An engineer is implementing a new SSID on a Cisco Catalyst 9800 Series WLC that must be broadcast on 6 GHz radios. Users will be required to use EAP-TLS to authenticate. Which wireless Layer 2 security method is required?
What does the LAP send when multiple WLCs respond to the CISCO_CAPWAP-CONTROLLER.localdomain hostname during the CAPWAP discovery and join process?
An engineer is installing a new pair of routers in a redundant configuration. Which protocol ensures that traffic is not disrupted in the event of a hardware failure?
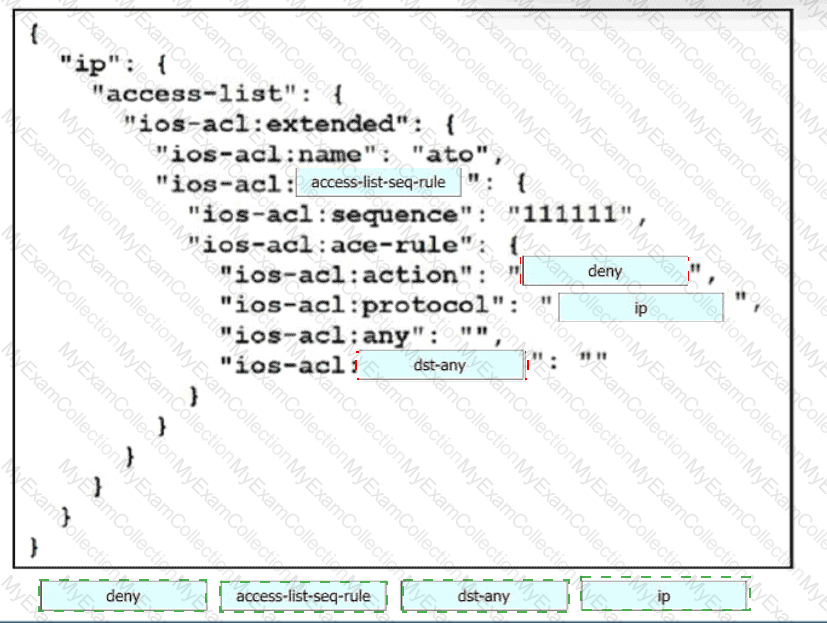
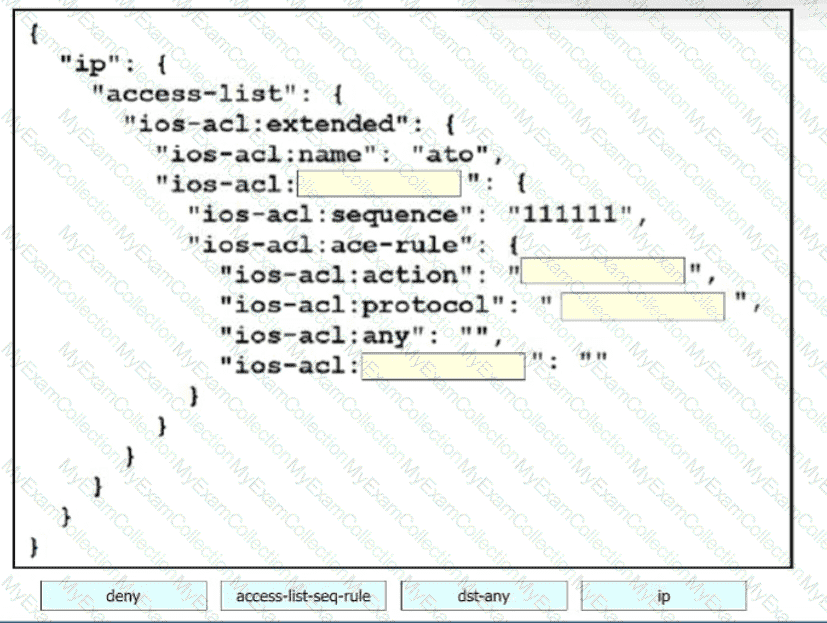
Drag and drop the code snippets from the bottom onto the blanks in the code to construct a request that configures a deny rule on an access list?
Which characteristic applies to a traditional WAN solution but not to a Cisco Catalyst SD-WAN solution?
What is one characteristic of an AP that is operating in Mobility Express mode?
Which AP mode allows a supported AP to function like a WLAN client would, associating and identifying client connectivity issues?
In a Cisco Mobility Express wireless deployment, which AP takes over if the primary AP fails?
An engineer is reviewing a PCAP file that contains a packet capture of a four-way handshake exchange between a dient and AP using WPA2 Enterprise Which EAPOL message validates and confirms that the client device has successfully Installed the GTK?
When using a Cisco Catalyst 9800 Series WLC, which tag/profile can be applied to APs to change the mode to FlexConnect in a specific location?
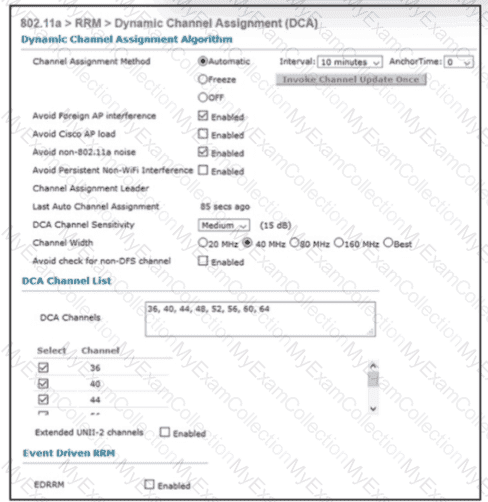
Refer to the exhibit An engineer is troubleshooting an issue with non-Wi-Fi interference on the 5-GHz band The engineer has enabled Cisco CleanAir and set the appropriate traps, but the AP does not change the channel when it detects significant interference Which action will resolve the issue?
When a wireless client roams between two different wireless controllers, a network connectivity outage is experience for a period of time. Which configuration issue would cause this problem?
What is used by vManage to interact withCiscoSD-WAN devices in the fabric?
Which features does Cisco EDR use to provide threat detection and response protection?
Which two nodes comprise a collapsed core in a two-tier Cisco SD-Access design? (Choose two.)
What is the name of the numerical relationship of the wireless signal compared to the noise floor?
Which tool is used in Cisco Catalyst Center (formerly DNA Center) to build generic configurations that are able to be applied on devices with similar network settings?
Which security mechanism is offered on a next-generation firewall but not on a traditional firewall?
Which method displays text directly into the active console with a synchronous EEM applet policy?
An engineer must configure a new WLAN that supports 802.11r and requires users to enter a passphrase. What must be configured to support this requirement?
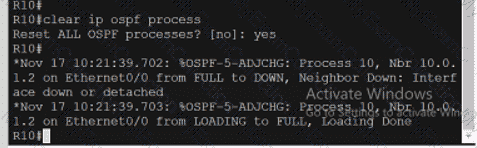
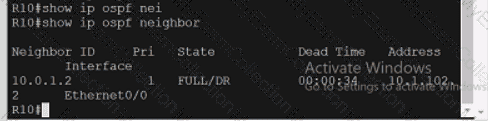
An engineer must create an EEM script to enable OSPF debugging in the event the OSPF neighborship goes down. Which script must the engineer apply?
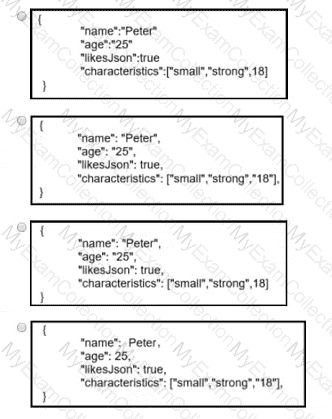
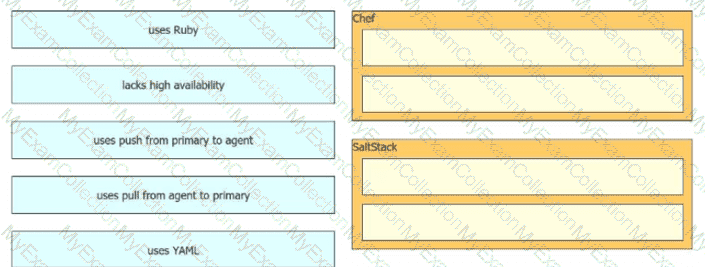
Drag and drop the automation characteristics from the left onto the appropriate tools on the right. Not all options are used.
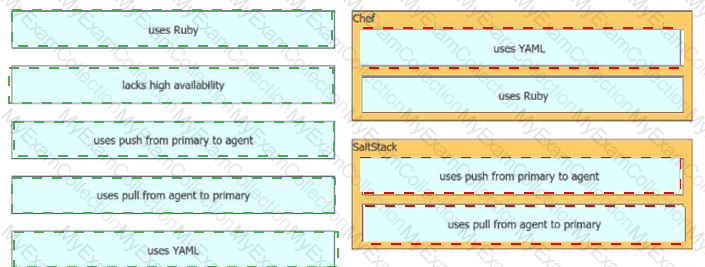
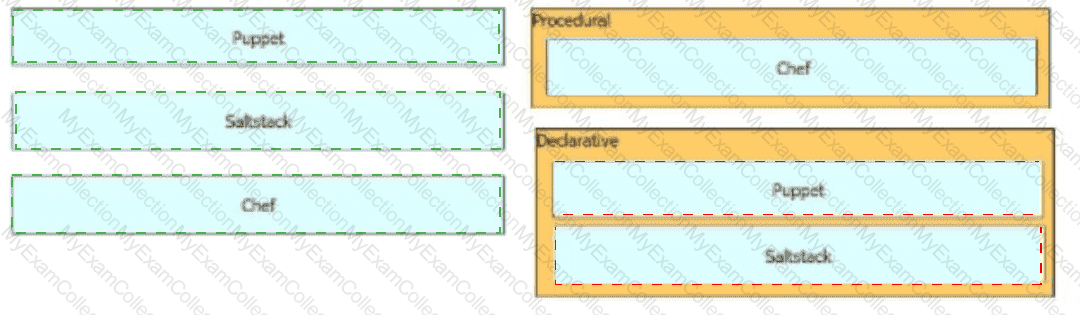
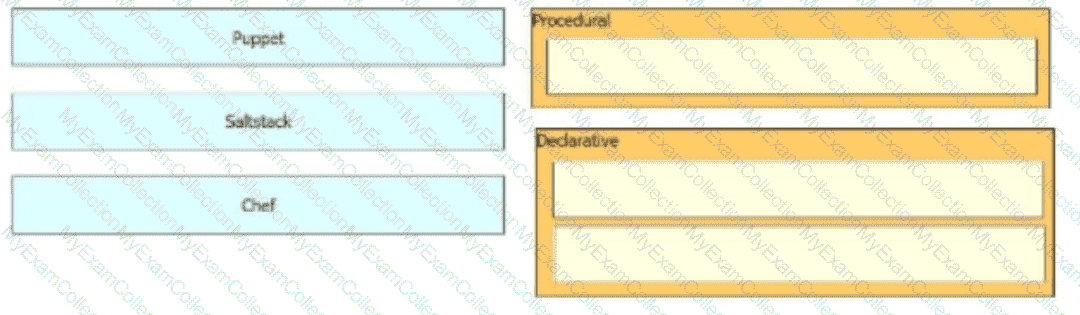
Drag and drop the configuration management tools from the left onto the configuration styles they use on the right
Which protocol is used by vmanage to push centralized policies to vsmart controllers?
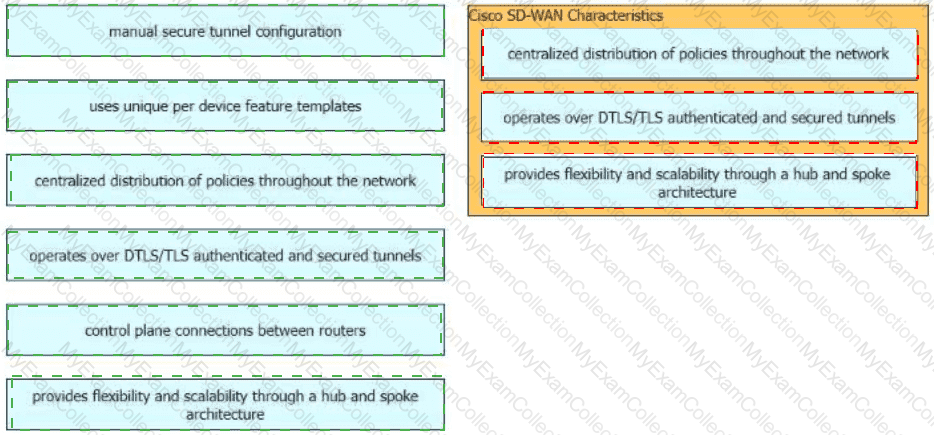
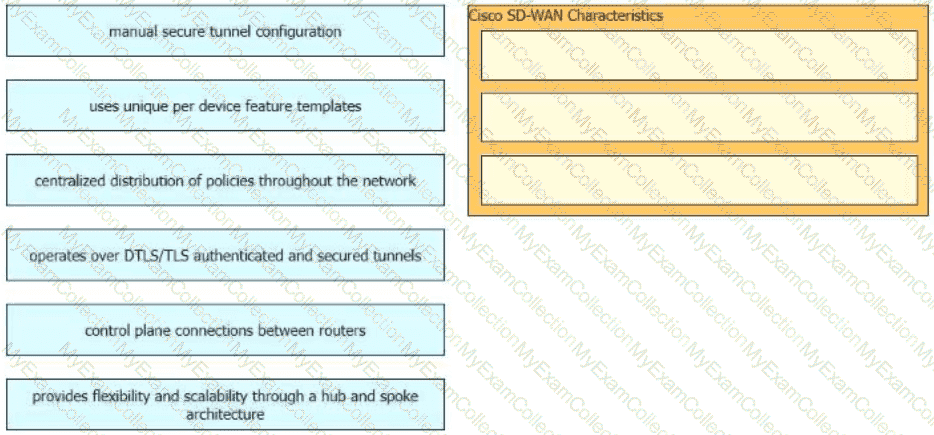
Drag and drop the characteristics of Cisco Catalyst SD-WAN from the left onto the right. Not all options are used.
Which design principle states that a user has no access by default to any resource, and unless a resource is explicitly granted, it should be denied?
What is a consideration when designing a Cisco SD-Access underlay network?
In a high-density AP environment, which feature can be used to reduce the RF cell size and not demodulate radio packets above a given threshold?
Which solution simplifies management of secure access to network resources?
A network administrator prepares to deploy a new software-defined fabric across campuses. What is needed to ensure success for the overall design?
A customer requests a design that includes GLBP as the FHRP. The network architect discovers that the members of the GLBP group have different throughput capabilities. Which GLBP load balancing method supports this environment? Â
Which feature is used to propagate ARP. broadcast, and link-local frames across a Cisco SD-Access fabric to address connectivity needs for silent hosts that require reception of traffic to start communicating?
Which character formatting is required for DHCP Option 43 to function with current AP models?
What is the recommended minimum SNR for data applications on wireless networks?
Which characteristic applies to the endpoint security aspect of the Cisco Threat Defense architecture?