What are three examples of solution components of the network infrastructure that help enforce security policy compliance on all devices as they seek to access the network and computing resources, thereby limiting damage from emerging security threats such as viruses, worms, and spyware? (Choose three)
A network automation team plans to develop tasks to configure services on a network by using a Python controller The configuration tasks must be implemented by using operations that support network-wide transactions The candidate configuration must be validated automatically for all targeted devices before being applied to each specific device What can be used to apply the configuration to the network devices?
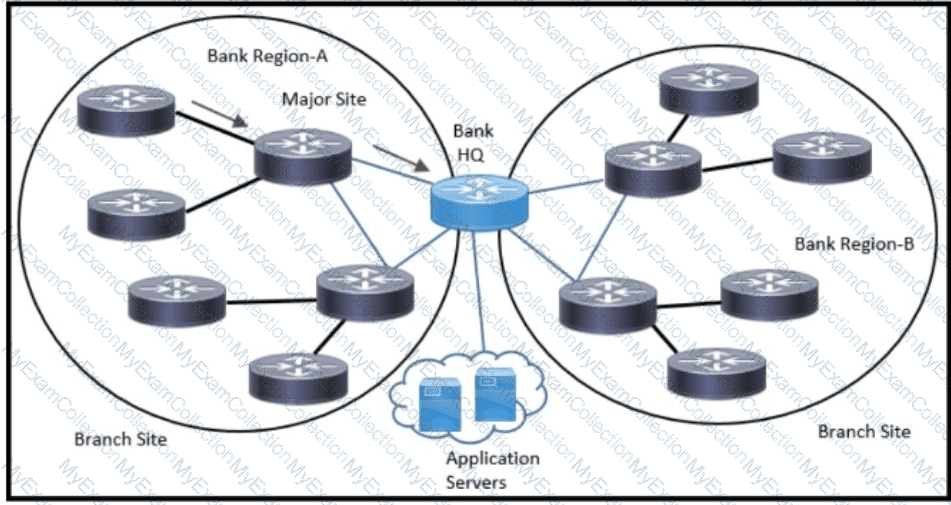
Refer to the exhibit. An architect has been tasked to design an ISIS solution for a medium-size financial customer. The resulting design must meet these requirements:
Which two ISIS design aspects must be included? (Choose two.)
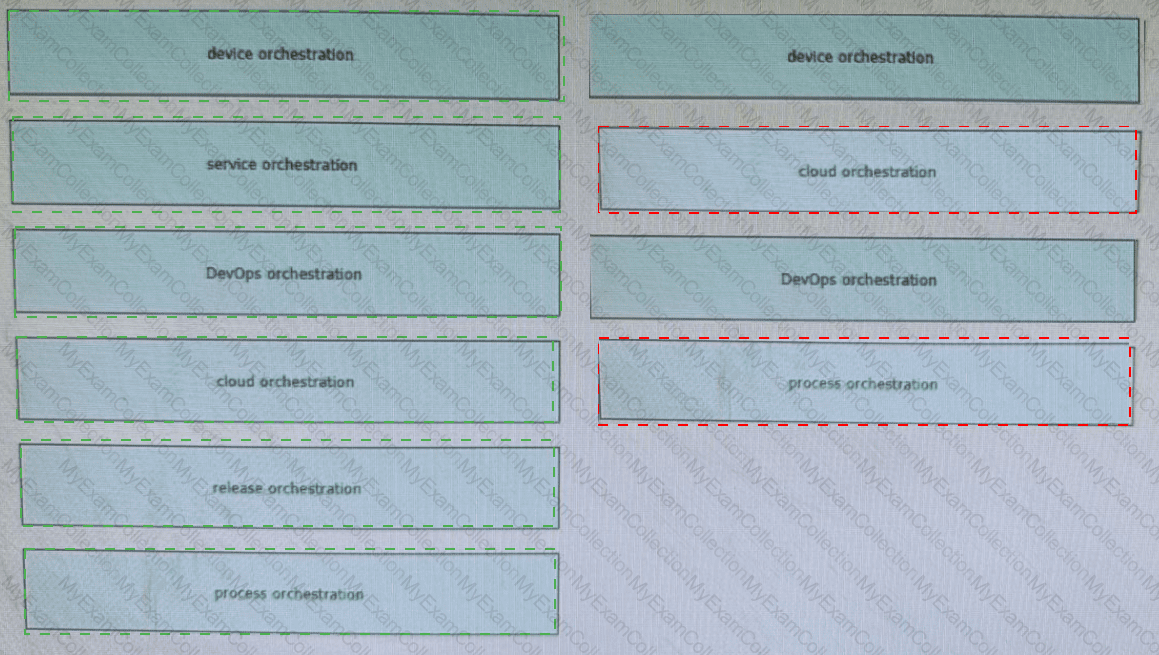
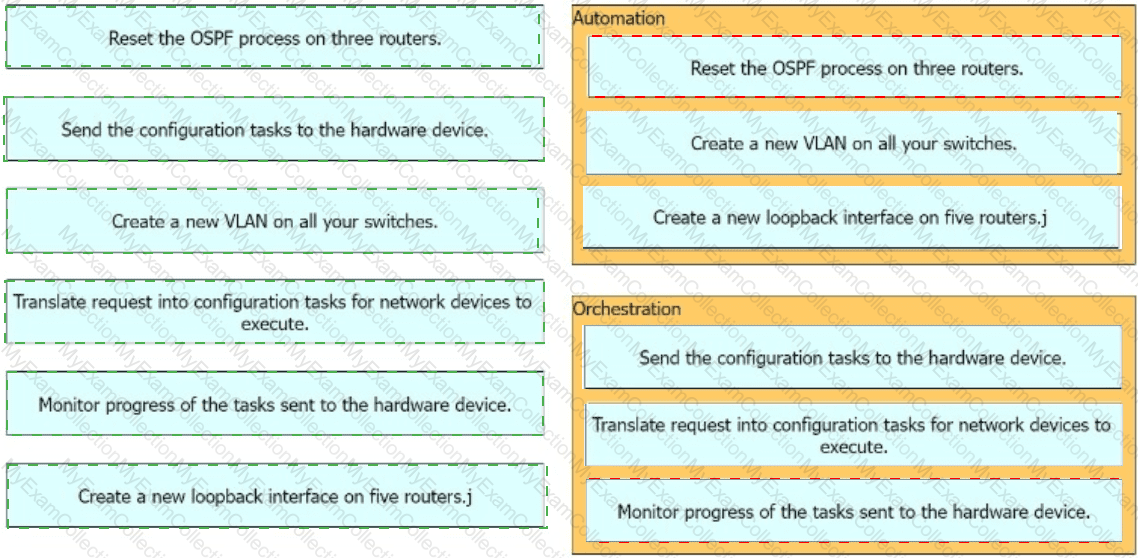
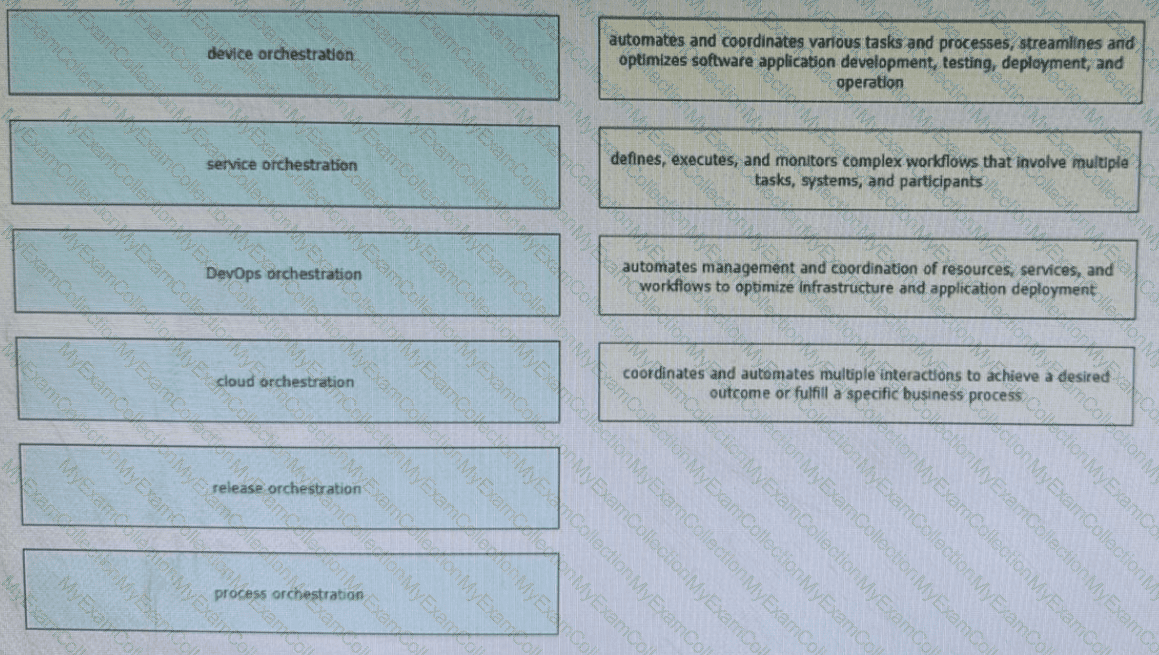
Network orchestration enables network administrators to focus on strategic initiatives, innovation, and value-added tasks rather than spending time on manual and repetitive network management activities. Drag and drop the orchestration types from the left onto the corresponding functions on the right. Not all options are used.
In a multi-cloud environment, which two practices should be implemented to safeguard the integrity of Al-driven network decisions? (Choose two.)
An enterprise service provider is planning to migrate the customer network to MPLS to connect cloud applications The customer network team and service provider team are analyzing all process (tows before live migration and implementation Before planning the migration, what is a crucial task that must be executed?
A software-defined network can be defined as a network with an API that allows applications to understand and react to the state of the network in near real time A vendor is building an SDN solution that exposes an API to the RIB and potentially the forwarding engine directly The solution provides off-box processes with the capability to interact with the routing table in the same way as a distributed routing process Which SDN framework model does the solution use?
The goal for any network designer is to strive to build a resilient network that adapts to changing conditions rapidly with minimal impact on the services running over the network A resilient network can adapt to failures but which soft failure can be harder to define and detect?
Which three tools are used for ongoing monitoring and maintenance of a voice and video environment? (Choose three.)
Which two statements describe network automation and network orchestration? (Choose two)
Company XYZ has two routing domains in their network, EIGRP and OSPF. The company wants to provide full reachability between the two domains by implementing redistribution on a router running both protocols They need to design the redistribution in a way that the OSPF routers will see link costs added to external routes. How must the redistribution strategy be designed for this network?
SDN controllers need to sustain healthy operation under the pressure of different objectives from the applications they host. High availability can be achieved through improved southbound APIs and controller placement heuristics and formal models. Which two implementation strategy help to maximize resilience and scalability? (Choose two.)
Which interface between the controller and the networking device enables the two to communicate and allows the controller to program the data plane forwarding tables of the networking device?
A network consists of multiple planes where each plane represents a different area of network operations and cames different types of network traffic Which two statements describe the concepts of assurance in the context of control planes ' ? (Choose two.)
A company with an existing multivendor network is moving from 1 G dark fiber to an ISP virtual leased-line solution The company ' s internal security policy states that any traffic traversing a network that is not owned by the company must be encrypted What must be used to meet the requirements?

Refer lo the exhibit Company XYZ BGP topology is as shown in the diagram The interface on the LA router connected toward the 10 1 5 0/24 network is faulty and is going up and down, which affects the entre routing domain Which routing technique can be used in the routing policy design so that the rest of the network is not affected by the flapping issue ?
What are two parameters that can be leveraged by SAML in mixed private/public cloud environments by using identity and asset management? (Choose two)
Which component of the SDN architecture automatically ensures that application traffic is routed according to policies established by network administrators?
A large enterprise customer is planning a new WAN connection to its headquarters The current architecture is dual homed with static routing but users complain when a specific link fails Failure of the other link does not affect any services or applications The new WAN connection must provide the headquarters with a resilient network design and increase the return on investment Which solution should be recommended to the customer?
In large-scale networks controllers needs to be able to process millions of flows per second without compromising the quality of the service What are two actions that must be implemented to address scaling limitations when deploying the network*? (Choose two.)
A customer migrates from a traditional Layer 2 data center network Into a new SDN- based, spine-and-leaf VXLAN EVPN data center within the same location. The networks are joined to enable host migration at Layer 2. Which activity should be completed each time a legacy network is migrated?
What are two reasons for a company to prefer a hybrid approach rather than a mixed approach while transitioning to a software-defined network? (Choose two.)
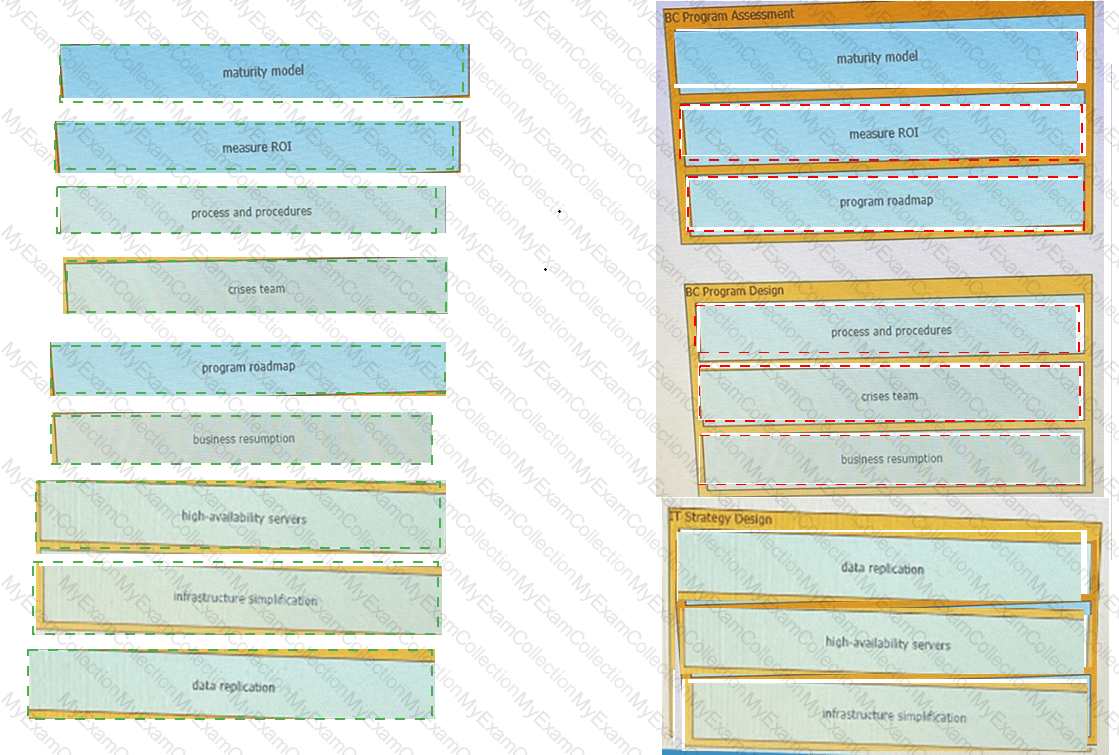
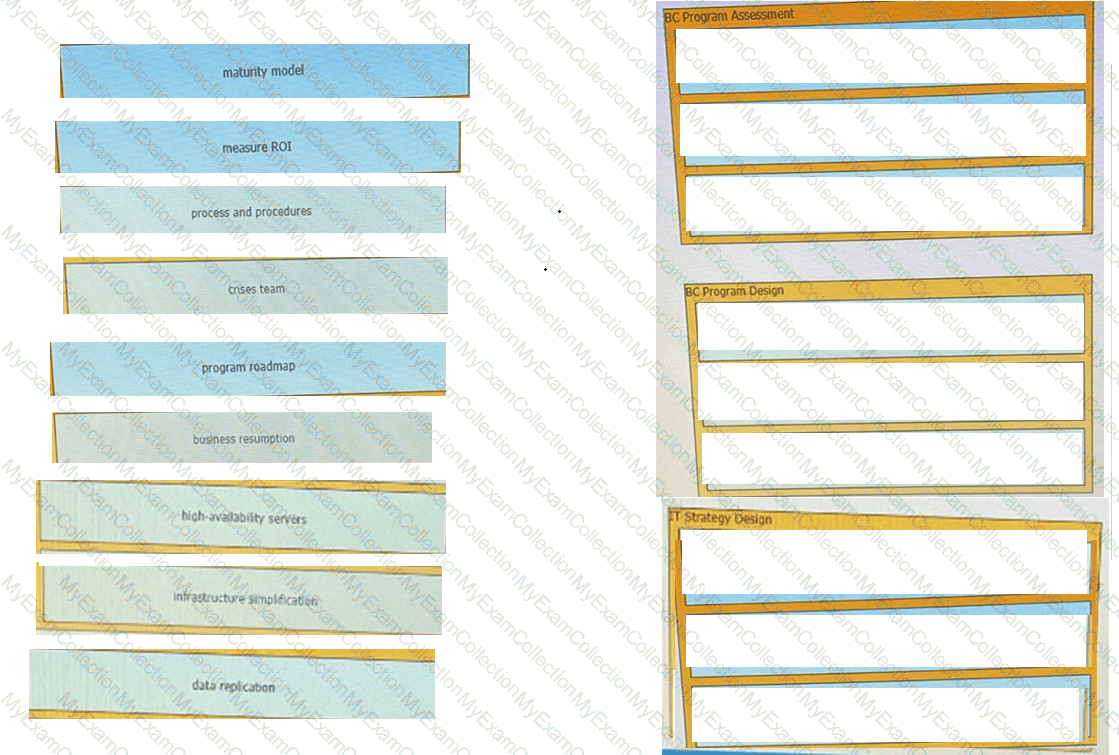
The goal of a business continuity plan is to provide exhaustive information about backup sites and disaster recovery services, to specify who is responsible for business continuity planning and recovery efforts, and to define how different teams should respond Plans should also include step-by-step operational strategies to ensure operations during short-term and long-term disruptions Drag and drop the activities from the left onto the corresponding stages on the tight.
An enterprise requires MPLS connected branches to access cloud-based Microsoft 365 services over an SD-WAN solution. Internet access Is available only at dual regional hub sites that are connected to the MPLS network. Which connectivity method provides an optimum access method to the cloud-based services If one ISP suffers loss or latency?
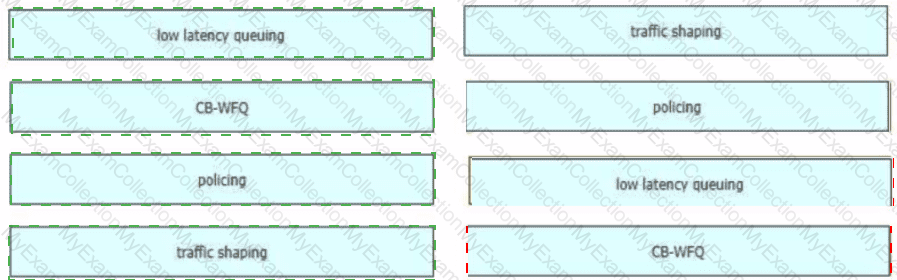
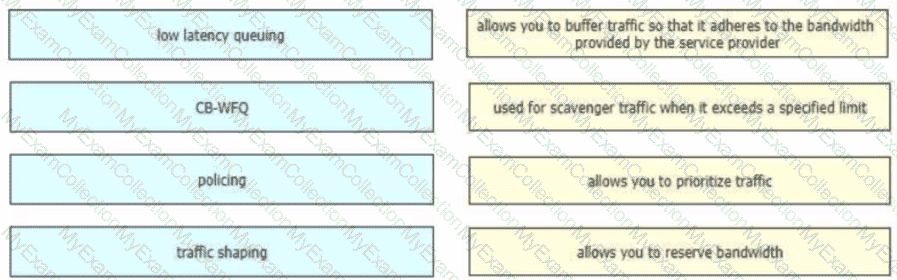
Drag and drop the QoS technologies from the left onto the correct capabilities on the right
A small organization of 20 employees is looking to deliver a network design service for modernizing customer networks to support advanced solutions.
Project scope and weekly progress should be visualized by the management.
Always consider feedback and make changes accordingly during the project.
Should consider flexibility to change scope at the point of time.
Which project methodology meets the requirements and have the least impact on the outcome?
While positive feedback loops generally don ' t last long enough to bring down a network completely, they can still last long enough to disrupt traffic flows or to cause the network to converge more slowly than it should.
What are two examples of cases where a positive feedback loop can be long-lived and devastating to the network ' s control plane? (Choose two)
A bank recently had their security compromised during an initial key exchange between devices using a symmetric cryptography algorithm, and as a result the key was revealed/leaked. Going forward, they want to ensure that key exchanges are performed using asymmetric cryptography algorithms. Which algorithm offers the desired functionality?
Drag and drop the design characteristics from the left onto the correct network filter techniques on the right. Not all options are used.
What is the key strategy to address scalability challenges In the rapidly evolving digital landscape with resilient designs?
The advantages of a hybrid SDN/OSPF control plane are broadly recognized in the networking community, as it promises the best of two worlds: programmability and agility of SDN and the reliability and fault tolerance of OSPF, but there are tradeoffs. Which two challenges of a hybrid SDN control plane exist in an operational network? (Choose two.)
It is often seen that companies pick a cloud vendor solely based on technical preferences without putting enough weight on the business strategies that are driving the cloud initiatives Which strategic requirement may come into play where it is more likely that the decision makers will look to leverage laaS over SaaS or PaaS?
The Layer 3 control plane is the intelligence over the network that steers traffic toward its intended destination Which two techniques can be used in service provider-style networks to offer a more dynamic, flexible, controlled, and secure control plane design? (Choose two.)
What is the best approach in a large legacy application migration scenario when the goal is to complete the migration in the shortest possible time?
When consumers that leverage laaS reach 100% resource capacity what can be used to redirect the overflow of traffic to the public cloud, so there is no disruption to service?
A global e-commerce company is expanding its operations and planning to migrate its entire infrastructure to a hybrid cloud solution. They are concerned about data governance and want to ensure that their customers ' data is treated with utmost respect to sovereignty and privacy. What is an appropriate approach?
Comparing traditional networks with SDN, where the network is only application aware, what is the advantage of SDN architecture?
A mega store plans to expand its business into the online world, and wants to operate using the highest possible security standards to prove to their customers that they take handling of their payment information seriously. Only TLS v1.3 will be allowed on their websites. Which type of SSL certificate will emphasize their commitment to enforcing high security standards and minimize risk of spoofing?
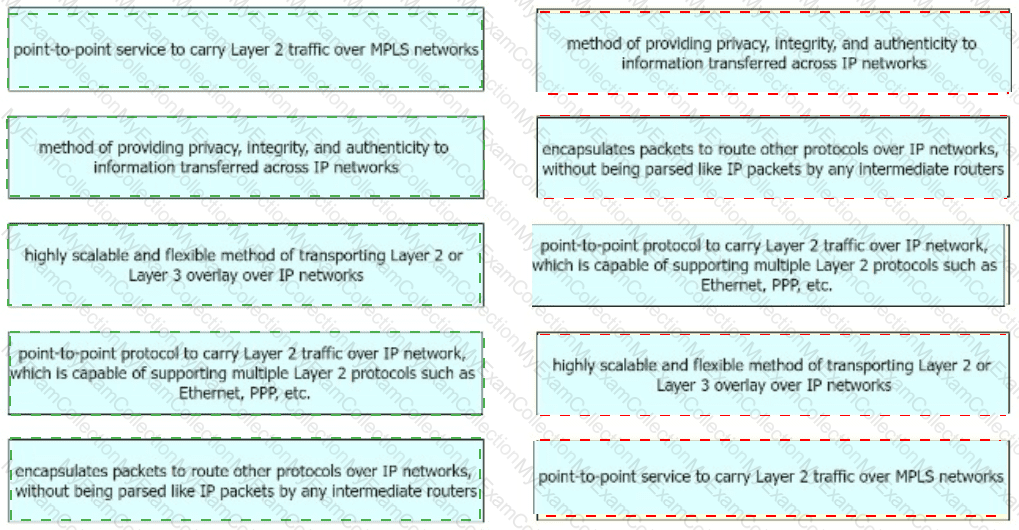
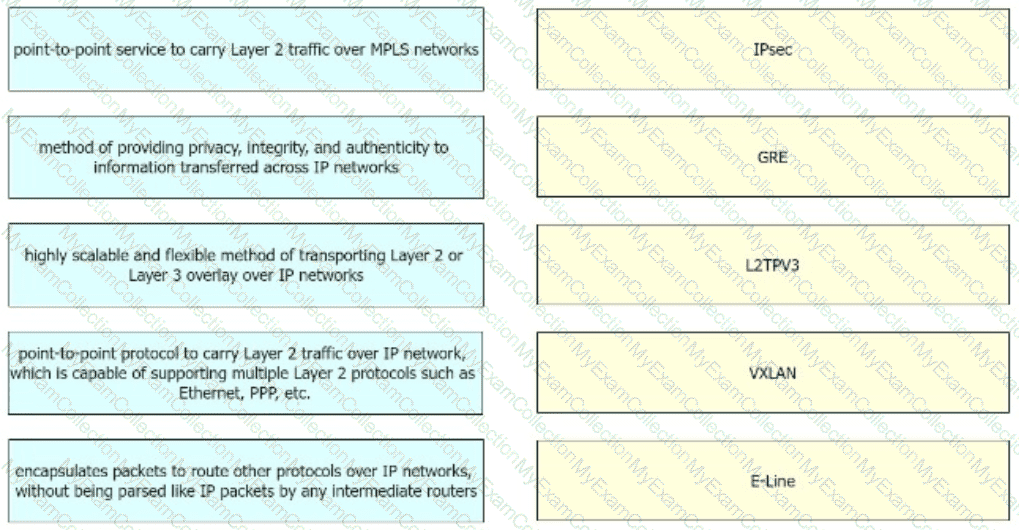
Drag and drop the right functional descriptions from the left onto the corresponding protocols on the right.
Company XYZ plans to run OSPF on a DMVPN network They want to use spoke-to-spoke tunnels in the design What is a drawback or concern in this type of design?
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
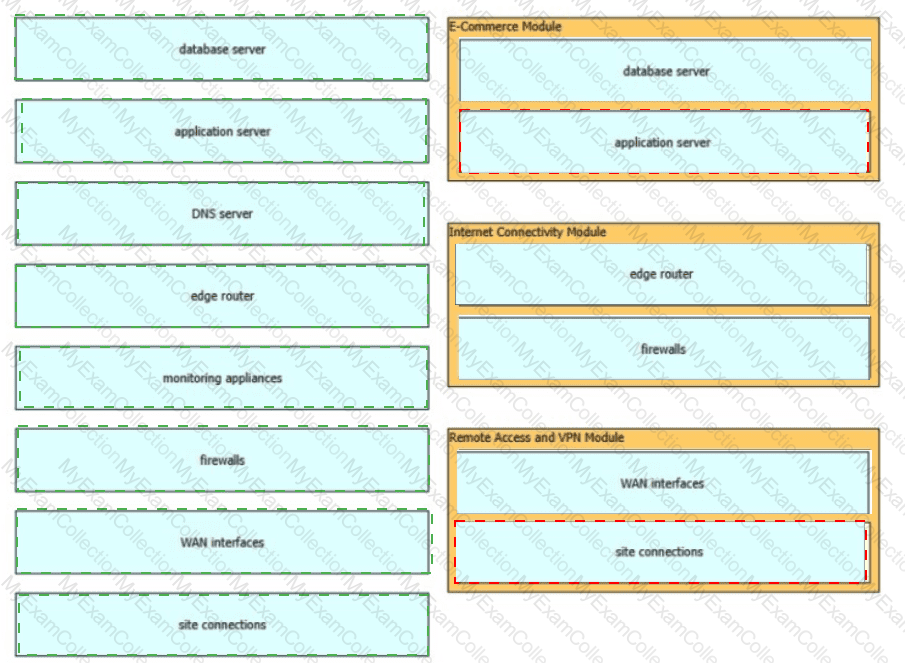
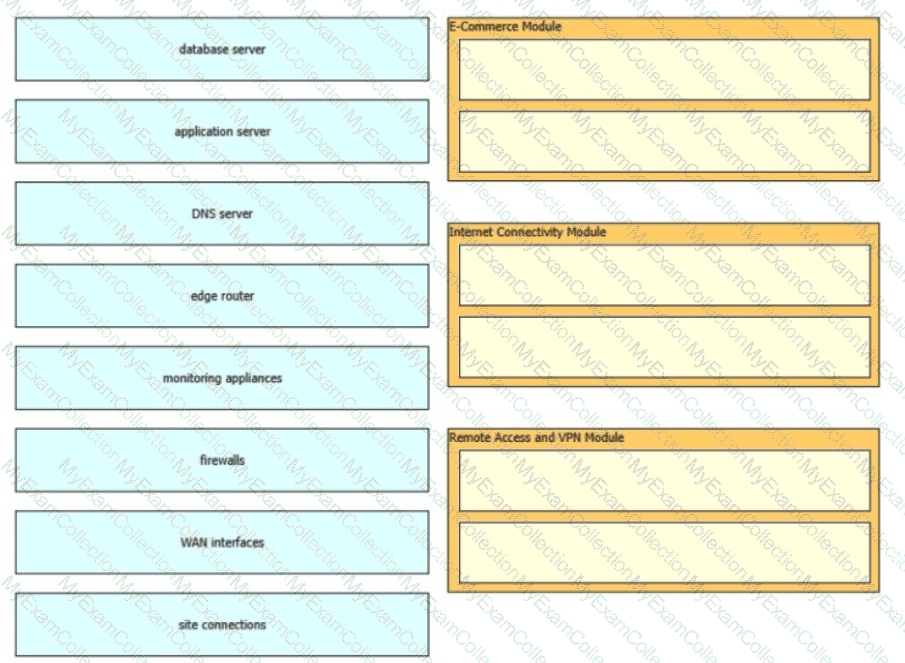
The Enterprise Edge infrastructure modules aggregate the connectivity from the various elements outside the campus—using various services and WAN technologies as needed typicaly provisioned from service providers and route the traffic into the Campus Core layer The Enterprise Edge modules perform security functions when enterprise resources connect across public networks and the internet Drag and drop the network device types from the left onto the corresponding modules on the right Not all options are used
Which purpose of a dynamically created tunnel interface on the design of IPv6 multicast services Is true?
Company XYZ has a multicast domain that spans across multiple autonomous systems The company wants to choose a technology that provides a simplified and controlled approach to interconnecting the multicast domains Which technology is the best fit for this purpose?
A network architect is working on a large project involving migration to a software-defined networking platform, and is currently working on writing an executive summary for final approval by the management board. When writing the executive summary, What is a limitation of or challenges with software-defined networks that must be listed?
An enterprise SDWAN customer based in the US has several branches in Europe Currently branches use the HQ in the US to access both internal and external services over an MPLS arcuit The design team has been tasked to suggest a solution allowing branches to access their cloud-based office productivity tools and services directly Since all their applications and services are hosted in the cloud, the design team has also been asked to come up with a solution, so branches can connect to the cloud directly from the branch as well Which two cost-effective and optimized solutions can be suggested? (Choose two)
cloud onRamp (SaaS)
Company XYZ is designing the network for IPv6 security and they have these design
requirements:
A switch or router must deny access to traffic from sources with addresses that are correct, but are topologically incorrect
Devices must block Neighbor Discovery Protocol resolution for destination addresses that are not found in the binding table.
Which two IPv4 security features are recommended for this company? (Choose two)
Scalability is a desirable attribute of a network, system, or process Poor scalability can result in poor system performance, necessitating the reengineering or duplication of systems Load scalability is the ability of a system to perform gracefully as traffic increases Which two problems can occur due to poor load scalability design? (Choose two )
Refer to the exhibit. This network is running legacy STP 802.1 d. Assuming " hello_timer " is fixed to 2 seconds, which parameters can be modified to speed up convergence times after single link/node failure?
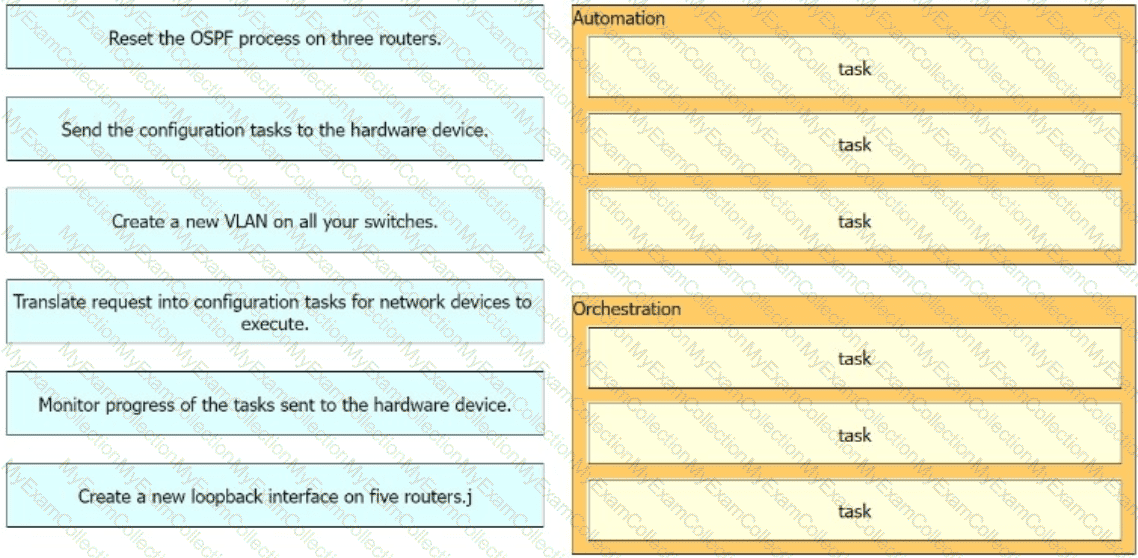
Indicate the nature of automation and orchestration tasks by dragging the tasks on the left to the corresponding category on the right in no particular order.
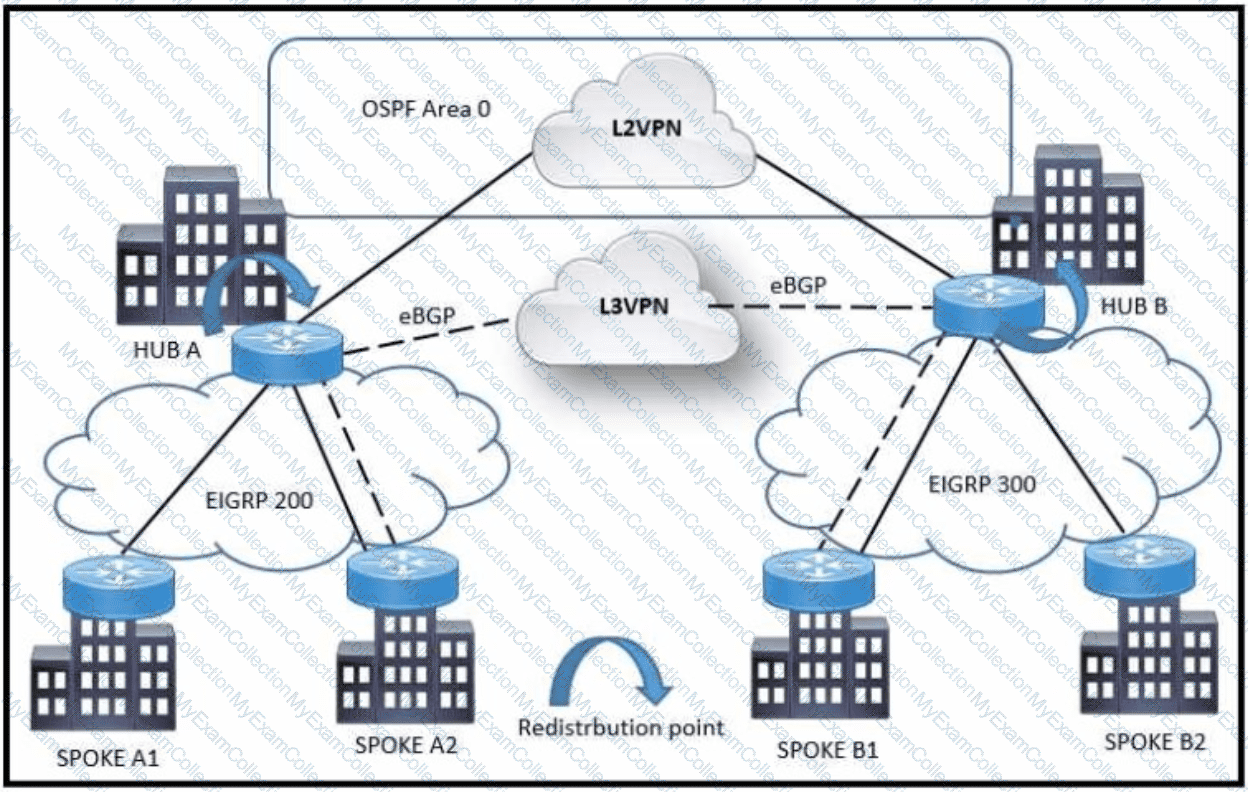
Refer to the exhibit A customer network design team is planning a migration from a legacy TDM-based L2VPN to an MPLS-based L3VPN Migration is planned in a phased approach:
•OSPF backbone Link between HUB A and HUB B sites to be migrated to eBGP
•Spoke A2 and Spoke B1 will be migrated to the L3VPN
Which solution design can be considered to avoid routing loops during backbone link migration
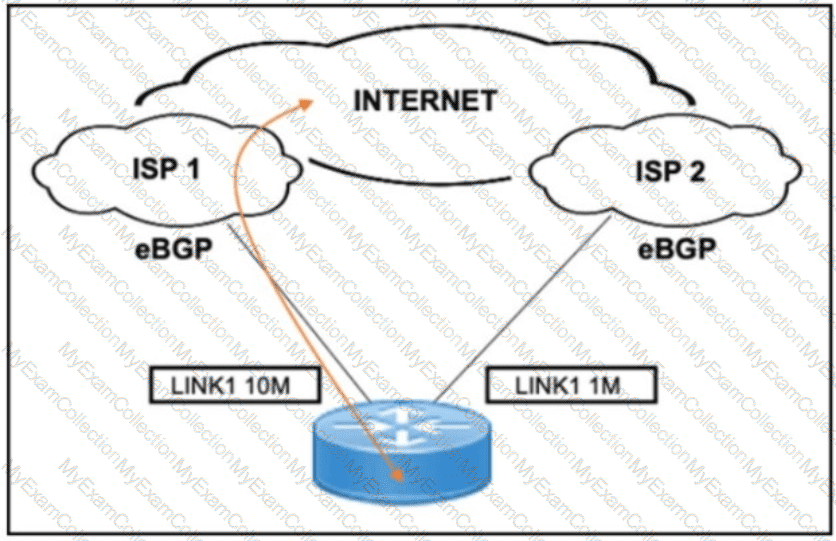
Refer to the exhibit. A customer needs to implement a connectivity model by using one active link for inbound and outbound traffic and a second link for backup. The backup link is low speed and is required only during outages of the primary link. Which design solution should be implemented?
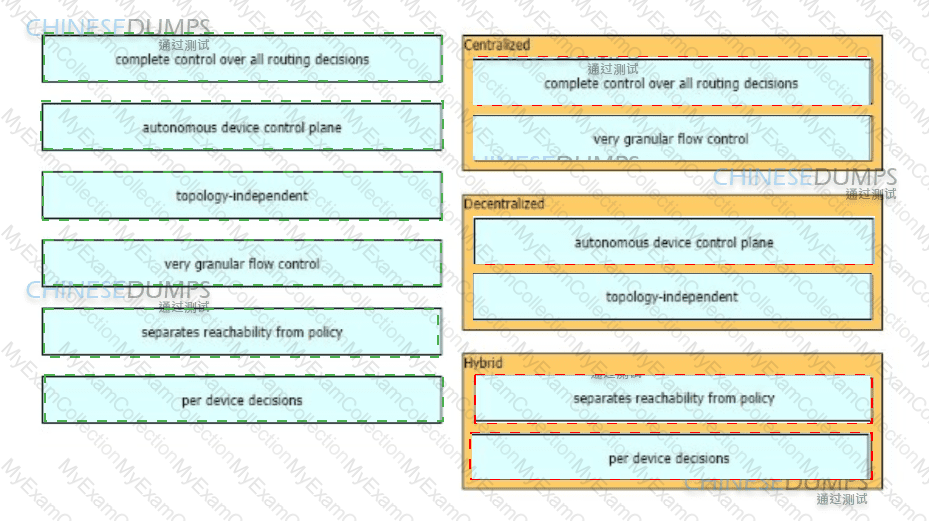
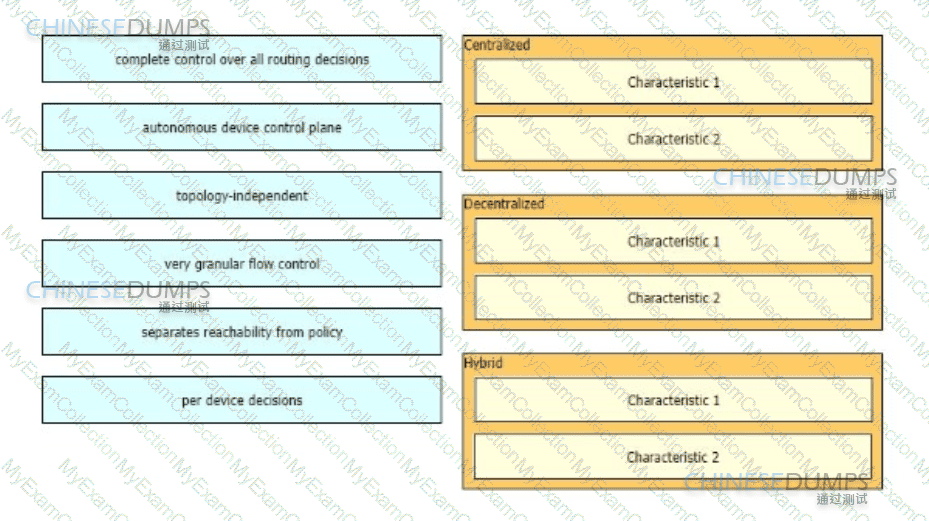
As part of a design solution a consultant needs to describe the trade-offs between different SDN models Drag the characteristics on the left to the correct controller-based network designs on the right in no particular order.
The first step to building en A! strategy is understanding how it helps achieve business goals and objectives Al-first scorecard is an assessment of your organization ' s readiness to adopt and integrate AI technologies to gauge your capabilities and align stakeholders. Which scorecard is useful to understand whether the organization ' s digital infrastructure is strong enough to ensure seamless, standardized data flow between systems with optimal performance?
What are two advantages of the Agile project management methodology? (Choose two)
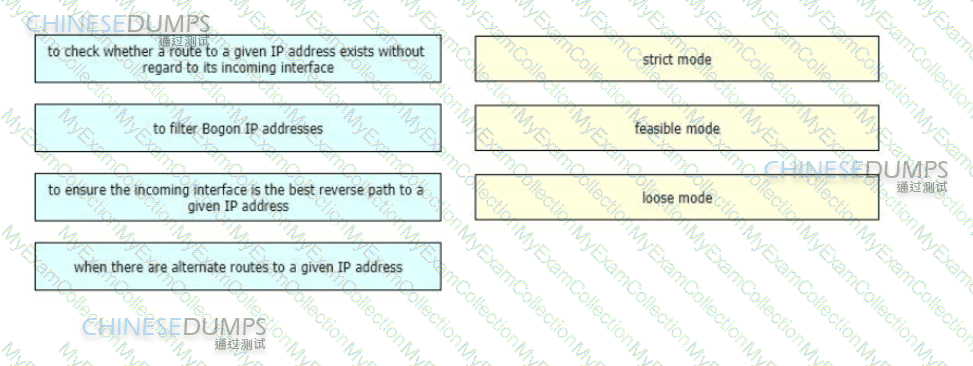
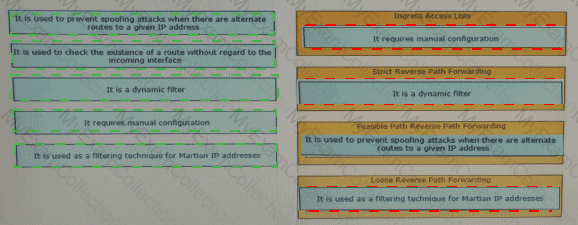
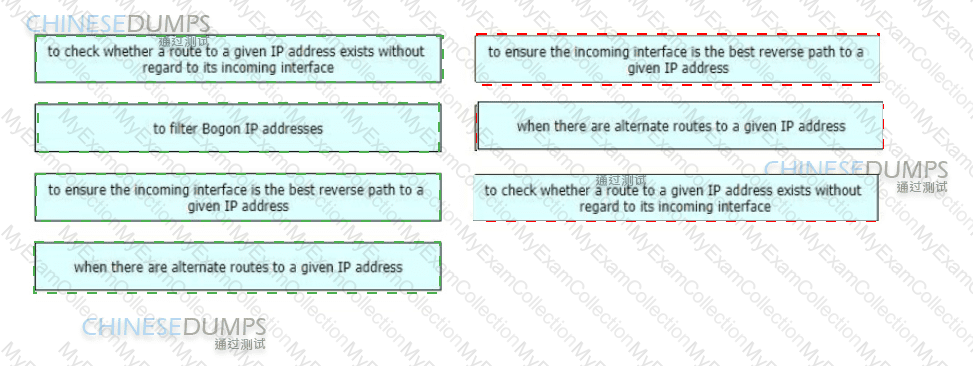
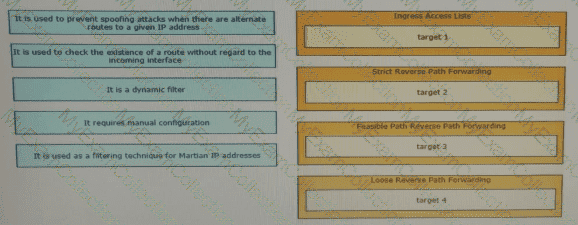
A networking team needs to prevent spoofing attacks They are describing the different uRPF design use cases so they can identify and deploy the optimal mode in various parts of their network
Drag and drop the use cases from the left onto the corresponding uRPF technique on the right Not all options are used