Which web services protocol is used to communicate to the Check Point R81 Identity Awareness Web API?
What is the recommended configuration when the customer requires SmartLog indexing for 14 days and SmartEvent to keep events for 180 days?
Which Check Point process provides logging services, such as forwarding logs from Gateway to Log Server, providing Log Export API (LEA) & Event Logging API (EL-A) services.
Identity Awareness allows easy configuration for network access and auditing based on what three items?
Alice & Bob are going to use Management Data Plane Separation and therefore the routing separation needs to be enabled. Which of the following command is true for enabling the Management Data Plane Separation (MDPS):
After some changes in the firewall policy you run into some issues. You want to test if the policy from two weeks ago have the same issue. You don't want to lose the changes from the last weeks. What is the best way to do it?
Packet acceleration (SecureXL) identifies connections by several attributes. Which of the attributes is NOT used for identifying connection?
You find one of your cluster gateways showing “Down†when you run the “cphaprob stat†command. You then run the “clusterXL_admin up†on the down member but unfortunately the member continues to show down. What command do you run to determine the cause?
Which Check Point software blades could be enforced under Threat Prevention profile using Check Point R81.20 SmartConsole application?
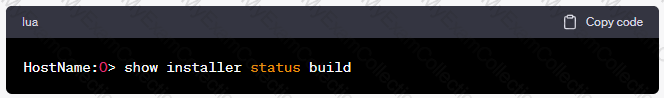
You need to see which hotfixes are installed on your gateway, which command would you use?
Using mgmt_cli, what is the correct syntax to import a host object called Server_1 from the CLI?
Which statement is WRONG regarding the usage of the Central Deployment in SmartConsole?
Customer’s R81 management server needs to be upgraded to R81.20. What is the best upgrade method when the management server is not connected to the Internet?
UserCheck objects in the Application Control and URL Filtering rules allow the gateway to communicate with the users. Which action is not supported in UserCheck objects?
According to out of the box SmartEvent policy, which blade will automatically be correlated into events?
After having saved the Clish Configuration with the "save configuration config.txt" command, where can you find the config.txt file?
SmartConsole R81 x requires the following ports to be open for SmartEvent.
If the Active Security Management Server fails or if it becomes necessary to change the Active to Standby, the following steps must be taken to prevent data loss. Providing the Active Security Management Server is responsive, which if these steps should NOT be performed:
Which Identity Source(s) should be selected in Identity Awareness Tot when there is a requirement for a higher level of security for sensitive servers?
When simulating a problem on ClusterXL cluster with cphaprob –d STOP -s problem -t 0 register, to initiate a failover on an active cluster member, what command allows you remove the problematic state?
What is the command to check the status of the SmartEvent Correlation Unit?
Please choose correct command to add an “emailserver1†host with IP address 10.50.23.90 using GAiA management CLI?
Fill in the blank: A ________ VPN deployment is used to provide remote users with secure access to internal corporate resources by authenticating the user through an internet browser.
The WebUI offers several methods for downloading hotfixes via CPUSE except:
What feature allows Remote-access VPN users to access resources across a site-to-site VPN tunnel?
Joey want to configure NTP on R81 Security Management Server. He decided to do this via WebUI. What is the correct address to access the Web UI for Gaia platform via browser?
What object type would you use to grant network access to an LDAP user group?
Which is the command to identify the NIC driver before considering about the employment of the Multi-Queue feature?
In R81.20 a new feature dynamic log distribution was added. What is this for?
- Configure the Security Gateway to distribute logs between multiple active Log Servers to support a better rate of Logs and Log Servers redundancy
- In case of a Management High Availability the management server stores the logs dynamically on the member with the most available disk space in /var/log
- Synchronize the log between the primary and secondary management server in case of a Management High Availability
What are valid authentication methods for mutual authenticating the VPN gateways?
Hit Count is a feature to track the number of connections that each rule matches, which one is not benefit of Hit Count.
In the Check Point Security Management Architecture, which component(s) can store logs?
Which Check Point software blade provides visibility of users, groups and machines while also providing access control through identity-based policies?
Check Point recommends configuring Disk Space Management parameters to delete old log entries when available disk space is less than or equal to?
R81.20 management server can manage gateways with which versions installed?
The SmartEvent R81 Web application for real-time event monitoring is called:
Fill in the blank: Browser-based Authentication sends users to a web page to acquire identities using ________ .
What is the most ideal Synchronization Status for Security Management Server High Availability deployment?
What kind of information would you expect to see using the sim affinity command?
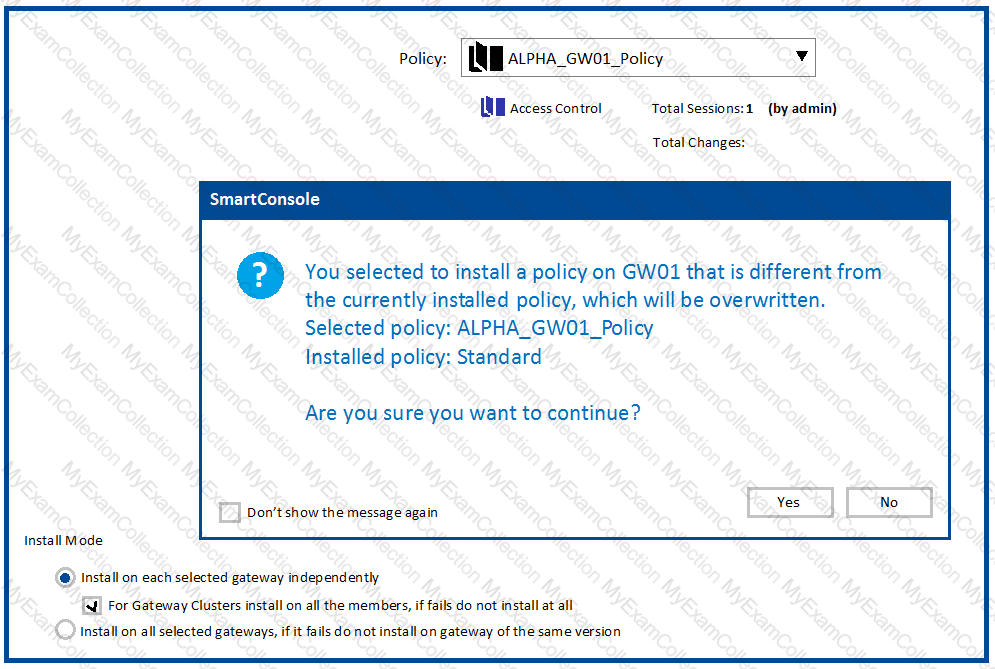
One of major features in R81 SmartConsole is concurrent administration.
Which of the following is NOT possible considering that AdminA, AdminB and AdminC are editing the same Security Policy?
To ensure that VMAC mode is enabled, which CLI command should you run on all cluster members?
Which tool provides a list of trusted files to the administrator so they can specify to the Threat Prevention blade that these files do not need to be scanned or analyzed?
Ken wants to obtain a configuration lock from other administrator on R81 Security Management Server. He can do this via WebUI or via CLI.
Which command should he use in CLI? (Choose the correct answer.)
What is the recommended number of physical network interfaces in a Mobile Access cluster deployment?
You want to verify if your management server is ready to upgrade to R81.20. What tool could you use in this process?
Fill in the blank: The R81 SmartConsole, SmartEvent GUI client, and _______ consolidate billions of logs and shows then as prioritized security events.
Capsule Connect and Capsule Workspace both offer secured connection for remote users who are using their mobile devices. However, there are differences between the two.
Which of the following statements correctly identify each product's capabilities?
Fill in the blank: Identity Awareness AD-Query is using the Microsoft _______________ API to learn users from AD.
You have a Gateway is running with 2 cores. You plan to add a second gateway to build a cluster and used a device with 4 cores.
How many cores can be used in a Cluster for Firewall-kernel on the new device?
When SecureXL is enabled, all packets should be accelerated, except packets that match the following conditions:
Which command would you use to set the network interfaces’ affinity in Manual mode?
Which file gives you a list of all security servers in use, including port number?
You notice that your firewall is under a DDoS attack and would like to enable the Penalty Box feature, which command you use?
What is the minimum amount of RAM needed for a Threat Prevention Appliance?
Tom has connected to the R81 Management Server remotely using SmartConsole and is in the process of making some Rule Base changes, when he suddenly loses connectivity. Connectivity is restored shortly afterward.
What will happen to the changes already made?
Which file contains the host address to be published, the MAC address that needs to be associated with the IP Address, and the unique IP of the interface that responds to ARP request?
During the Check Point Stateful Inspection Process, for packets that do not pass Firewall Kernel Inspection and are rejected by the rule definition, packets are:
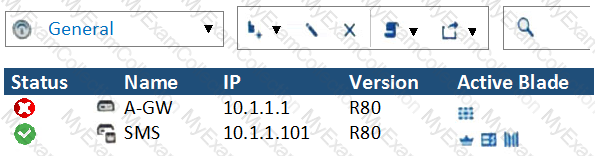
What does it mean if Deyra sees the gateway status? (Choose the BEST answer.)
After the initial installation on Check Point appliance, you notice that the Management-interface and default gateway are incorrect.
Which commands could you use to set the IP to 192.168.80.200/24 and default gateway to 192.168.80.1.
Which statement is most correct regarding about “CoreXL Dynamic Dispatcher�
Fill in the blank. Once a certificate is revoked from the Security Gateway by the Security Management Server, the certificate information is ________ .
Pamela is Cyber Security Engineer working for Global Instance Firm with large scale deployment of Check Point Enterprise Appliances using GAiA/R81.20. Company’s Developer Team is having random access issue to newly deployed Application Server in DMZ’s Application Server Farm Tier and blames DMZ Security Gateway as root cause. The ticket has been created and issue is at Pamela’s desk for an investigation. Pamela decides to use Check Point’s Packet Analyzer Tool-fw monitor to iron out the issue during approved Maintenance window.
What do you recommend as the best suggestion for Pamela to make sure she successfully captures entire traffic in context of Firewall and problematic traffic?
What is correct statement about Security Gateway and Security Management Server failover in Check Point R81.X in terms of Check Point Redundancy driven solution?
Which of the following is NOT an option to calculate the traffic direction?
Vanessa is a Firewall administrator. She wants to test a backup of her company’s production Firewall cluster Dallas_GW. She has a lab environment that is identical to her production environment. She decided to restore production backup via SmartConsole in lab environment.
Which details she need to fill in System Restore window before she can click OK button and test the backup?
After trust has been established between the Check Point components, what is TRUE about name and IP-address changes?
During inspection of your Threat Prevention logs you find four different computers having one event each with a Critical Severity. Which of those hosts should you try to remediate first?
NAT rules are prioritized in which order?
1. Automatic Static NAT
2. Automatic Hide NAT
3. Manual/Pre-Automatic NAT
4. Post-Automatic/Manual NAT rules
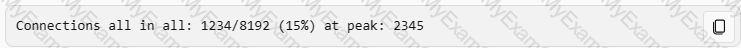
Which command can you use to verify the number of active concurrent connections?
To fully enable Dynamic Dispatcher with Firewall Priority Queues on a Security Gateway, run the following command in Expert mode then reboot:
SSL Network Extender (SNX) is a thin SSL VPN on-demand client that is installed on the remote user’s machine via the web browser. What are the two modes of SNX?
Check Point Management (cpm) is the main management process in that it provides the architecture for a consolidates management console. CPM allows the GUI client and management server to communicate via web services using ___________.
The Firewall Administrator is required to create 100 new host objects with different IP addresses. What API command can he use in the script to achieve the requirement?
GAIA greatly increases operational efficiency by offering an advanced and intuitive software update agent, commonly referred to as the:
Which of the following is NOT a method used by identity Awareness for acquiring identity?
Which is the lowest gateway version supported by R81.20 management server?
Mobile Access Gateway can be configured as a reverse proxy for Internal Web Applications Reverse proxy users browse to a URL that is resolved to the Security Gateway IP address. Which of the following Check Point command is true for enabling the Reverse Proxy:
Which of the following is NOT a type of Check Point API available in R81.x?
As a valid Mobile Access Method, what feature provides Capsule Connect/VPN?
SandBlast has several functional components that work together to ensure that attacks are prevented in real-time. Which the following is NOT part of the SandBlast component?
Fill in the blank: The tool _____ generates a R81 Security Gateway configuration report.
Which two of these Check Point Protocols are used by SmartEvent Processes?
You want to gather and analyze threats to your mobile device. It has to be a lightweight app. Which application would you use?
When requiring certificates for mobile devices, make sure the authentication method is set to one of the following, Username and Password, RADIUS or ________.
You are working with multiple Security Gateways enforcing an extensive number of rules. To simplify security administration, which action would you choose?
SmartEvent does NOT use which of the following procedures to identify events:
To add a file to the Threat Prevention Whitelist, what two items are needed?
Can multiple administrators connect to a Security Management Server at the same time?
To accelerate the rate of connection establishment, SecureXL groups all connection that match a particular service and whose sole differentiating element is the source port. The type of grouping enables even the very first packets of a TCP handshake to be accelerated. The first packets of the first connection on the same service will be forwarded to the Firewall kernel which will then create a template of the connection. Which of the these is NOT a SecureXL template?
Which of the following authentication methods ARE NOT used for Mobile Access?
Check Pont Central Deployment Tool (CDT) communicates with the Security Gateway / Cluster Members over Check Point SIC _______ .
CPM process stores objects, policies, users, administrators, licenses and management data in a database. The database is:
In a Client to Server scenario, which inspection point is the first point immediately following the tables and rule base check of a packet coming from outside of the network?
When doing a Stand-Alone Installation, you would install the Security Management Server with which other Check Point architecture component?
If you needed the Multicast MAC address of a cluster, what command would you run?
Tom has been tasked to install Check Point R81 in a distributed deployment. Before Tom installs the systems this way, how many machines will he need if he does NOT include a SmartConsole machine in his calculations?
You can select the file types that are sent for emulation for all the Threat Prevention profiles. Each profile defines a(n) _____ or _____ action for the file types.
The CPD daemon is a Firewall Kernel Process that does NOT do which of the following?
Fill in the blank: The R81 utility fw monitor is used to troubleshoot ______________________.
What are the different command sources that allow you to communicate with the API server?
The fwd process on the Security Gateway sends logs to the fwd process on the Management Server via which 2 processes?
You want to store the GAIA configuration in a file for later reference. What command should you use?
Which of the following type of authentication on Mobile Access can NOT be used as the first authentication method?
Which of the following Check Point processes within the Security Management Server is responsible for the receiving of log records from Security Gateway?
Which command can you use to enable or disable multi-queue per interface?
What makes Anti-Bot unique compared to other Threat Prevention mechanisms, such as URL Filtering, Anti-Virus, IPS, and Threat Emulation?
The Security Gateway is installed on GAIA R81. The default port for the Web User Interface is ______ .
What is the main difference between Threat Extraction and Threat Emulation?
When gathering information about a gateway using CPINFO, what information is included or excluded when using the “-x†parameter?
In SmartEvent, what are the different types of automatic reactions that the administrator can configure?
After making modifications to the $CVPNDIR/conf/cvpnd.C file, how would you restart the daemon?
What is the port used for SmartConsole to connect to the Security Management Server?
With Mobile Access enabled, administrators select the web-based and native applications that can be accessed by remote users and define the actions that users can perform the applications. Mobile Access encrypts all traffic using:
SmartConsole R81 requires the following ports to be open for SmartEvent R81 management:
Both ClusterXL and VRRP are fully supported by Gaia R81.20 and available to all Check Point appliances. Which the following command is NOT related to redundancy and functions?
What is a best practice before starting to troubleshoot using the “fw monitor†tool?
SandBlast offers flexibility in implementation based on their individual business needs. What is an option for deployment of Check Point SandBlast Zero-Day Protection?
You noticed that CPU cores on the Security Gateway are usually 100% utilized and many packets were dropped. You don’t have a budget to perform a hardware upgrade at this time. To optimize drops you decide to use Priority Queues and fully enable Dynamic Dispatcher. How can you enable them?
Which is the least ideal Synchronization Status for Security Management Server High Availability deployment?