Consider the following diagram using the Implementation and Migration extension:
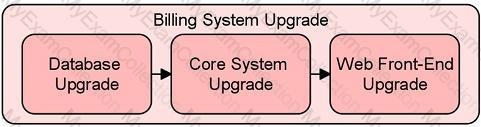
Which of the following statements correctly describes the concepts shown in the diagram?
Consider the following four diagrams:
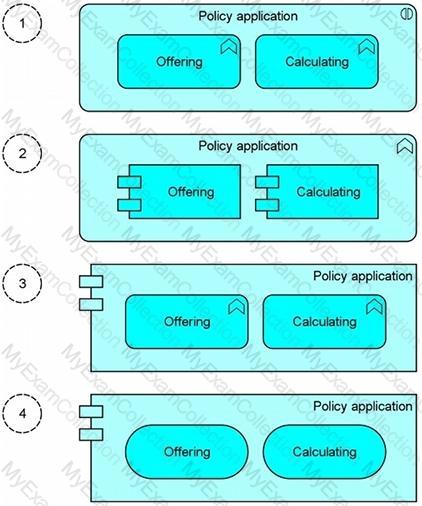
Which diagram depicts a “Policy application†as an application component with the two application functions “Offering†and “Calculating�
The ArchiMate modeling language can be used to describe different types of architecture and the relationships between them.
Which of the following lists the three main layers of the ArchiMate language?
Consider the following three graphical notations:

Which of the three graphical notations represent the concept of a network?
Consider the following diagram which shows the service Contracting that is delivered by the business process Close contract.
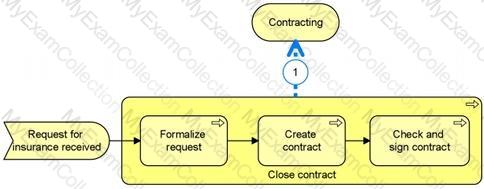
What is the most appropriate ArchiMate relationship to be used for (1)?
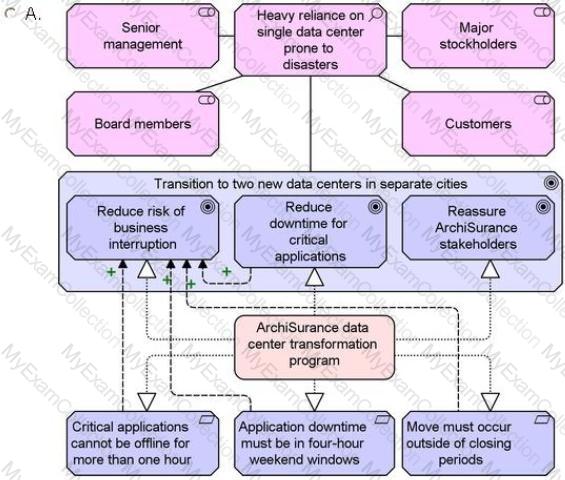
Scenario
Please read this scenario prior to answering the question
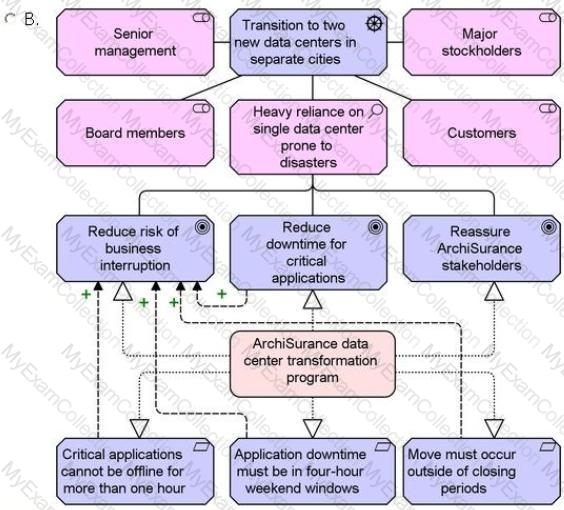
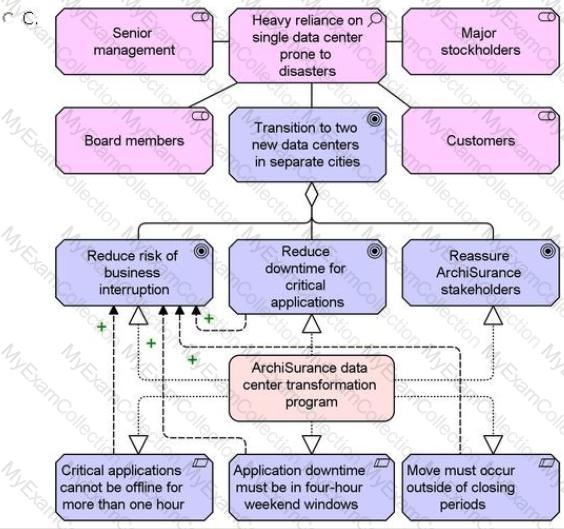
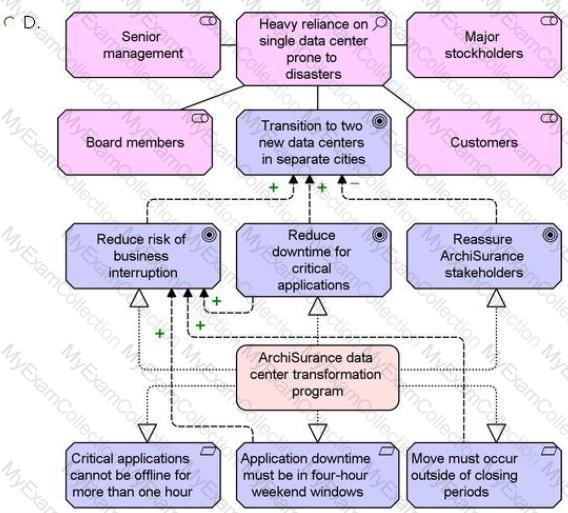
ArchiSurance senior management; board members, customers and major stockholders have long been concerned about disaster resiliency in light of the company's heavy reliance on a single data center. The data center is located in an area that is prone to flooding and earthquakes, according to expert assessments done by consultants retained for this purpose. In addition, the data center is located under a busy cafeteria, and water occasionally leaks through its ceiling.
To address these problems, ArchiSurance has developed a plan to move from its current data center to a pair of ready-to-use data centers in separate cities. The data center move is designed to reduce the risk of business interruption, reduce both planned and unplanned downtime for critical applications, and reassure ArchiSurance stakeholders. However, a number of limitations make the planned transition to the new data centers particularly challenging. A number of critical ArchiSurance applications cannot be offline for more than an hour, and any downtime for these application must only occur in certain four-hour windows each weekend. Also, the move cannot occur during quarterly or year-end closing periods in order to avoid interrupting critical processing. Fulfillment of these specific type of requirements will reduce the risk of business interruption from the data center move activities themselves.
ArchiSurance management has therefore planned a multi-phase data center transformation program. All of the activities in each phase are necessary to ensure a progression of stable and fully functional data center configurations. The first phase consists of detailed scheduling and planning to produce a comprehensive transformation plan that meets ArchiSurance timing and scheduling requirements. During the second phase, ArchiSurance is to contract for the hardware and software required for the new datacenters, as well for refunds for the hardware and software to be returned from the current data center once it is shut down. During the third phase, the new data centers are to be set up, and the new hardware and software are to be tested in parallel with what is already in production. The actual transition between the old and new data centers occurs in the fourth phase, and the fifth phase involves shutting down and dismantling the old data center, and returning its hardware and software for contracted refunds. Phases two through five are each to be initiated when specific conditions are met in the previous phase.
Refer to the Scenario
The head of IT has asked you to help her explain why ArchiSurance decided to transform its data center infrastructure. You must model the stakeholders, the motivations, and the influencing relationships between these motivations. You must also model the specific goals realized by the data center transformation program and the limitations within which this program must operate.
Which answer provides the best explanation?
Scenario
Please read this scenario prior to answering the question
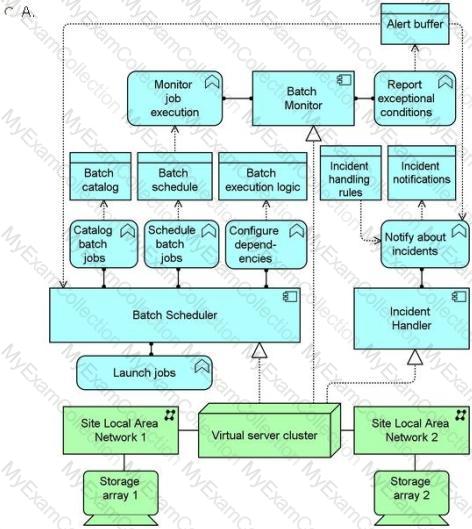
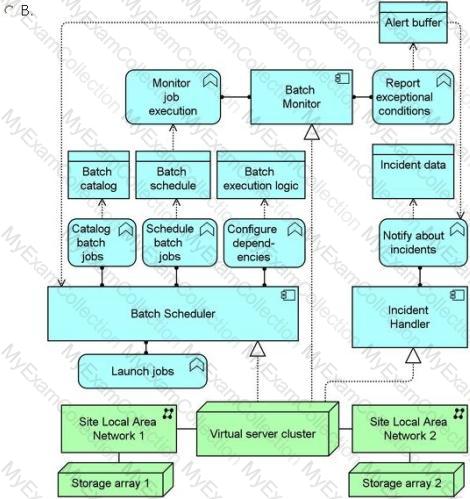
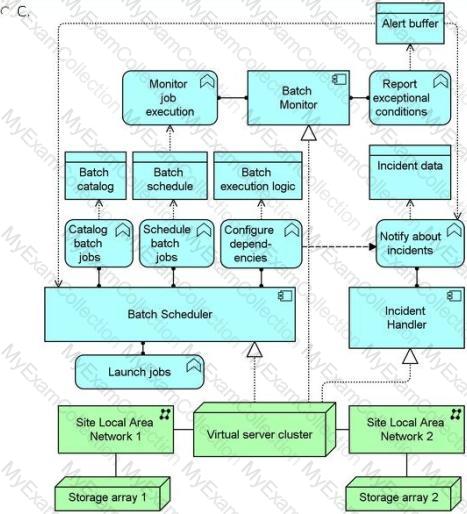
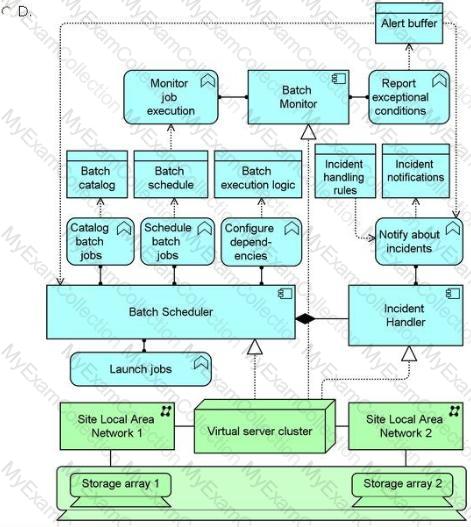
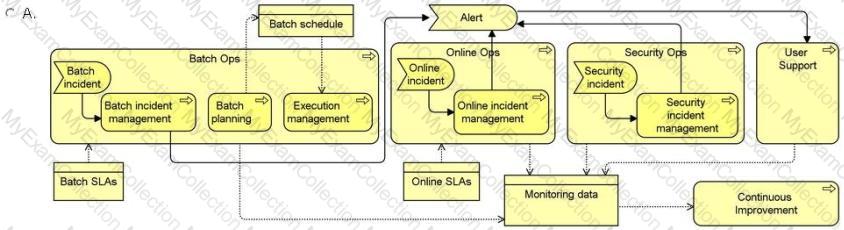
The ArchiSurance IT Operations (IT Ops) department has five core responsibilities, and continuously executes a core business process for each responsibility. (1) The Batch Ops process makes sure that batch jobs execute completely, successfully, and on time, consistent with their service level agreements (SLAs). (2) The Online Ops process makes sure that all web applications and content delivery services are available and performing according to their SLAs. (3) The Security Ops process protects ArchiSurance IT operations from being damaged by malicious or careless incidents. (4)The User Support process assists users of ArchiSurance systems with problems or requests. (5) The Continuous Improvement process monitors and measures the performance ot each of the other processes and works to solve problems and optimize use of ArchiSurance resources. In order to enable monitoring, each of the other processes generates monitoring data that is read by the Continuous Improvement process.
The processes in the System Ops category, which are Batch Ops, Online Ops and Security Ops, each have a separate sub-process for incident management. These sub-processes are triggered, respectively, by Batch, Online and Security Incidents. One of the first steps in each incident management sub-process, is to pass an Incident Alert to each of the other System Ops processes. This is accomplished by posting the alert to the Alert Buffer.
The Batch Ops process uses a schedule that lists all batch jobs and their dependencies. The schedule is used by two Batch Ops sub-processes. The Batch Planning sub-process updates this schedule for use by the Execution Management sub-process.
The Batch Ops process uses a number of applications that interact with each other. The Batch Scheduler application enables users to manage a database of jobs, job schedules and dependencies, and launches batch jobs according to the database. The Batch Monitor application uses the job schedules as a reference to monitor job execution, and reports all exceptional conditions to the both the Batch Scheduler and the Incident Handler applications via the Alert Buffer described earlier In the scenario. The Incident Handler refers to a set of business rules to determine the systems and individuals that must be notified of each incident. Based on these determinations, the Incident Handler produces appropriate notifications.
Due to their critical ity, the Batch Scheduler, Batch Monitor and Incident Handler applications are hosted redundantly in multiple geographically distributed data centers. In each data center, the three applications are hosted on a fully redundant virtual server cluster. Each cluster is connected to two site local area networks, each of which connects to a separate physical storage array.
Refer to the scenario
As part of an IT service management initiative, you have been asked to show how applications and infrastructure support the Batch Ops process. Model the applications, their functions, the data they access, and the infrastructure that hosts the applications and data, along with the networks that connect the servers. It is only necessary to model a single data center.
Which answer provides the most complete and accurate model?
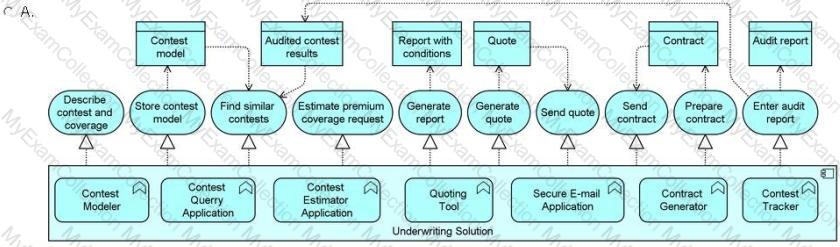
Scenario
Please read this scenario prior to answering the question
ArchiSurance has entered into a legal agreement to acquire ArchiSpecialty, a specialty insurer that has several lines of business, including insuring organizations that conduct high-stakes contests. Prior to entering into this agreement ArchiSurance staff carefully examined the ArchiSpecialty Enterprise Architecture to develop an integration plan with four successive phases. Each phase of the plan provides a stable foundation for ArchiSurance to conduct its newly expanded business while making significant progress toward the targeted integration of ArchiSpecialty operations. The first phase of the plan, Common Ownership, will begin on the acquisition date specified in the legal agreement. The second through fourth phases will begin after their predecessors are complete.
During the Common Ownership phase, the two companies' websites will be linked to each other and their Interactive voice response(IVR) system menus will be integrated. During the second phase, known as Integrated Organizations, the corresponding ArchiSurance and ArchiSpecialty departments will be combined and all financial processing will be migrated to the original ArchiSurance systems. In the third Phase, known as Integrated Customer Operations, ArchiSpecialty customer relationship management (CRM) data will be migrated to the corresponding ArchiSurance applications. In the fourth and final phase, known as Integrated Operations, the ArchiSpecialty claims data will be migrated to the corresponding ArchiSurance applications. However, the ArchiSpecialty underwriting solution for high-stakes contests will be retained due to its unique capabilities.
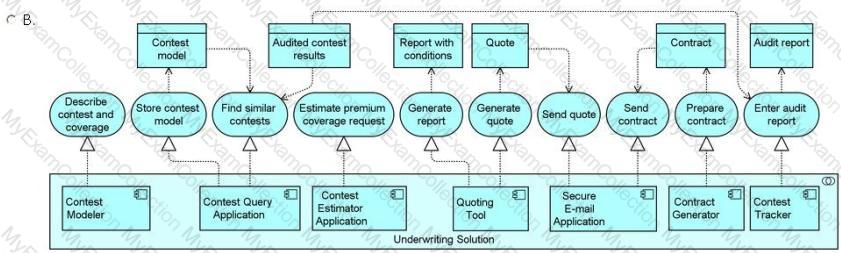
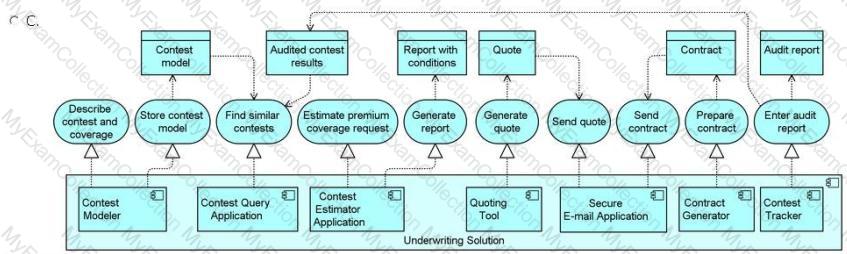
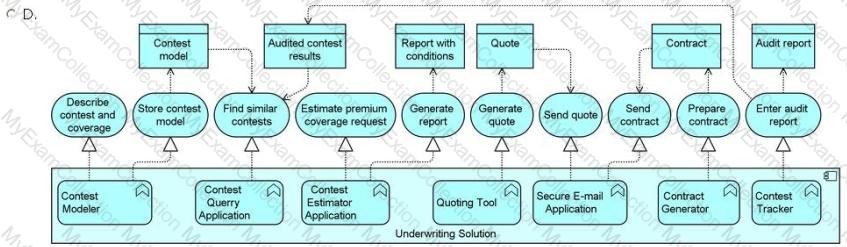
The underwriting solution for high-stakes contests assists underwriters in creating a policy to insure against the possibility of a contestant winning an improbable but expensive award, such as $1 million US for hitting a hole-in-one on a golf course, or a luxury world cruise for a winning spin of a roulette wheel. In return for a single premium payment, the insurer agrees to pay the award if a contestant earns it fairly. When an underwriter receives a request for an insurance quote, either from a promotions company that isplanning the contest or from a company with its own promotions department, he uses the Contest Modeler application to precisely describe the planned contest and the coverage requested, and to store the contest model in a machine-readable format. Then, the underwriter uses the Contest Query application, which reads the contest model and queries a collection of audited contest results to find records of similar contests. Then, the underwriter uses the Contest Estimator application to estimate the premium for the coverage request, and also to produce a report with a recommended set of conditions to provide with the quote. After consulting the report, the underwriter uses the Quoting Tool application to prepare a quote for the customer. Then, the underwriter sends the quote to the customer via secure email. If the customer accepts the quote, the underwriter uses the Contract Generator to prepare t contract for the customer, which he also sends via secure email. In the contract, the customer agrees to employ a contest auditorwho will report the audited results of the contest regardless of whether prizes are awarded. The underwriter uses the Contest Tracker application to add these reports to the collection of audited contest results. Note that all reports are delivered in a standard markup language that can be read by other software programs and either processed in the background or rendered visually.
Refer to the Scenario
The ArchiSurance chief information officer has asked you to explain the unique suite of applications that ArchiSpecialty uses to underwrite high-stakes contest insurance. You must model these applications, the services they provide and the data they access.
Which answer provides the best explanation?
Scenario
Please read this scenario prior to answering the question
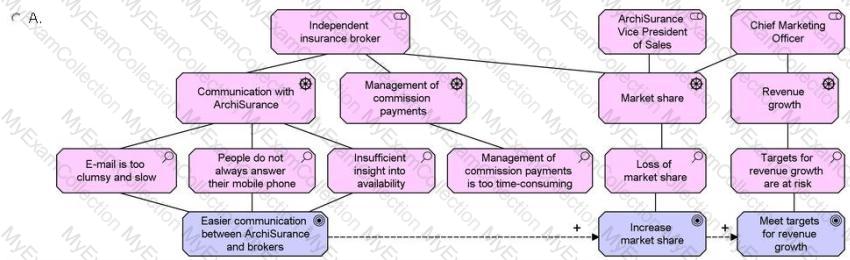
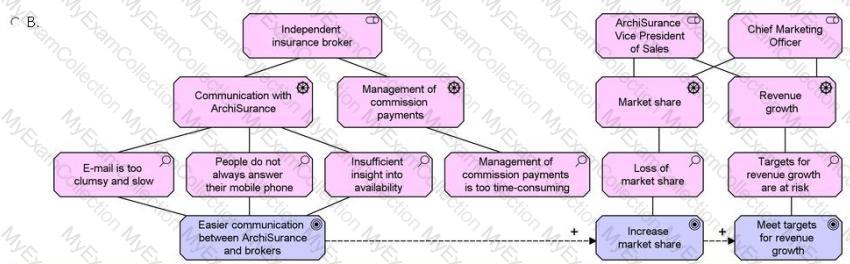
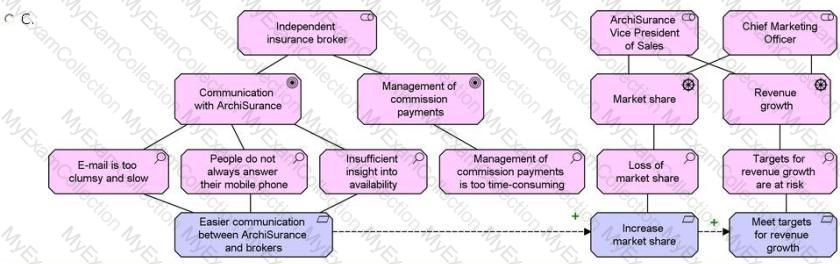
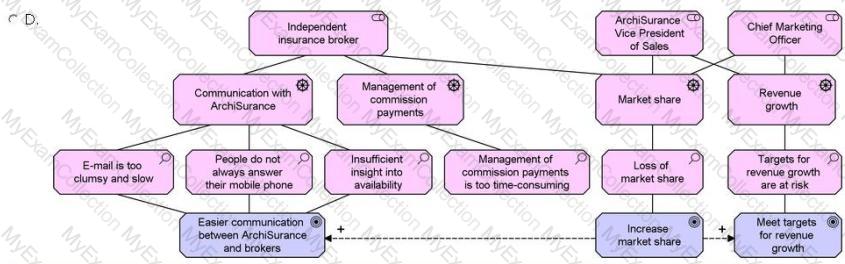
Independent insurance brokers that work with ArchiSurance have complained of difficulty in communicating with salespeople and other personnel at ArchiSurance. They have said that email is too clumsy and slow for working on urgent deals, people do not always answer their mobile phones, and it is difficult to tell whether an individual is available. They have also complained that it is too time-consuming for them to manage their commission payments using an older web application that requires them to print out and mail forms for making some routine changes, and also does not work on many mobile devices. Some brokers have said that it is easier to do business with ArchiSurance competitors that provide easy-to-use mobile applications for both general communication and commission management. In fact, the ArchiSurance Vice President of Sales and Chief Marketing Officer have both expressed concern about reports from the ArchiSurance market research department that the company is gradually losing market share withsome of the same brokers that have been complaining. These executives are also concerned that ArchiSurance may not meet the targets for revenue growth.
Upon hearing about these issues, the ArchiSurance Chief Information Officer (CIO) hired a consultant to design a new mobile infrastructure for broker interaction. This infrastructure is required to enable easier communication with ArchiSurance brokers in order to help the company increase its market share with each of them and consequently attain its targets for revenue growth. In order to ensure that the new infrastructure would meet these goals, the CIO told the consultant that the new infrastructure must make it easy for ArchiSurance to develop and deploy applications and content for its brokers. It must provide federated authentication and an encrypted communication channel as well as instant messaging and presence services.
The new mobile broker interaction infrastructure architecture includes a number of system software components. A secure reverse proxy authenticates users and provides an encrypted channel to communicate with them. The proxy uses a service provided by directory server software to authenticate users. The directory server communicates with the ArchiSurance federation server, which in turn communicates with peer federation servers hosted by trusted brokerage organizations. Once the user is authenticated, the ArchiSurance broker portal uses the ArchiSurance web content management system to assemble authorized and relevant content for each broker. In order to provide presence services, a unified communications (UC) server exchanges information with the directory server and an instant messaging server.
All of these components are hosted on a single physical hardware platform hosting a virtualized server infrastructure. The server infrastructure is connected to a converged local area network (LAN), which is also connected to a commercial wide area network (WAN) over which ArchiSurance communicates with its brokers.
Refer to the Scenario
The solution delivery team for broker interaction would like to get a clearer idea of the motivations behind this solution as they plan a second release. You must model the stakeholders, drivers, assessments and goals that shape this strategic initiative. You must also show the relationships between these motivational elements.
Which answer provides the most complete and accurate model?
Scenario
Please read this scenario prior to answering the question
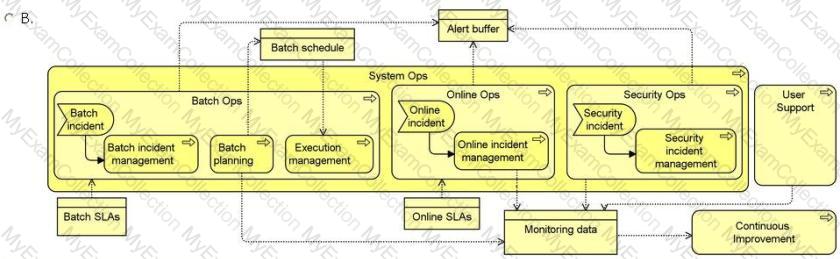
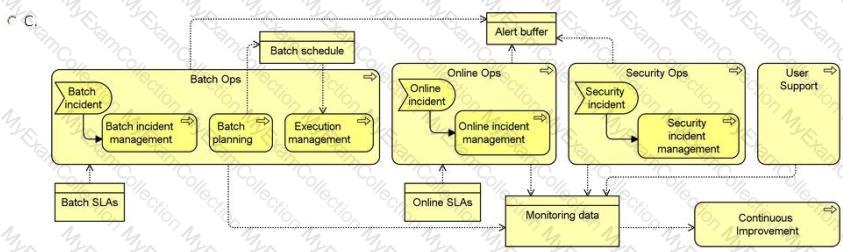
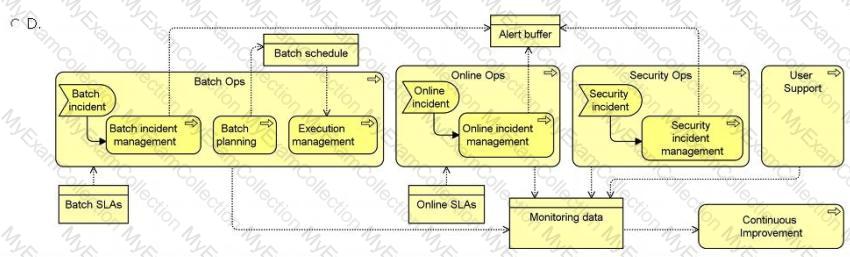
The ArchiSurance IT Operations (IT Ops) department has five core responsibilities, and continuously executes a core business process for each responsibility. (1) The Batch Ops process makes sure that batch jobs execute completely, successfully, and on time, consistent with their service level agreements (SLAs). (2) The Online Ops process makes sure that all web applications and content delivery services are available and performing according to their SLAs. (3) The Security Ops process protects ArchiSurance IT operations from being damaged by malicious or careless incidents. (4)The User Support process assists users of ArchiSurance systems with problems or requests. (5) The Continuous Improvement process monitors and measures the performance of each of the other processes and works to solve problems and optimize use of ArchiSurance resources. In order to enable monitoring, each of the other processes generates monitoring data that is read by the Continuous Improvement process.
The processes in the System Ops category, which are Batch Ops, Online Ops and Security Qds, each have a separate sub-process for incident management. These sub-processes are triggered, respectively, by Batch, Online and Security Incidents. One of the first steps in each incident management sub-process, is to pass an Incident Alert to each of the other System Ops processes. This is accomplished by posting the alert to the Alert Buffer.
The Batch Ops process uses a schedule that lists all batch jobs and their dependencies. The schedule is used by two Batch Ops sub-processes. The Batch Planning sub-process updates this schedule for use by the Execution Management sub-process.
The Batch Ops process uses a number of applications that interact with each other. The Batch Scheduler application enables users to manage a database of jobs, job schedules and dependencies, and launches batch jobs according to the database. The Batch Monitor application uses the job schedules as a reference to monitor job execution, and reports all exceptional conditions to the both the Batch Scheduler and the Incident Handler applications via the Alert Buffer described earlier in the scenario. The Incident Handlerrefers to a set of business rules to determine the systems and individuals that must be notified of each incident. Based on these determinations, the Incident Handler produces appropriate notifications.
Due to their criticality, the Batch Scheduler, Batch Monitor and Incident Handler applications are hosted redundantly in multiple geographically distributed data centers. In each data center, the three applications are hosted on a fully redundant virtual server cluster. Each cluster is connected to two site local area networks, each of which connects to a separate physical storage array.
Refer to the scenario
As part of an IT service management initiative, you have been asked to model the operations management business processes and sub-processes, including their relationships, the events that trigger them and the information they exchange.
Which answer provides the most complete and accurate model?
Scenario
Please read this scenario prior to answering the Question
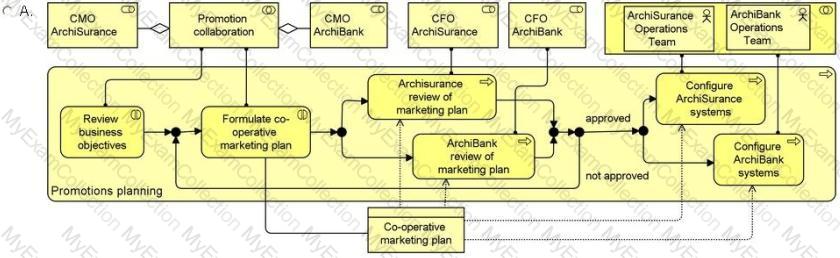
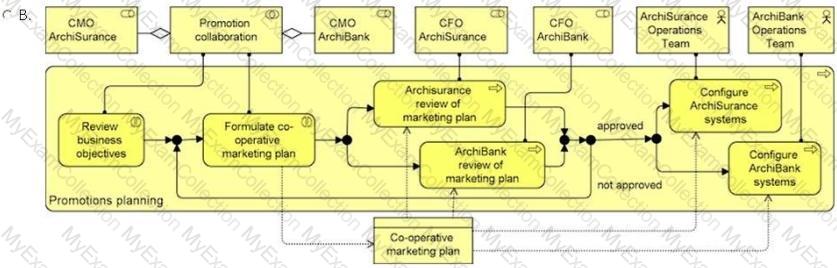
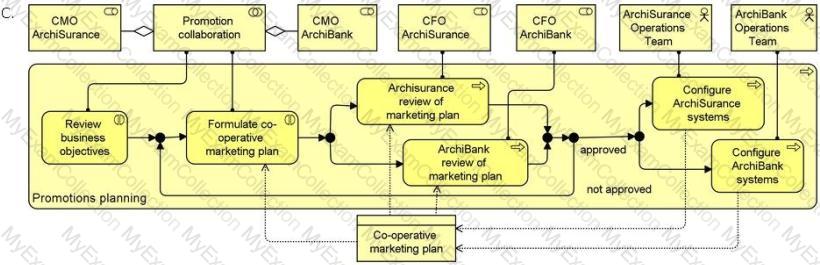
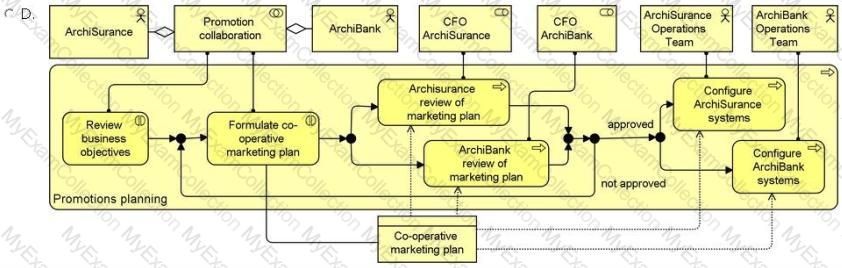
ArchiSurance has a partnership with ArchiBank in which the two companies market each other's consumer offerings to their own customers. Each quarter, the chief marketing officers (CMOs) of the two companies work together to plan the next quarter's promotions. First, they review each other's business objectives related to the partnership. Then, they formulate the co-operative marketing plan. The CMOs determine which offerings they will promote, the characteristics of the target customers, and the timing of each promotion. They assemble their findings into a co-operative marketing plan that is reviewed separately by the chief financial officer (CFO) of each organization. If either of the CFOs finds a problem, the CMOs must quickly work together to formulate another version of the plan. The review and reformulation process continues until both CFOs have approved a version of the plan. Then, the CMOs share the plans with their respective operations teams. Each organization's operations team configures the bank's systems to execute the joint promotions.
The cooperative marketing process is enabled by CRM software delivered as a service (SaaS). The two organizations each use separate logical instances of a multi-tenant customer relationship management (CRM) application hosted by a service provider. Each company's CRM instance is a dedicated function of the same CRM application component. The dedicated functions also share the same multi-tenant database. The component's data access layer is designed with safeguards to keep each company's data separate unless it is intentionally shared.
Each CRM instance has targeting, exchange and outreach sub-functions. The targeting sub-functions select customers based on criteria developed by the CMOs and configured by the operations teams. The exchange sub-functions share the selected customer profiles with each other, and the outreach sub-functions generate promotional email. In this way, each company's CRM system generates a list of target customers that the other company's CRM system uses to send promotional email.
The multi-tenant CRM application component is hosted on a large virtual server complex that is connected via a site network to a physical storage array and a commercial wide-area network (WAN) used by both companies. Both companies access their CRM systems via PCs connected to Local Area Networks (LANs) that are in turn connected to the shared commercial WAN.
Refer to the Scenario
In preparation for a presentation to investors, the ArchiSurance chief financial officer has asked you to model the business architecture of the partnership, including the executives and teams involved, the information they exchange, and the activities they perform.
Which answer best describes this business architecture?
Scenario
Please read this scenario prior to answering the question
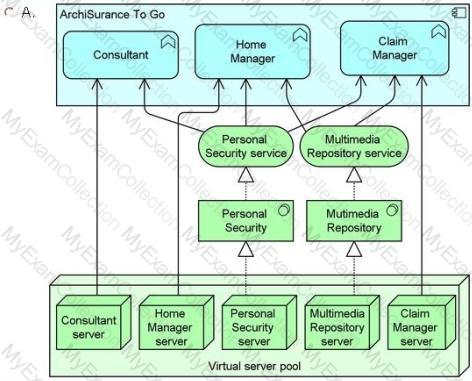
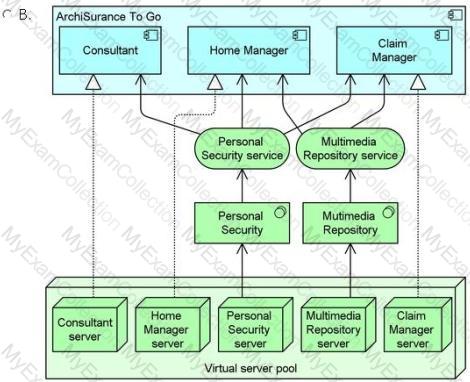
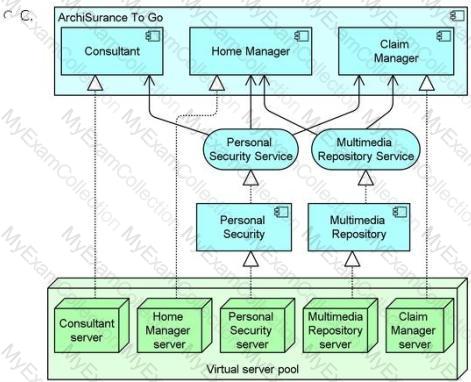
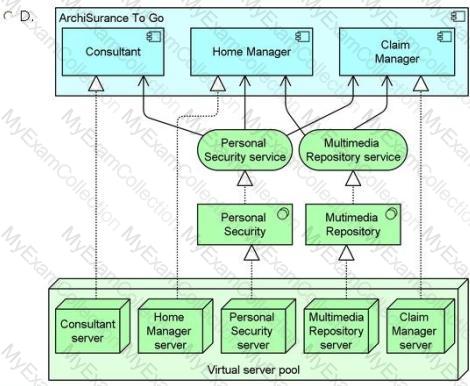
The ArchiSuranceTo Go mobile consumer solution is increasingly important to ArchiSurance, which uses it to sell and renew insurance products, provide customer service, enable accurate and convenient home recordkeeping, and capture and process claims. The solution consists of three components. The Consultant lets customers review their existing coverage, and update it based on common life events, such as getting a new car, moving into a new home, or having a family member move in or out. If necessary, they can speak or chat with a customer service representative. The Home Manager helps customers photograph and catalogue their valuable possessions in order to support the filing of accurate claims in case of loss or damage. The Claim Manager enables customers to quickly file a claim for loss or damage to an insured auto, home or possession. It enables customers to describe the incident by referencing information captured with the Consultant and the Home Manager applications. In addition, it allows the customer to add photographs, audio, video and text to support a claim, submit the claim, and monitor its progress.
The ArchiSurancetoGo components rely on a number of application services hosted by ArchiSurance. The first is an Auto Identification and Description (AID) service that the Consultant uses to validate and complete auto information entered by customers. The second service, Home Identification and Description (HID) performs the same function for home information, and is used by the Home Manager. The Consultant also uses the Virtual Agent service to guide customers as they select coverage options, the Payment Processor service to arrange premium payments, and the Coverage Activator service to generate policies and put them in force.
ArchiSurance to Go also relies on a number of infrastructure services. The Home Manager uses a Multimedia Repository service to store and retrieve information about insured homes. The Claim Manager also uses this service for claim information entered by customers. All three components of ArchiSuranceTo Go use a Personal Security service to register and authenticate customers, and to manage their profiles.
Each application service is realized by an application component with the same name. Also, each infrastructure service is realized by a system software environment with the same name. ArchiSurance hosts both the application components and system software environments in a virtual ized server pool within its data center. Each service has its own virtual server. Each server is connected to a data center network (DCN) which in turn connects to a commercial wide area network (WAN).
Refer to the Scenario
The new head of IT infrastructure would like a better understanding of the applications used by ArchiSurance to Go mobile solution and the hosting infrastructure that supports these applications.
Which answer provides the best description of the applications and their underlying infrastructure? (Please note that it is not necessary to model the networks).