You are onboarding an agentless, secure web gateway (SWG) endpoint for secure internet access (SIA). What will happen to the user ' s nonweb traffic? (Choose one answer)
Refer to the exhibit.

FortiGate has two separate firewall policies for Sales and Engineering to access the same web server with the same security profiles.
Which action must the administrator perform to consolidate the two policies into one?
Refer to the exhibit.
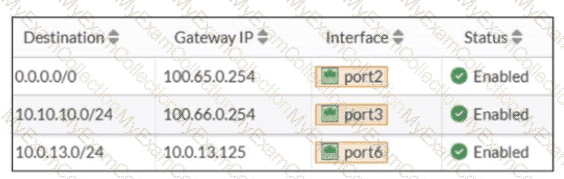
Based on the routing table shown in the exhibit, which two statements are true? (Choose two.)
An administrator wanted to configure an IPS sensor to block traffic that triggers the signature set number of times during a specific time period. How can the administrator achieve the objective?
A new administrator is configuring FSSO authentication on FortiGate using DC Agent Mode. Which step is not part of the expected process?
A network administrator has enabled full SSL inspection and web filtering on FortiGate. When visiting any HTTPS websites, the browser reports certificate warning errors. When visiting HTTP websites, the browser does not report errors.
What is the reason for the certificate warning errors?
Refer to the exhibit.
A partial cloud topology is shown.
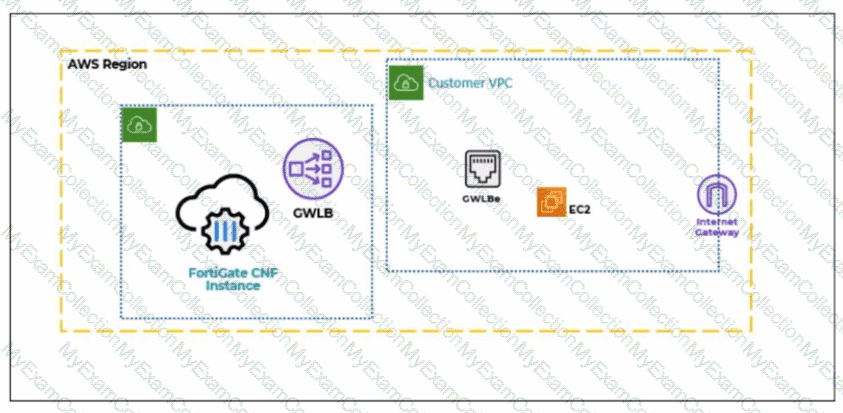
You deployed a FortiGate Cloud-Native Firewall (CNF) in AWS.
During the deployment, which components must the FortiGate CNF create to handle traffic from the EC2 instance?
An administrator configures FortiGuard servers as DNS servers on FortiGate using default settings.
What is true about the DNS connection to a FortiGuard server?
An administrator wants to address shadow IT visibility challenges and prevent users from sending sensitive files outside the organization without proper approval. Which FortiSASE method should the administrator implement to achieve these goals? (Choose one answer)
Refer to the exhibit.
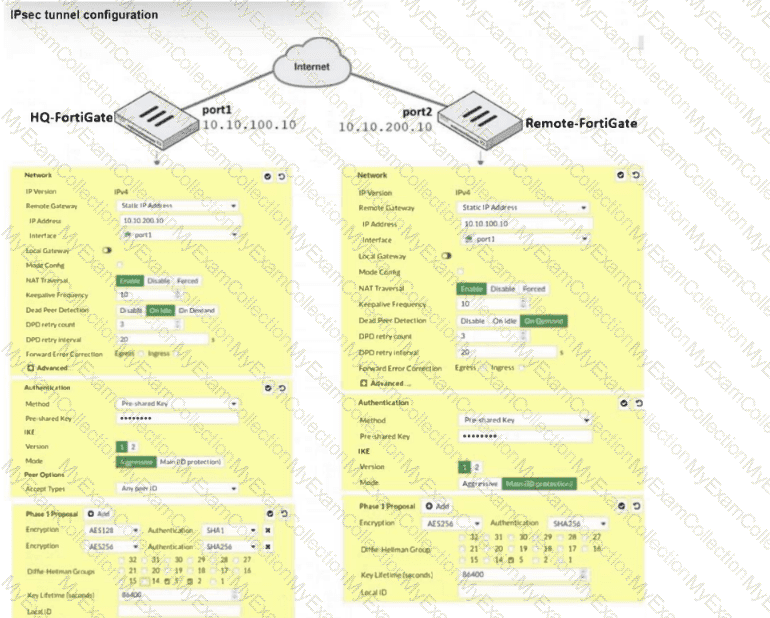
A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 failed to come up. The administrator has also re-entered the pre-shared key on both FortiGate devices to make sure they match.
Based on the phase 1 configuration and the diagram shown in the exhibit, which two configuration changes can the administrator make to bring phase 1 up? (Choose two.)
Which two statements describe characteristics of automation stitches? (Choose two answers)
Refer to the exhibit.
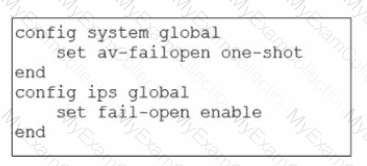
Based on this partial configuration, what are the two possible outcomes when FortiGate enters conserve mode? (Choose two.)
An administrator has configured the following settings.
config system settings
set ses-denied-traffic enable
end
config system global
set block-session-timer 30
end
What are the two results of this configuration? (Choose two.)
Refer to the exhibit.
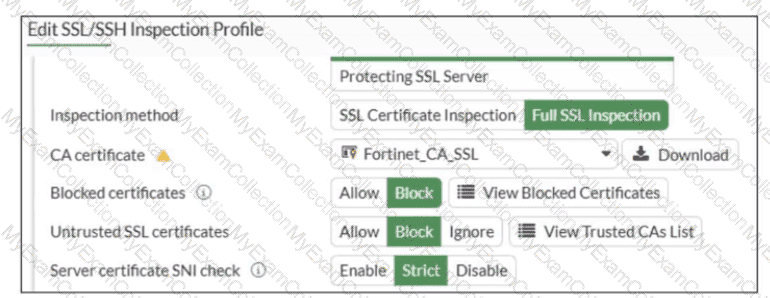
What would be the impact of these settings on the Server certificate SNI check configuration on FortiGate?
Refer to the exhibit showing a debug flow output.
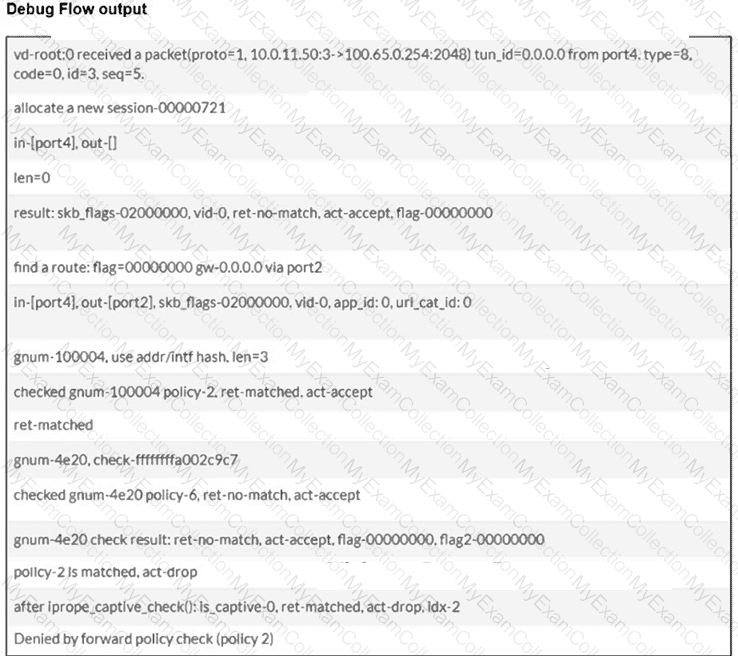
Which two conclusions can you make from the debug flow output? (Choose two answers)
Refer to the exhibit.
A routing table is shown
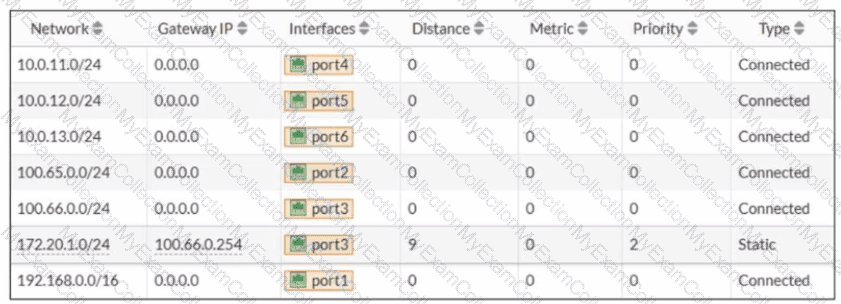
An administrator wants to create a new static route so the traffic to the subnet 172.20.1.0/24 is routed through port2 only. What are the two criteria that the administrator can use to achieve this objective? (Choose two.)
You have created a web filter profile named restrictmedia-profile with a daily category usage quota.
When you are adding the profile to the firewall policy, the restrict_media-profile is not listed in the available web profile drop down.
What could be the reason?
Refer to the exhibits.
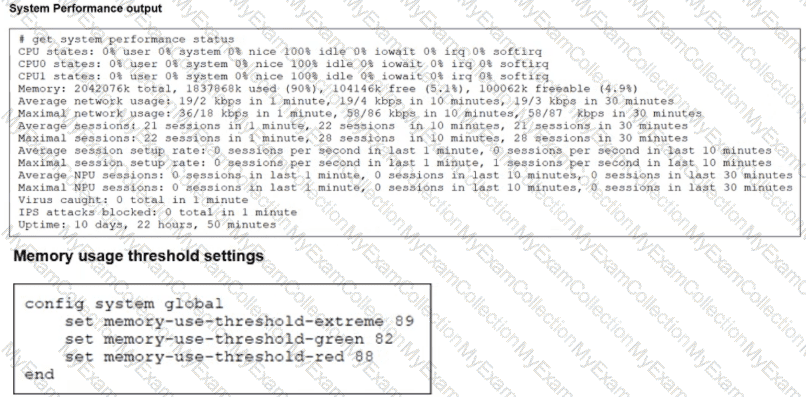
The exhibits show the system performance output and default configuration of high memory usage thresholds on a FortiGate device.
Based on the system performance output, what are the two possible outcomes? (Choose two.)
Refer to the exhibits.
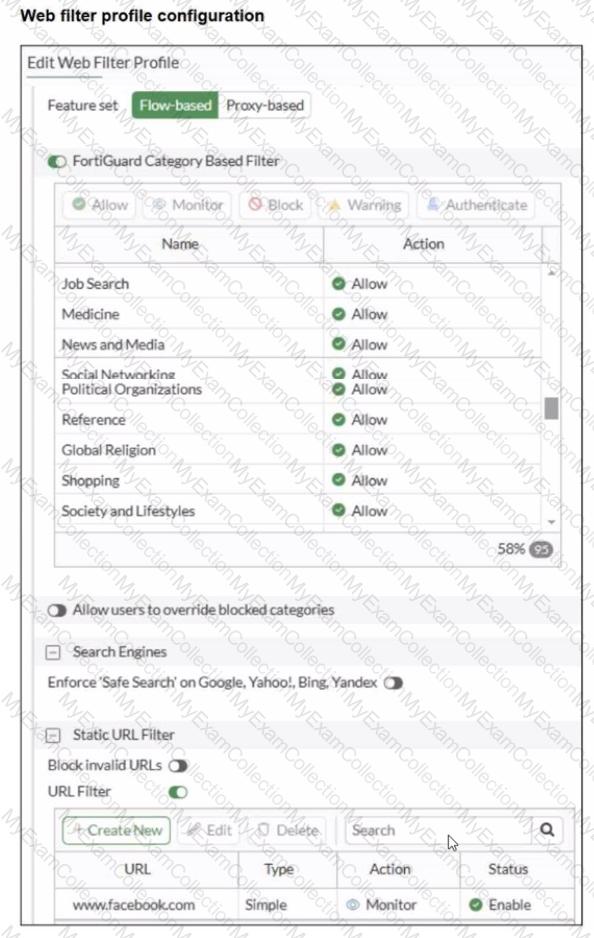
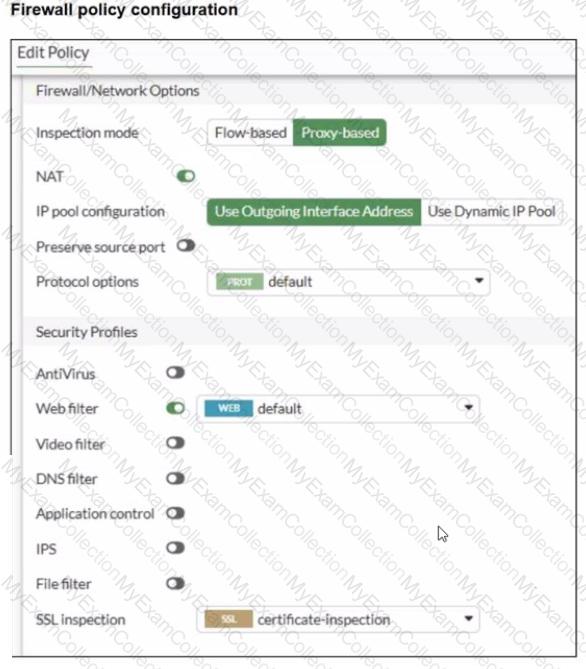
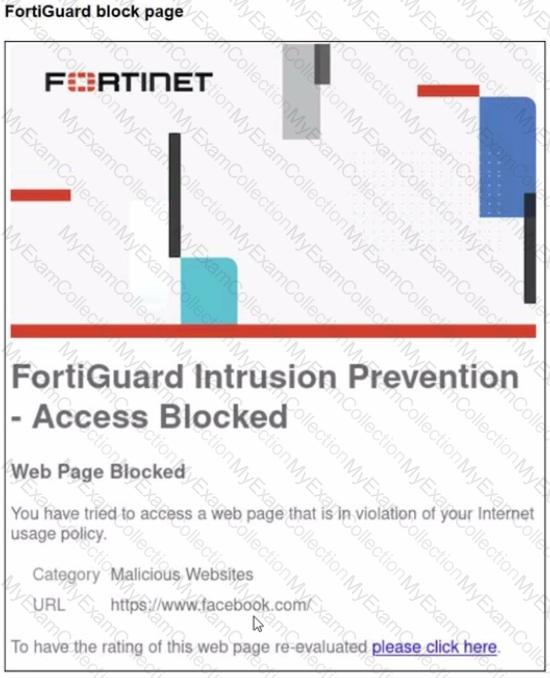
A web filter profile configuration and firewall policy configuration are shown.
You are trying to access www. facebook.com, but you are redirected to a FortiGuard web filtering block page.
Based on the exhibits, what is the possible cause of the issue?
Which three statements explain a flow-based antivirus profile? (Choose three answers)
Refer to the exhibits.
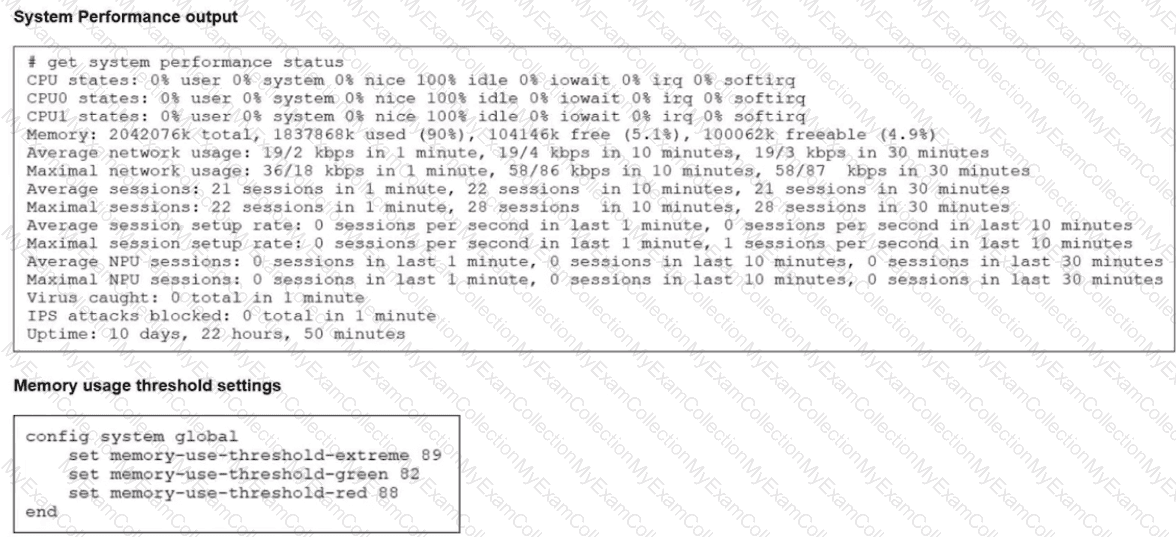
The system performance output and default configuration of high memory usage thresholds on a FortiGate device are shown.
Based on the system performance output, what are the two possible outcomes? (Choose two.)
Refer to the exhibit to view the firewall policy.
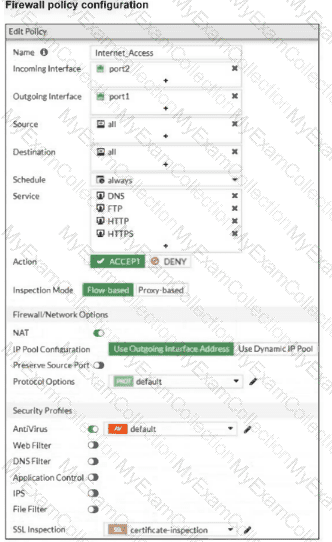
Why would the firewall policy not block a well-known virus, for example EICAR? (Choose one answer)

