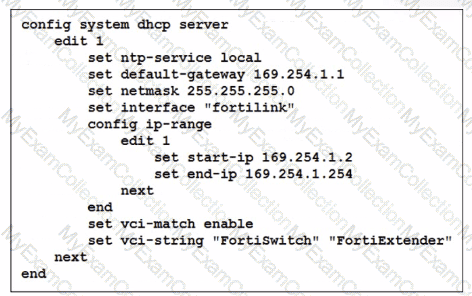
You ' ve configured the FortiLink interface, and the DHCP server is enabled by default. The resulting DHCP server settings are shown in the exhibit. What is the role of the vci-string setting in this configuration?
Refer to the exhibits.
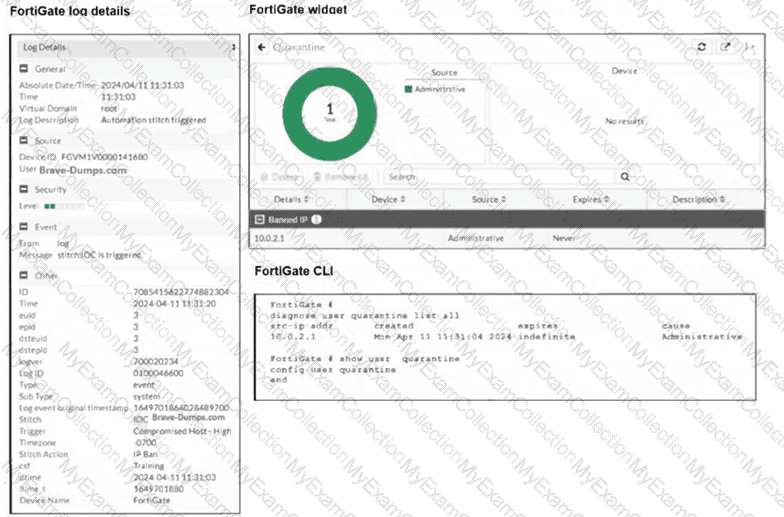
The exhibits show the FortiGate logs, widget, and CLI. Security Fabric quarantine automation is being tested using a device with the IP address 10.0.2.1, which is connected to a managed FortiSwitch. Shortly after attempting to access a malicious website, the device loses access to the internet and other VLANs within the network. However, it can still communicate with other devices within the same VLAN. Which configuration change is required to fix the issue?
Which statement about generating a certificate signing request (CSR) for a CER certificate is true?
A conference center wireless network provides guest access through a captive portal, allowing unregistered users to self-register and connect to the network. The IT team has been tasked with updating the existing configuration to enforce captive portal authentication over a secure HTTPS connection. Which two steps should the administrator take to implement this change? (Choose two.)
A FortiSwitch is not appearing in the FortiGate management interface after being connected via FortiLink. What could be a first troubleshooting step?
In addition to requiring a FortiAnalyzer device to configure the Security Fabric, which license must be added to FortiAnalyzer to use Indicators of Compromise (IOC) rules?
Refer to the exhibits.
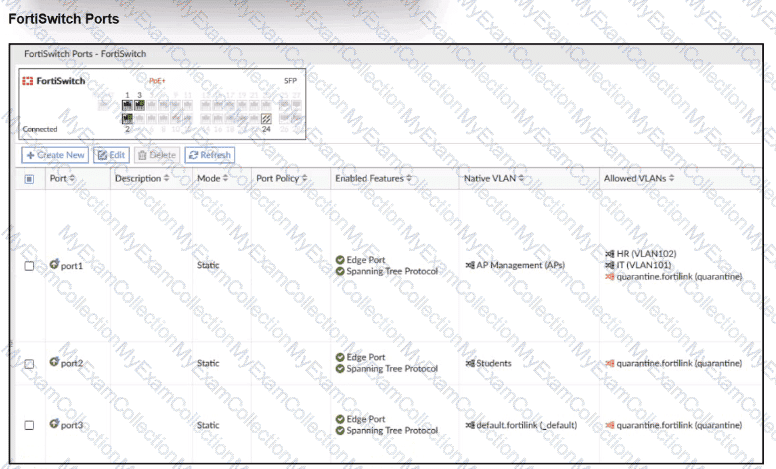
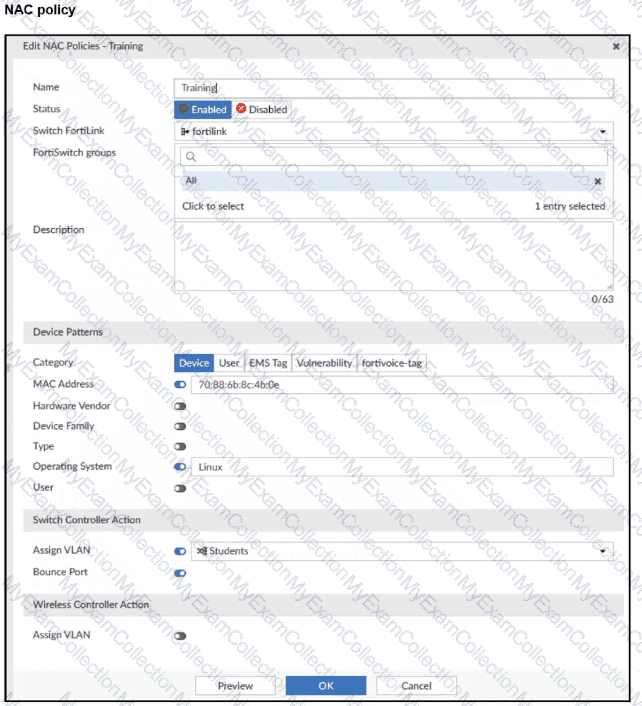
A NAC policy has been configured to apply traffic that flows through FortiSwitch port 2. Traffic that meets the NAC policy criteria will be assigned to the Students VLAN. However, the NAC policy does not seem to be taking effect.
Which configuration is missing?
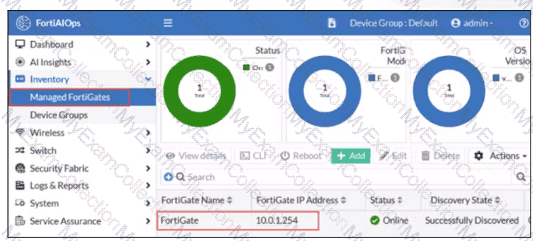
FortiGate has been added to FortiAIOps for management.
Which step must be performed on FortiAIOps to add a FortiSwitch device connected to the recently added FortiGate?
Refer to the exhibits.
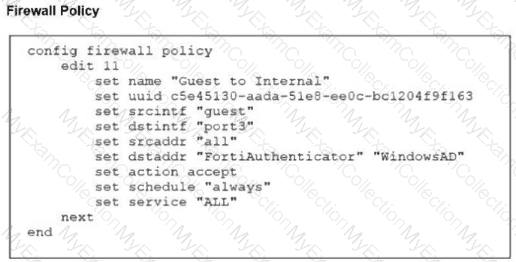
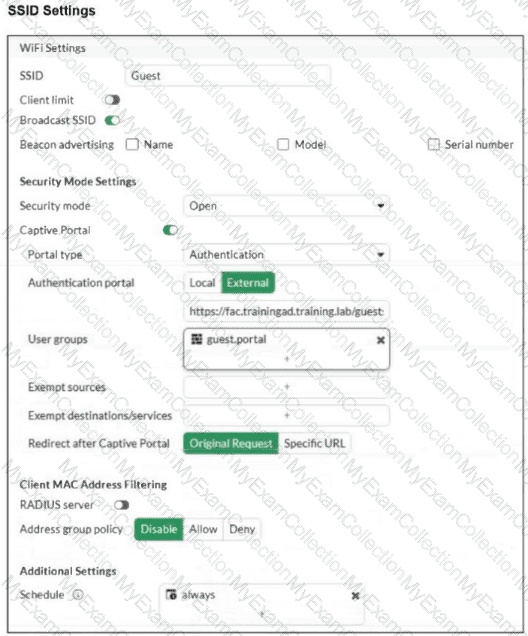
Examine the firewall policy configuration and SSID settings. Users trying to connect to the new Guest wireless network should be redirected to an external captive portal, however, these wireless users are not able to see the captive portal login page. The external captive portal URL has been verified as correct, yet the issue persists. Which configuration change should fix the problem?
Refer to the exhibit.
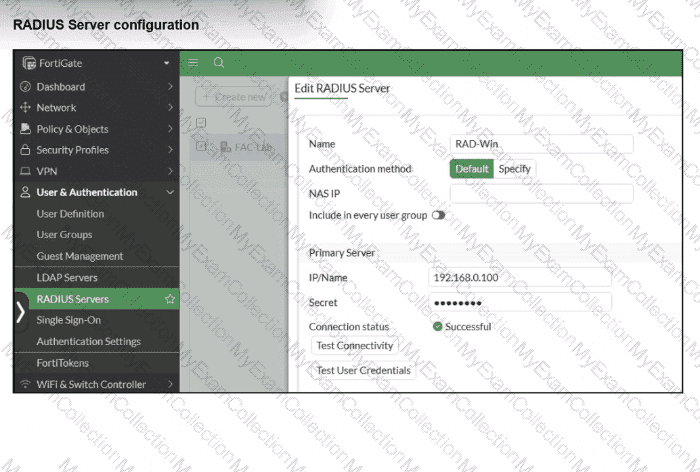
On FortiGate, a RADIUS server is configured to forward authentication requests to FortiAuthenticator, which acts as a RADIUS proxy. FortiAuthenticator then relays these authentication requests to a remote Windows AD server using LDAP.
While testing authentication using the CLI command diagnose test authserver. the administrator observed that authentication succeeded with PAP but failed when using MS-CHAFV2.
Which two solutions can the administrator implement to enable MS-CHAPv2 authentication? (Choose two.)
You are setting up a captive portal to provide Wi-Fi access for visitors. To simplify the process, your team wants visitors to authenticate using their existing social media accounts instead of creating new accounts or entering credentials manually.
Which two actions are required to enable this functionality? (Choose two.)

