Refer to the exhibit.
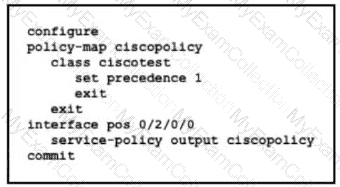
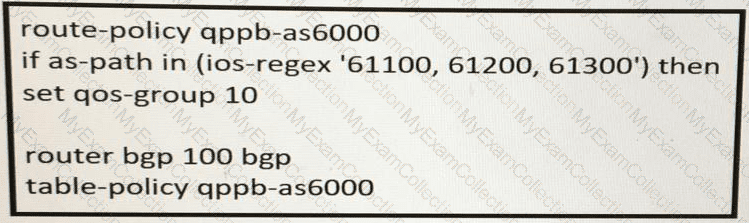
An engineer needs to implement this QoS policy on customer's network due to ongoing slow network issues. What will be the effect on the network when the engineer implements this configuration?
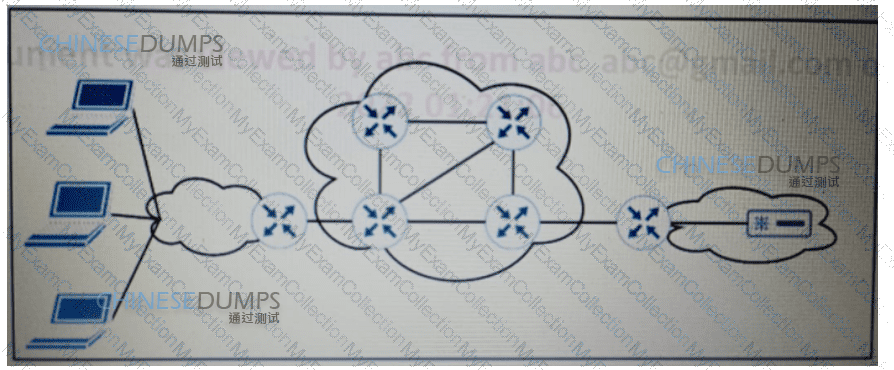
A customer has requested that the service provider use a Cisco MPLS TE tunnel to force the E-line service to take a specific route What is used to send the traffic over the tunnel?
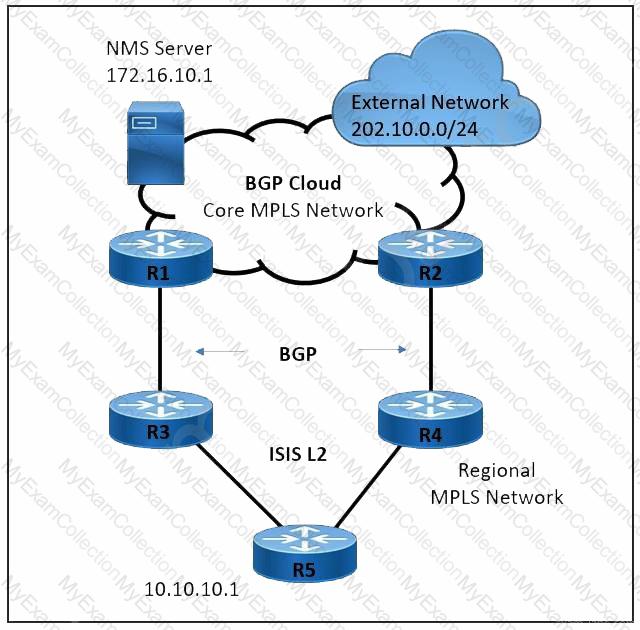
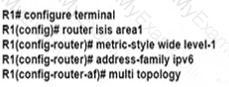
Refer to the exhibit. A large service provider is migrating device management from Layer 2 VLAN-based to Layer 3 IP-based solution. An engineer must configure the ISIS solution with these requirements:
Network management server IP 172.16.10.1 must be advertised from the core MPLS network to the regional domain.
The external network 202.10.0.0/24 must not establish ISIS peering with the R5 router.
The regional network must prevent sending unnecessary hello packets and flooding the routing tables of the R5 router.
Which two ISIS parameters must be implemented to meet these requirements? (Choose two.)
An engineer working for telecommunication company with an employee id: 3715 15 021 needs to secure the LAN network using a prefix list Which best practice should the engineer follow when he implements a prefix list?
After recent network outages and customer complaints, a large Tier 1 service provider has asked a network engineer to implement MPLS OAM policy on all Provider Edge devices in the MPLS network. To improve network performance and reliability, the policy must be able to detect 2% packet drops and a delay of 0.05 seconds. The solution must be based on RFC 6374 and RFC 4379 standards for MPLS OAM. The CCM to detect connectivity issues has already been configured with interval 1000. Which two actions must the engineer take to achieve the goal? (Choose two.)
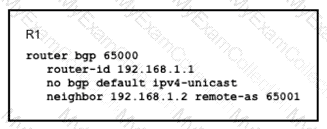
Refer to the exhibit.
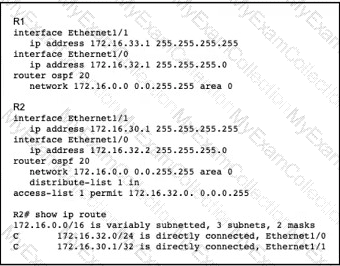
A network engineer notices that router R2 is failing to install network 172.16.33.1/32 in the routing table. Which configuration must the engineer apply to R2 to fix the problem?
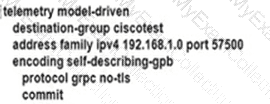
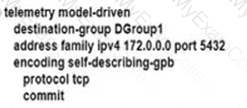
An engineer is developing a configuration script to enable dial-out telemetry streams using gRPC on several new devices. TLS must be disabled on the devices. Which configuration must the engineer apply on the network?
A)
B)
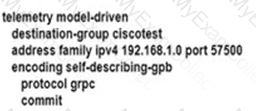
C)
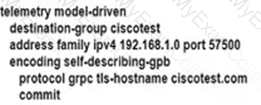
D)
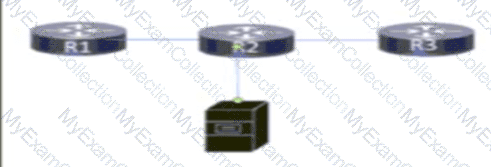
Refer to the exhibit. MPLS is configured within the network. The routers use OSPF to exchange routing information. Hosts that are connected to routers R1 and R3 use routers R2 and R4 to access servers that run a variety of intranet applications. A network engineer must ensure that R1 and R3 maintain an LDP session between them to support the flow of traffic between hosts and servers in case of failure on the path between R1 and R3. Which task should the engineer perform to provide LDP bindings in case of failure on the path between R1 and R3?
What is the purpose of OSPF-TE extensions to MPLS traffic engineering functionality?
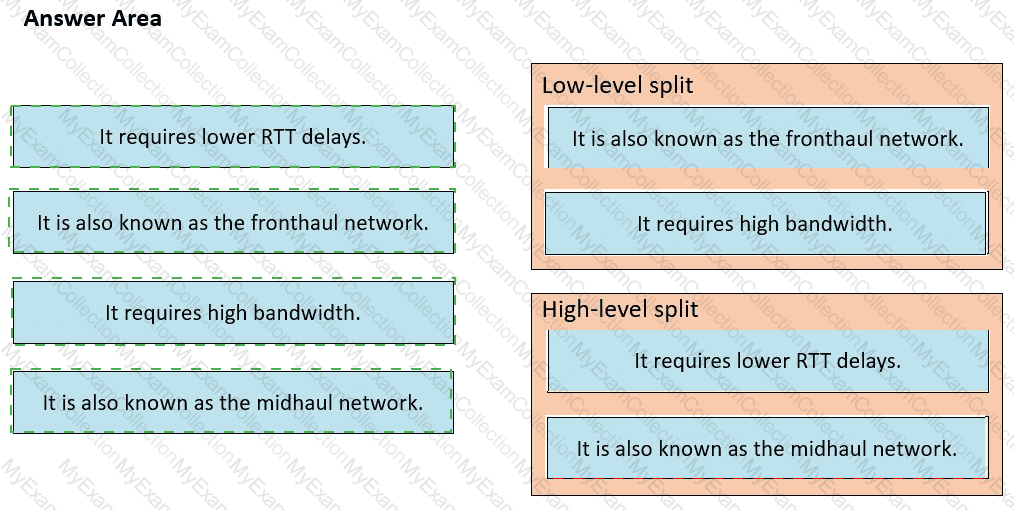
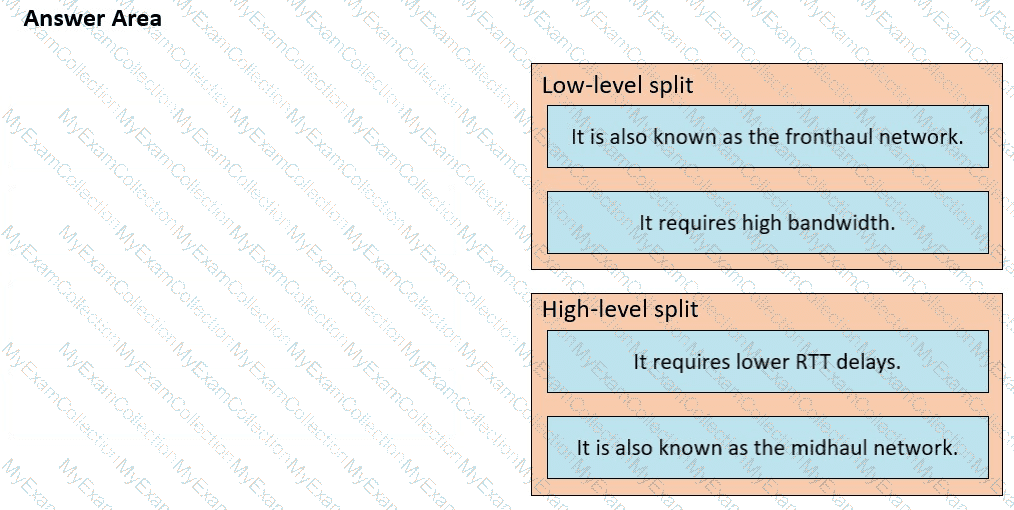
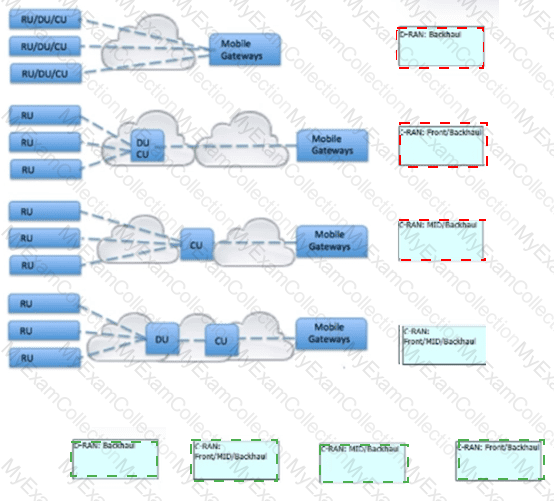
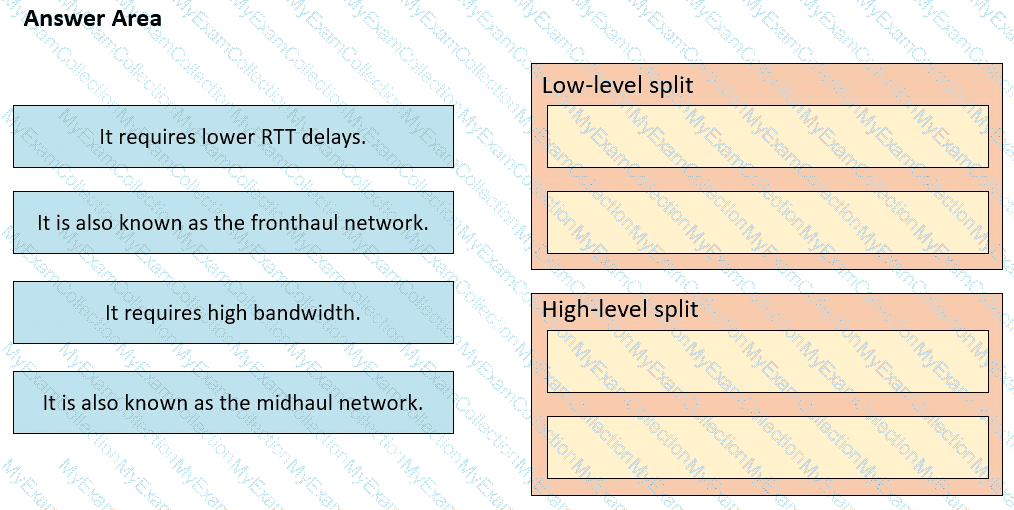
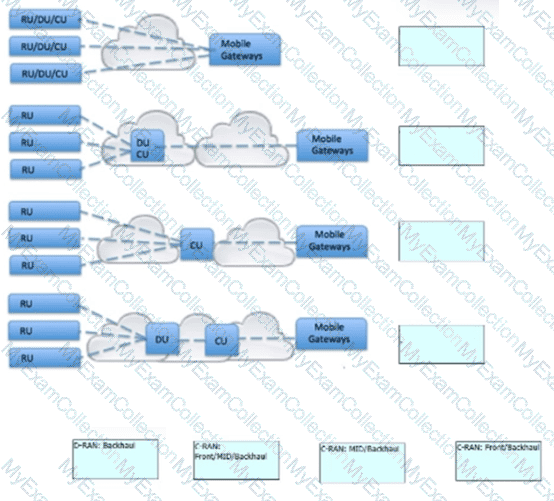
Drag and drop the characteristics from the left onto the corresponding radio splitting approaches on the right
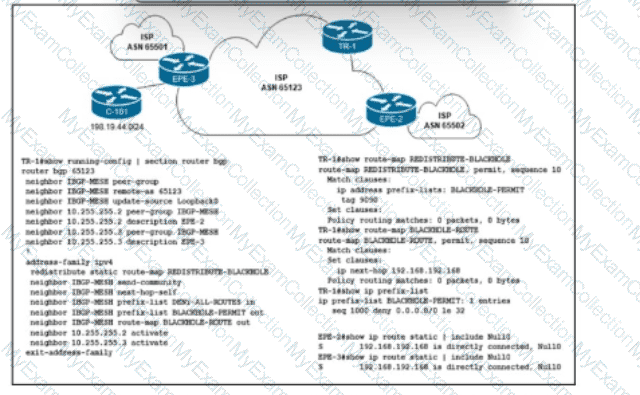
Refer to the exhibit. Customer C-101 in ASN 65123 requested that the ISP blackholes a host route 198.19.44.195, to which the customer is receiving a significant amount of malicious traffic. Which configuration must the network engineer implement on the trigger router TR-1 to fulfill the request without affecting other IP destinations in the customer's block?
The NOC team must update the BGP forwarding configuration on the network with these requirements:
BGP peers must establish a neighborship with NSF capability and restart the session for the capability to be exchanged after 120 seconds.
BGP peers must delete routes after 360 seconds of inactivity.
Which action meets these requirements?
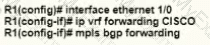
You are configuring MPLS traffic-engineering tunnels in the core.
Which two ways exist for the tunnel path across the core? (Choose two )
Refer to the exhibit.
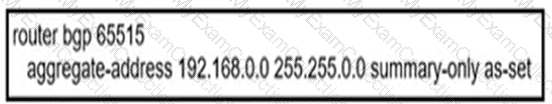
An engineer configured BGP summarization on a customer's network. Which route is advertised to BGP peers?
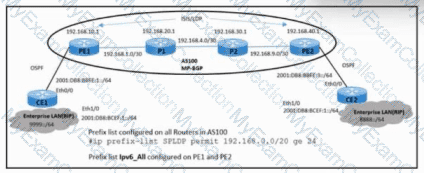
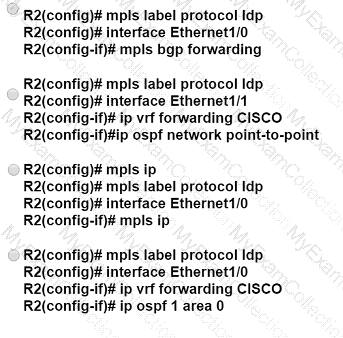
Refer to the exhibit. An engineer must update the configuration of the network with these requirements:
PE routers must define labels for IS-IS learned routes in AS100.
P routers must not receive LDP bindings for the external network in the IPv6 address family.
Which configuration must the engineer implement to meet these requirements?
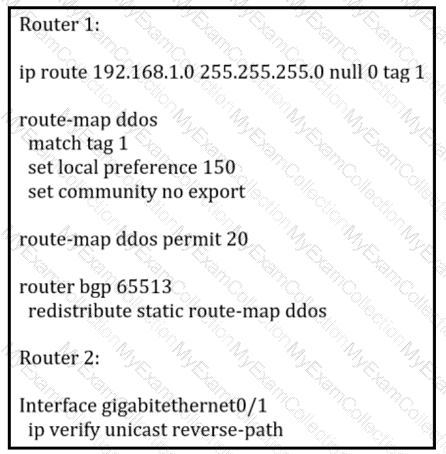
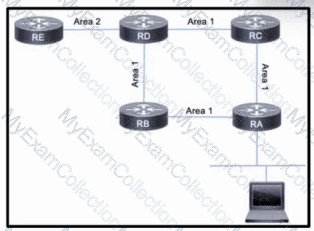
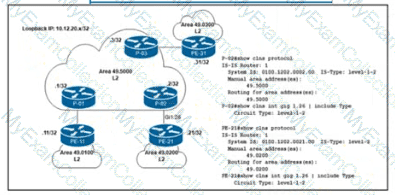
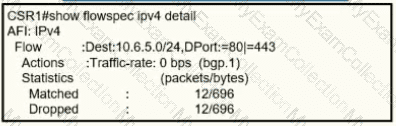
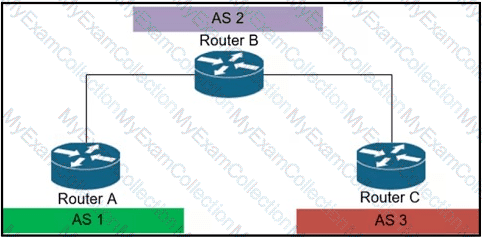
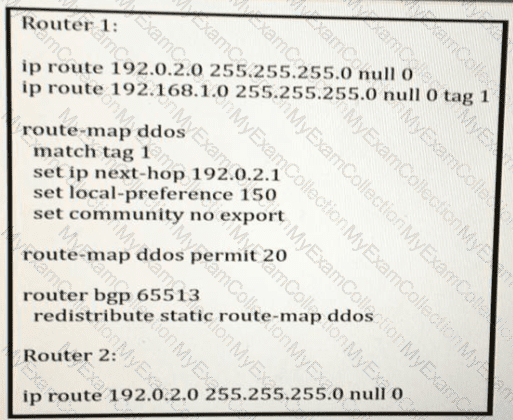
Refer to the exhibit:

Router 1 was experiencing a DDoS attack that was traced to interface gjgabitethernet0/1.
Which statement about this configuration is true?
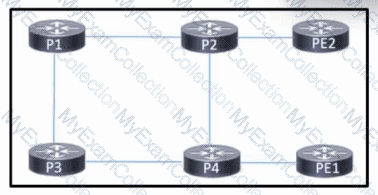
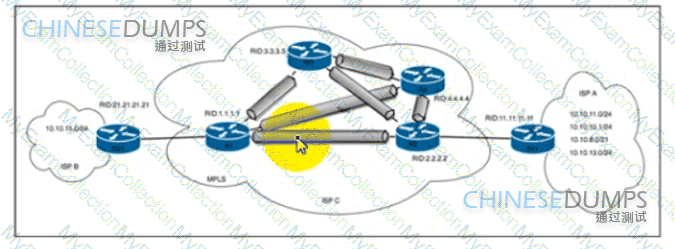
Refer to the exhibit:

P3 and PE4 are at the edge of the service provider core and serve as ABR routers Aggregation areas are on either side of the core.
Which statement about the architecture is true?
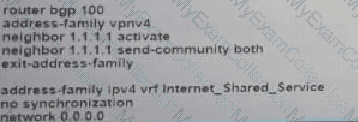
Refer to the exhibit. Which additional configuration must an engineer to the adge router to inject a default router into the MP-BGP address family for the internet_Shared_Services dedicated VRF?
A)
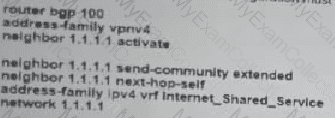
B)
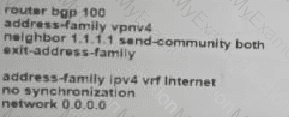
C)
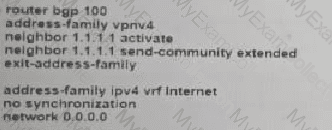
D)
The engineering team at a large ISP has been alerted a customer network is experiencing high traffic congestion. After a discussion between the ISP and technical personnel at the customer site, the team agrees that traffic to the customer network that exceeds a specific threshold will be dropped. Which task must the engineer perform on the network to implement traffic policing changes?
Refer to the exhibit. A service provider is running MPLS in the core to support Layer 3 VPN. OSPF is configured to support dynamic routing, and BGP is enabled throughout the network. A network engineer is adding a new P router to the infrastructure and is connecting it to P1 and P3.
Which task must the engineer perform on the new router to allow it to participate in the Layer 3 VPN?
A network administrator must monitor network usage to provide optimal performance to the network end users when the network is under heavy load. The administrator asked the engineer to install a new server to receive SNMP traps at destination 192.168.1.2. Which configuration must the engineer apply so that all traps are sent to the new server?
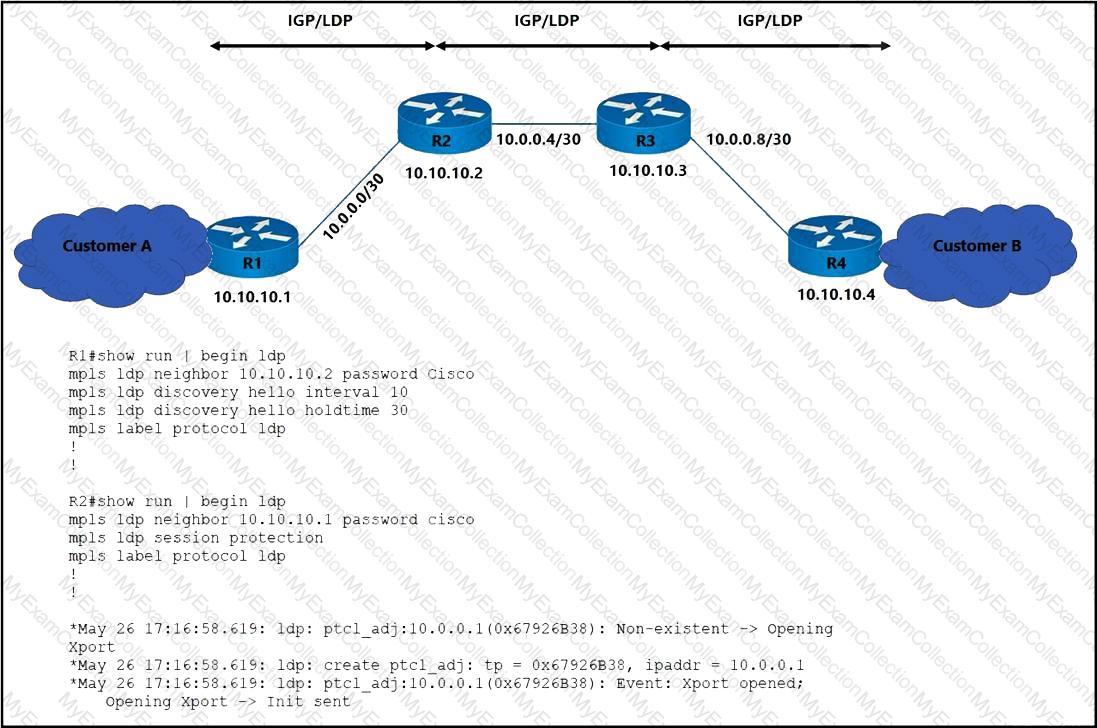
Refer to the exhibit:
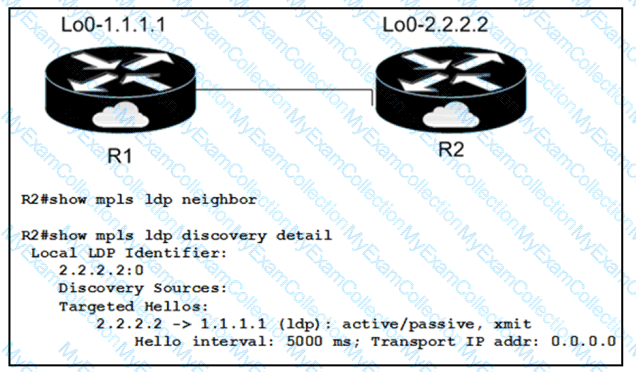
When implementing an LDP protocol, an engineer experienced an issue between two directly connected routers and noticed that no LDP neighbor exists for 1.1.1.1.
Which factor should be the reason for this situation?
What is the primary purpose of the flexible algorithm in a segment-routing environment?
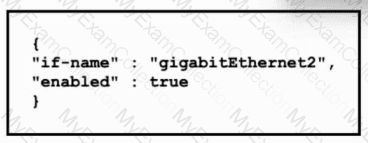
Refer to the exhibit.
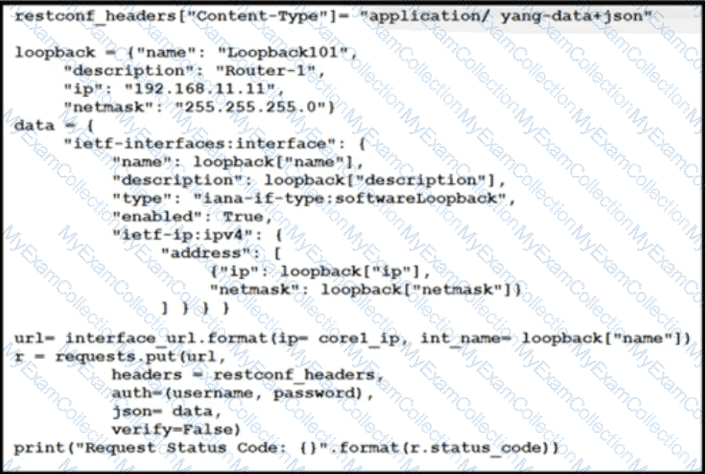
An engineer at a new ISP must configure many Cisco devices in the data center. To make the process more efficient, the engineer decides to automate the task with a REST API. Which action does this JSON script automate?
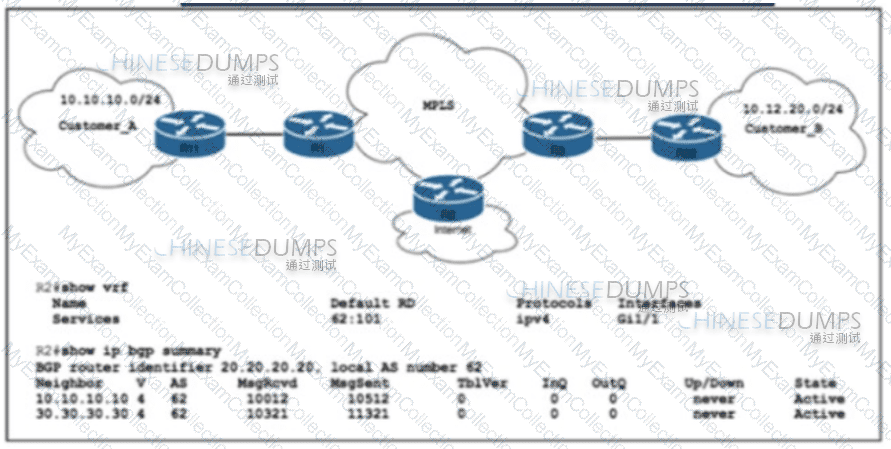
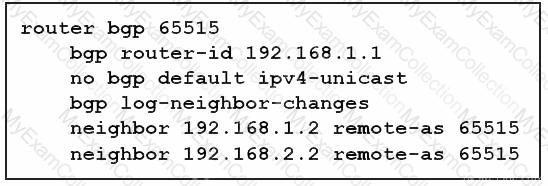
Refer to the exhibit:
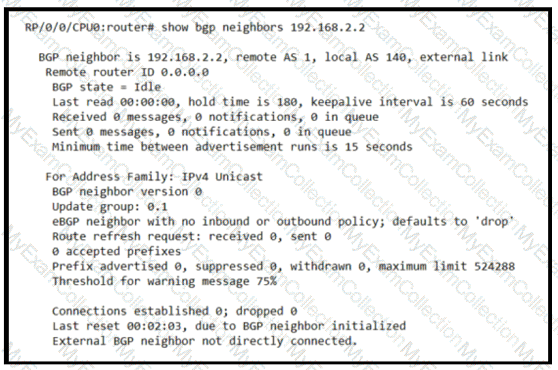
Based on the show/ command output, which result m true after BGP session is established?
Refer to the exhibit. ISP_A is about to launch a new internet service. ISP_A is already providing MPLS VPN Layer 3 services to Customer_A and Customer_B, which are connected to ISP_A via OSPF. A network engineer completed the BGP and VRF configurations on R2 to support the new internet service. Which additional action completed the launch?
Which control plane protocol is used between Cisco SD-WAN routers and vSmart controllers?
Which two IS-IS parameters must match before two Level 2 peers can form an adjacency? (Choose two)
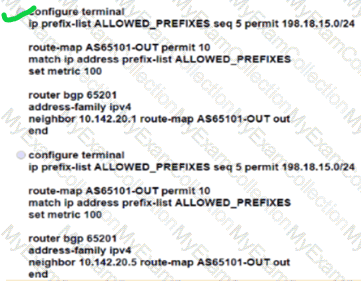
Refer to the exhibit:
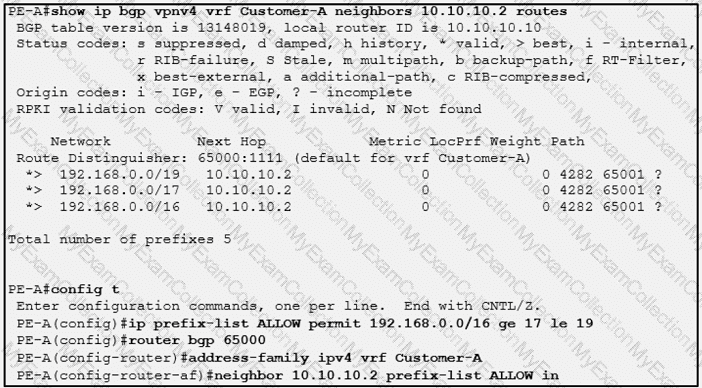
Which three outcomes occur if the prefix list is added to the neighbor? (Choose three)
Which additional configuration is required for NetFlow to provide traceback information?

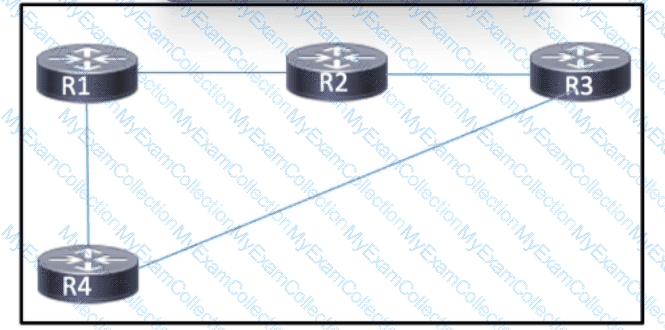
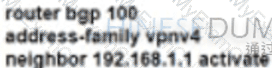
Refer to the exhibit. A network operator working for a private telecommunication company with an employee id: 7138: 13:414 just added new users to the network, which resides in VLANs connected to routers R1 and R4. The engineer now must configure the network so that routers R1 and R4 share routes to the VLANs, but routers R2 and R3 are prevented from including the routes in their routing tables. Which configuration must the engineer apply to R4 to begin implementing the request?
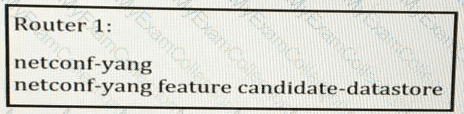
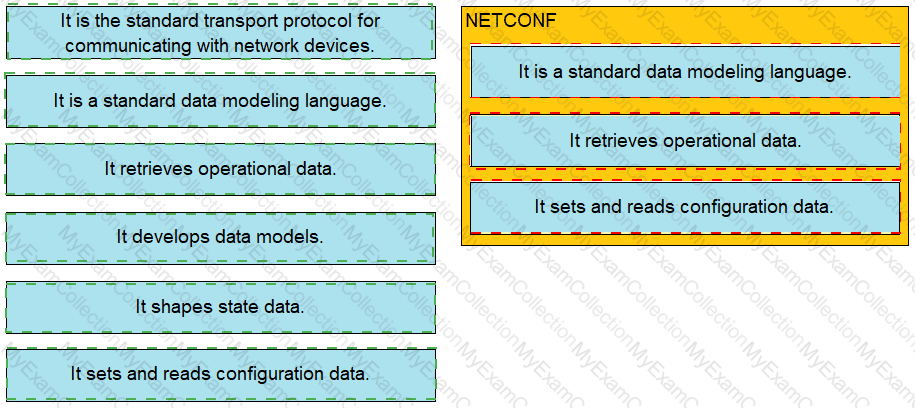
A network engineer is testing an automation platform that interacts with Cisco networking devices via NETCONF over SSH. In accordance with internal security requirements:
NETCONF sessions are permitted only from trusted sources in the 172.16.20.0/24 subnet.
CLI SSH access is permitted from any source.
Which configuration must the engineer apply on R1?
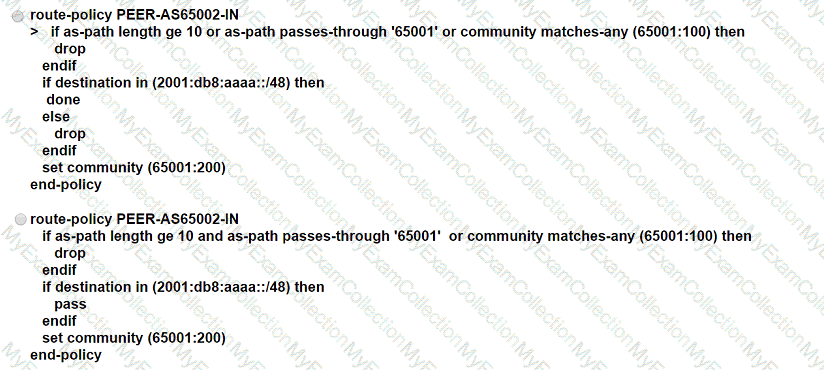
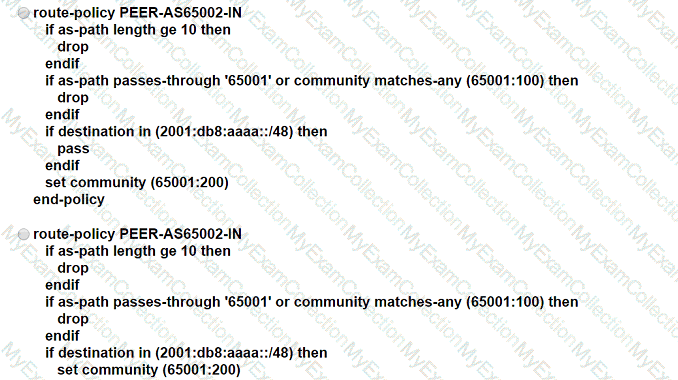
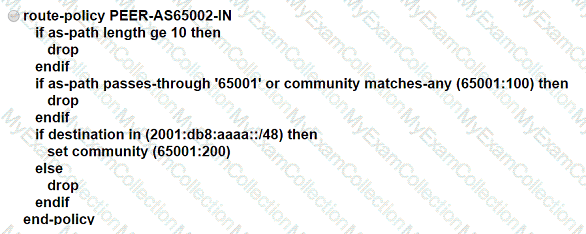
ASN 65001 is peering with ASN 65002 to exchange IPv6 BGP routes. All routes that originate in ASN 65001 have a standard community value of 65001:100, and ASN 65002 is allowed to advertise only 2001 :db8:aaaa::/48. An engineer needs to update the ASN 65001 route-filtering configuration to meet these conditions:
* Looped routes into ASN 65001 and routes that have traversed 10 or more ASNs must be denied.
* Routes accepted into ASN 65001 must be assigned a community value of 65001:200.
Which configuration must the engineer apply to the ASN 65001 border router?
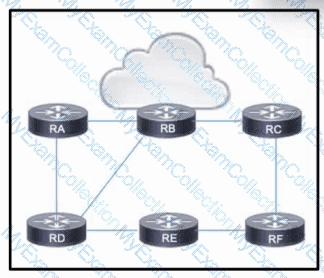
Refer to the exhibit. The network is running OSPF, and access to the internet is provided through router RB. Router RA connects to several servers that provide services to users connected to RC and RF. User traffic is growing, and the engineering team wants to mitigate the future potential for congestion when the servers are experiencing heavy use.
Which action must the team take to maintain better network performance?
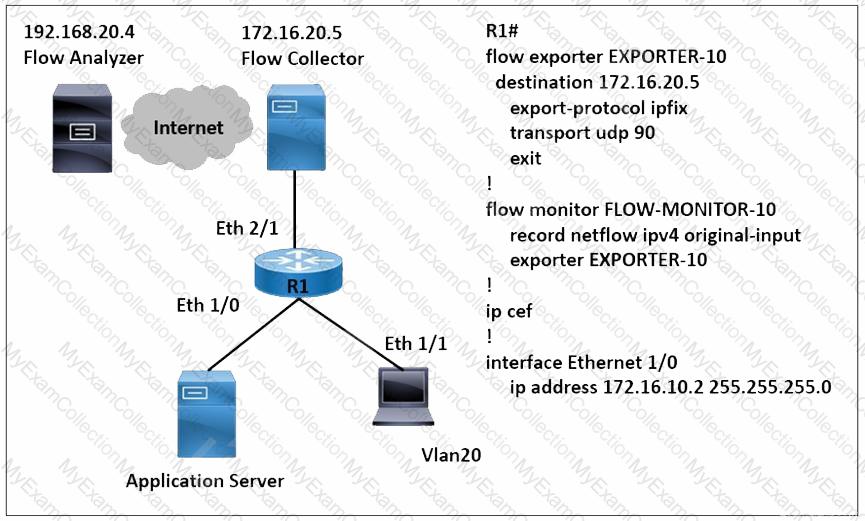
Refer to the exhibit. A network engineer wants to monitor traffic from the application server and send the output to the external monitoring device at 172.16.20.5. Application server traffic should pass through the R1 Eth2/1 interface for further analysis after it is monitored. Which configuration must be applied on the R1 router?
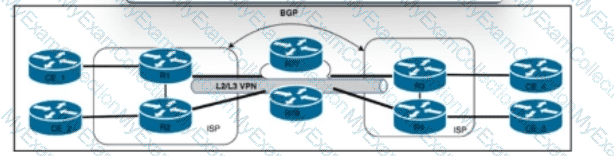
An engineering team must implement Unified MPLS to scale an MPLS network. Devices in the core layer use different IGPs, so the team decided to split the network into different areas. The team plans to keep the MPLS services as they are and introduce greater scalability. Which additional action must the engineers take to implement the Unified MPLS?
Guidelines -
This is a lab item in which tasks will be performed on virtual devices.
• Refer to the Tasks tab to view the tasks for this lab item.
• Refer to the Topology tab to access the device console(s) and perform the tasks.
• Console access is available for all required devices by clicking the device icon or using the tab(s) above the console window.
• All necessary preconfigurations have been applied.
• Do not change the enable password or hostname for any device.
• Save your configurations to NVRAM before moving to the next item.
• Click Next at the bottom of the screen to submit this lab and move to the next question.
• When Next is clicked, the lab closes and cannot be reopened.
Topology:
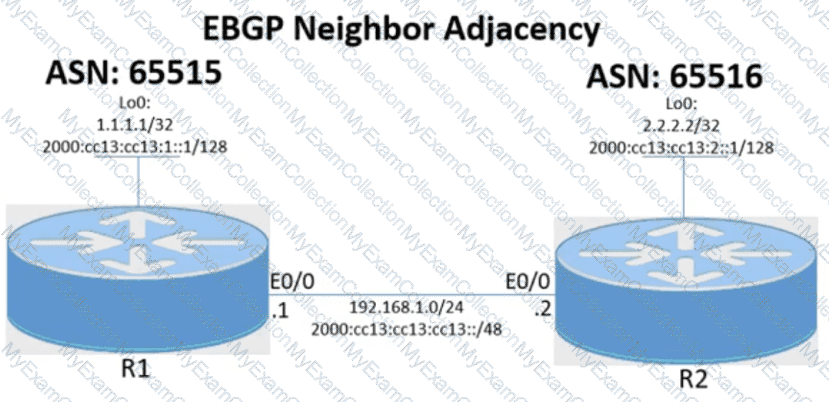
Tasks -
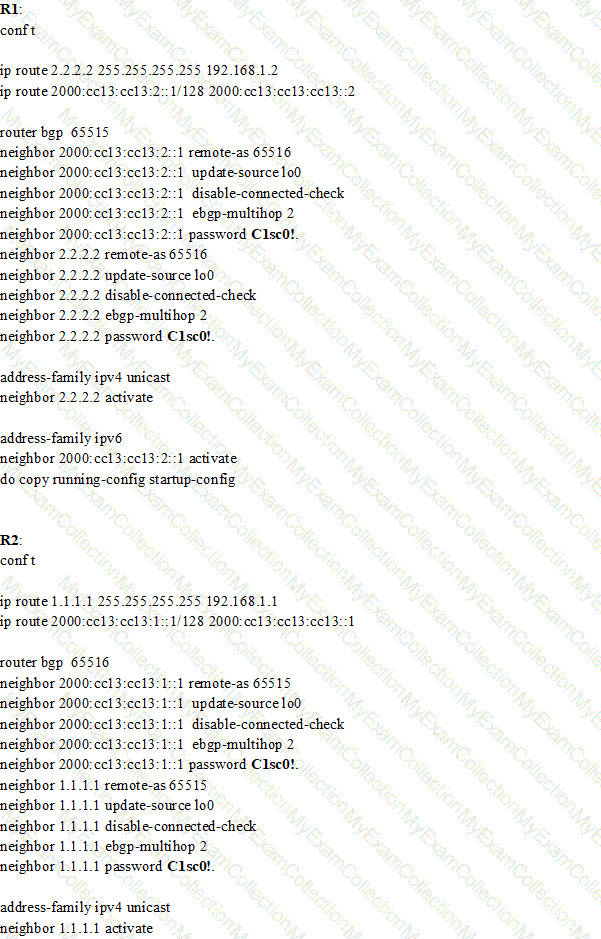
Configure the BGP routing protocol for R1 and R2 according to the topology to achieve these goals:
1. Configure EBGP neighbor adjacency for the IPv4 and IPv6 address family between R1 and R2 using Loopback0 IPv4 and IPv6 addresses. All BGP updates must come from the Loopback0 interface as the source. Do not use IGP routing protocols to complete this task.
2. Configure MD5 Authentication for the EBGP adjacency between R1 and R2. The password is clear text C1sc0!.
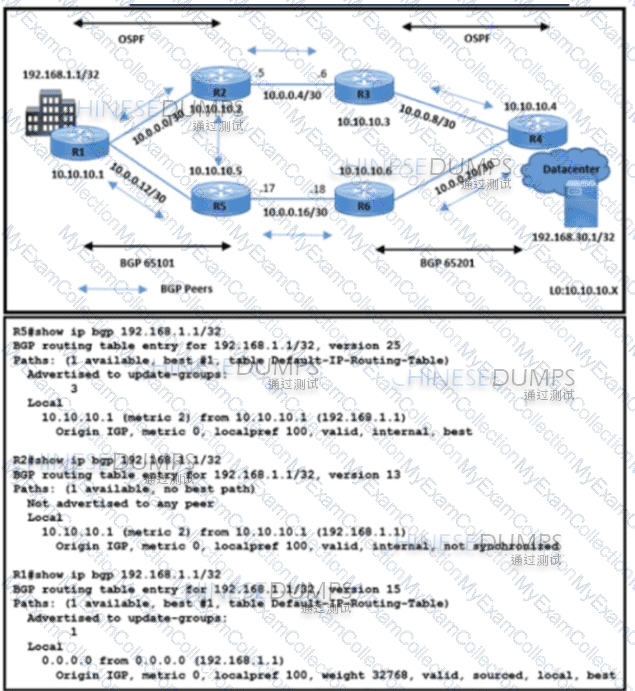
Refer to the exhibit. All BGP peering in AS 65101 and 65201 is enabled. The operations team is told that traffic destined to 192.168.1.1/32 from R4 does not use the path R3-R2-R1 as expected. An engineer debugs the issue and determines that 192.168.1.1/32 is advertised in the BGP routing table on R1. Which action resolves the issue?
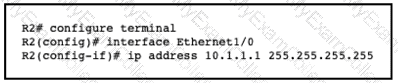
Refer to the exhibit.
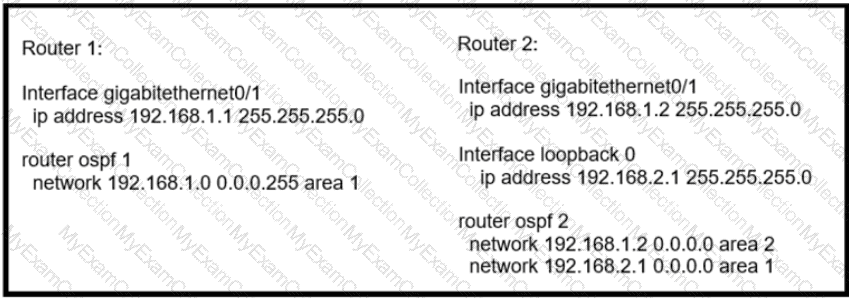
Router 1 is missing the route for the router 2 loopback 0. What should the engineer change to fix the problem?
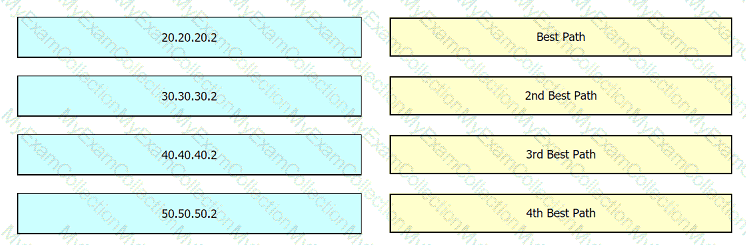
Refer to the exhibit.
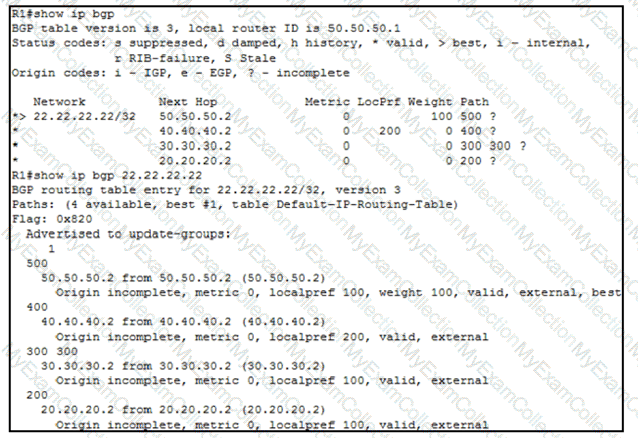
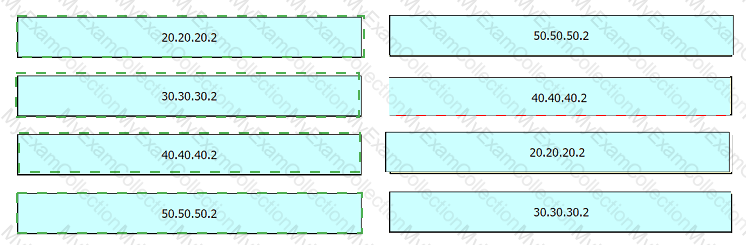
An engineer wants to determine which paths are best, second best, third best, and fourth best. Drag and drop the peer addresses on the left to the corresponding BGP best-path selection order on the right.
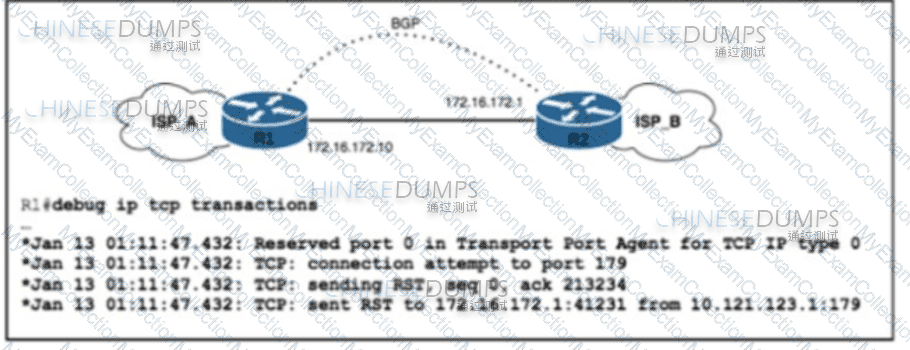
Refer to the exhibit. ISP_A and ISP_B use AS numbers 38321 and 16213 respectively. After a network engineer reloaded router R1, the BGP session with R2 failed to establish. The engineer confirmed BGP next-hop availability with a connectivity test between the router loopback addresses 10.121.123.2 and 10.121.123.1, as well as between interfaces Gi1/1 and Gi1/2. EBGP multihop has been configured on both routers. Which action must the engineer take to resolve the issue?
Refer to the exhibit.
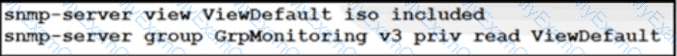
A network engineer must implement SNMPv3 on a Cisco IOS XR router running BGP. The engineer configures SNMPv3 to use SHA for authentication and AES for privacy on the routers, which are in a different data center in the same exchange as other routers. The engineer must also verify the associated MIB view family name, storage type, and status. Which set of actions meets these requirements?
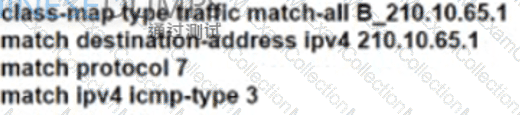
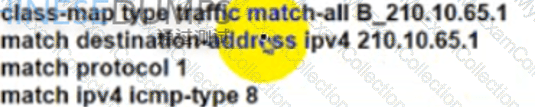
Refer to the exhibit. ISP A provides VPLS services and DDoS protection to Company XYZ to connect their branches across the North America and Europe regions. The uplink from the data center to the ISP is Mbps. The company XYZ security team asked the ISP to redirect ICMP requests which are currently going to the web server to a new local security appliance which configuration must an ISPP engineer apply to router R2 to redirect the ICMP traffic?
A)
B)
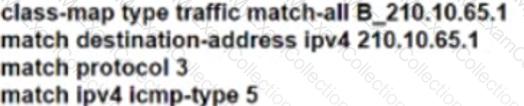
C)
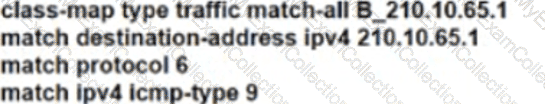
D)
After a possible security breach, the network administrator of an ISP must verify the times that several different users logged into the network. Which command must the administrator enter to display the login time of each user that activated a session?
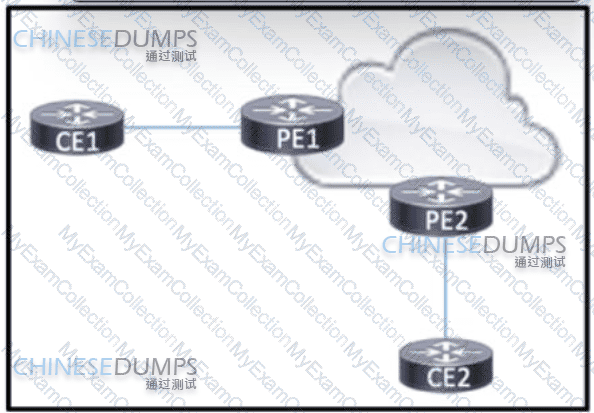
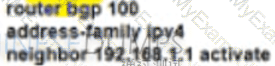
Refer to the exhibit BGP is running in the core of the service provider to exchange routes for its customers, and OSPF serves as the PE-CE routing protocol. The service provider s existing customer at CE1 is opening a new office in a different geographical location connected via CE2. A network engineer must update the BGP implementation so that PE1 and PE2 will share routes and provide communication between CE1 and CE2 Which action must the engineer take?
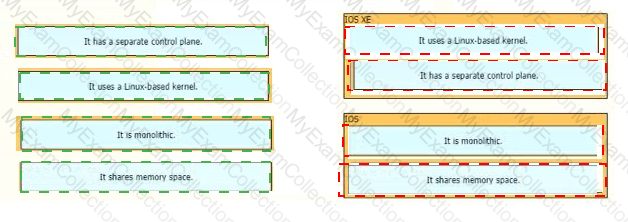
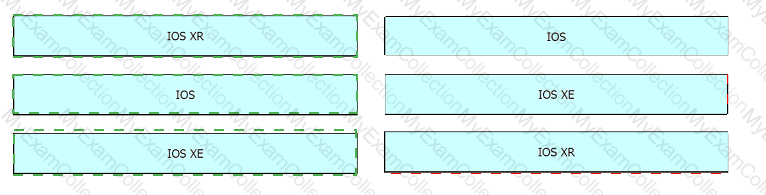
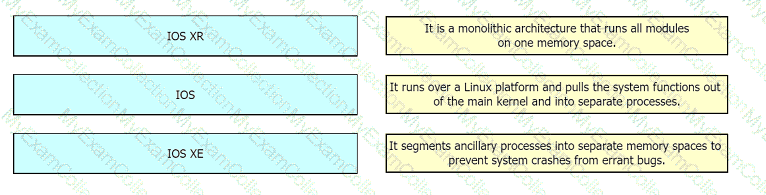
Drag and drop the descriptions from the left onto the corresponding OS types on the right.

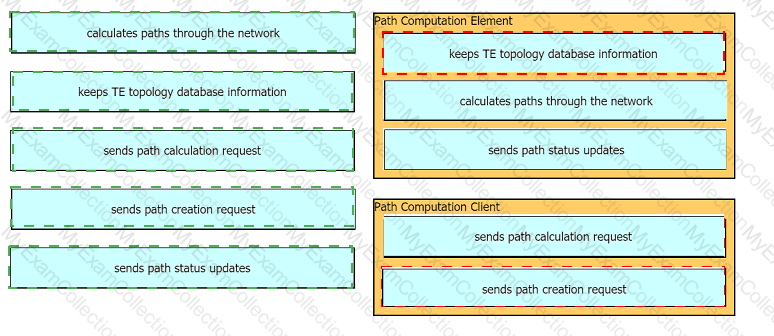
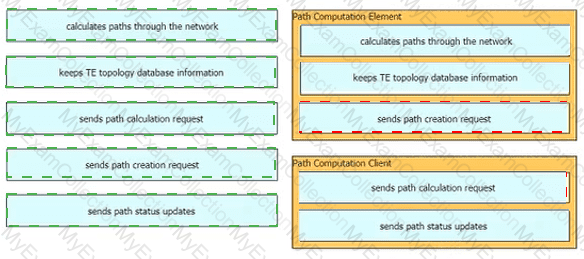
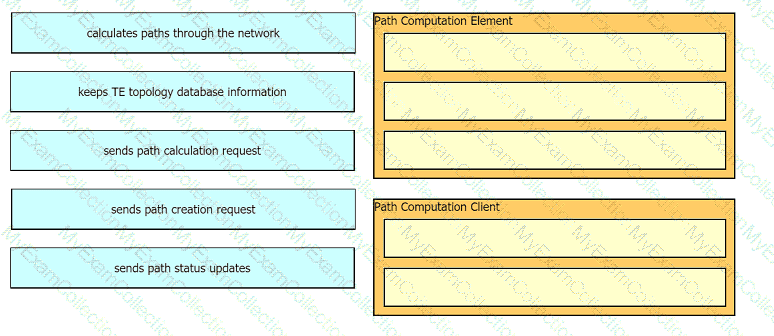
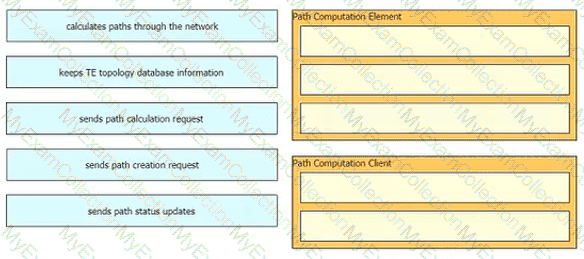
Drag and drop the functions from the left onto the Path Computation Element Protocol roles on the right.

Refer to the exhibit. Which part of the diagram will host OpenStack components?
Which feature will an operator use while implementing MPLS TE on customer's network, to prevent an LSP from using any overseas inks?
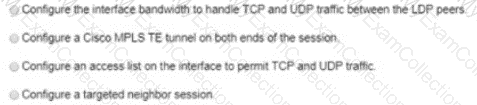
An engineer a cisco MPLS tunnel to improve the streaming experience for the clients of a video -on-demand server. Which action must the engineer perform to configure extended discovery to support the MPLS LDP session between the headend and tailend routers?
An engineer needs to implement QOS mechanism on customer's network as some applications going over the internet are slower than others are. Which two actions must the engineer perform when implementing traffic shaping on the network in order to accomplish this task? (Choose two)
Refer to the exhibit:
This configuration is being applied on an IOS XR router.
Which statement about this configuration is true?
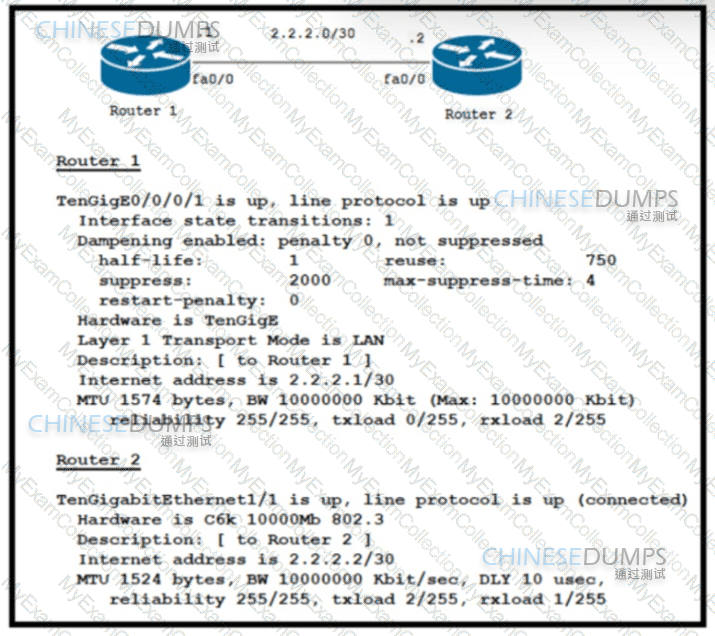
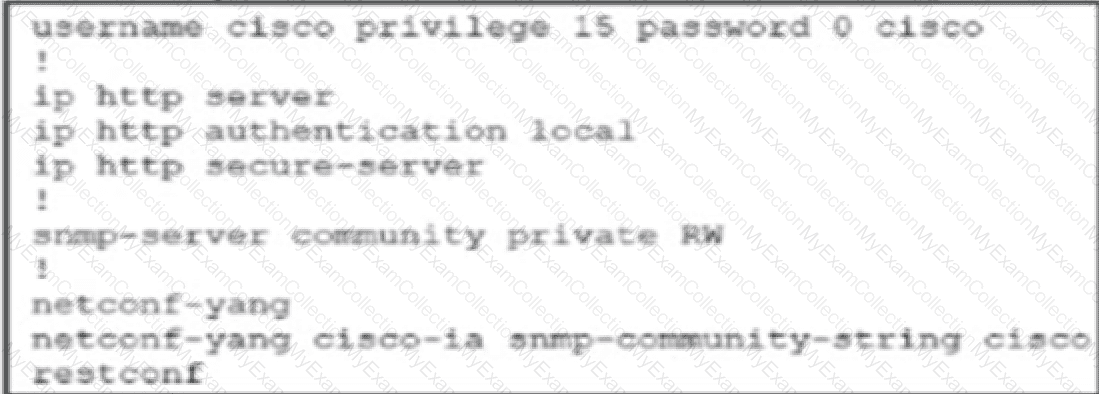
Refer to the exhibit:
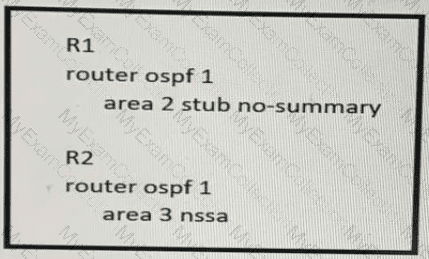
In which way does router R1 operate differently than router R2?
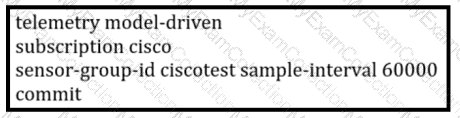
A service provider requires continuous real-time network monitoring to provide reliable SLAs to its customers. To satisfy this requirement, a network administrator is implementing gRPC dial out on an ASR with TLS. Receiver 192.168.10.2 will be assigned one of the subscriptions, and it will manage the ASR. Which configuration must the engineer apply to the router as part of the configuration process?
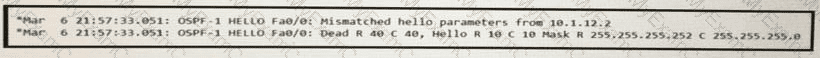
Refer to the exhibit An engineer at ISP C is configuring a new interconnection with ISPs A and B using the BGP protocol After the initial configuration the engineer noticed high memory usage and an abnormally large LIB table on router R2 Which two actions must the engineer take on R2 to minimize memory usage? (Choose two.)

Refer to the exhibit. Customers report occasional forwarding issues from hosts connected to R6 to hosts connected to R1. A network engineer has just updated the MPLS configuration on the network, and a targeted LDP session has been established between R1 and R5. Which additional task must the engineer perform so that the team can identify the path from R6 to R1 in case the forwarding issues continue?
The service provider is serving hosts with two different multicast streams from source X and source Y. Source X is multicast group 224.0.0.0/8, and source Y is multicast group 226.0.0.0/8. Multicast source X should send its stream through bidirectional RP address 10.20.1.1, and multicast source Y should send its stream through RP address 10.20.2.1. Which configuration meets these requirements?
Refer to the exhibit:
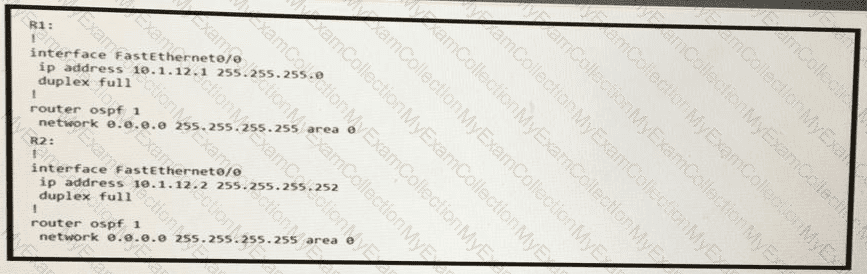
R1 and R2 are directly connected with Fast Ethernet interfaces and have the above configuration applied OSPF adjacency is not formed. When the debug ip ospf hello command is issued on R1. these log messages are seen.
Which command can be configured on routers R1 and R2 on fO/O interfaces to form OSPF adjacency?
Refer to the exhibit. Company A's network architect is implementing the capabilities that are described in RFC 4379 to provide new options for troubleshooting the company's MPLS network. MPLS LSPs are signaled via the BGP routing protocol with IPv4 unicast prefix FECs. Due to company security policies, access is controlled on the control plane and management plane. Which two tasks must the architect perform to achieve the goal? (Choose two.)
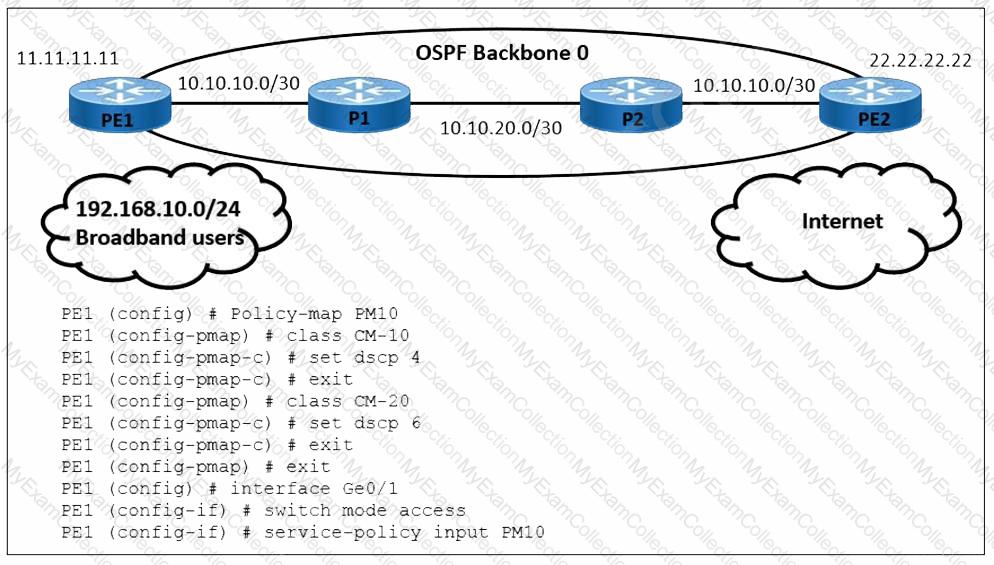
Refer to the exhibit A user is performing QoS marking on internet traffic and sending it with IPv4 and IPv6 headers on the provider edge device PE1. IPv4 traffic is classified with DSCP 4 and IPv6 traffic is classified with DSCP 6. Which action must the engineer take to begin implementing a QoS configuration on PE1 for the IPv6 traffic?
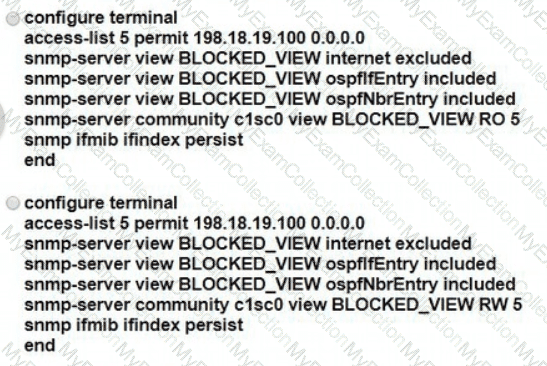
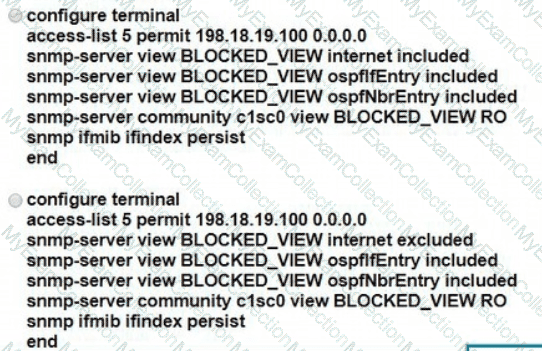
A network engineer must implement SNMPv2 with these parameters
Enable SNMP community string C1sc0 with read-only permissions.
Enable interface index persistence.
Restrict the SNMP community to only the monitoring server with IP address 198.18 19 100/32.
Provide view-only access to ospflfEntry and ospfNbrEntry.
Which configuration must the engineer apply?
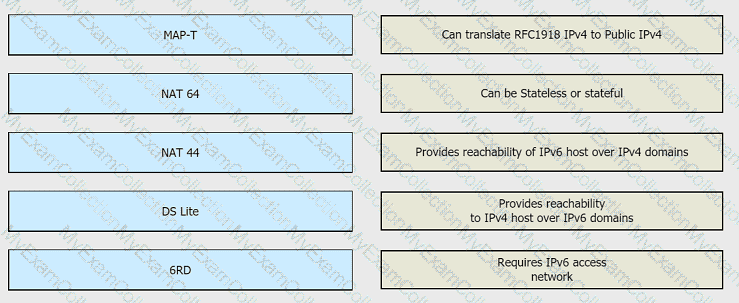
Drag and drop the functionalities from the left onto the correct target fields on the right.

Guidelines
-
This is a lab item in which tasks will be performed on virtual devices.
• Refer to the Tasks tab to view the tasks for this lab item.
• Refer to the Topology tab to access the device console(s) and perform the tasks.
• Console access is available for all required devices by clicking the device icon or using the tab(s) above the console window.
• All necessary preconfigurations have been applied.
• Do not change the enable password or hostname for any device.
• Save your configurations to NVRAM before moving to the next item.
• Click Next at the bottom of the screen to submit this lab and move to the next question.
• When Next is clicked, the lab closes and cannot be reopened.
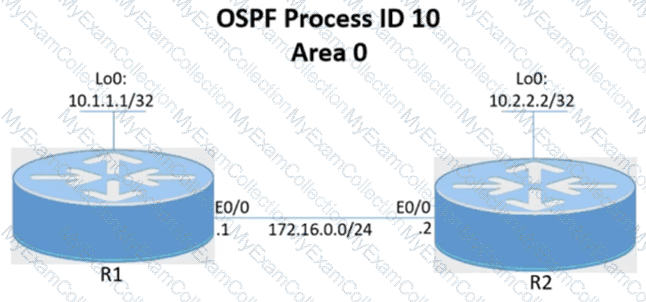
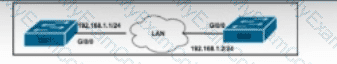
Topology
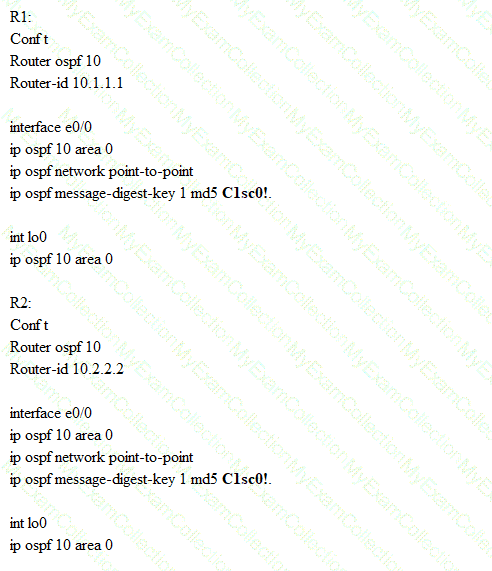
Tasks
-
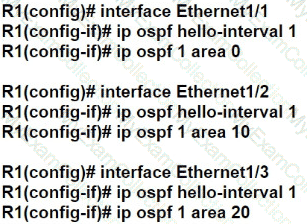
Configure and verify the OSPF neighbor adjacency between R1 and R2 in OSPF area 0 according to the topology to achieve these goals:
1. Establish R1 and R2 OSPF adjacency. All interfaces must be advertised in OSPF by using the OSPF interface command method. Use Loopback0 as the OSPF ID.
2. There must be no DR/BDR elections in OSPF Area 0 when establishing the neighbor relationship between R1 and R2. OSPF must not generate the host entries /32 for the adjacent interfaces.
3. Enable OSPF MD5 Authentication between both routers at the interface level with password C1sc0!.
Refer to the exhibit.
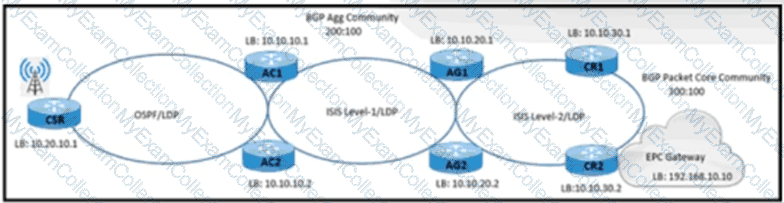
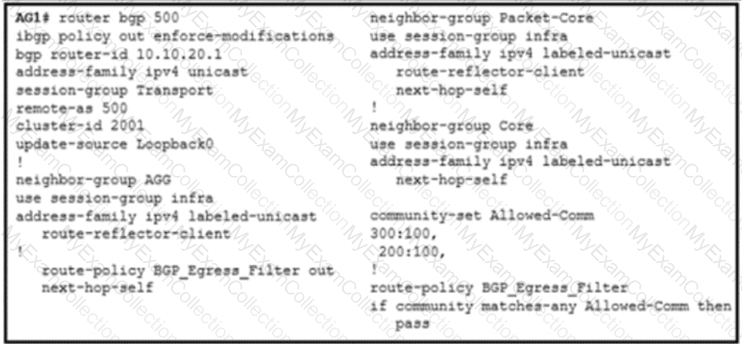
A NOC engineer is configuring label-based forwarding from CSR to the EPC gateway. Cell-site operation and maintenance for IPv4 traffic between 10.20.10.1 and 192.168.10.10 is already up. CR1 and CR2 are configured as route reflectors for AG1 and AG2. Which action completes the configuration?
While an engineer deploys a new Cisco device to redistribute routes from OSPF to BGP, they notice that not all OSPF routes are getting advertised into BGP. Which action must the engineer perform so that the device allows O, OIA, OE1, and OE2 OSPF routes into other protocols?

Refer to the exhibit. A large enterprise has multiple branch offices that span several geographic regions. The enterprise runs MPLS within the core to propagate VPNv4 routes using BGP. After a recent series of DDoS attacks disrupted the network, a network engineer has been asked to reconfigure BGP to help mitigate future attacks. Which configuration must the engineer apply?
A)

B)
C)
D)
Refer to the exhibit: 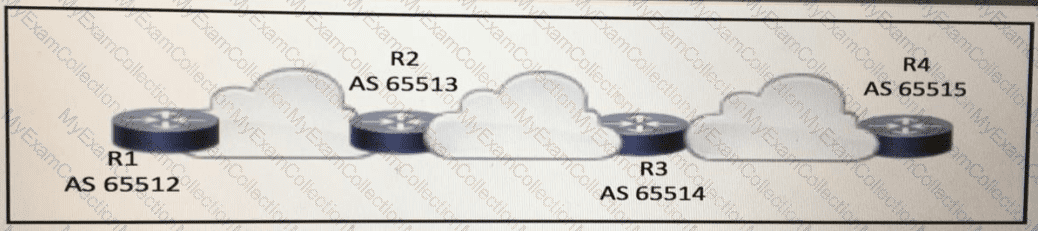
BGPsec is implemented on R1. R2. R3. and R4 BGP peering is established between neighboring autonomous systems Which statement about implementation is true?
An engineer Is implementing NSR with OSPF on a large campus that requires high availability. Which task must an engineer perform to complete the process with minimal disruption to traffic?
Refer to the exhibit. A client wants to filter routes to a BGP peer to limit access to restricted areas within the network. The engineer configures the route map ciscotest to filter routes from the BGP neighbor. The engineer also sets a tag that will be used for QoS in the future. Which task must be performed to complete the Implementation?
Which two tasks must you perform when you implement LDP NSF on your network? (Choose two.)
R1 serves as a route reflector on a BGP-enabled network and has dual RPs installed. To ensure that all routes have been processed when an RP fails over, R1 must send the router request to all peers configured with NSR to refresh the route database. Which action completes the implementation?
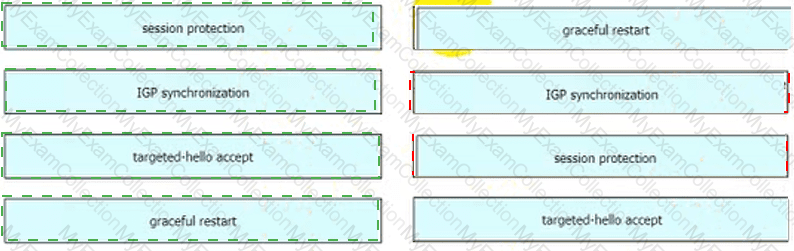
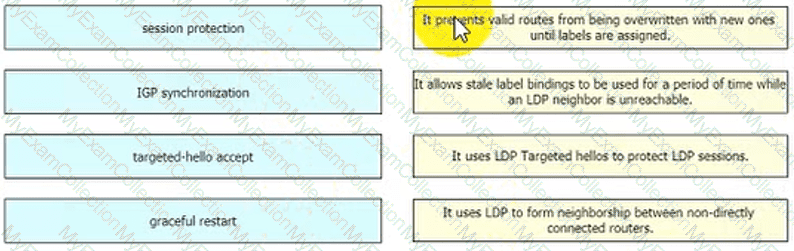
Drag and drop the LDP features from the left onto their usages on the right.
Refer to the exhibit:
This output is included at the end of an output that was provided by a device using NETCONF.
What does the code show?
Refer the exhibit.
Users on a network connected to router R3 report slow speeds when they connect to the server connected to R2. After analyzing traffic on the network, a network engineer identified congestion on the link between R2 and R3 as the cause. Which QoS service must the engineer implement to drop traffic on the link when it exceeds a configured threshold?
A new PE router is configured to run OSPF as an IGP with LDP on all interfaces. The engineer is trying to prevent black holes after convergence when the PERSON device loses an LDP session with other PE routers. Which action must the engineer take to implement LDP session protection on a new PE router?
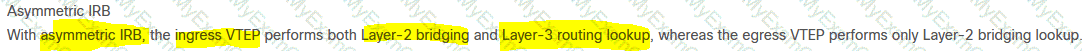
Which action does the ingress VTEP perform on traffic between EVPN VXLAN overlays?
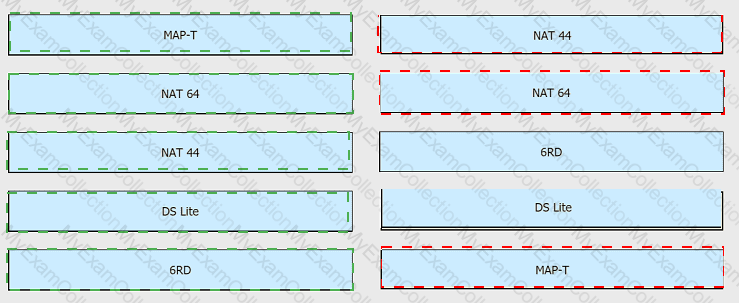
Refer to the exhibit.
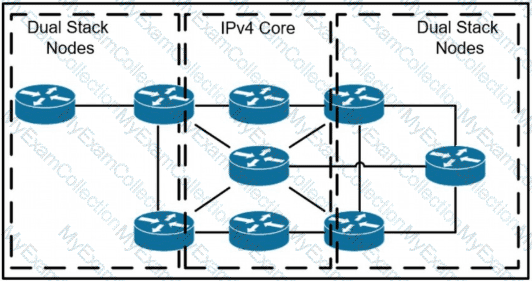
A network operator has two IPv4 and IPv6 dual-stacked network on each side of the IPv4 core network. The operator must be able to provide connectivity between them while using specific assigned IPv6 space provided from the company IP administrator team. Which technology should the network operator use to accomplish this goal?
What occurs when a high bandwidth multicast stream is sent over an MVPN using Cisco hardware?
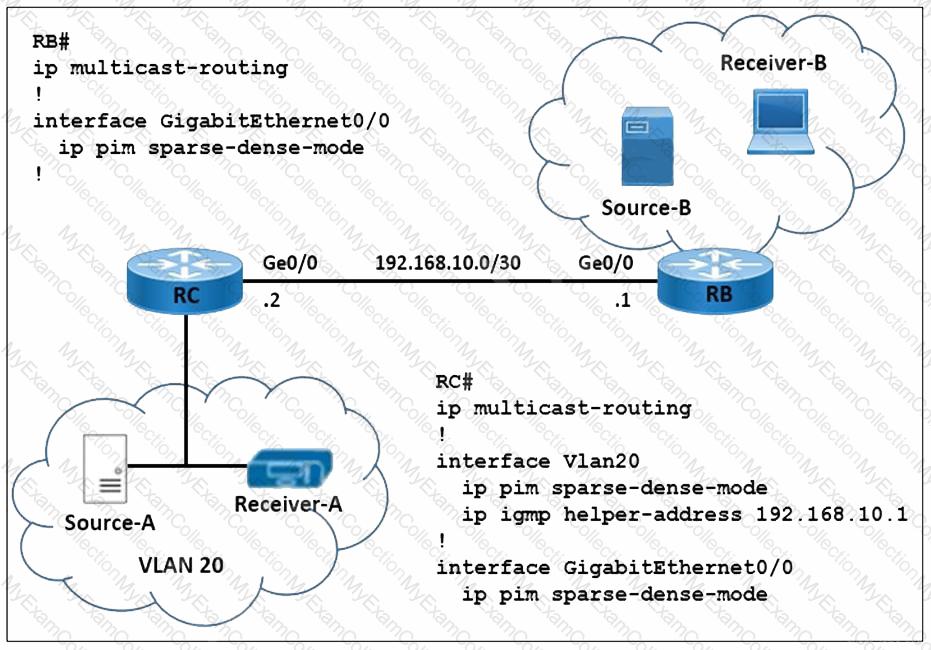
Refer to the exhibit. A network engineer is implementing multicast Source-A to send a multicast stream for Receiver-A, and multicast Source-B to send a multicast stream for Receiver-B. Router RC forwards the IGMP host a report and leaves messages to IP address 192.168.10.1. How must the multicast features be implemented to prevent RB from receiving multicast flooding from Source-A?
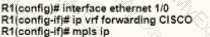
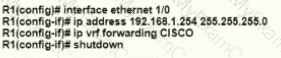
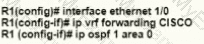
A network engineer is deploying VRF on ASBR router R1. The interface must have connectivity over an MPLS VPN inter-AS Option AB network. Which configuration must the engineer apply on the router to accomplish this task?
A)
B)
C)
D)
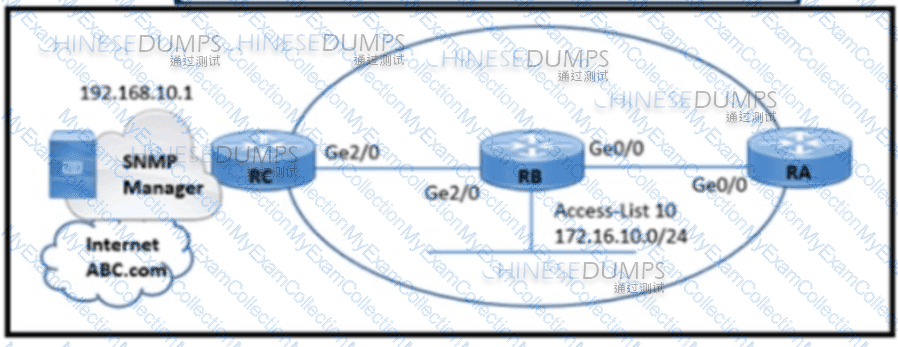
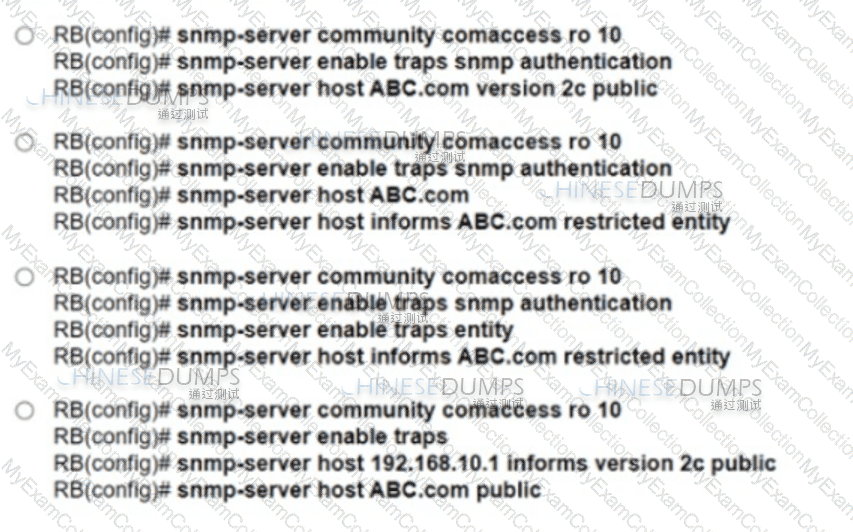
Refer to the exhibit. A network engineer is configuring an SNMP community on router RB with these requirements:
Allow read-only access for all objects to members of Access-List 10 that use the comaccess community string.
Other SNMP managers must not have access to objects.
SNMP authentication failure traps must be sent to SNMPv2c and then to the host using SNMPv2c with the public community string.
Which configuration meets these requirements?
Drag and drop the OSs from the left onto the correct deceptions on the right.
Refer to the exhibit:
An engineer is preparing to implement data plane security configuration.
Which statement about this configuration is true?
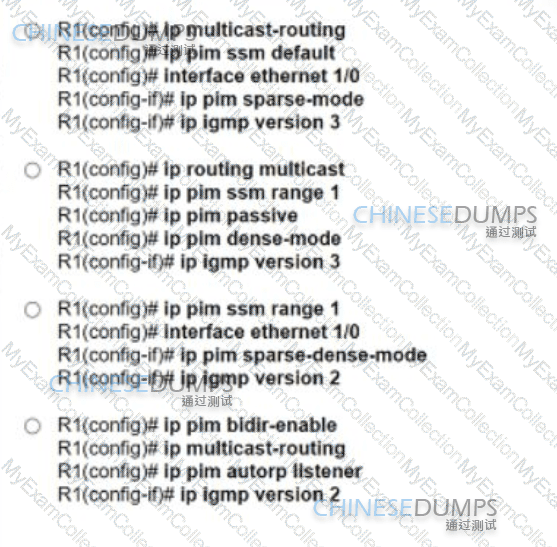
A network operator with an employee ID 4531 26:504 must implement a PIM-SSM multicast configuration on the customer's network so that users in different domains are able to access and stream live traffic. The IGMP version must be enabled to support the SSM implementation. Which action must the engineer perform on R1 to complete the SSM implementation?
What is a primary benefit of IPoATM or MPLS over ATM backbone service provider networks?
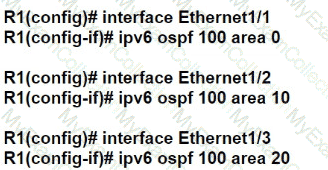
Refer to the exhibit.
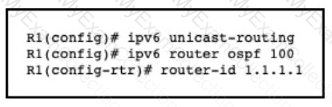
An engineer is configuring router R1 for OSPFv3 as shown. Which additional configuration must be performed so that the three active interfaces on the router will advertise routes and participate in OSPF IPv6 processes?
A)
B)
C)
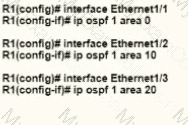
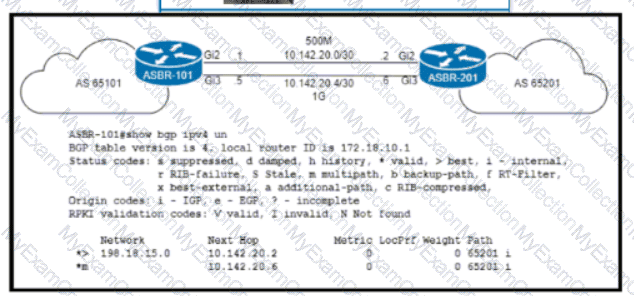
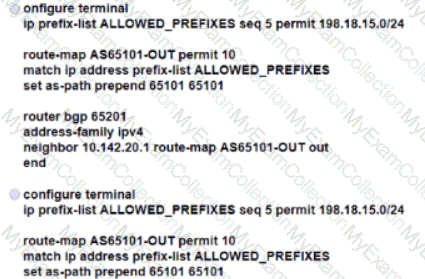
Refer to the exhibit an engineer working for a private telecommunication company with an employee Id: 4065:96:080 upgrades the WAN link between routers ASBR-101 and ASBR-201 to 1Gb by Installing a new physical connection between the Gi3 Interfaces. Which BGP attribute must the engineer configure on ASBR-201 so that the existing WAN link on Gi2 Is maintained as a backup?
Drag and drop the characteristics from the left onto the automation tool on the right.
Refer to the exhibit. Router 1 and Router 2 were installed in the data center. Router 1 is the core router in the network, but it fails to establish an OSPF peering with Router 2. and customer traffic is unable to pass. Router 1 also reports an increase in CPU and memory usage. However, the CPU for R2 is stable. Which action resolves this issue?
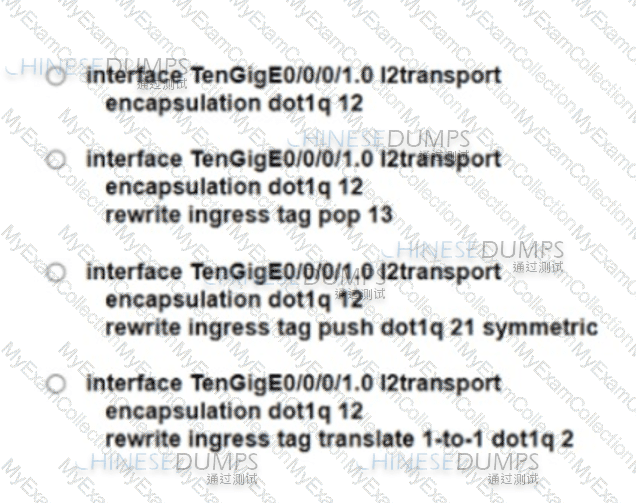
A mod-size service provider uses L2VPN as its standard for connectivity between offices. A small company wants the service provider to connect the company’s two sites across the service provider core. To meet service requirements, the service provider must extend the layer 2 domain between the company’s two locations. Which configuration must the engineer apply to implement an attachment circuit between the two sites using a VLAN tag of 12?
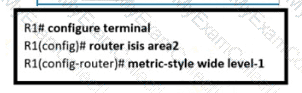
Refer to the exhibit.
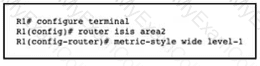
An engineer is configuring multitiopology IS-IS for IPv6 on router R1. Which additional configuration must be applied to complete the task?
A)
B)
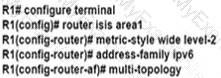
C)
D)
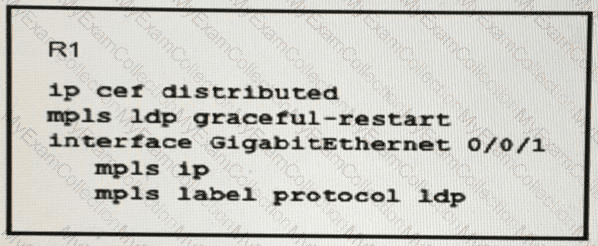
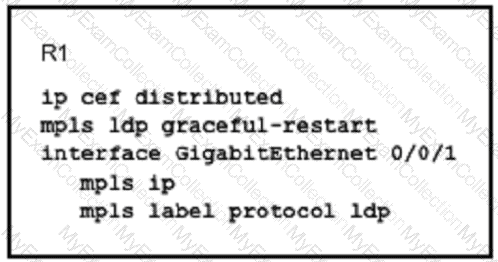
A router is configured to perform MPLS LDP graceful restart.
Which three steps are included when the RP sends an LDP initialization to a neighbor to establish an LDP session? (Choose three)
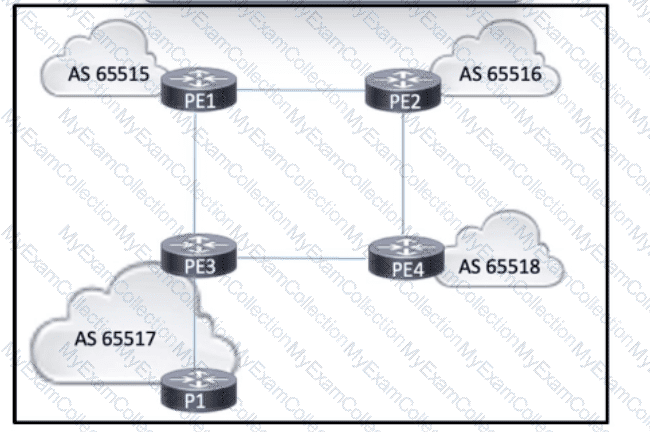
Refer to the exhibit. AS 65517 is running OSPF within the core. BGP is running between all four autonomous systems, interconnecting several ISPs that provide intranet and extranet services. All of the PE routers are connected, and eBGP peering relationships have been established. A network engineer also configured an iBGP peering between PE3 and P1, and the peering is up. However, P1 cannot reach routes outside of AS 65517. Which action must the engineer take so that P1 reaches external routes?)
A network engineer is configuring a router to send multicast traffic for the 239.10.10.10 group. Which configuration must an .... forward the traffic?
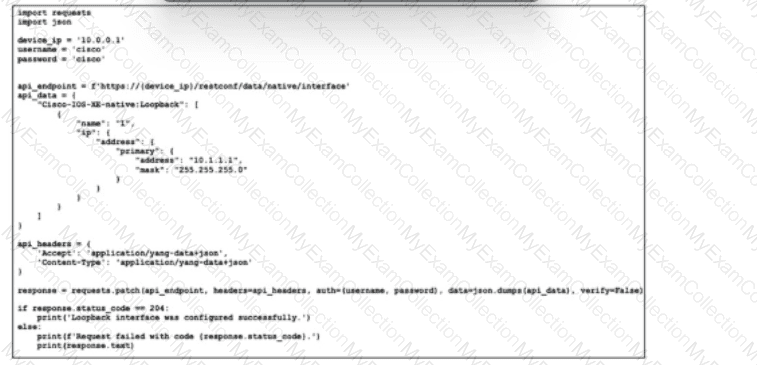
Refer to the exhibit. An operations team recently located an archive of scripts for deploying routine network changes with an error-free approach. A junior network engineer, who is working to modify the scripts to support RESTCONF, has been asked to document the purpose of each updated script. Which two actions does the given script take? (Choose two.)
Refer to the exhibit. A network engineer is configuring a new router for iBGP to improve the capacity of a growing network. The router must establish an iBGP peer relationship with its neighbor. The underlay network is already configured with the correct IP addresses. Which step should the engineer apply to complete this task?
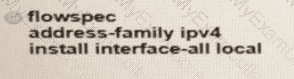
Which configuration enables BGP FlowSpec client function and installation of policies on all local interfaces?
A)
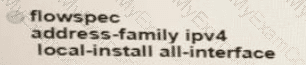
B)
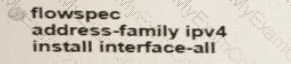
C)
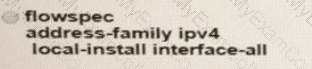
D)
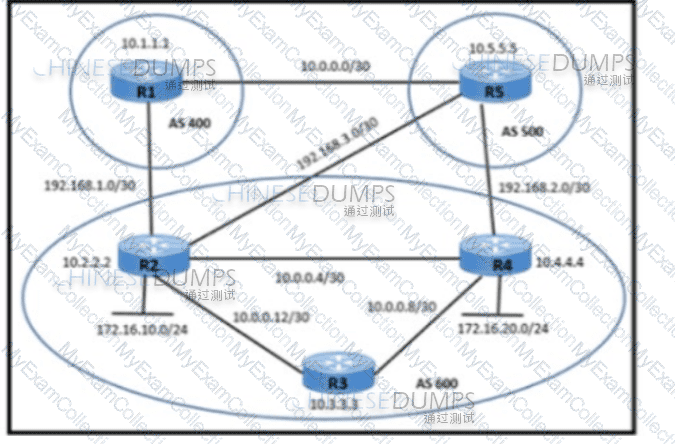
Refer to the exhibit. A network engineer is implementing iBGP and eBGP between AS 600 and AS 500 with these requirements:
R2 must establish eBGP peering on 192.168.3.0/30 with R5 for sending unicast and multicast traffic
R2 must wait for 30 seconds before sending BGP updates to R5 for multicast traffic.
Which action must be taken on R2 to meet the requirements?
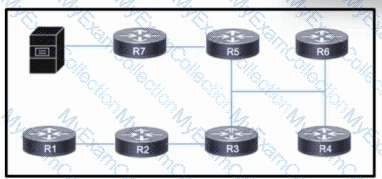
Refer to the exhibit. The network is configured with OSPF. A networking team just connected a streaming multicast server to router R7, and they now must enable access for users throughout the network to stream video from the server.
Which action must the team take so that users can stream video without overloading the network?
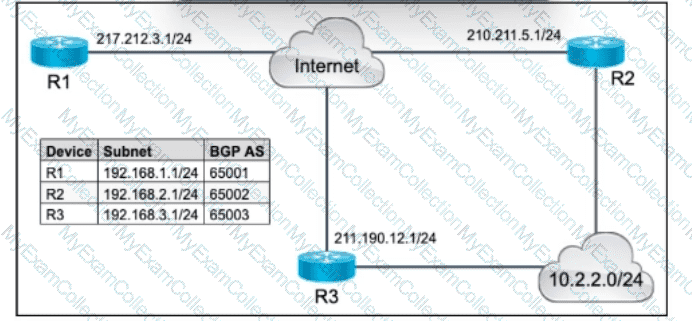
Refer to the exhibit. A growing company wants to ensure high availability and redundancy for its critical web servers, which are located in an offsite data center. The network architect decided to implement BGP so that the network can use redundant paths for outbound traffic toward the destination subnet 10.2.2.0/24. A network engineer already configured basic BGP settings on edge router R1, which is a Cisco ASR-1001X router. The engineer also confirmed loopback reachability to routers R2 and R3, and the AS path length toward the destination is the same via R2 and R3. Which action must the engineer take on R1 to complete the implementation?
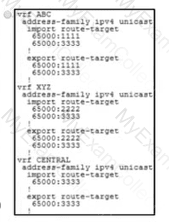
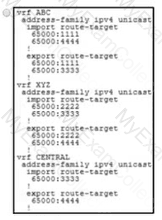
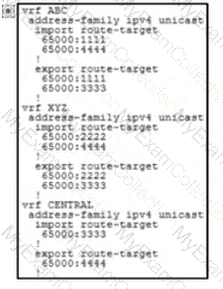
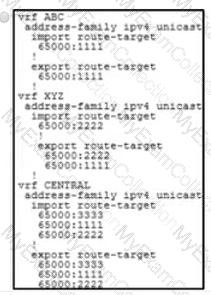
An engineer is setting up overlapping VPNs to allow VRF ABC and XYZ to communicate with VRF CENTRAL but wants to make sure that VRF ABC and XYZ cannot communicate. Which configuration accomplishes these objectives?
Refer to the exhibit:
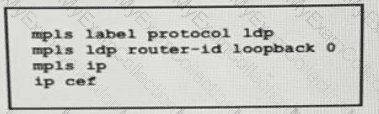
A network operator working for service provider with an employee id 3715 15:021 applied this configuration to a router.
Which additional step should the engineer use to enable LDP?
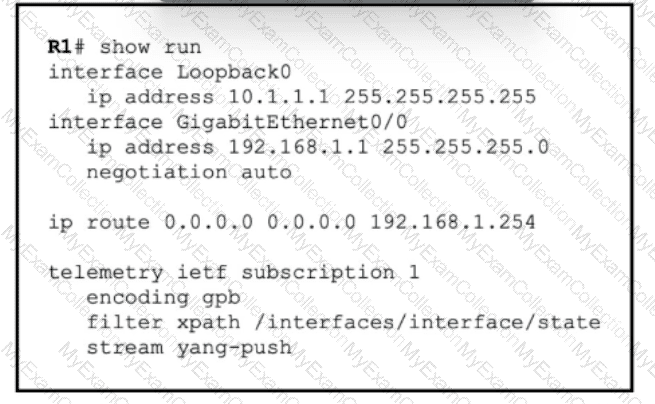
Refer to the exhibit. A regional company is implementing a network-health monitoring solution on their Cisco ISR routers to monitor network performance metrics and gather real-time data. The router R1 Ethernet interface, GigabitEthernet0/0, is assigned IP address 192.168.1.1/24, and basic IP addressing and connectivity to the data-collection server have already been configured. A network engineer must update R1 to ensure secure and reliable data transmission to the monitoring server, which is located at IP address 192.168.50.50 on port 50051. To achieve secure communication, the configuration must comply with RFC 5246, and to ensure reliable data transmission, it must follow RFC 793. Which command must the engineer execute to configure data collection?
Refer to the exhibit:
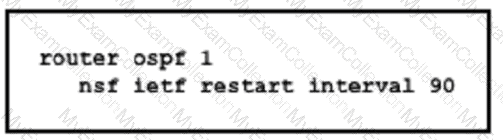
Which purpose of implementing NSF with this configuration is true?
Refer to the exhibit.
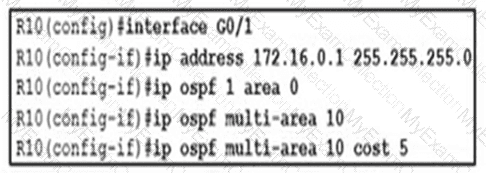
A network engineer Is implementing OSPF multiarea. Which command on interface G0/1 resolves adjacency Issues in the new area?
Which role does the Adjacency-SID sub-TLV extension perform in the IS-IS routing protocol?
Refer to the exhibit. The operations team is implementing an LDP-based configuration in the service provider core network with these requirements:
R1 must establish LDP peering with the loopback IP address as its Router-ID.
Session protection must be enabled on R2.
How must the team update the network configuration to successfully enable LDP peering between R1 and R2?
Refer to the exhibit. The company is running IS-IS in its core. A network engineer must segment the network into two areas to isolate departments. However, some networks must be shared from area 2 to area 1, so the engineer has decided to implement route filtering between devices.
Which action must the engineer take so that the correct networks are shared between IS-IS areas?
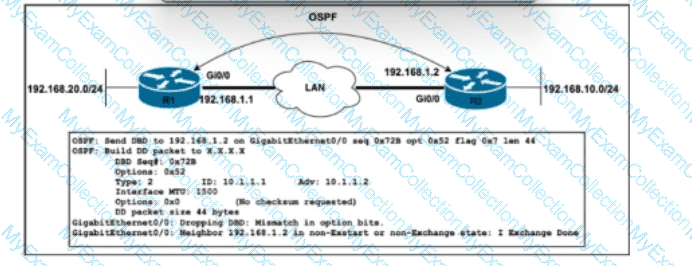
Refer to the exhibit. A network engineer just upgraded the Cisco IOS XE Software to the newest version on OSPF routers R1 and R2, added the point-to-point network type under Gi0/0 on R2, and configured ip route 192.168.10.0 255.255.255.0 192.168.1.2 on R1. After the engineer restarted the routers, R1 entered the Exstart state with its neighbor, but the adjacency has not been established. Which action must the engineer take to resolve the issue?
A network operator working for a telecommunication company with an employee Id: 4065 96080 it trying to implement BFD configuration on an existing network of Cisco devices Which task must the engineer perform to enable BFD on the interfaces?
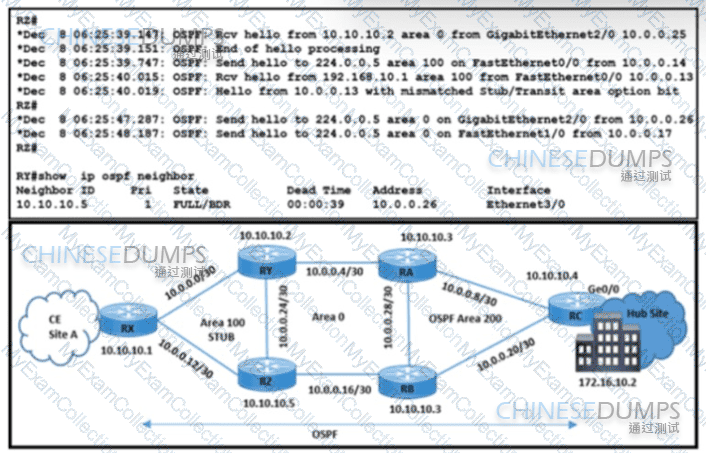
Refer to the exhibit. A network engineer received a complaint about these problems in OSPF stub area 100:
The Ethernet link is down between routers RX and RY because the fiber was cut.
CE site A traffic to the hub site is being dropped.
Which action resolves these issues?
A mid-size service provider uses L2VPN as its standard for connectivity between offices. A small company wants the service provider to connect the company's two sites across the service provider core. To meet service requirements, the service provider must extend the Layer 2 domain between the company's two locations.
Which configuration must the engineer apply to implement an attachment circuit between the two sites using a VLAN tag of 12?
Refer to the exhibit.
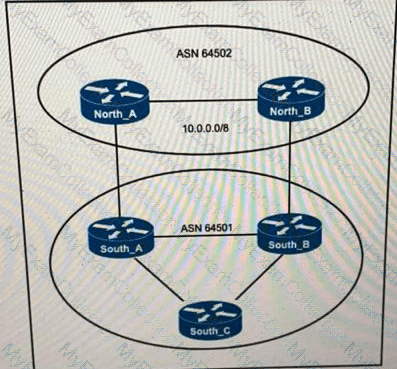
ASN 64501 currently reaches the networks under the 10.0.0.0/8 prefix via the North_B router, which is a slow backup link. The administrator of ASN 64502 wants traffic from ASN 64501 to 10.0.0.0/8 to travel via the primary link North_A. Which change to the network configuration accomplishes this task?
Refer to the exhibit:
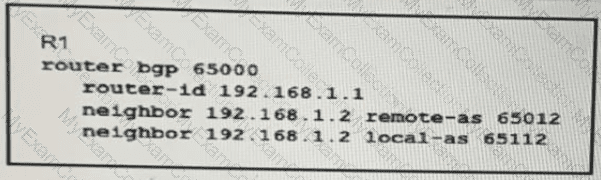
A network engineer is implementing a BGP protocol. Which effect of the local-as keyword in this configuration is true?
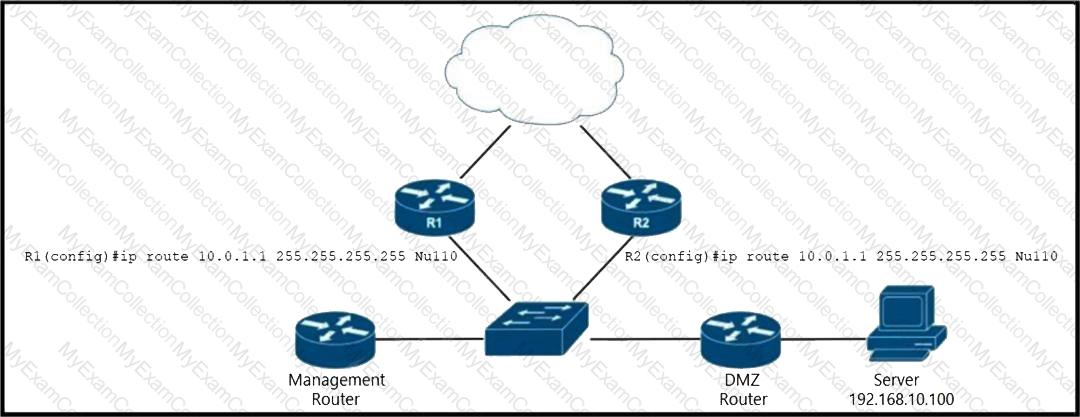
router(config)# route-map blackhole-trigger
router(config-route-map)# match tag 777
router(config-route-map)# set ip next-hop 10.0.1.1
router(config-route-map)# set origin igp
router{config-route-map)# set community no-export
Refer to the exhibit. EIGRP is running across the core to exchange internal routes, and each router maintains iBGP adjacency with the other routers on the network. An operator has configured static routes on the edge routers R1 and R2 for IP address 10.0.1.1, which is used as a black hole route as shown. Which configuration should the operator implement to the management router to create a route map that will redistribute tagged static routes into BGP and create a static route to blackhole traffic with tag 777 that is destined to the server at 192.168.10.100?
Drag and drop the SG KAN architecture types from the bottom next to the corresponding topologies on the right.
A regional company is planning to bolster the security of their LAN infrastructure by implementing advanced encryption techniques between their core switch and their distribution switch. The solution must leverage hardware-accelerated encryption capabilities to transparently encrypt all traffic between the two switches at the data-link layer to safeguard against unauthorized access. However, it is important for the solution to have minimal impact on network performance and latency.
Which action must the engineer take to meet the requirements?
Refer to the exhibit. A multinational corporation with a Cisco-based network wants to leverage Cisco security features to enhance the security of their LAN and protect against eavesdropping and man-in-the-middle attacks. The solution must comply with the IEEE 802.1AE standard. A network engineer must implement the new security configurations on a pair of interconnected Cisco switches. The engineer already completed the configuration to enable AAA new-model and set up a basic AAA configuration for user authentication. Management VLAN 10 is in place for network administration. Which action must the engineer take to meet the requirements?
A company uses PIM-SM multicast with IGMPv2 to stream training videos from a server in one network to hosts in a different network. As the company has grown, the networking team decided to implement SSM to improve efficiency for multicast within Layer 2. Which action must the team take to begin the process?
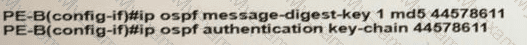
Refer to the exhibit:
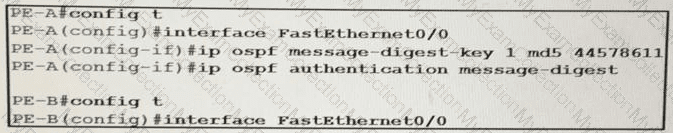
An engineer wants to authenticate the OSPF neighbor between PEA and PE-B using MD5.
Which command on PE-B successfully completes the configuration?
A)
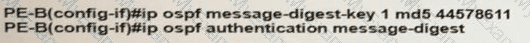
B)
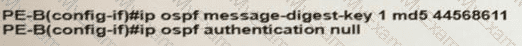
C)
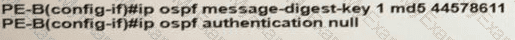
D)
Refer to me exhibit.
Refer to the exhibit. A network engineer notices PE-21 convergence degradation due to the growing LSDB size of Level 2 areas in the network. The engineer decides to migrate router PE-21 from an inter-area design to an intra-area implementation. Inter-area routing must be accomplished via an ATT-bit set by the Level 1/Level 2 router. Which configuration must the engineer implement on PE-21 to complete the migration?
Which set of facts must the network architect consider when deciding whether to implement SaltStack or Chef?
Refer to me exhibit.
A network operator recently configured BGP FlowSpec for me internal IT network What will be inferred from the configuration deployed on me network?
When implementing a REST API, how does an engineer mitigate security risks?
Refer to the exhibit.
An engineer is configuring two routers to support MPLS LDP sessions between them. The R1 configuration is complete, and work has started on R2 as shown. Which additional configuration must the engineer apply to R2 to complete the task?
Refer to the exhibit.
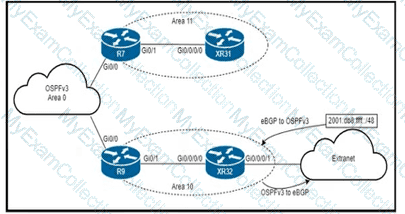
An engineer is updating this network to meet these conditions:
• Area 10 will receive inter-area routes and support mutual redistribution of external routes with the extranet.
• The ::/0 route is prohibited in Area 10.
• Area 11 will receive only the ::/0 route from the ABR.
• External route redistribution is not supported in Area 11.
• The ABR in Area 11 will advertise no interarea routes.
Which two configurations must be performed to meet the requirements? (Choose two.)
How does an untrusted interface at the boundary of an administrative domain handle incoming packets?
Drag and drop the functions from the path computation element protocol roles on the right.
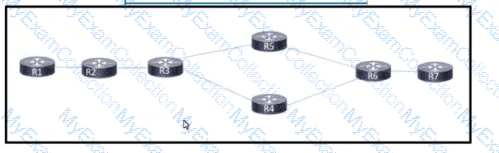
Refer to the exhibit. After a networking team configured this MPLS topology, the supervisor wants to view MPLS labels to verify the path that packets take from router R1 to router R7 The team already Issued an ICMP ping to verify connectivity between the devices. Which task must the team perform to allow the supervisor to view the label switch path?
An ISP Is Implementing end-to-end fault monitoring for a customer based on the IEEE 802.3ah standard. The solution must detect when 15 or more corrupted Ethernet packets arrive within 10 ms and stop propagating traffic through the ISP backbone network or to the customer side. Which configuration must the ISP engineer apply?
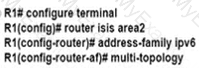
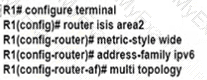
Refer to the exhibit.
An engineer is configuring multitopology IS-IS for IPv6 on router R1. Which additional configuration must be applied to the router to complete the task?
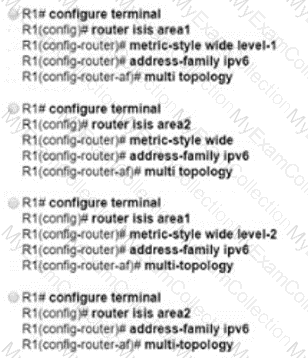
Refer to Exhibit.
A network engineer is trying to retrieve SNMP MIBs with RESTCONF on the Cisco switch but fails. End-to-end routing is in place. Which configuration must the engineer implement on the switch to complete?
Refer to the exhibit.
While troubleshooting the OSPF adjacency between routers R1 and R2 an engineer noticed that both routers are stuck in the EXCHANGE/EXSTART state. What should the engineer fix to solve the ongoing issue?
While implementing TTL security, an engineer issues the PE(config-router-af)#neighbor 2.2.2.2 ttl-security hops 2 command. After issuing this command, which BGP packets does the PE accept?
Refer to the exhibit.
An engineer working for private Service Provider with employee id: 3948:11:613 is configuring the BGPsec framework. Which two conditions must the engineer take into account? (Choose two.)
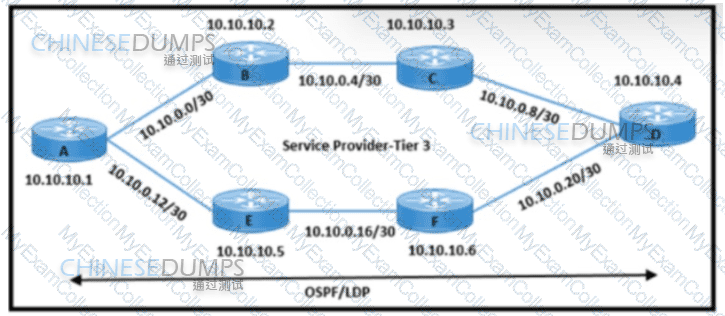
Refer to the exhibit. An engineering team must update the network configuration so that data traffic from router A to router D continues in case of a network outage between routers B and C. During a recent outage on the B-C link, the IGP traffic path was switched to the alternate path via routers E and F. but label forwarding did not occur on the new path. Which action ensures that traffic on the end-to-end path continues?
Refer to the exhibit:
An engineer is preparing to implement data plane security configuration.
Which statement about this configuration is true?