A security incident occurred with the potential of impacting business services. Who performs the attack?
Which tool is used by threat actors on a webpage to take advantage of the software vulnerabilities of a system to spread malware?
Which evasion method is being used when TLS is observed between two endpoints?
An engineer needs to configure network systems to detect command and control communications by decrypting ingress and egress perimeter traffic and allowing network security devices to detect malicious outbound communications. Which technology should be used to accomplish the task?
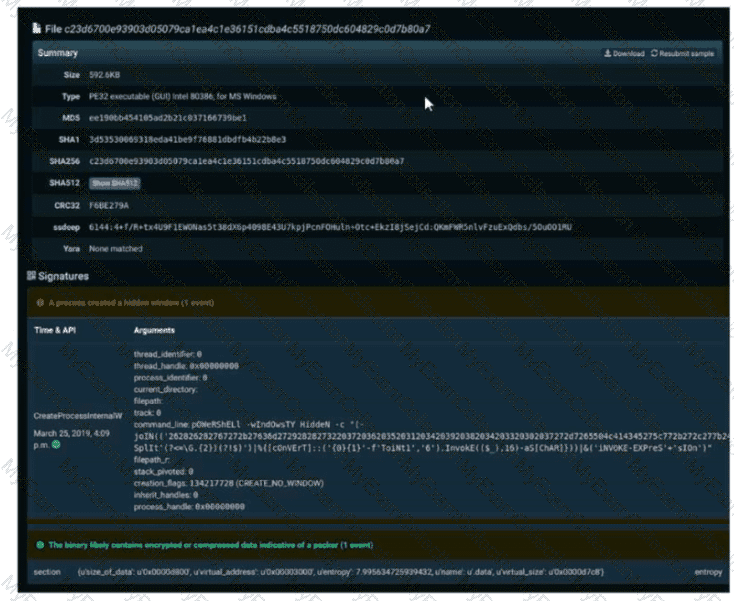
Refer to the exhibit. A SOC engineer is analyzing Cuckoo Sandbox report for a file that has been identified as suspicious by the endpoint security system. What is the state of the file?
A company receptionist received a threatening call referencing stealing assets and did not take any action assuming it was a social engineering attempt. Within 48 hours, multiple assets were breached, affecting the confidentiality of sensitive information. What is the threat actor in this incident?
The security team has detected an ongoing spam campaign targeting the organization. The team's approach is to push back the cyber kill chain and mitigate ongoing incidents. At which phase of the cyber kill chain should the security team mitigate this type of attack?
Which type of attack is a blank email with the subject "price deduction" that contains a malicious attachment?
An analyst see that this security alert "Default-Botnet-Communication-Detection-By-Endpoint" has been raised from the IPS. The analyst checks and finds that an endpoint communicates to the C&C. How must an impact from this event be categorized?
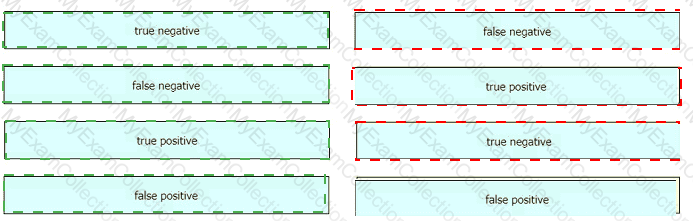
A security analyst reviews the firewall and observes the large number of frequent events. The analyst starts the packet capture with the Wireshark and identifies that TCP port reuse was detected incorrectly as a TCP split-handshake attack by the firewall. How must an impact from this event be categorized?
In digital communications, which method is recommended for securely exchanging public keys between users T0n2262144790 and D4n4126220794?
An automotive company provides new types of engines and special brakes for rally sports cars. The company has a database of inventions and patents for their engines and technical information Customers can access the database through the company's website after they register and identify themselves. Which type of protected data is accessed by customers?
Which classification of cross-site scripting attack executes the payload without storing it for repeated use?
Which security principle is violated by running all processes as root or administrator?
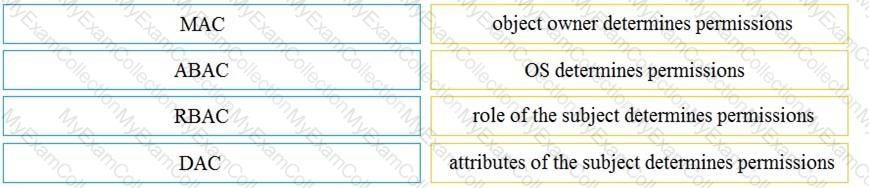
What is the difference between mandatory access control (MAC) and discretionary access control (DAC)?
Which metric in CVSS indicates an attack that takes a destination bank account number and replaces it with a different bank account number?
A security engineer must investigate a recent breach within the organization. An engineer noticed that a breached workstation is trying to connect to the domain "Ranso4730-mware92-647". which is known as malicious. In which step of the Cyber Kill Chain is this event?
What should a security analyst consider when comparing inline traffic interrogation with traffic tapping to determine which approach to use in the network?
What is the difference between statistical detection and rule-based detection models?
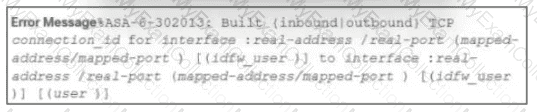
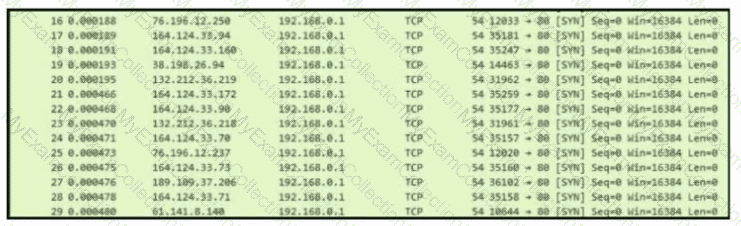
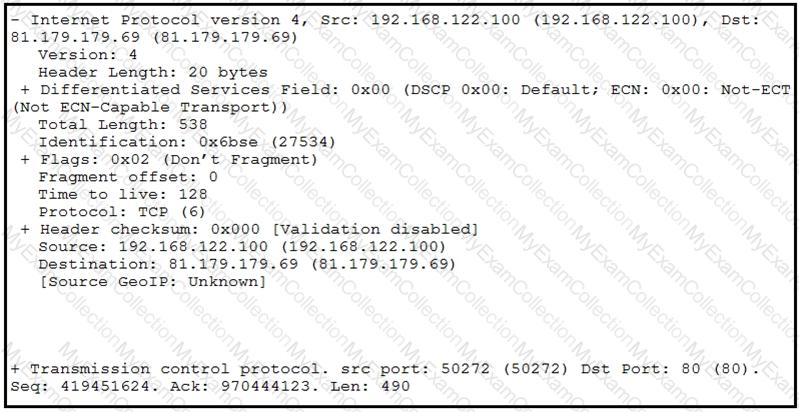
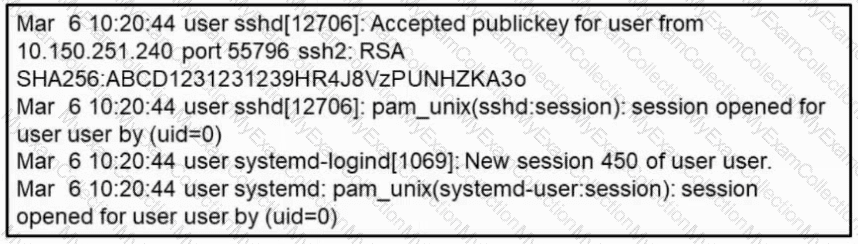
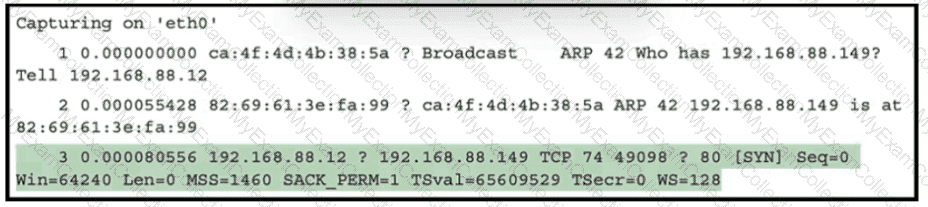
Refer to the exhibit.
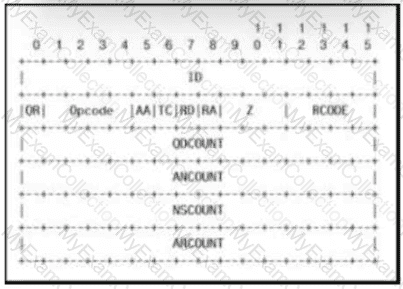
Which field contains DNS header information if the payload is a query or a response?
What is the impact of false positive alerts on business compared to true positive?
A company had a recent breach and lost confidential data to a competitor. An internal investigation found out that a new junior accounting specialist logged in to the accounting server with their user ID and stole confidential data. The junior accounting specialist denies the action and claims that the attempt was done by someone else. During court proceedings, the company presents logs and CCTV camera recordings that show the malicious insider in action. Which type of evidence has the company presented?
What is a difference between authorization and authentication from an access control perspective?
An intruder attempted malicious activity and exchanged emails with a user and received corporate information, including email distribution lists. The intruder asked the user to engage with a link in an email. When the fink launched, it infected machines and the intruder was able to access the corporate network.
Which testing method did the intruder use?
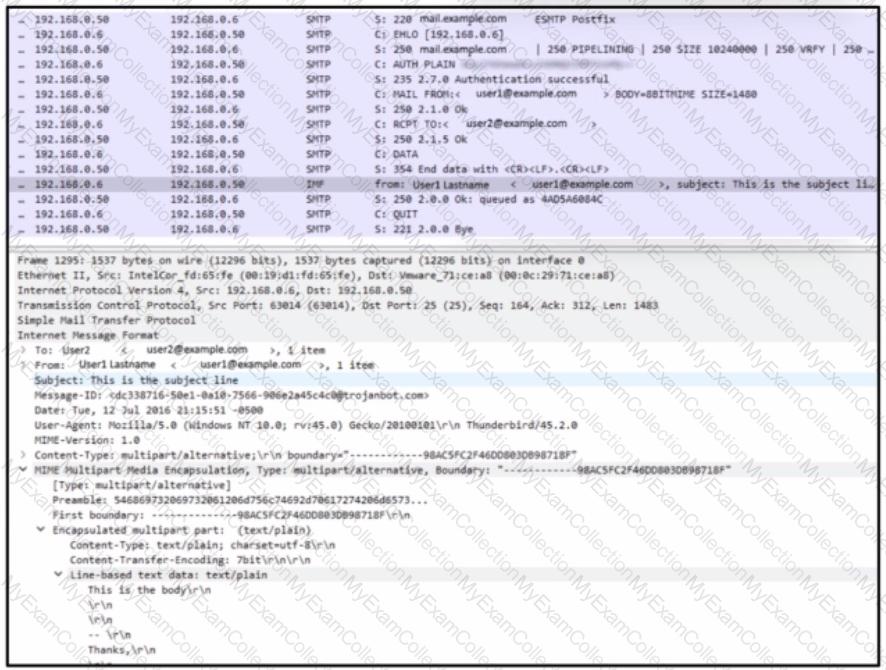
Refer to the exhibit.
During the analysis of a suspicious scanning activity incident, an analyst discovered multiple local TCP connection events Which technology provided these logs?
An employee of a company receives an email with an attachment. They notice that this email is from a suspicious source, and they decide not to open the attached file. After further investigation, a security analyst concludes that this file is malware. To which category of the Cyber Kill Chain model does this event belong?
An organization is cooperating with several third-party companies. Data exchange is on an unsecured channel using port 80 Internal employees use the FTP service to upload and download sensitive data An engineer must ensure confidentiality while preserving the integrity of the communication. Which technology must the engineer implement in this scenario'?
According to CVSS, which condition is required for attack complexity metrics?
What specific type of analysis is assigning values to the scenario to see expected outcomes?
Which metric should be used when evaluating the effectiveness and scope of a Security Operations Center?
Refer to the exhibit.
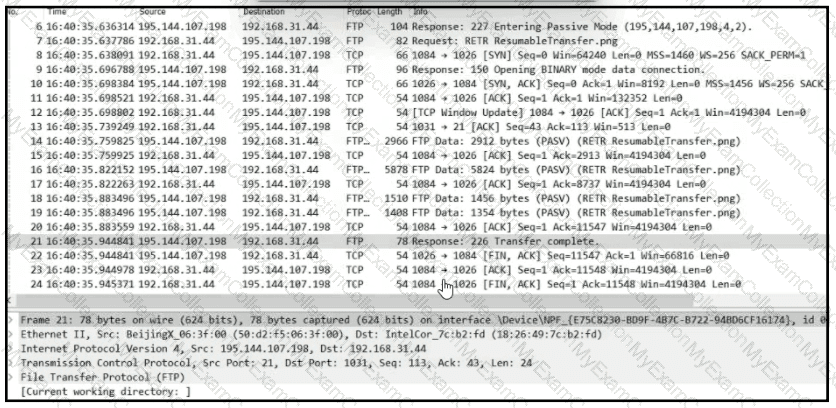
Which frame numbers contain a file that is extractable via TCP stream within Wireshark?
An analyst is investigating a host in the network that appears to be communicating to a command and control server on the Internet. After collecting this packet capture, the analyst cannot determine the technique and payload used for the communication.
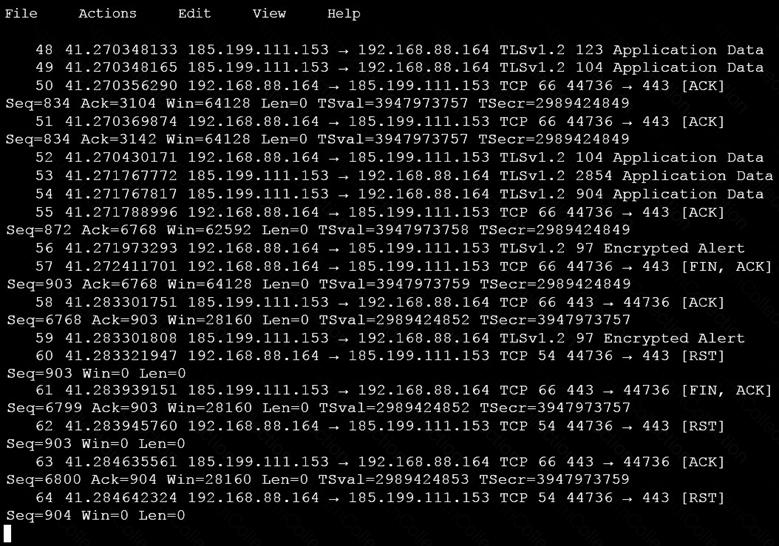
Which obfuscation technique is the attacker using?
Refer to the exhibit.
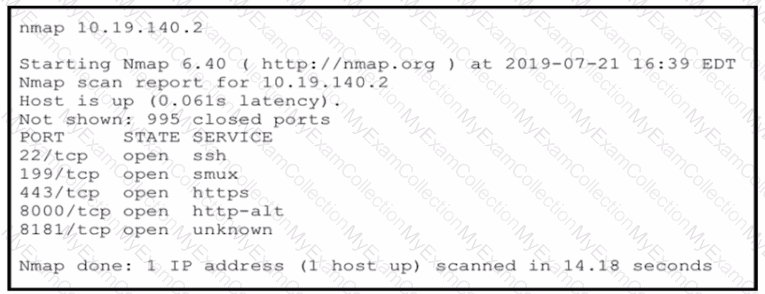
An attacker gained initial access to the company s network and ran an Nmap scan to advance with the lateral movement technique and to search the sensitive data Which two elements can an attacker identify from the scan? (Choose two.)
Which SOC metric represents the time to stop the incident from causing further damage to systems or data?
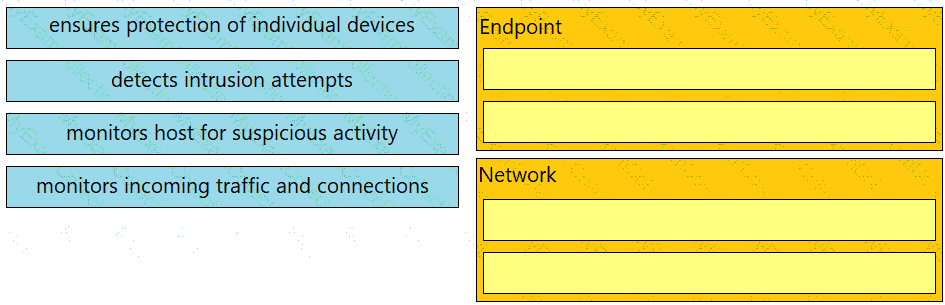
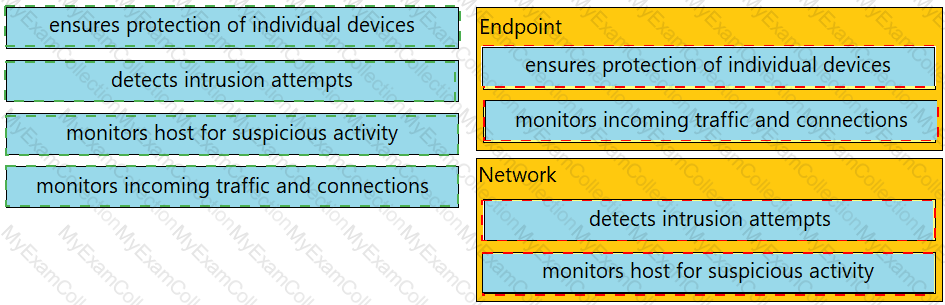
Drag and drop the uses on the left onto the type of security system on the right.
What is a difference between signature-based and behavior-based detection?
Refer to the exhibit.
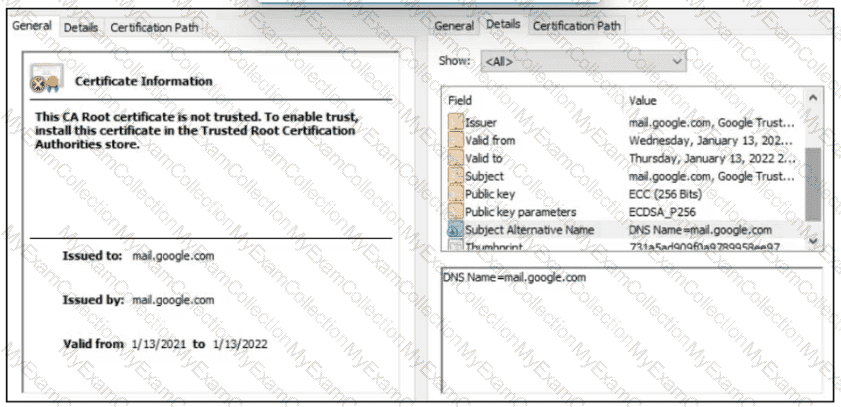
A company employee is connecting to mail google.com from an endpoint device. The website is loaded but with an error. What is occurring?
A security specialist is investigating an incident regarding a recent major breach in the organization. The accounting data from a 24-month period is affected due to a trojan detected in a department's critical server. A security analyst investigates the incident and discovers that an incident response team member who detected a trojan during regular AV scans had made an image of the server for evidence purposes. The security analyst made animage again to compare the hashes of the two images, and they appeared to differ and do not match. Which type of evidence is the security analyst dealing with?
Which technique obtains information about how the system works without knowing it's design details?
How does an SSL certificate impact security between the client and the server?
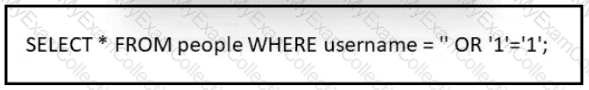
Refer to the exhibit.
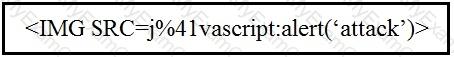
Which kind of attack method is depicted in this string?
A network engineer discovers that a foreign government hacked one of the defense contractors in their home country and stole intellectual property. What is the threat agent in this situation?
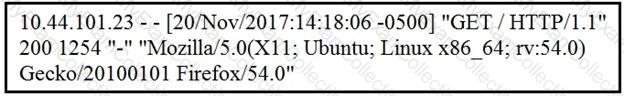
Refer to the exhibit.
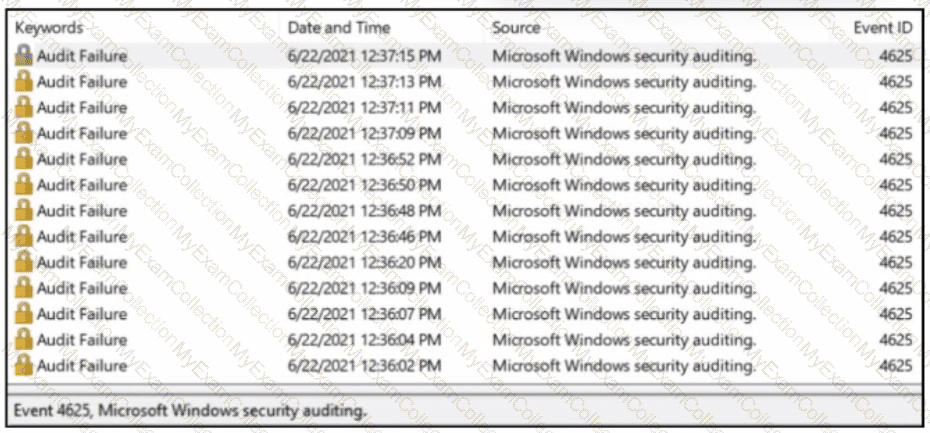
A SOC analyst received a message from SIEM about abnormal activity on the Windows server The analyst checked the Windows event log and saw numerous Audit Failures logs. What is occurring?
Drag and drop the access control models from the left onto the correct descriptions on the right.
Which type of data must an engineer capture to analyze payload and header information?
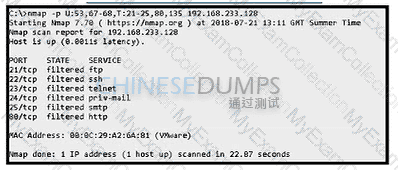
Refer to the exhibit. An attacker scanned the server using Nmap. What did the attacker obtain from this scan?
What describes the difference when comparing attack surface and vulnerability in practice?
What is the key difference between mandatory access control (MAC) and discretionary access control (DAC)?
An organization's security team has detected network spikes coming from the internal network. An investigation has concluded that the spike in traffic was from intensive network scanning How should the analyst collect the traffic to isolate the suspicious host?
Refer to the exhibit.
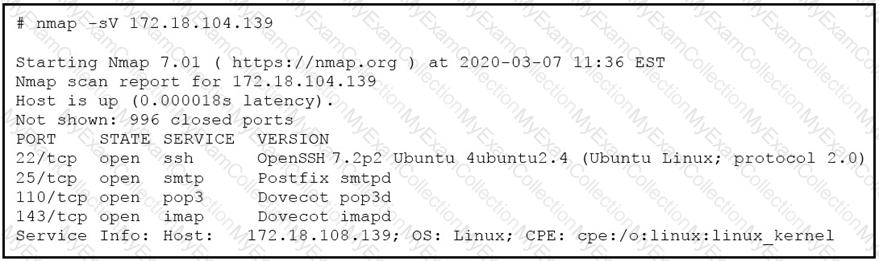
What does the output indicate about the server with the IP address 172.18.104.139?
Which security principle requires more than one person is required to perform a critical task?
One of the objectives of information security is to protect the CIA of information and systems. What does CIA mean in this context?
What is a collection of compromised machines that attackers use to carry out a DDoS attack?
An engineer is working with the compliance teams to identify the data passing through the network. During analysis, the engineer informs the compliance team that external penmeter data flows contain records, writings, and artwork Internal segregated network flows contain the customer choices by gender, addresses, and product preferences by age. The engineer must identify protected data. Which two types of data must be identified'? (Choose two.)
An analyst is investigating an incident in a SOC environment. Which method is used to identify a session from a group of logs?
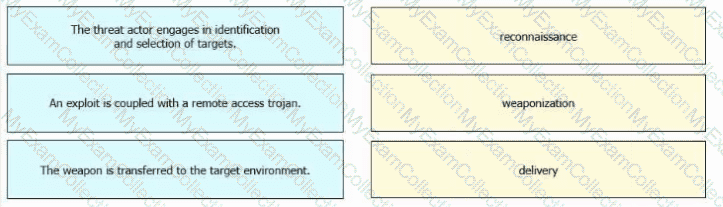
Which action matches the weaponization step of the Cyber Kill Chain model?
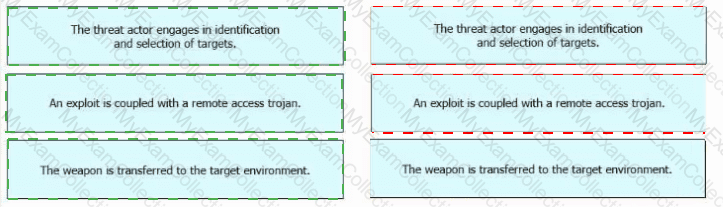
Drag and drop the definitions from the left onto the phases on the right to classify intrusion events according to the Cyber Kill Chain model.
What is the difference between indicator of attack (loA) and indicators of compromise (loC)?
Which technology assures that the information transferred from point A to point B is unaltered and authentic?
Which type of evidence supports a theory or an assumption that results from initial evidence?
Which type of attack uses a botnet to reflect requests off of an NTP server to overwhelm a target?
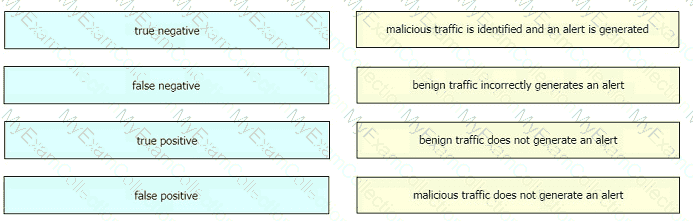
Drag and drop the event term from the left onto the description on the right.
Why should an engineer use a full packet capture to investigate a security breach?
An employee reports that someone has logged into their system and made unapproved changes, files are out of order, and several documents have been placed in the recycle bin. The security specialist reviewed the system logs, found nothing suspicious, and was not able to determine what occurred. The software is up to date; there are no alerts from antivirus and no failed login attempts. What is causing the lack of data visibility needed to detect the attack?
Which principle is being followed when an analyst gathers information relevant to a security incident to determine the appropriate course of action?
Which management concept best describes developing, operating, maintaining, upgrading, and disposing of all resources?
Refer to the exhibit.
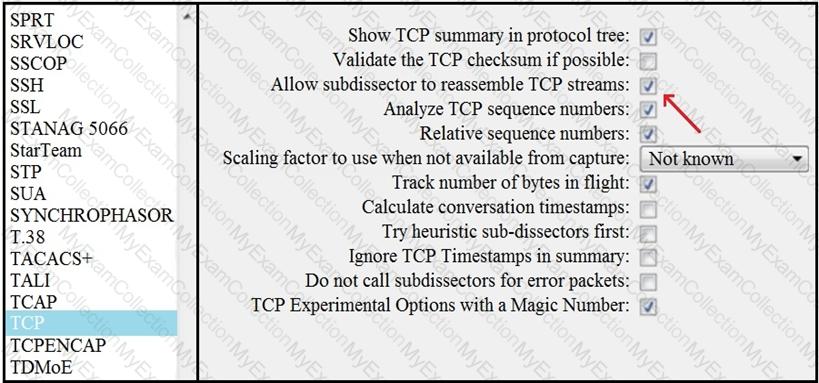
What is the expected result when the "Allow subdissector to reassemble TCP streams" feature is enabled?
What should an engineer use to aid the trusted exchange of public keys between user tom0411976943 and dan1968754032?
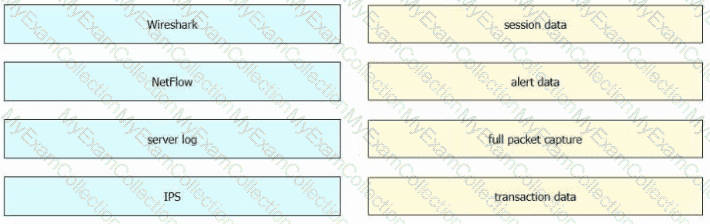
Drag and drop the data sources from the left onto the corresponding data types on the right.
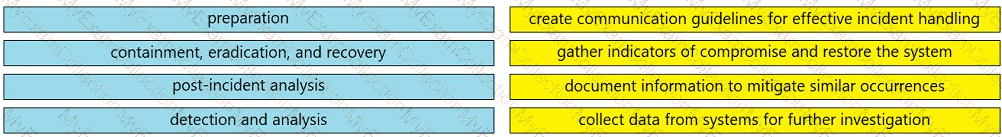
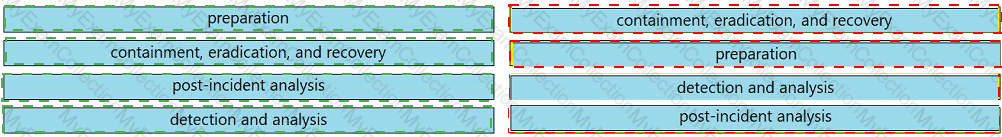
Drag and drop the elements from the left into the correct order for incident handling on the right.
Which type of verification consists of using tools to compute the message digest of the original and copied data, then comparing the similarity of the digests?
A security team receives a ticket to investigate suspicious emails sent to company employees from known malicious domains. Further analysis shows that a targeted phishing attempt was successfully blocked by the company’s email antivirus. At which step of the Cyber Kill Chain did the security team mitigate this attack?
A compliance analyst receives a complaint from a customer regarding personal data being unlawfully retained despite a deletion request. The company is based in Europe and must comply with GDPR. The only data collected is the email address 0524l9i75@gmail.com. How should the compliance analyst act?
An analyst performs traffic analysis to detect data exfiltration and identifies a high frequency of DNS requests in a small period of time Which technology makes this behavior feasible?
What is a difference between inline traffic interrogation and traffic mirroring?
An engineer received an alert affecting the degraded performance of a critical server. Analysis showed a heavy CPU and memory load. What is the next step the engineer should take to investigate this resource usage?
A forensic investigator is analyzing a recent breach case. An external USB drive was discovered to be connected and transmitting the data outside of the organization, and the owner of the USB drive could not be identified. Video surveillance shows six people during a two-month period had close contact with the affected asset. How must this type of evidence be categorized?
Which two components reduce the attack surface on an endpoint? (Choose two.)
Which technology on a host is used to isolate a running application from other applications?
A security analyst notices a sudden surge of incoming traffic and detects unknown packets from unknown senders After further investigation, the analyst learns that customers claim that they cannot access company servers According to NIST SP800-61, in which phase of the incident response process is the analyst?
During which phase of the forensic process are tools and techniques used to extract information from the collected data?
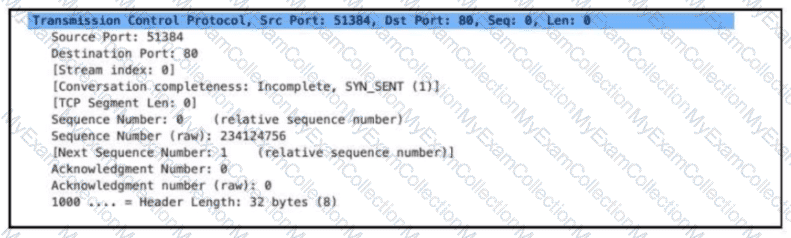
An engineer is addressing a connectivity issue between two servers where the remote server is unable to establish a successful session. Initial checks show that the remote server is not receiving an SYN-ACK while establishing a session by sending the first SYN. What is causing this issue?
What is a difference between rule-based and role-based access control mechanisms?
What causes events on a Windows system to show Event Code 4625 in the log messages?
An analyst received a ticket about degraded processing capability for one of the HR department's servers. On the same day, an engineer noticed disabled antivirus software and could not determine when or why it occurred. According to the NIST Incident Handling Guide, what is the next phase of this investigation?
When an event is investigated, which type of data provides the investigate capability to determine if data exfiltration has occurred?
Which two measures are used by the defense-m-depth strategy? (Choose two)

 A screenshot of a computer Description automatically generated
A screenshot of a computer Description automatically generated
 A close-up of several blue rectangular boxes Description automatically generated
A close-up of several blue rectangular boxes Description automatically generated