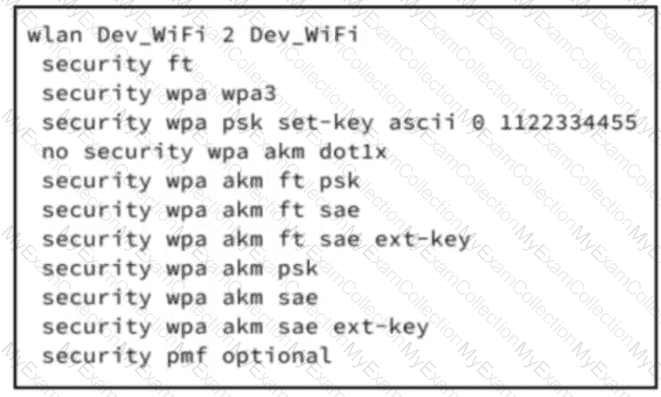
Refer to the exhibit. A startup company has recently moved to new offices and performed a full network refresh. The application development team requested a high-speed reliable wireless network to use for testing real-time applications. Although, the wireless network is Wi-Fi 7 enabled, the wireless clients are connecting using lower speeds. Which configuration must be applied on the WLC to increase throughput?
Which function does FRA use to optimize client experience and network coverage?
An onsite engineer is working to connect devices to the wireless network using central switching in a corporate environment. Security protocols and network-specific settings must be configured as per enterprise policy. After the initial wireless settings are applied on an iOS tablet, the engineer must ensure that VLAN ID 10 is assigned on the client device to complete a successful enterprise Wi-Fi connection. Which action meets this requirement?
A network engineer must ensure that guest users connecting to a Cisco 9800 WLC are assigned IP addresses from a specific subnet that is separate from corporate users. The guest network must support at least 200 simultaneous connections and isolate traffic from internal devices. The DHCP server must allocate addresses only within the 10.20.30.0/24 subnet. Which action must the network engineer take to accomplish this task?
A network administrator at a marketing company is deploying a Cisco Catalyst 9800 Series Wireless Controller running Cisco IOS XE 17.x. The corporate WLAN named XYZ-Guest supports visitor devices. To address intermittent connectivity issues due to client association limits and short session timeouts, the network administrator must optimize the WLAN to allow more client connections and extend session timeouts for the devices. The administrator must set the maximum number of clients for the XYZ-Guest WLAN to 50 and must set a session timeout to prevent frequent device disconnections. Which two commands must be configured on the controller? (Choose two.)
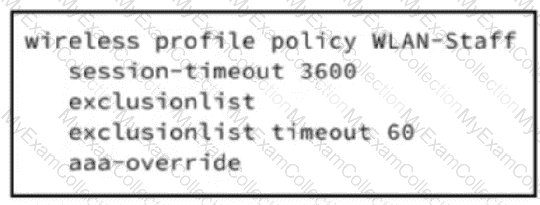
Refer to the exhibit. A network administrator must configure a client management parameter for a wireless deployment in a multi-site enterprise. The enterprise is using Cisco ISE as the management platform to oversee wireless access policies. To meet the organization's compliance requirements, all wireless endpoints must be evaluated against a posture policy before gaining access. Which configuration change must be applied on the WLAN level of the WLC to meet the requirement?
A school district is deploying Cisco Catalyst 9176 APs to remote sites with occasional WAN outages. The IT team wants the APs to attempt joining a secondary or tertiary Catalyst 9800 WLC if the primary controller is unreachable. The team must preconfigure all controller IP addresses using the AP CLI before deploying. Which set of CLI commands sets the primary, secondary, and tertiary controller IP addresses on a Catalyst 9176 AP?
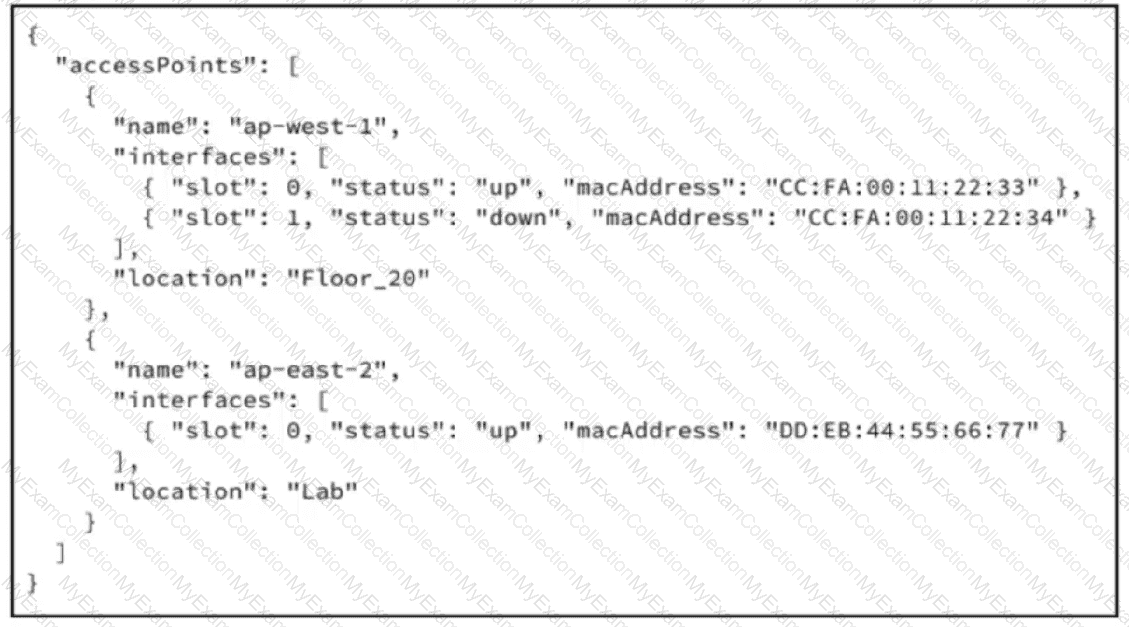
Refer to the exhibit. A JSON response from a wireless management API contains access point inventory and interface state information. Which JSON expression retrieves the MAC address of the second interface on the first access point?
A network engineer is integrating Cisco ISE with a wireless controller for 802.1X authentication. The controller is registered with Cisco ISE as a network device. To secure communication, the engineer must configure a shared secret for RADIUS authentication. Which CLI command on the WLC accomplishes this task?
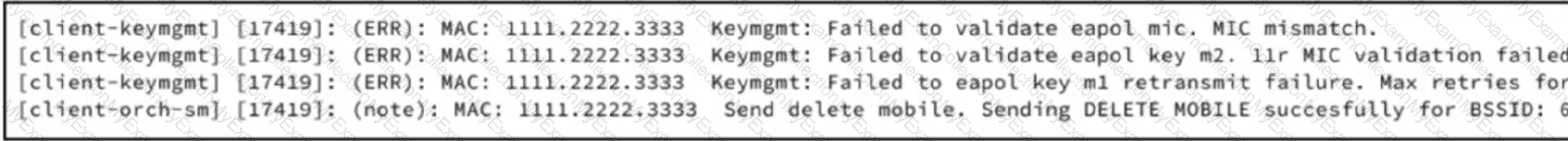
Refer to the exhibit. A network engineer must create a PSK WLAN that will be anchored to the DMZ. After this WLAN is created, users cannot connect to it. Based on the output from the RA trace, which action must the engineer take to resolve the issue?
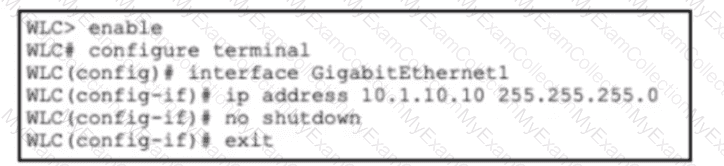
Refer to the exhibit. A network engineer is deploying a new Cisco 9800 WLC and is performing the Day-0 setup. The IP address and subnet mask have been assigned to the management interface, and network connectivity between the WLC and the upstream switch has been verified. Which CLI command must the engineer use next to configure management access?
A retail store has a Cisco 9176 FlexConnect AP at a branch location and must ensure that wireless clients continue to access the network even if the WAN link to the central controller is down. The AP must authenticate users locally during outages and still sync with the controller when connectivity is restored. The IT administrator wants centralized management for all APs but requires high availability for branch users. Which set of CLI commands on the 9800 WLC configures the AP to meet these requirements?
A network administrator at a construction company manages a Cisco Catalyst 9800 Series Wireless Controller running Cisco IOS XE 17.x. The WLAN named XYZ-Conference is set up for a large event, but attendees report slow network performance due to misbehaving clients. To improve connectivity, the network administrator decides to change the client exclusion policy on the WLAN to temporarily block the misbehaving clients. The XYZ-Conference WLAN must enable a client exclusion policy with a timeout of 120 seconds for misbehaving clients. Which set of Cisco IOS XE commands must be used?
A network administrator at a retail company recently deployed a Cisco Catalyst 9800 WLC. The NOC was unaware of wireless issues until it received reports from users. The network administrator must configure Cisco Catalyst Center to enable effective client issue alerts via email to prevent this happening again. Which action must the network administrator take in Cisco Catalyst Center to meet the requirements?
Exhibit:
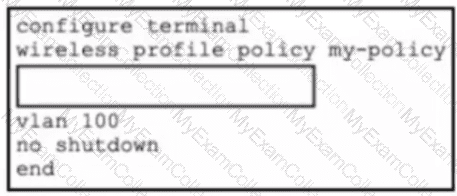
Refer to the exhibit. An enterprise is deploying Cisco Catalyst 9800 WLCs and is using Catalyst Center as the management platform to oversee wireless access policies. To meet the organization's compliance requirements, all wireless endpoints must be evaluated with security posture validation before gaining access. Which set of CLI commands must be added to the box in the code to complete the configuration?
A deployment requires that several APs be connected to edge switches, and each AP must support management and guest Wi-Fi traffic. The APs tag guest traffic separately from management, and the organization expects to add more VLANs for IoT and voice soon, so the configuration must support scalability. The security team requires that guest traffic never mix with internal resources. Which port configuration must be used for the switch interfaces that connect to the APs?
How does viewing trend deviation in Cisco Catalyst Center AI Analytics benefit wireless operation?
A managed service is rolling out advanced wireless infrastructure to support an expanding organization with diverse device types. The implementation requires integration of dynamic endpoint profiling for secure access and device classification. According to the baseline deployment with ISE policy sets, the engineering group must enforce access parameters based on device category rules. Which configuration action must be taken to fulfill the initiative?
Exhibit:
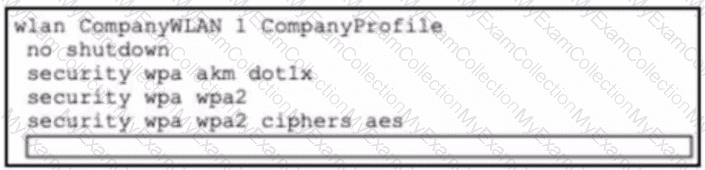
Refer to the exhibit. A Cisco 9800 WLC is deployed at a branch location to facilitate secure client connectivity. A network engineer configures a WLAN using WPA2 Enterprise authentication and activates the RADIUS server-based method to align with company security policies. Which CLI command must be added to the box in the configuration to enable client authentication for this WLAN?
Which process enables seamless Layer 2 handoff in a wireless network during roaming?
Refer to the exhibit.
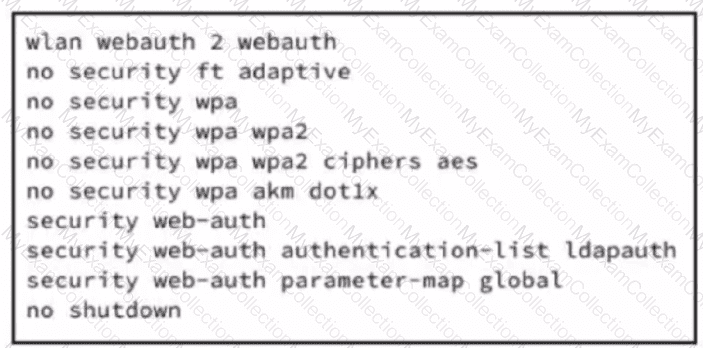 A wireless controller is deployed at a branch location to facilitate guest client connectivity. A network engineer configures one WLAN using Web authentication and activates web-based method to align with company security policies. Which configuration enables client authentication for this WLAN?
A wireless controller is deployed at a branch location to facilitate guest client connectivity. A network engineer configures one WLAN using Web authentication and activates web-based method to align with company security policies. Which configuration enables client authentication for this WLAN?
A network engineer must isolate all guest users connected to the WLAN on a Cisco 9800 WLC so they cannot communicate with each other but can access the internet. The WLAN must meet these requirements:
•SSID named VisitorAccess assigned to VLAN 30
•guests prohibited from sharing files with other guests
•must be scalable to multiple access points in the building
Which action must the network engineer take to meet the requirements?
An IT team is deploying Meraki APs at a remote branch and must ensure that they are automatically assigned to the correct network in the Meraki dashboard. The branch is scheduled to receive 20 new APs, and site connectivity to headquarters was set up. Before shipping the APs, the team must make sure that each one is claimed by the intended network for management and monitoring. Which deployment action must they take before physically connecting the APs?
Which Cisco Ultra-Reliable Wireless Backhaul process enables devices to establish a reliable connection with the next AP along their path before losing connectivity to the current one in a wireless network during roaming?

