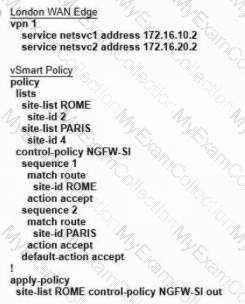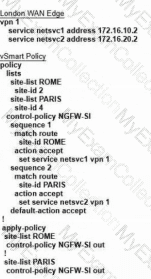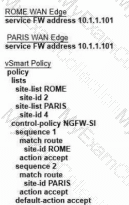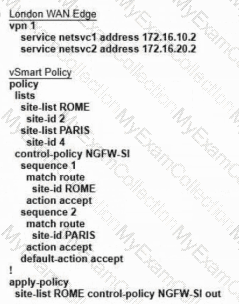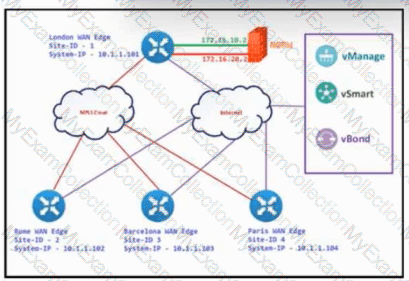
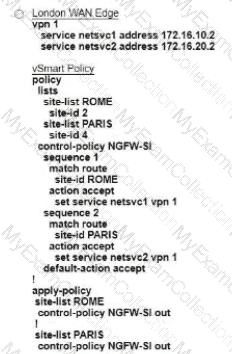
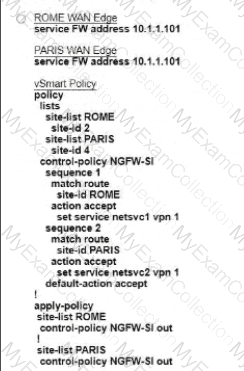
Refer to the exhibit. The Cisco SD-WAN is deployed using the default topology. The engineer wants to configure a service insertion policy such that all data traffic between Rome to Paris is forwarded through the NGFW located in London. Which configuration fulfills this requirement, assuming that the Service VPN ID is 1?
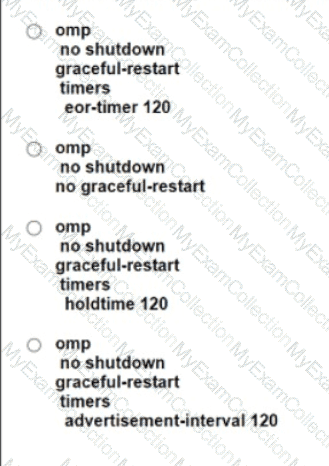
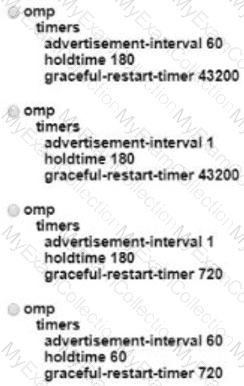
A company deploys a Cisco SD-WAN solution but has an unstable Internet connection. When the link to vSmart comes back up, the WAN Edge router routing table is not refreshed, and some traffic to the destination network is dropped. The headquarters is the hub site, and it continuously adds new sites to the SD-WAN network. An engineer must configure route refresh between WAN Edge and vSmart within 2 minutes. Which configuration meets this requirement?
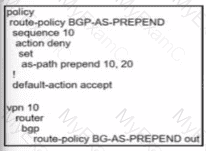
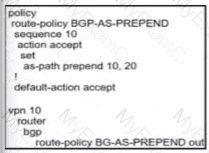
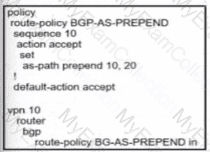
When the VPN membership policy is being controlled at the vSmart controller, which policy disallows VPN 1 at sites 20 and 30?
A)
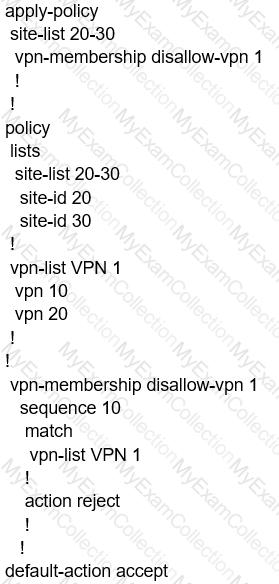
B)

C)
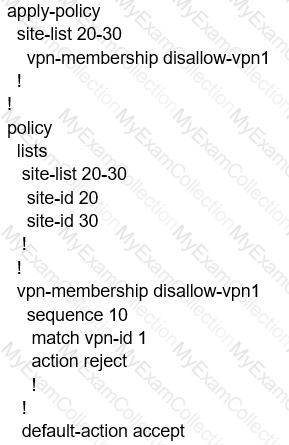
D)
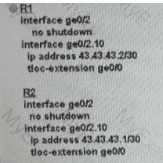
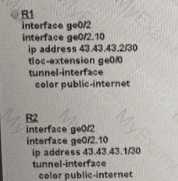
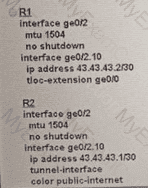
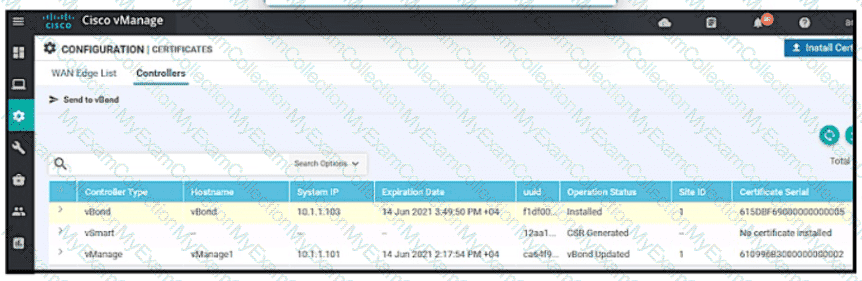
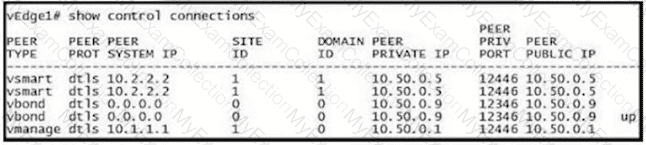
Refer to the exhibit.
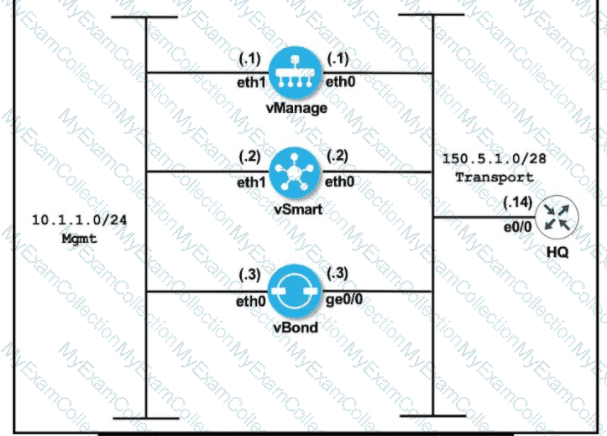

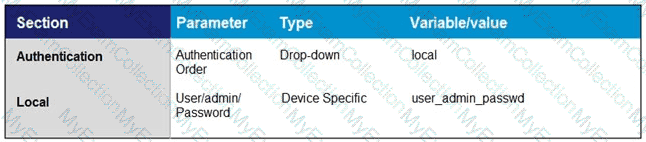
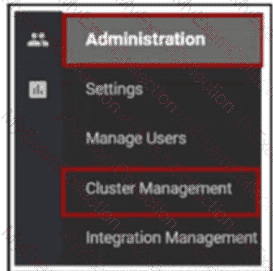
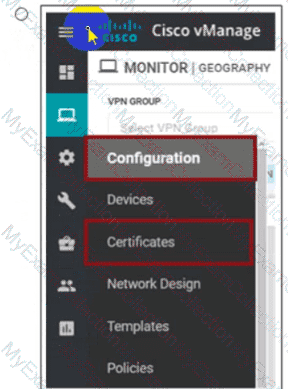
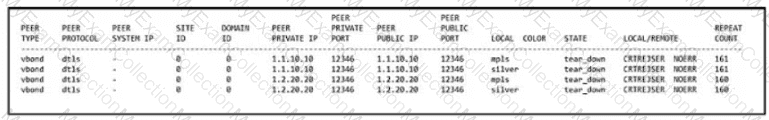
An engineer is troubleshooting an issue where vManage and vSmart have a problem establishing a connection to vBond. Which action fixes the issue?
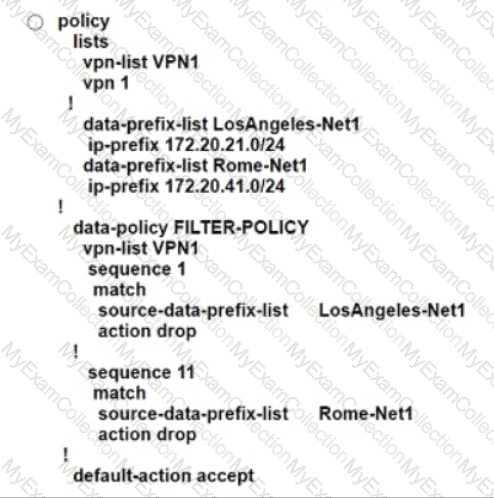
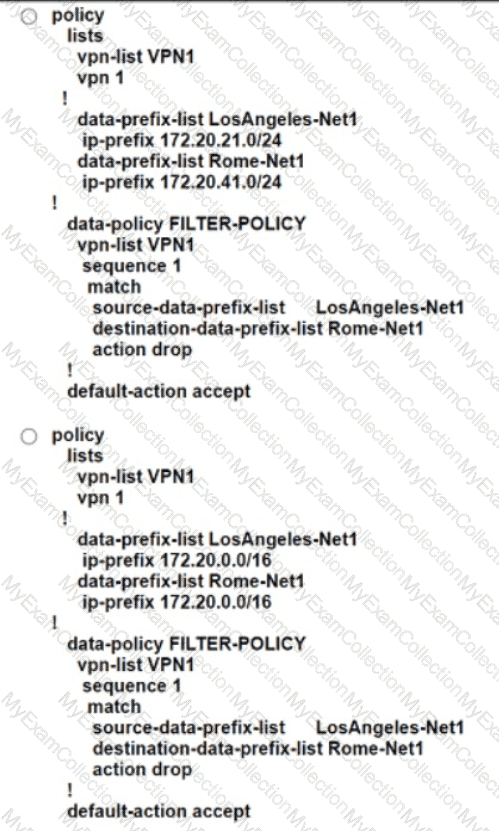
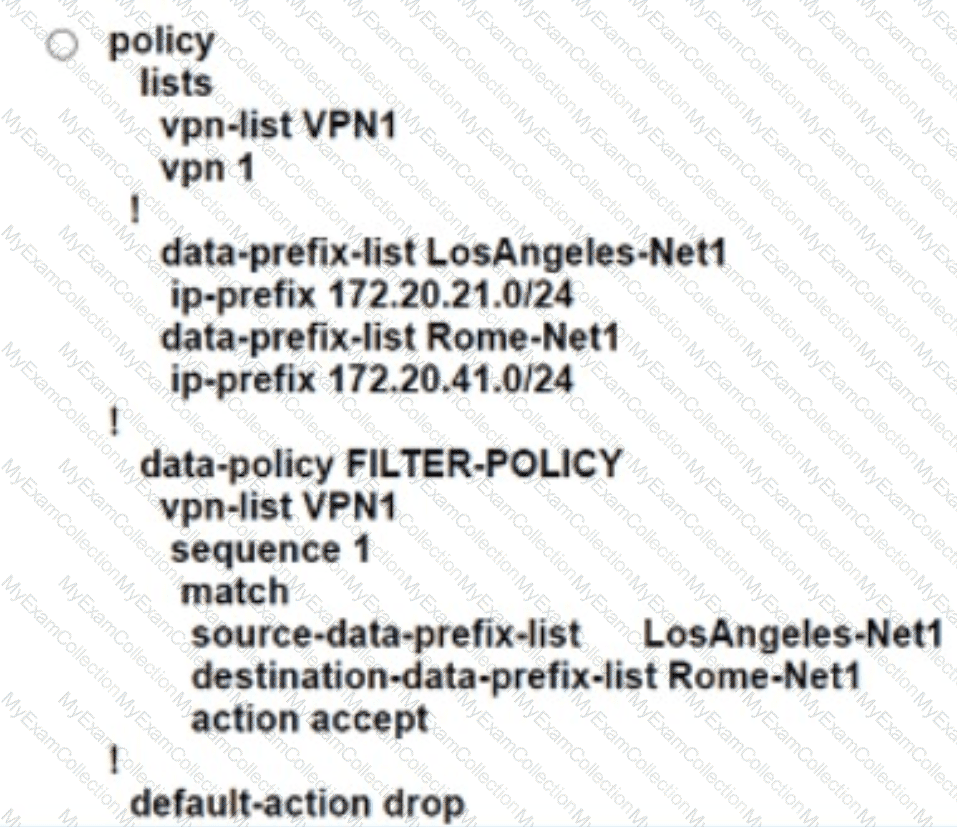
An engineer creates a data policy to prevent communication from the 172.20.21.0/24 network to the 172.20.41.0/24 network. Which configuration accomplishes this task?
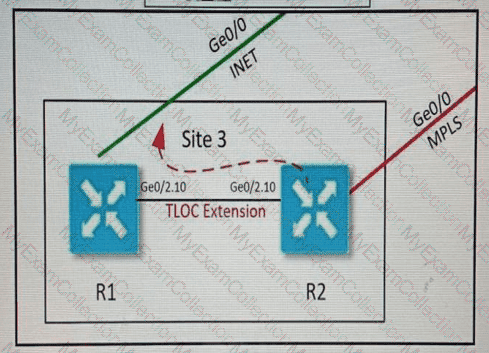
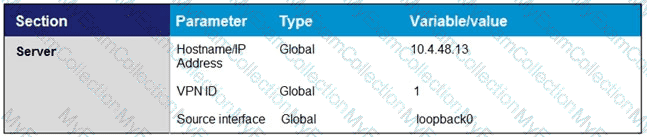
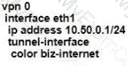
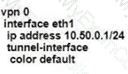
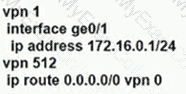
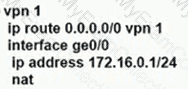
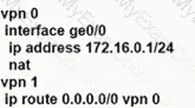
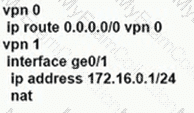
Refer to the exhibit. Which configuration extends the INET interface on R1 to be used by R2 for control and data connections?
A)
B)
C)
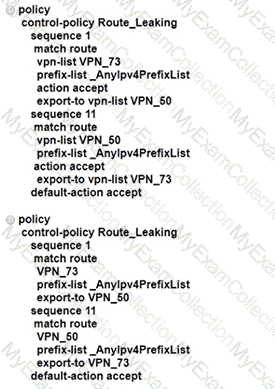
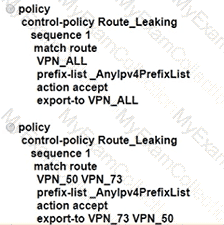
An enterprise has several sites with multiple VPNs that are isolated from each other A new requirement came where users in VPN 73 must be able to talk to users in VPN 50 Which configuration meets this requirement?
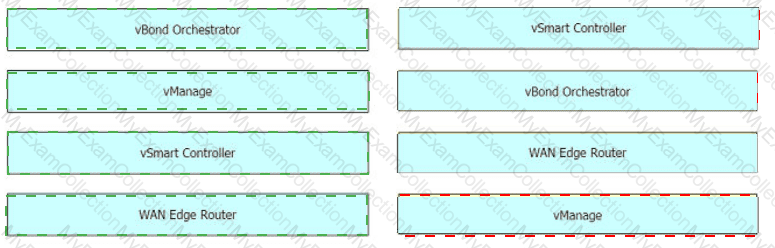
Which component of the Cisco SD-WAN control plane architecture should be located in a public Internet address space and facilitates NAT-traversal?
An engineer must apply the configuration for certificate installation to vBond Orchestrator and vSmart Controller. Which configuration accomplishes this task?

On which device is a service FW address configured to Insert firewall service at the hub?
What are the two components of an application-aware firewall? (Choose two.)
Which plane builds and maintains the network topology and makes decisions on traffic flows?
Which two performance data details are provided by Cisco SO-WAN vAnalytics? (Choose two)
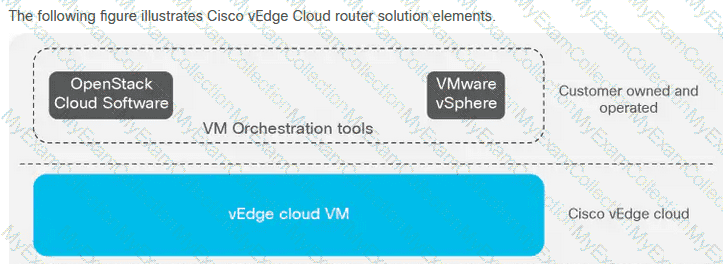
Which two virtualized environments are available for a company to install the controllers using the on-premises model? (Choose two )
Which TCP Optimization feature is used by WAN Edge to prevent unnecessary retransmissions and large initial TCP window sizes to maximize throughput and achieve a better quality?
Which protocol Is used by the REST API to communicate with network services in the Cisco SO-WAN network?
Which encryption algorithm is used for encrypting SD-WAN data plane traffic?
Which two platforms for the Cisco SD-WAN architecture are deployable in a hypervisor on-premises or in IAAS Cloud? (Choose two.)
An administrator needs to configure SD-WAN to divert traffic from the company's private network to an ISP network. What action should be taken to accomplish this goal?
What is an advantage of using auto mode versus static mode of power allocation when an access point is connected to a PoE switch port?
Which table is used by the vSmart controller to maintain service routes of the WAN Edge routers in the hub and local branches?
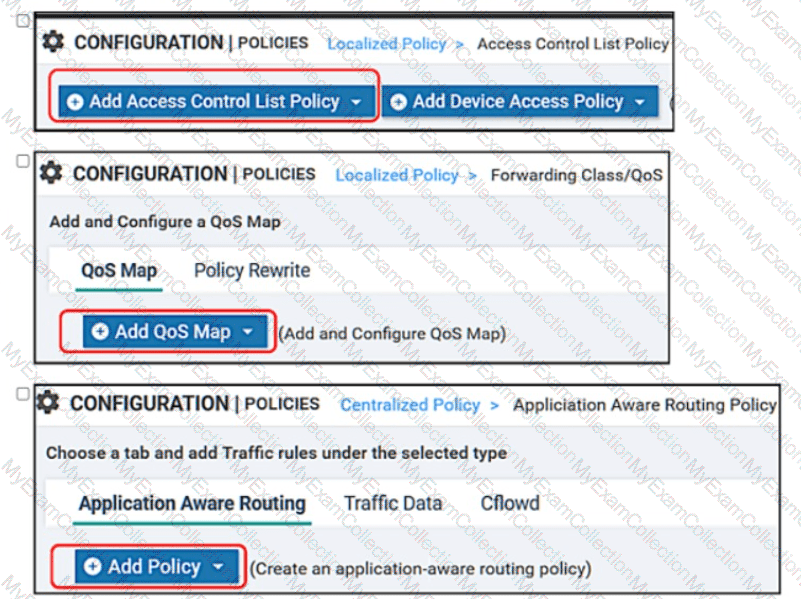
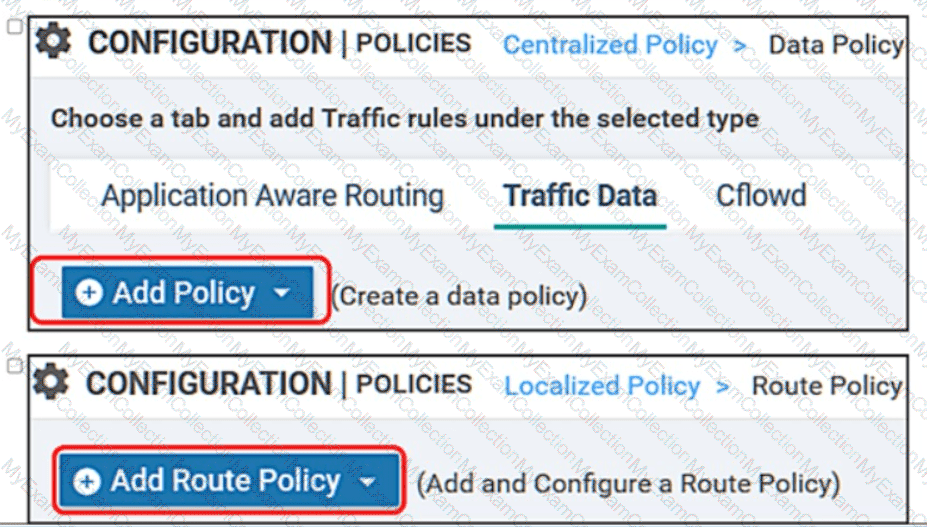
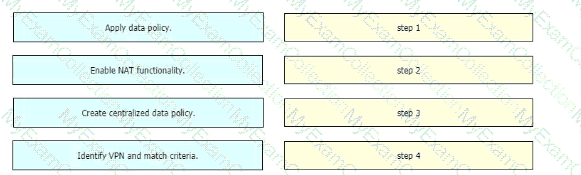
An engineer must use data prefixes to configure centralized data policies using the vManage policy configuration wizard. What is the first step to accomplish this task?
What is the result during a WAN Edge software upgrade process if the version of the WAN Edge software is higher than the one running on a controller device?
Which feature allows reachability to an organization’s internally hosted application for an active DNS security policy on a device?
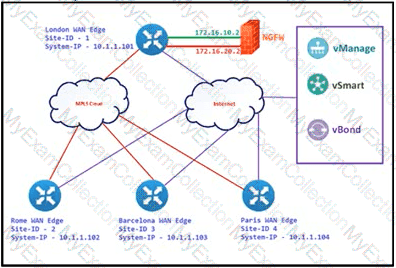
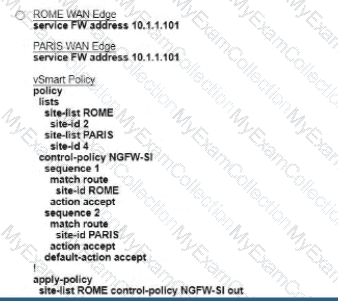
Refer to the exhibit. The Cisco SD-VYAN is deployed using the default topology. The engineer v/ants to configure a service insertion policy such that all data traffic between Rome to Paris is forwarded through the NGFW located in London. Which configuration fulfills this requirement, assuming that the Sen/ice VPN ID is 1?
A)
B)

C)
D)
An engineer modifies a data policy for DIA in VPN 200 to meet the requirements for traffic destined to these locations:
* external networks; must be translated
* external networks; must use a public TLOC color
* syslog servers, must use a private TLOC color
Here is the existing data policy configuration:
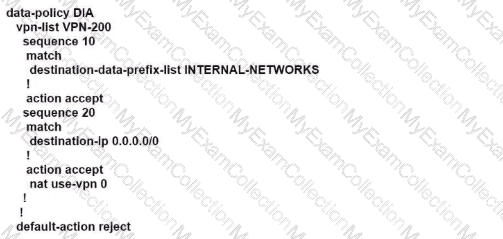
Which policy configuration sequence set meets the requirements?
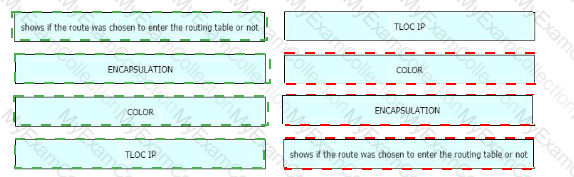
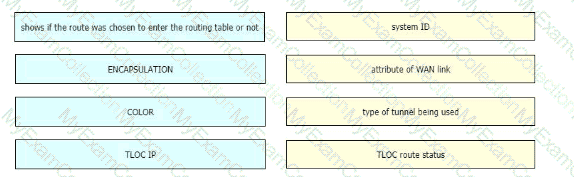
Drag and drop the route verification output from show omp tlocs from the left onto the correct explanations on the right.
How many cloud gateway instance(s) can be created per region when provisioning Cloud OnRamp for Multicloud from AWS in a multiregion environment?
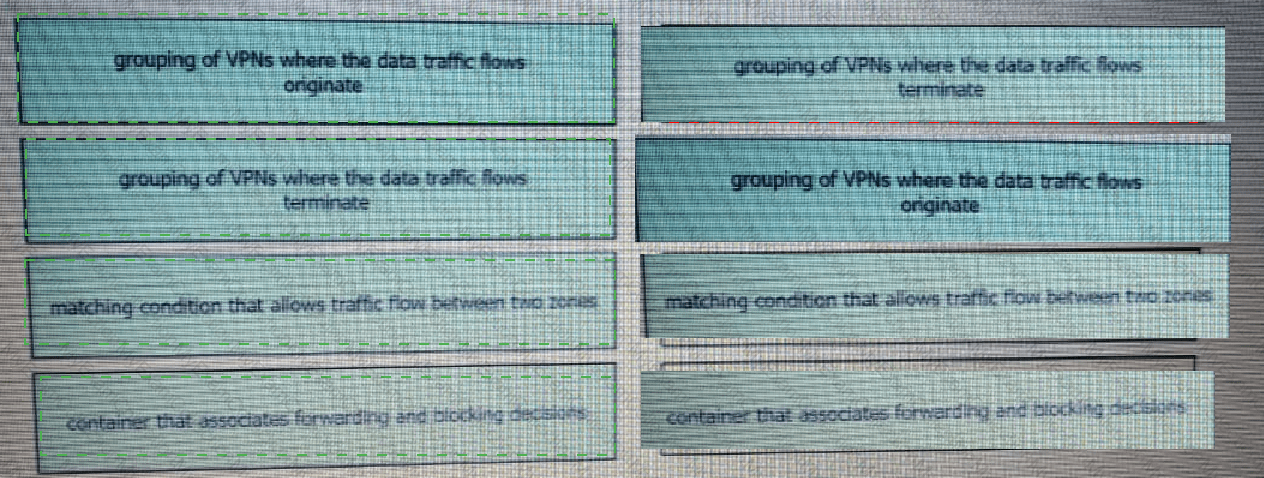
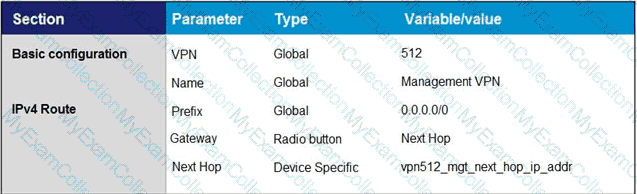
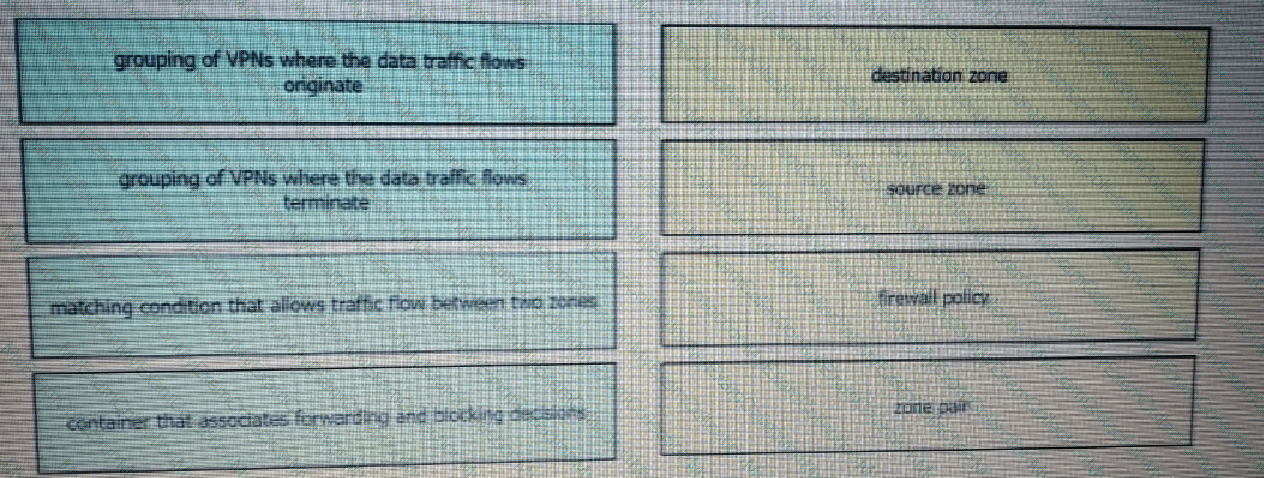
Drag and drop the definitions from the left to the configuration on the right.
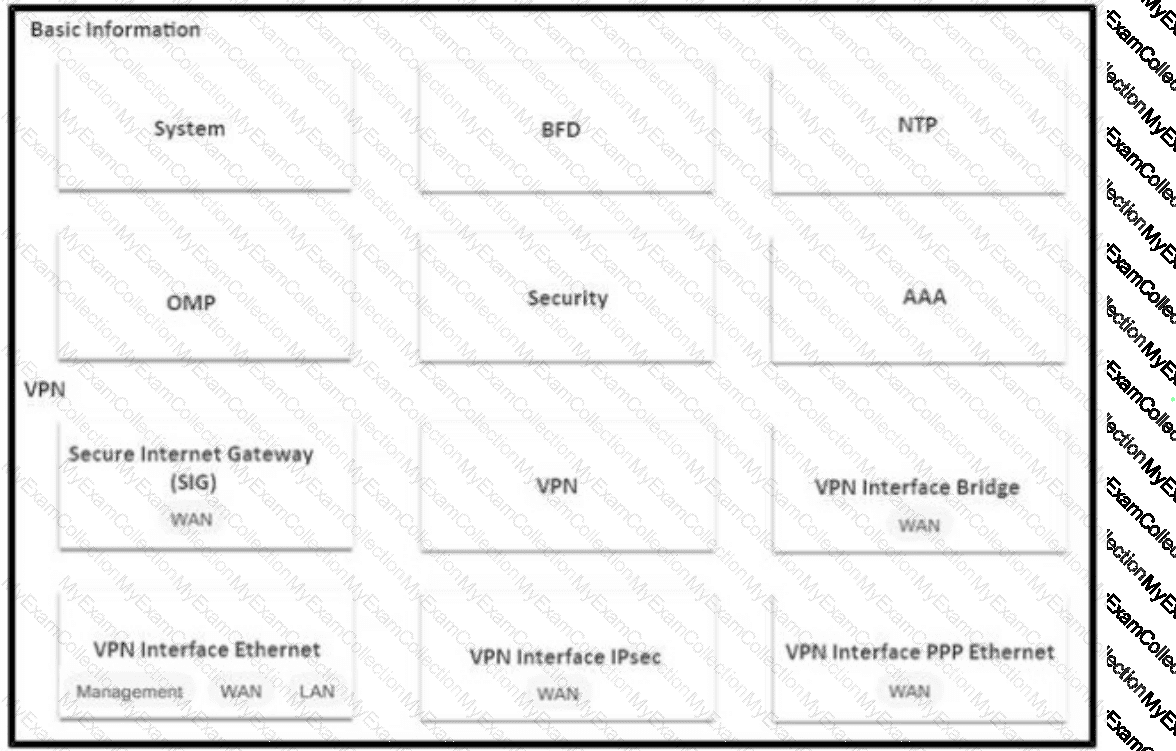
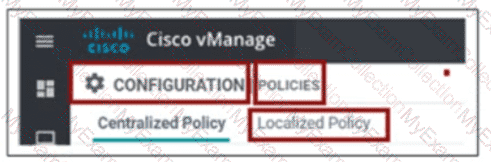
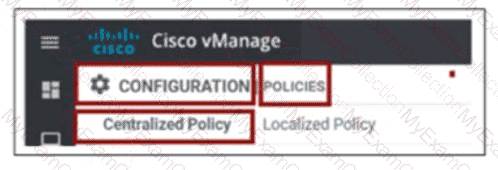
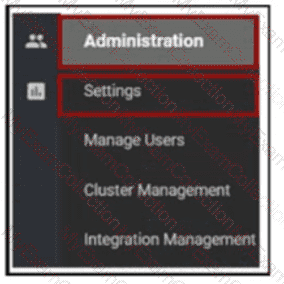
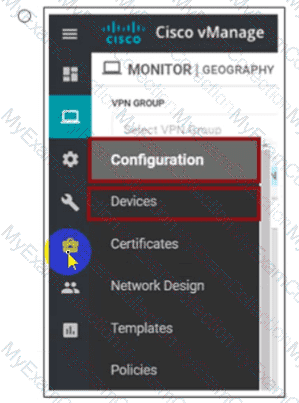
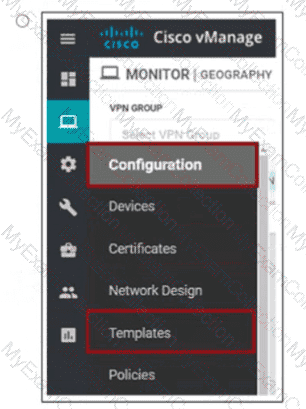
An engineer wants to change the configuration of the certificate authorization mode from manual to automated. Which GUI selection will accomplish this?
What are the two advantages of configuration groups in a Cisco SD-WAN deployment? (Choose two.)
Which two mechanisms are used to guarantee the integrity of data packets in the Cisco SD-WAN architecture data plane? {Choose two)
In Cisco SD-WAN, what protocol is used for control connections between SD-WAN devices?
An engineer must configure the SD-WAN Edge router to identify DSCP 26 traffic coming from the router's local site and then change the DSCP value to DSCP 18 before sending it over to the SD-WAN fabric. What are the two ways to create the required configuration? (Choose two).
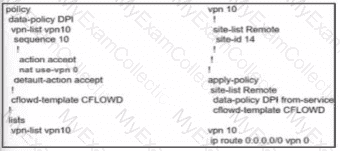
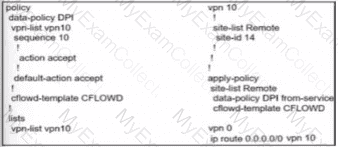
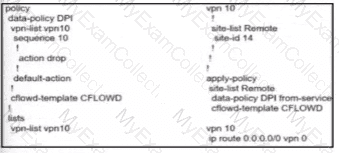
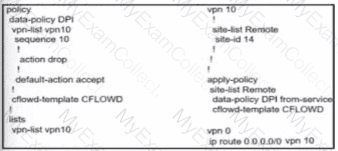
An engineer creates this data policy for DIA for VPN 10:
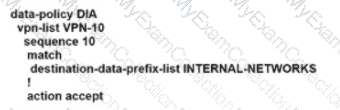
Which policy sequence enables DIA for external networks?

Refer to the exhibit.
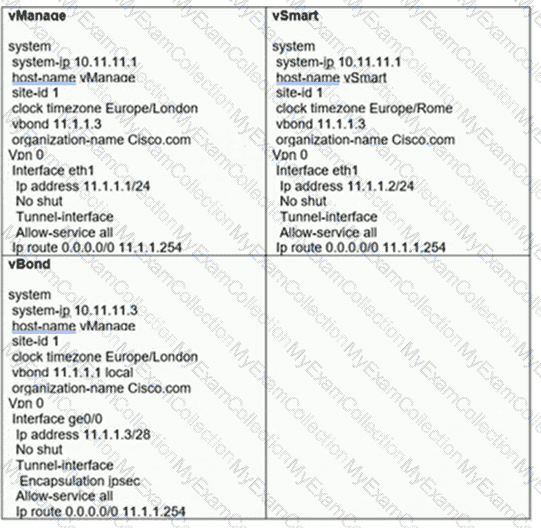
vManage and vSmart have an issue establishing a connection to vBond. Which configuration resolves the issue?
An engineer is configuring a WAN Edge router for DIA based on matching QoS parameters. Which two actions accomplish this task? (Choose two.)
Which command on a WAN Edge device displays the information about the colors present in the fabric that are learned from vSmart via OMP?
A network administrator is tasked to make sure that an OMP peer session is closed after missing three consecutive keepalive messages in 3 minutes. Additionally, route updates must be sent every minute. If a WAN Edge router becomes unavailable, the peer must use last known information to forward packets for 12 hours. Which set of configuration commands accomplishes this task?
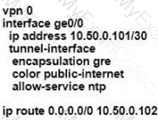
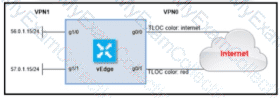
Refer to the exhibit.
Which command-line configuration on a WAN Edge device achieves these results?
A)
B)
C)
D)
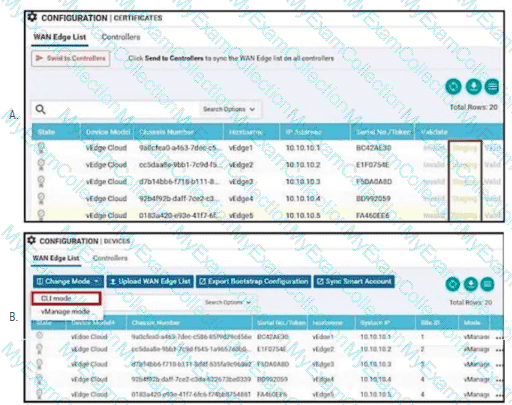
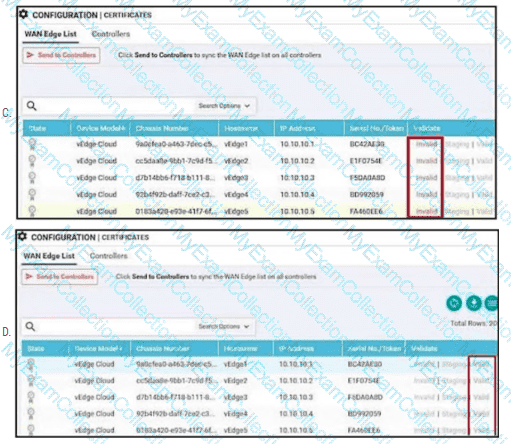
Refer to the exhibit.
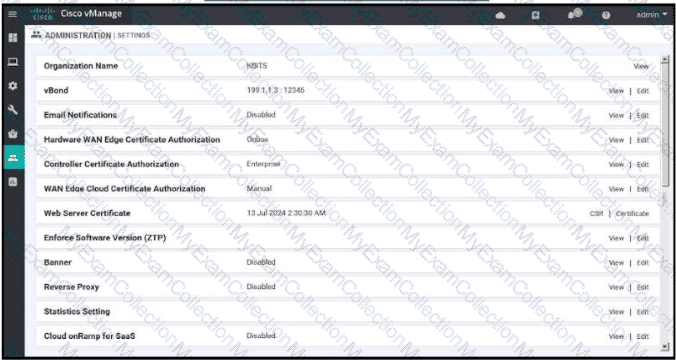
Which two configurations are needed to get the WAN Edges registered with the controllers when certificates are used? (Choose two)
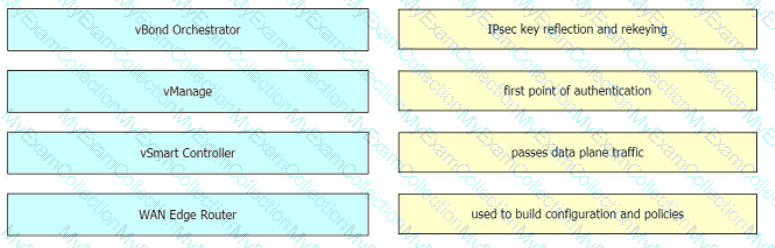
Drag and drop the Cisco SD-WAN components from the left onto their functions on the right.
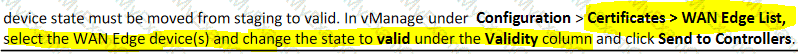
Which configuration step is taken on vManage after WAN Edge list is uploaded?
Which policy is configured to ensure that a voice packet is always sent on the link with less than a 50 msec delay?
An application team is getting ready to deploy a new business-critical application to the network. To protect the traffic, the network team must add another queue to the QoS map and then deploy the map to fabric Which configuration slop must be completed prior to adding the queue to the QoS map and applying If

Refer to the exhibit. An engineer must block FTP traffic coming in from a particular Service VPN on a WAN Edge device Which set of steps achieves this goal?
A network administrator is bringing up one WAN Edge for branch connectivity. Which types of tunnels form when the WAN edge router connects to the SD-WAN fabric?
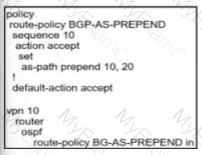
An engineer must avoid routing loops on the SD-WAN fabric for routes advertised between data center sites Which BGP loop prevention attribute must be configured on the routers to meet this requirement?
A network administrator is configuring VRRP to avoid a traffic black hole when the transport side of the network is down on the master device. What must be configured to get the fastest failover to standby?
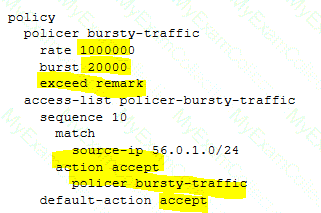
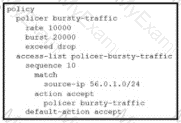
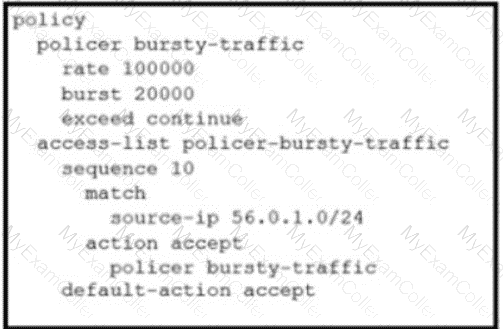
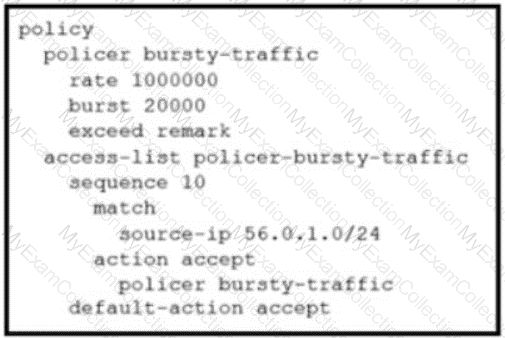
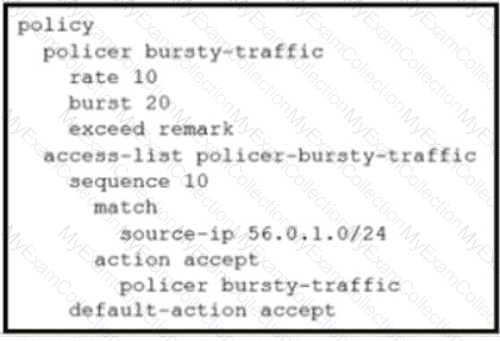
An engineer configures policing with a rate of 125 Bps and a burst rate of 8000 bits, as shown here:
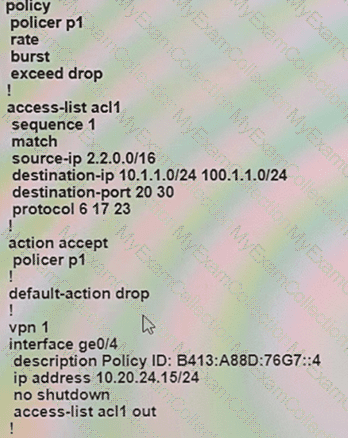
Which configuration completes this task?
How do WAN Edge devices operate when vSmart is inaccessible or fails to be reached by the WAN Edge?
An engineer is modifying an existing data policy for VPN 115 to meet these additional requirements:
When browsing government websites, the traffic must use direct internet access.
The source address of the traffic leaving the site toward the government websites must be set to an IP range associated with the country itself, a particular TLOC.
The policy configuration is as follows:

Which policy sequence meets the requirements without interfering with other destinations?
What is a benefit of the application aware firewall feature in the Cisco SD-WAN solution?
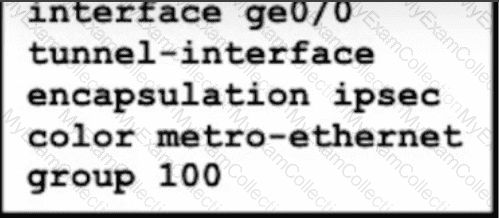
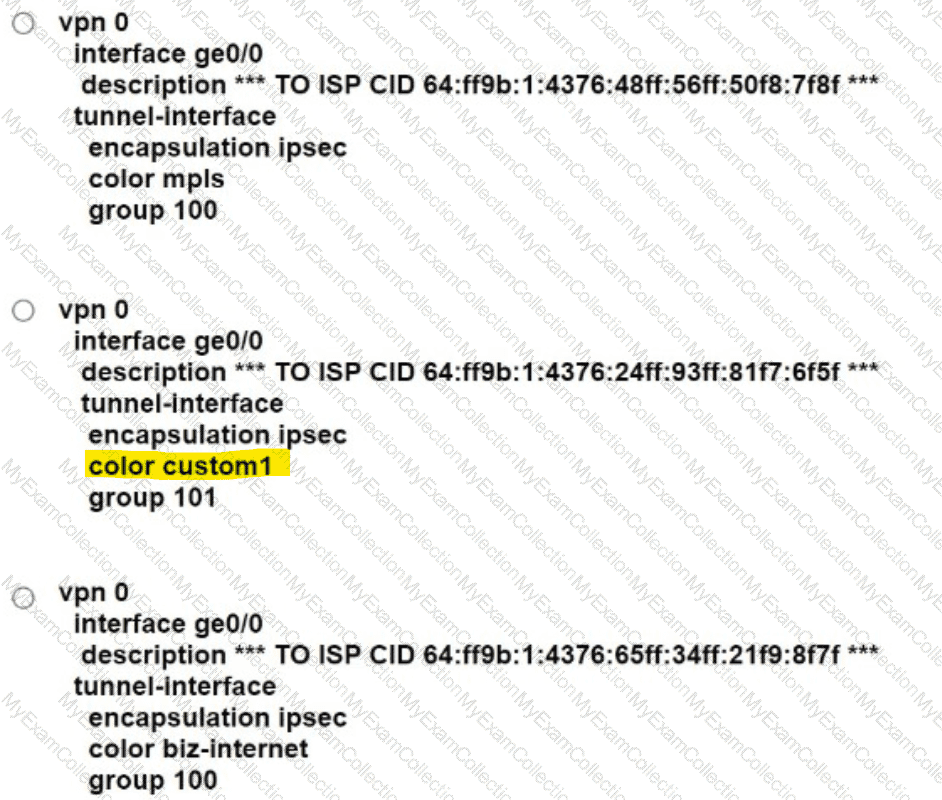
A network administrator is configuring a tunnel interface on a branch Cisco IOS XE router to run TLOC extensions. Which configuration will extend a TLOC over a GRE tunnel to another router in the branch?

An engineer must configure a centralized policy on a site in which all HTTP traffic should use the Public Internet circuit if the loss on this circuit is below 10%. otherwise MPLS should be used Which configuration wizard fulfils this requirement?
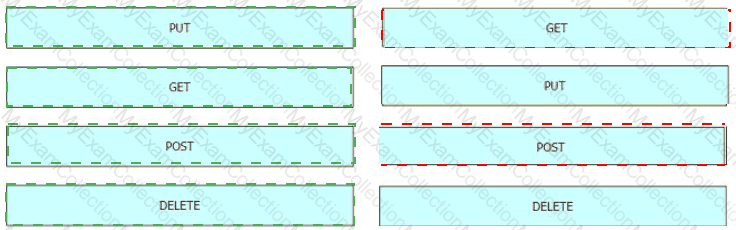
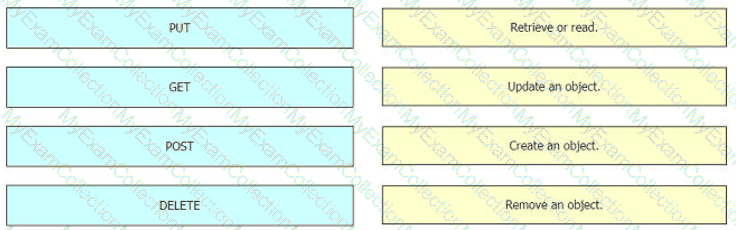
Drag and drop the REST API calls from the left onto the functions on the right.
When redistribution is configured between OMP and BGP at two Data Center sites that have Direct Connection interlink, which step avoids learning the same routes on WAN Edge routers of the DCs from LAN?
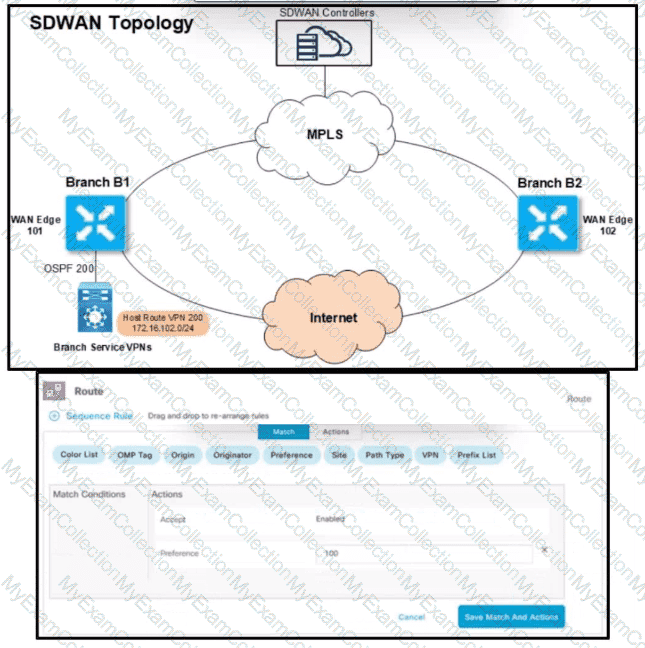
Refer to the exhibit. An engineer must configure the Overlay Management Protocol route preference so that when B2 tries to reach host routes advertised by B1 it always chooses the MPLS circuit. Which two match conditions must be configured to accomplish this task? (Choose two.)
WAN Edge routers are configured manually to use UDP port offset to use nondefault offset values when IPsec tunnels are created. What is the offse range?
How many subnets are necessary in Azure VNet for a WAN Edge device to function in the cloud deployment?
Refer to the exhibit vManage and vBond have an issue establishing a connection to vSmart Which two actions does the administrator take to fix the issue? (Choose two)
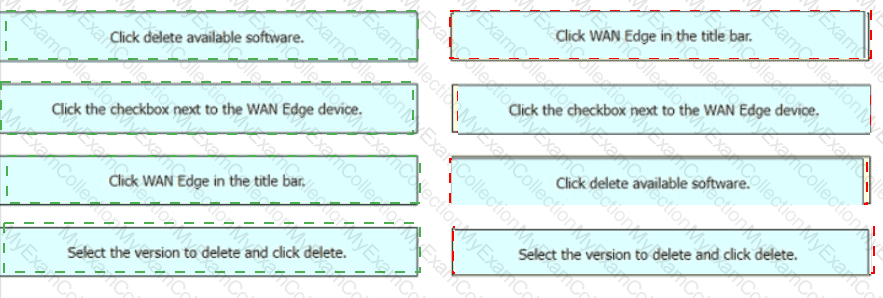
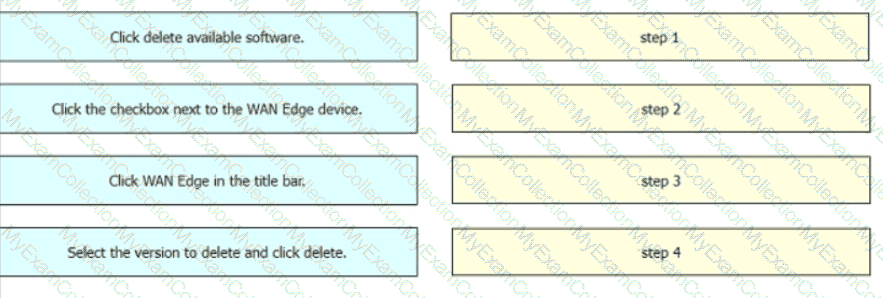
Drag and drop the steps from the left Into the order on the right to delete a software image for a WAN Edge router starting with Maintenance > Software Upgrade > Device list on vManage.
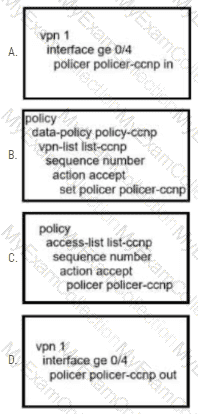
An administrator wants to create a policy to add a traffic policer called "politer-ccnp" to police data traffic on the WAN Edge. Which configuration accomplishes this task in vSmart?
Which policy allows communication between TLOCs of data centers and spokes and blocks communication between spokes?
Which two metrics must a cloud Edge router use to pick the optimal path for a SaaS application reachable via a gateway site? (Choose two.)
What is the default value (in milliseconds) set tor the poll interval in the BFD basic configuration?
What are the two requirements for plug-and-play provisioning on Cisco IOS XE SD-WAN devices? (Choose two.)
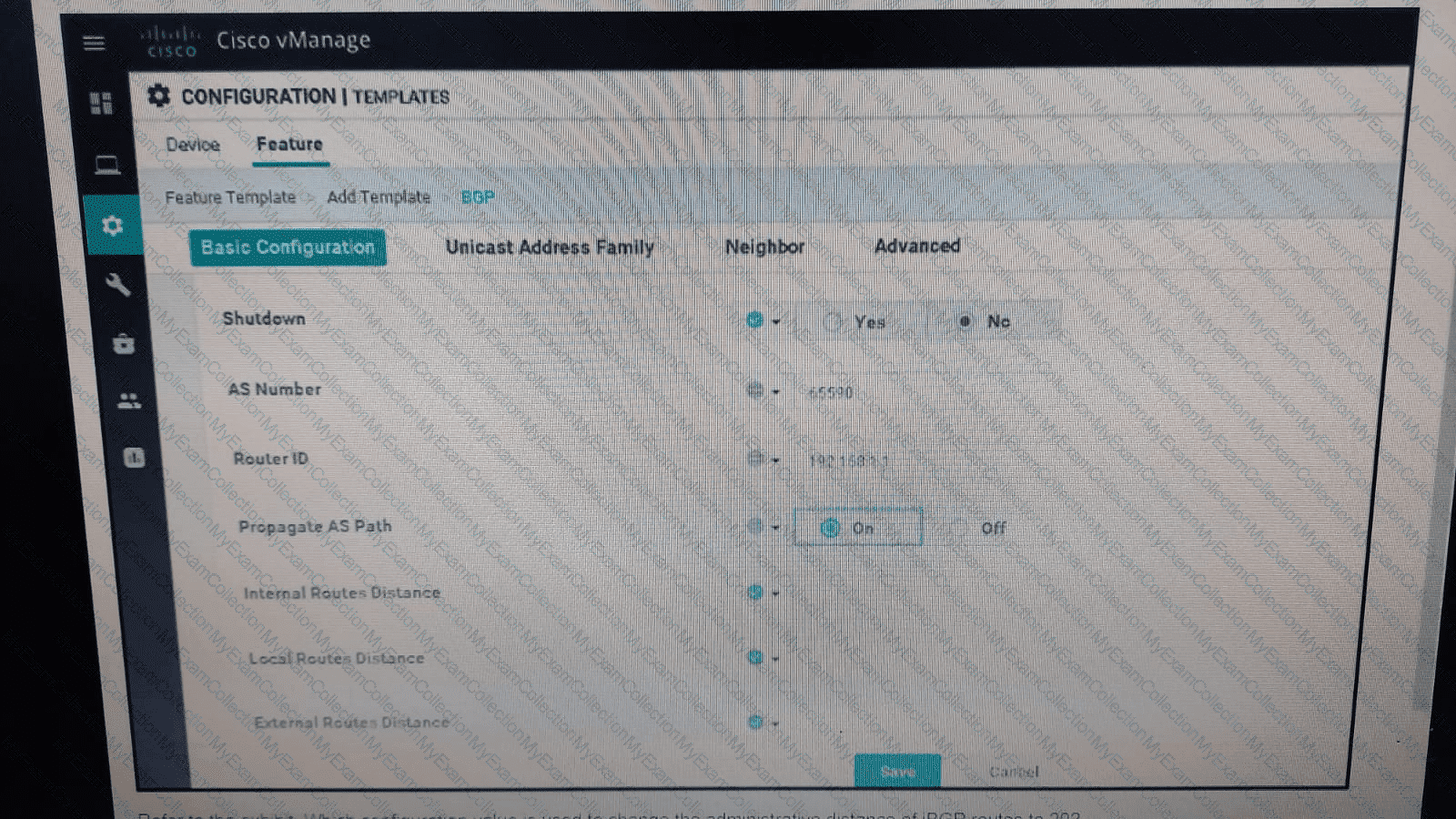
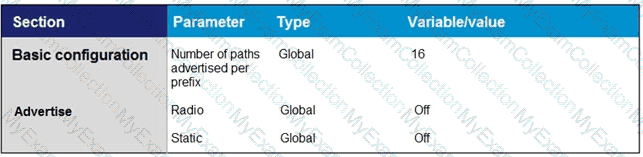
Refer to the exhibit. Which configuration value is used to change the administrative distance of iBGP routes to 20?
What are two benefits of installing Cisco SD-WAN controllers on cloud-hosted services? (Choose two.)
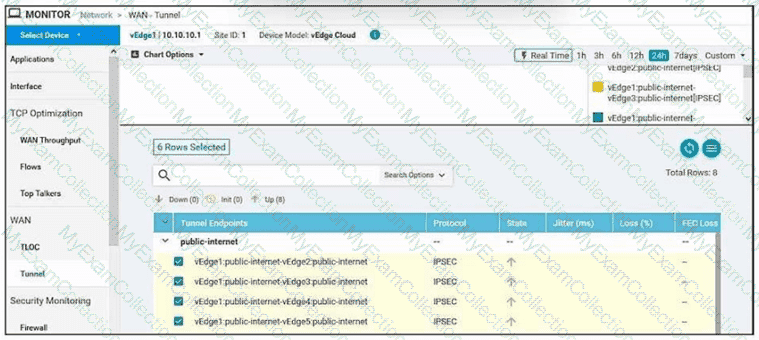
Refer to the exhibit.
An SD-WAN customer has 23 sites connected to its hub site, where a pair of WAN Edge devices and controllers are placed. All other branches have a single WAN Edge device connected to multiprotocol label switching (MPLS) and public internet circuits. An engineer must configure application-aware routing for a branch that has MPLS and public internet circuits provisioned using feature templates. The requirements for application-aware routing are:
All types of traffic prefers using public-internet circuit.
If the average latency reaches 100 ms, jitter 85 ms, and packet loss 5%, then video and voice traffic switches to the MPLS circuit.
Which feature template must be configured or modified in addition to configuring a centralized policy?
Which encryption algorithm secures binding exchanges Between Cisco TrustSec SXP peers?
I
In which file format is a critical severity report downloaded from the MONITOR I ALARM tab in the vManage GUI?
An administrator must configure an ACL for traffic coming in from the service-side VPN on a specific WAN device with circuit ID 391897770. Which policy must be used to configure this ACL?
Which secure connection should be used to access the REST APIs through the Cisco vManage web server?
Which device information is required on PNP/ZTP to support the zero-touch onboarding process?
A network administrator configures SNMFV3 on a Cisco WAN Edge router from CL I for monitoring purposes How many characters are supported by the snmp user username command?
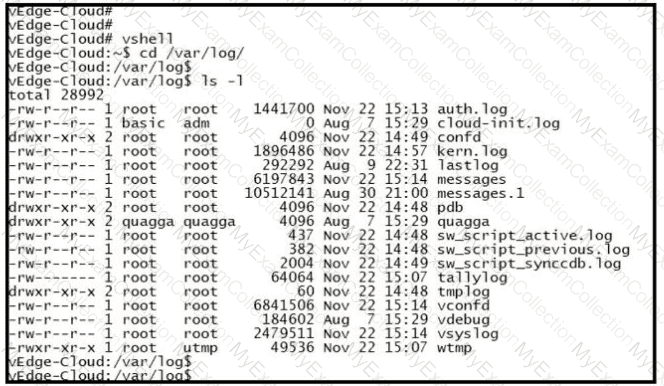
Refer to the exhibit.
An organization is testing a Cisco SD-WAN solution and decided to have the control plane established first and not the data plane at the time of migration. Which configuration achieves this goal?
Which routes are similar to the IP route advertisements when the routing information of WAN Edge routers is learned from the local site and local routing protocols?
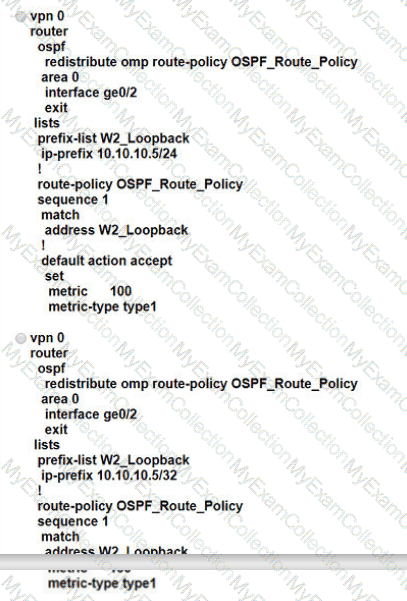
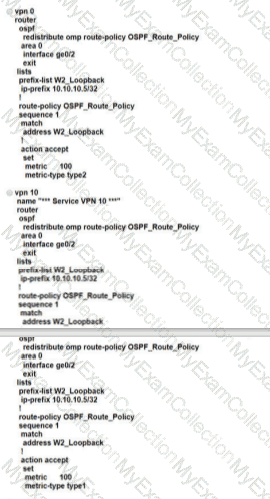
A customer is receiving routes via OMP from vSmart controller for a specific VPN. The customer must provide access to the W2 loopback received via OMP to the OSPF neighbor on the service-side VPN, which configuration fulfils these requirements?
What problem happens on a device with two serial numbers, a unique device identifier (UDI), and secure unique device identifier (SUDI) when an engineer provisions ISR 4000 by PnP using only a UDI?
Refer to the exhibit.
The network design team has advised to use private IP addresses and private colors over the SP circuit for the data plane connections. The Public IP should be used for control connections. Which configuration should be applied at SiteA to achieve this task?

A customer has MPLS and Internet as the TLOC colors An engineer must configure conlroJIers with the Internet and not with MPLS Which configuration achieves this requirement on vManage?
A)

B)

C)
D)
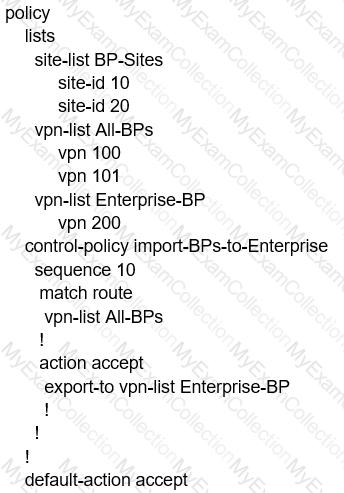
A network engineer must configure all branches to communicate with each other through the Service Chain Firewall located at the headquarters site. Which configuration allows the engineer to accomplish this task?
A)
B)
C)
D)
An enterprise needs DIA on some of its branches with a common location ID: A041:B70C: D78E::18 Which WAN Edge configuration meets the requirement?
A)
B)
C)
D)
Which two services are critical for zero touch provisioning on-boarding? (Choose two)
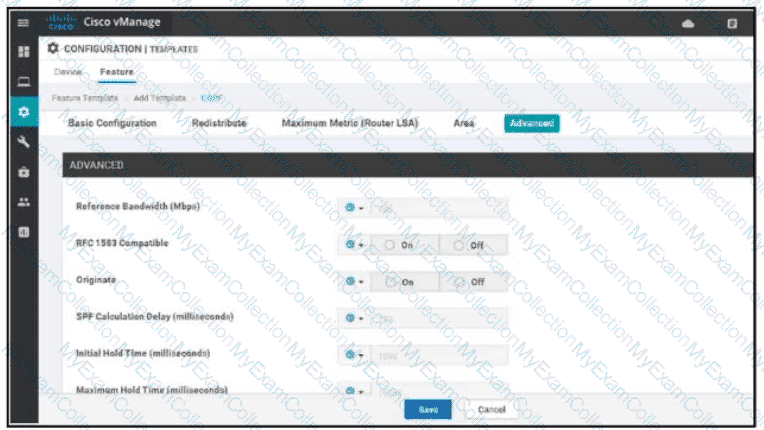
Refer to the exhibit. A network administrator is configuring OSPF advanced configuration pararmeters from a template using the vManager GUI for a branch WAN Edge router to calculate the cost of summary routes to an ASBR. Which action achieves this configuration?
In the Cisco SD_WAN solution, vSmart controller is responsible for which two actions? (Choose two.)
An engineer is configuring a list that matches all IP prefixes with lengths from /1 to /16 in a centralized control policy. Which list accomplishes this task?
Which queue must an engineer configure for control and BFD traffic for convergence on a WAN Edge router?
Which configuration allows VPN 10 traffic to have direct internet access locally from the WAN Edge device?
A)
B)
C)
D)
Which data policy configuration influences BGP routing traffic flow from LAN to WAN?
A)
B)
C)
D)
A bank is looking for improved customer experience for applications and reduce overhead related to compliance and security. Which key feature or features of the Cisco SD-WAN solution will help the bank to achieve their goals?
Which value of the IPsec rekey timer must be set by the engineer for an OMP graceful restart value set for 24 hours?
Which website allows access to visualize the geography screen from vManager using the internet?
The Cisco SD-WAN engineer is configuring service chaining for a next-generation firewall located at the headquarters. Which configuration creates the service?
A)
B)
C)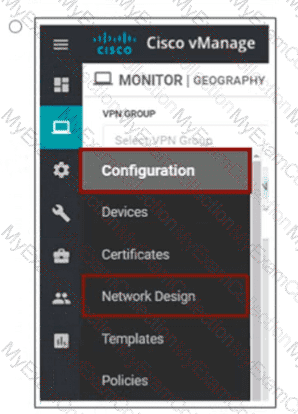
D)
Which type of connection is created between a host VNet and a transit VNet when configuring Cloud OnRamp for laaS?
Which two vRoute attributes should be matched or set in vSmart policies and modified by data policies? (Choose two.)
Refer to the exhibit A WAN Edge device was recently added to vManage but a control connection could not be established Which action resolves this issue?
REST applications communicate over HTTP or HTTPS to make calls between network devices. Which two HTTPS standard methods are included? (Choose two.)
An engineer is adding a tenant with location JD 306432373 in vManage. What is the maximum number of alphanumeric characters that are accepted in the tenant name field?
Which type of route represents prefixes received from a local site via an SD-WAN Edge router in a Cisco SD-WAN architecture?
Which service VPN must be reachable from all WAN Edge devices and the controllers?
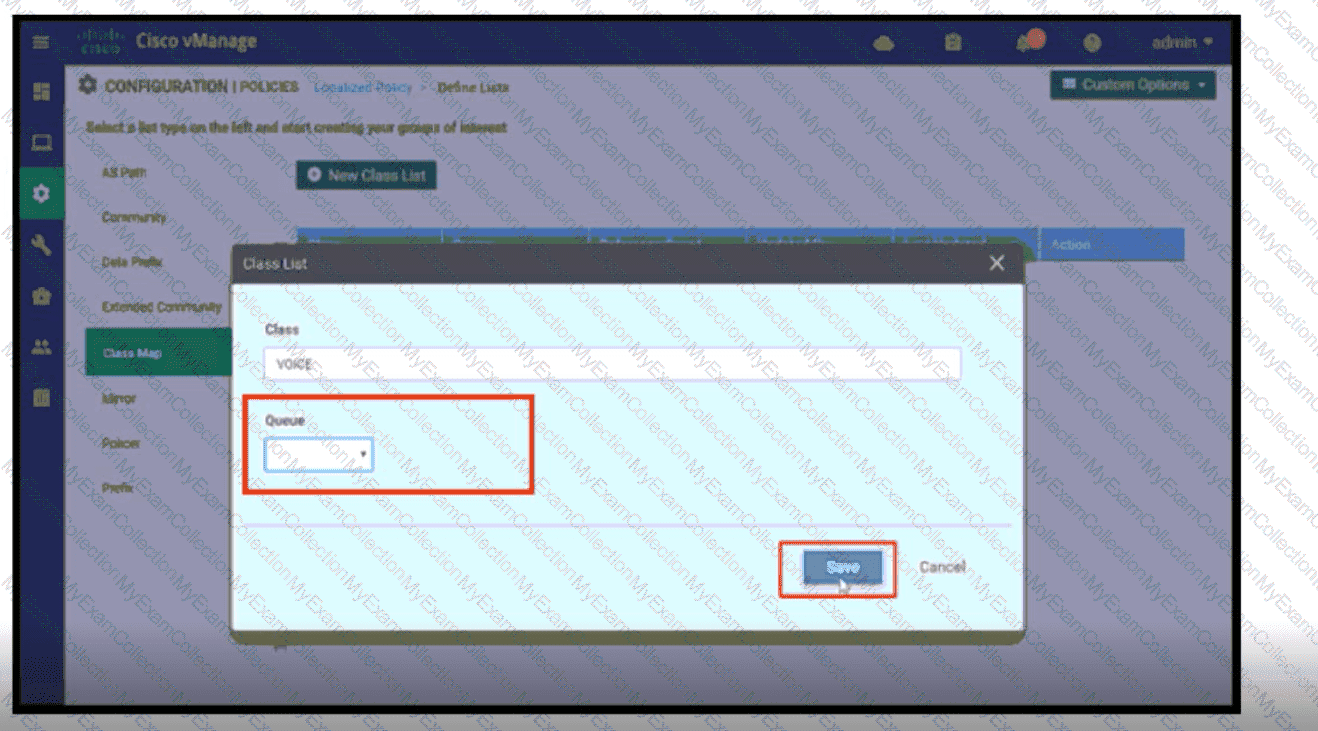
Refer to the exhibit. A network administrator is setting the queueing value for voice traffic for one of the WAN Edge routers using vManager GUI. Which queue value must be set to accomplish this task?
Refer to the exhibit.
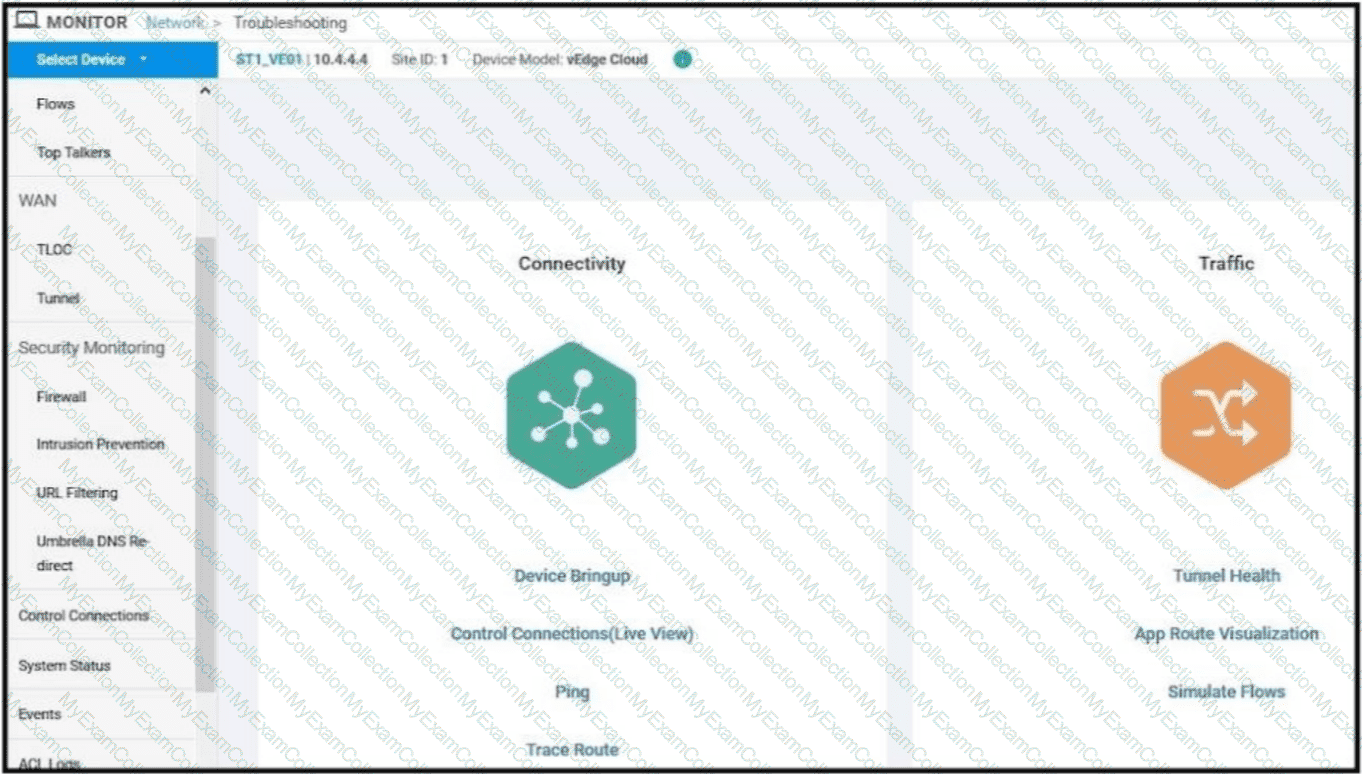
An enterprise has enabled load balancing over MPLS and Internet links. Which feature from the monitoring tool does an engineer use to visualize the available links utilized by the data traffic between Service VPNs?
If Smart Account Sync is not used, which Cisco SD-WAN component is used to upload an authorized serial number file?
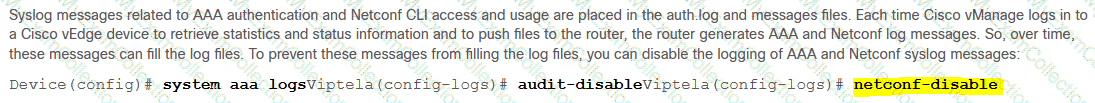
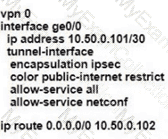
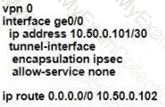
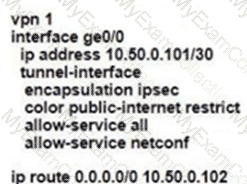
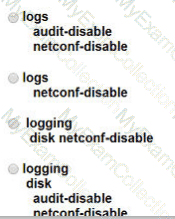
Refer to the exhibit. Which configuration stops Netconf CLI logging on WAN Edge devices during migration?
How must the application-aware enterprise firewall policies be applied within the same WAN Edge router?
What are the two impacts of losing vManage connectivity to fabric in the Cisco SD-WAN network? (Choose two)
How is a TLOC uniquely identified from a WAN Edge router to the SD-WAN transport network?
Which two products that perform lifecycle management for virtual instances are supported by WAN Edge cloud routers? (Choose two.)
Which command verifies a policy that has been pushed to the vEdge router?
Which protocol is used for the vManage to connect to the vSmart Controller hosted in Cloud?
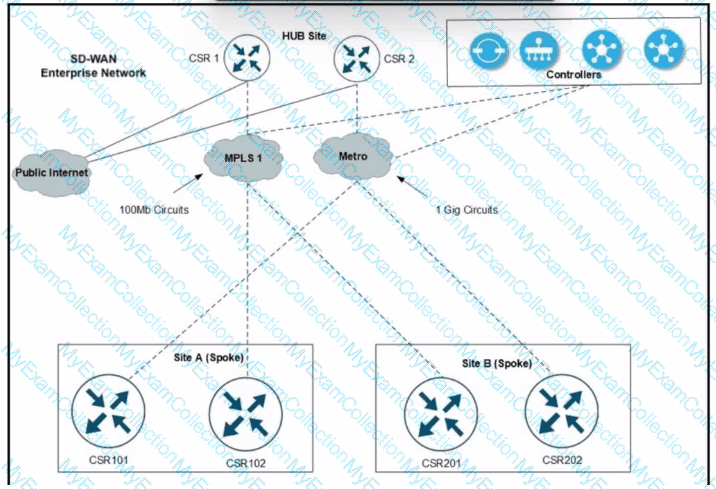
Refer to the exhibit. A Cisco SD-WAN network carries traffic for several departments and over 1200 users with several applications at site A and site B branches over the MPLS1 circuit. An engineer is provisioning a higher bandwidth on-demand metro circuit as a backup connection. Which two configurations must the engineer apply to implement the on-demand tunnels? (Choose two.)
Refer to the exhibit. The ge0/0 interface connects to a 30-MB link. A network administrator wants to always have 10 MB available for high priority traffic. When lower-priority traffic busts exceed 20 MB. Traffic should be redirected to the second WAN interface ge0/1. Which set of configurations accomplishes this task?
A)
B)
C)
D)
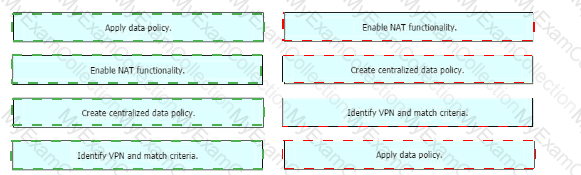
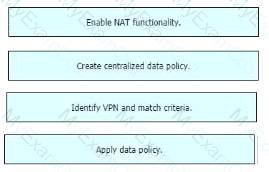
Drag and drop the actions from the left into the correct sequence on the right to create a data policy to direct traffic to the Internet exit.
Which vBond system configuration under VPN 0 allows for a routable public IP address even if the DNS name, hostname, or IP address of the vBond orchestrator are omitted?
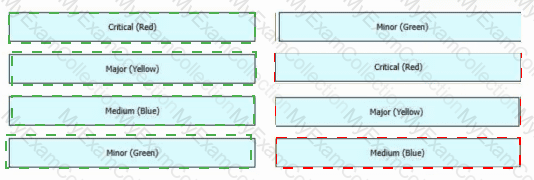
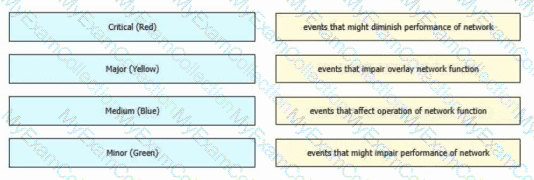
Drag and drop the alarm states from the left onto the corresponding alarm descriptions on the right.
The network administrator is configuring a QoS scheduling policy on traffic received from transport side tunnels on WAN Edge 5000 routers at location 406141498 Which command must be configured on these devices?
A policy is created to influence routing in the network using a group of prefixes. What policy application will achieve this goal when applied to a site list?