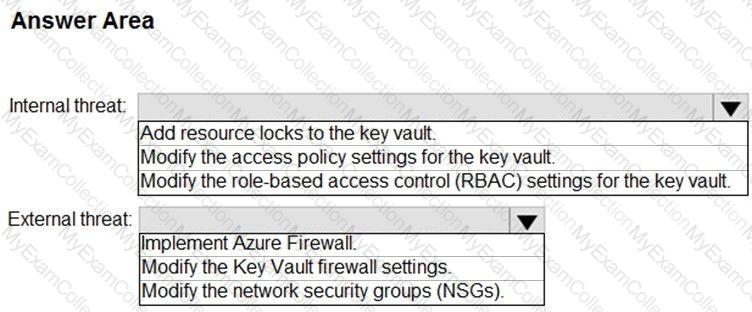
You need to recommend remediation actions for the Azure Defender alerts for Fabrikam.
What should you recommend for each threat? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
The issue for which team can be resolved by using Microsoft Defender for Office 365?
You need to recommend a solution to meet the technical requirements for the Azure virtual machines. What should you include in the recommendation?
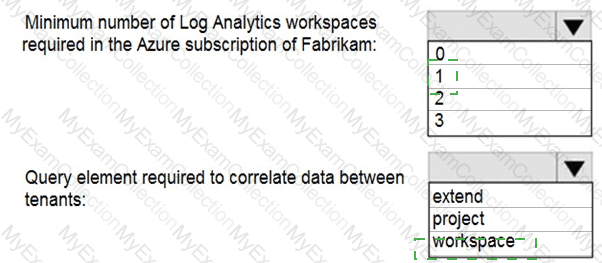
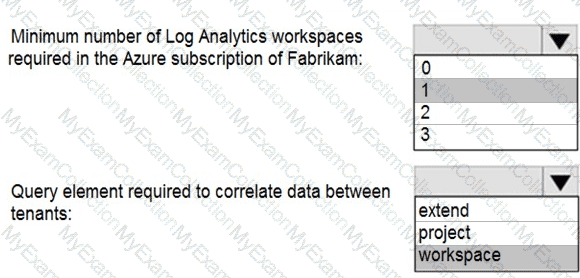
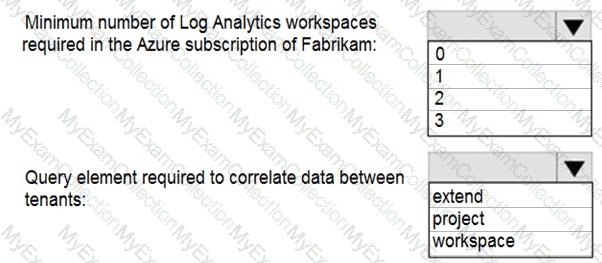
You need to implement Azure Sentinel queries for Contoso and Fabrikam to meet the technical requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
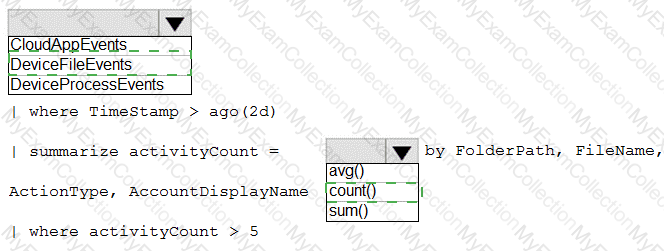
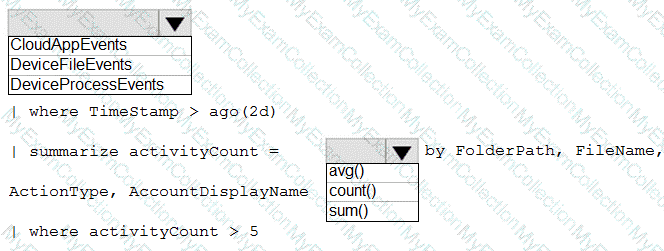
You need to create an advanced hunting query to investigate the executive team issue.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to remediate active attacks to meet the technical requirements.
What should you include in the solution?