While conducting a business continuity tabletop exercise, the security team becomes concerned by potential impacts if a generator fails during failover. Which of the following is the team most likely to consider in regard to risk management activities?
A Chief Information Security Officer wants to monitor the company ' s servers for SQLi attacks and allow for comprehensive investigations if an attack occurs. The company uses SSL decryption to allow traffic monitoring. Which of the following strategies would best accomplish this goal?
Which of the following describes when a user installs an unauthorized application by bypassing the authorized application store and installing a binary file?
After failing an audit twice, an organization has been ordered by a government regulatory agency to pay fines. Which of the following caused this action?
A security officer is implementing a security awareness program and is placing security-themed posters around the building and is assigning online user training. Which of the following would the security officer most likely implement?
An organization has issues with deleted network share data and improper permissions. Which solution helps track and remediate these?
An employee clicked a malicious link in an email and downloaded malware onto the company ' s computer network. The malicious program exfiltrated thousands of customer records. Which of the following should the company implement to prevent this in the future?
A security analyst is reviewing logs and discovers the following:
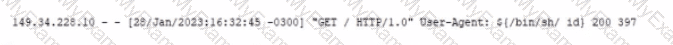
Which of the following should be used lo best mitigate this type of attack?
A company is implementing a vendor ' s security tool in the cloud. The security director does not want to manage users and passwords specific to this tool but would rather utilize the company ' s standard user directory. Which of the following should the company implement?
Which of the following should be deployed on an externally facing web server in order to establish an encrypted connection?
An IT manager is putting together a documented plan describing how the organization will keep operating in the event of a global incident. Which of the following plans is the IT manager creating?
A company wants to minimize the chance of its outgoing marketing emails getting flagged as spam. The company decides to list the email servers on the proper DNS record. Which of the following protocols should the company apply next?
A systems administrator creates a script that validates OS version, patch levels, and installed applications when users log in. Which of the following examples best describes the purpose of this script?
A security analyst developed a script to automate a trivial and repeatable task. Which of the following best describes the benefits of ensuring other team members understand how the script works?
A company receives an alert that a widely used network device vendor has been banned by the government. What will general counsel most likely be concerned with during hardware refresh?
Which of the following strategies most effectively protects sensitive data at rest in a database?
A wireless administrator sets up a new network in a small office using a password. The network must reduce the impact of brute-force attacks if the password is subjected to over-the-air interception. Which of the following security settings will help achieve this goal?
Which of the following incident response activities ensures evidence is properly handied?
Which of the following is the best way to consistently determine on a daily basis whether security settings on servers have been modified?
A cyber operations team informs a security analyst about a new tactic malicious actors are using to compromise networks.
SIEM alerts have not yet been configured. Which of the following best describes what the security analyst should do to identify this behavior?
A company is developing a critical system for the government and storing project information on a fileshare. Which of the following describes how this data will most likely be classified? (Select two).
A software developer would like to ensure. The source code cannot be reverse engineered or debugged. Which of the following should the developer consider?
An organization is struggling with scaling issues on its VPN concentrator and internet circuit due to remote work. The organization is looking for a software solution that will allow it to reduce traffic on the VPN and internet circuit, while still providing encrypted tunnel access to the data center and monitoring of remote employee internet traffic. Which of the following will help achieve these objectives?
Which of the following tools can assist with detecting an employee who has accidentally emailed a file containing a customer’s PII?
Which of the following agreements defines response time, escalation, and performance metrics?
Which of the following is used to add extra complexity before using a one-way data transformation algorithm?
A systems administrator works for a local hospital and needs to ensure patient data is protected and secure. Which of the following data classifications should be used to secure patient data?
After a recent vulnerability scan, a security engineer needs to harden the routers within the corporate network. Which of the following is the most appropriate to disable?
An organization wants a third-party vendor to do a penetration test that targets a specific device. The organization has provided basic information about the device. Which of the following best describes this kind of penetration test?
An enterprise is trying to limit outbound DNS traffic originating from its internal network. Outbound DNS requests will only be allowed from one device with the IP address 10.50.10.25. Which of the following firewall ACLs will accomplish this goal?
Which of the following is a benefit of an RTO when conducting a business impact analysis?
An employee receives a text message from an unknown number claiming to be the company ' s Chief Executive Officer and asking the employee to purchase several gift cards. Which of the following types of attacks does this describe?
A penetration test has demonstrated that domain administrator accounts were vulnerable to pass-the-hash attacks. Which of the following would have been the best strategy to prevent the threat actor from using domain administrator accounts?
A security officer observes that a software development team is not complying with its corporate security policy on encrypting confidential data. Which of the following categories refers to this type of non-compliance?
An administrator discovers a cross-site scripting vulnerability on a company website. Which of the following will most likely remediate the issue?
An organization’s internet-facing website was compromised when an attacker exploited a buffer overflow. Which of the following should the organization deploy to best protect against similar attacks in the future?
Alerts from email protection systems and MSSPs must be entered into an IT service management system and assigned to the security team. Which of the following should an organization implement to enable this functionality?
Which of the following would most likely be used by attackers to perform credential harvesting?
Which of the following actions is best performed by ticketing automation to ensure that incidents receive the correct level of attention and response?
Which of the following actions best addresses a vulnerability found on a company ' s web server?
A new vulnerability enables a type of malware that allows the unauthorized movement of data from a system. Which of the following would detect this behavior?
Which vulnerability is most likely mitigated by setting up an MDM platform?
A company wants to ensure secure remote access to its internal network. The company has only one public IP and would like to avoid making any changes to the current network setup. Which of the following solutions would best accomplish this goal?
Which of the following best describe why a process would require a two-person integrity security control?
Prior to implementing a design change, the change must go through multiple steps to ensure that it does not cause any security issues. Which of the following is most likely to be one of those steps?
Which of the following should a security operations center use to improve its incident response procedure?
An organization experiences a cybersecurity incident involving a command-and-control server. Which of the following logs should be analyzed to identify the impacted host? (Select two).
Which of the following elements of digital forensics should a company use If It needs to ensure the integrity of evidence?
An analyst is evaluating the implementation of Zero Trust principles within the data plane. Which of the following would be most relevant for the analyst to evaluate?
Which of the following is the primary purpose of a service that tracks log-ins and time spent using the service?
While a school district is performing state testing, a security analyst notices all internet services are unavailable. The analyst discovers that ARP poisoning is occurring on the network and then terminates access for the host. Which of the following is most likely responsible for this malicious activity?
Sine© a recent upgrade (o a WLAN infrastructure, several mobile users have been unable to access the internet from the lobby. The networking team performs a heat map survey of the building and finds several WAPs in the area. The WAPs are using similar frequencies with high power settings. Which of the following installation considerations should the security team evaluate next?
A company wants to ensure that only authorized devices can enter an environment. Which of the following will the company most likely use to implement the control?
An attacker uses XSS to compromise a web server. Which of the following solutions could have been used to prevent this attack?
Which of the following should be used to aggregate log data in order to create alerts and detect anomalous activity?
According to various privacy rules and regulations, users have the power to request that all data pertaining to them is deleted. This is known as:
A new corporate policy requires all staff to use multifactor authentication to access company resources. Which of the following can be utilized to set up this form of identity and access management? (Select two)
Which of the following are cases in which an engineer should recommend the decommissioning of a network device? (Select two).
Which of the following should an internal auditor check for first when conducting an audit of the organization ' s risk management program?
Which of the following risk analysis attributes measures the chance that a vulnerability will be exploited?
A security administrator receives multiple reports about the same suspicious email. Which of the following is the most likely reason for the malicious email ' s continued delivery?
Which of the following methods would most likely be used to identify legacy systems?
A security analyst and the management team are reviewing the organizational performance of a recent phishing campaign. The user click-through rate exceeded the acceptable risk threshold, and the management team wants to reduce the impact when a user clicks on a link in a phishing message. Which of the following should the analyst do?
An organization wants to limit potential impact to its log-in database in the event of a breach. Which of the following options is the security team most likely to recommend?
A network administrator deploys an FDE solution on all end user workstations. Which of the following data protection strategies does this describe?
Which of the following is a social engineering attack in which a bad actor impersonates a web URL?
Which of the following would enable a data center to remain operational through a multiday power outage?
A software development manager wants to ensure the authenticity of the code created by the company. Which of the following options is the most appropriate?
The management team reports employees are missing features on company-provided tablets, causing productivity issues. The team directs IT to resolve the issue within 48 hours. Which of the following is the best solution?
Which of the following is the best safeguard to protect against an extended power failure?
An organization has recently decided to implement SSO. The requirements are to leverage access tokens and focus on application authorization rather than user authentication. Which of the following solutions would the engineering team most likely configure?
Which of the following is best used to detect fraud by assigning employees to different roles?
A malicious update was distributed to a common software platform and disabled services at many organizations. Which of the following best describes this type of vulnerability?
A company is changing its mobile device policy. The company has the following requirements:
Company-owned devices
Ability to harden the devices
Reduced security risk
Compatibility with company resources
Which of the following would best meet these requirements?
Which of the following phases of an incident response involves generating reports?
Which of the following threat actors is the most likely to use large financial resources to attack critical systems located in other countries?
While considering the organization ' s cloud-adoption strategy, the Chief Information Security Officer sets a goal to outsource patching of firmware, operating systems, and applications to the chosen cloud vendor. Which of the following best meets this goal?
A company ' s Chief Information Security Officer (CISO) wants to enhance the capabilities of the incident response team. The CISO directs the incident response team to deploy a tool that rapidlyanalyzes host and network data from potentially compromised systems and forwards the data for further review. Which of the following tools should the incident response team deploy?
A company relies on open-source software libraries to build the software used by its customers. Which of the following vulnerability types would be the most difficult to remediate due to the company ' s reliance on open-source libraries?
Which of the following is an example of a data protection strategy that uses tokenization?
An organization is implementing a COPE mobile device management policy. Which of the following should the organization include in the COPE policy? (Select two).
An attorney prints confidential documents to a copier in an office space near multiple workstations and a reception desk. When the attorney goes to the copier to retrieve the documents, the documents are missing. Which of the following would best prevent this from reoccurring?
A client demands at least 99.99% uptime from a service provider ' s hosted security services. Which of the following documents includes the information the service provider should return to the client?
Various stakeholders are meeting to discuss their hypothetical roles and responsibilities in a specific situation, such as a security incident or major disaster. Which of the following best describes this meeting?
In which of the following scenarios is tokenization the best privacy technique 10 use?
Which of the following is the best way to prevent an unauthorized user from plugging a laptop into an employee ' s phone network port and then using tools to scan for database servers?
An organization experiences a suspected data breach that affects sensitive client information. The incident response team must preserve logs, server images, and email communications related to the breach. Which of the following best describes this course of action?
A security engineer is installing an IPS to block signature-based attacks in the environment. Which of the following modes will best accomplish this task?
Which of the following describes a situation where a user is authorized before being authenticated?
Which of the following is used to validate a certificate when it is presented to a user?
A security analyst receives an alert that there was an attempt to download known malware. Which of the following actions would allow the best chance to analyze the malware?
Which of the following best describes the main difference between an MOU and an SOW?
An employee fell for a phishing scam, which allowed an attacker to gain access to a company PC. The attacker scraped the PC’s memory to find other credentials. Without cracking these credentials, the attacker used them to move laterally through the corporate network. Which of the following describes this type of attack?
An employee decides to collect PII data from the company ' s system for personal use. The employee compresses the data into a single encrypted file before sending the file to their personal email. The security department becomes aware of the attempted misuse and blocks the attachment from leaving the corporate environment. Which of the following types of employee training would most likely reduce the occurrence of this type of issue?
(Select two).
A company ' s accounts payable clerk receives a message from a vendor asking to change their bank account before paying an invoice. The clerk makes the change and sends the payment to the new account. Days later, the clerk receives another message from the same vendor with a request for a missing payment to the original bank account. Which of the following has most likely occurred?
Which of the following best protects sensitive data in transit across a geographically dispersed Infrastructure?
A new security regulation was announced that will take effect in the coming year. A company must comply with it to remain in business. Which of the following activities should the company perform next?
An administrator is installing an SSL certificate on a new system. During testing, errors indicate that the certificate is not trusted. The administrator has verified with the issuing CA and has validated the private key. Which of the following should the administrator check for next?
Which of the following activities should a systems administrator perform to quarantine a potentially infected system?
A systems administrator is working on a solution with the following requirements:
• Provide a secure zone.
• Enforce a company-wide access control policy.
• Reduce the scope of threats.
Which of the following is the systems administrator setting up?
A security administrator observed the following in a web server log while investigating an incident:

Which of the following attacks did the security administrator most likely see?
An organization is adopting cloud services at a rapid pace and now has multiple SaaS applications in use. Each application has a separate log-in. so the security team wants to reduce the number of credentials each employee must maintain. Which of the following is the first step the security team should take?
A company discovers suspicious transactions that were entered into the company ' s database and attached to a user account that was created as a trap for malicious activity. Which of the following is the user account an example of?
A security administrator recently reset local passwords and the following values were recorded in the system:
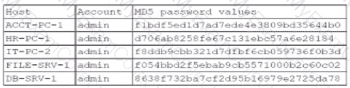
Which of the following in the security administrator most likely protecting against?
Which of the following should a security analyst consider when prioritizing remediation efforts against known vulnerabilities?
A security professional discovers a folder containing an employee ' s personal information on the enterprise ' s shared drive. Which of the following best describes the data type the securityprofessional should use to identify organizational policies and standards concerning the storage of employees ' personal information?
An organization designs an inbound firewall with a fail-open configuration while implementing a website. Which of the following does the organization consider to be the highest priority?
A security analyst receives an alert that an employee has clicked on a phishing email and exposed their credentials. Which of the following should the analyst do?
Which of the following can best protect against an employee inadvertently installing malware on a company system?
A site reliability engineer is designing a recovery strategy that requires quick failover to an identical site if the primary facility goes down. Which of the following types of sites should the engineer consider?
Which of the following security concepts is accomplished when granting access after an individual has logged into a computer network?
During a recent log review, an analyst discovers evidence of successful injection attacks. Which of the following will best address this issue?
A security analyst is reviewing the following logs about a suspicious activity alert for a user ' s VPN log-ins. Which of the following malicious activity indicators triggered the alert?
✅Log Summary:
User logs in fromChicago, ILmultiple times, then suddenly a successful login appears fromRome, Italy, followed again by Chicago logins — all within ashort time span.
Which of the following methods to secure data is most often used to protect data in transit?
Which of the following cryptographic methods is preferred for securing communications with limited computing resources?
A website user is locked out of an account after clicking an email link and visiting a different website Web server logs show the user ' s password was changed, even though the user did not change the password. Which of the following is the most likely cause?
A customer of a large company receives a phone call from someone claiming to work for the company and asking for the customer ' s credit card information. The customer sees the caller ID is the same as the company ' s main phone number. Which of the following attacks is the customer most likely a target of?
A security analyst reviews logs and finds a large number of malicious requests that have caused performance issues on the company ' s site. Which of the following would have most likely prevented this attack?
A business provides long-term cold storage services to banks that are required to follow regulator-imposed data retention guidelines. Banks that use these services require that data is disposed of in a specific manner at the conclusion of the regulatory threshold for data retention. Which of the following aspects of data management is the most important to the bank in the destruction of this data?
An organization plans to expand its operations internationally and needs to keep data at the new location secure. The organization wants to use the most secure architecture model possible. Which of the following models offers the highest level of security?
Which of the following alert types is the most likely to be ignored over time?
Which of the following best represents how frequently an incident is expected to happen each year?
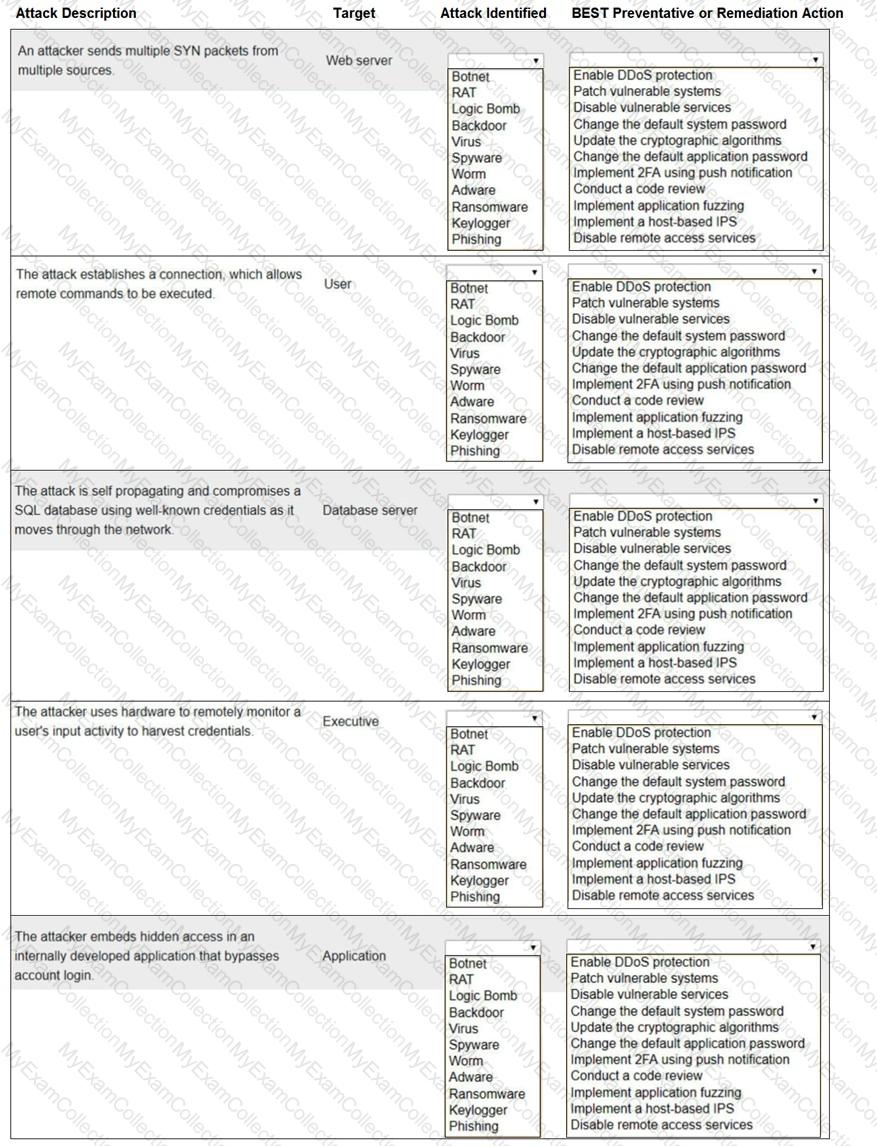
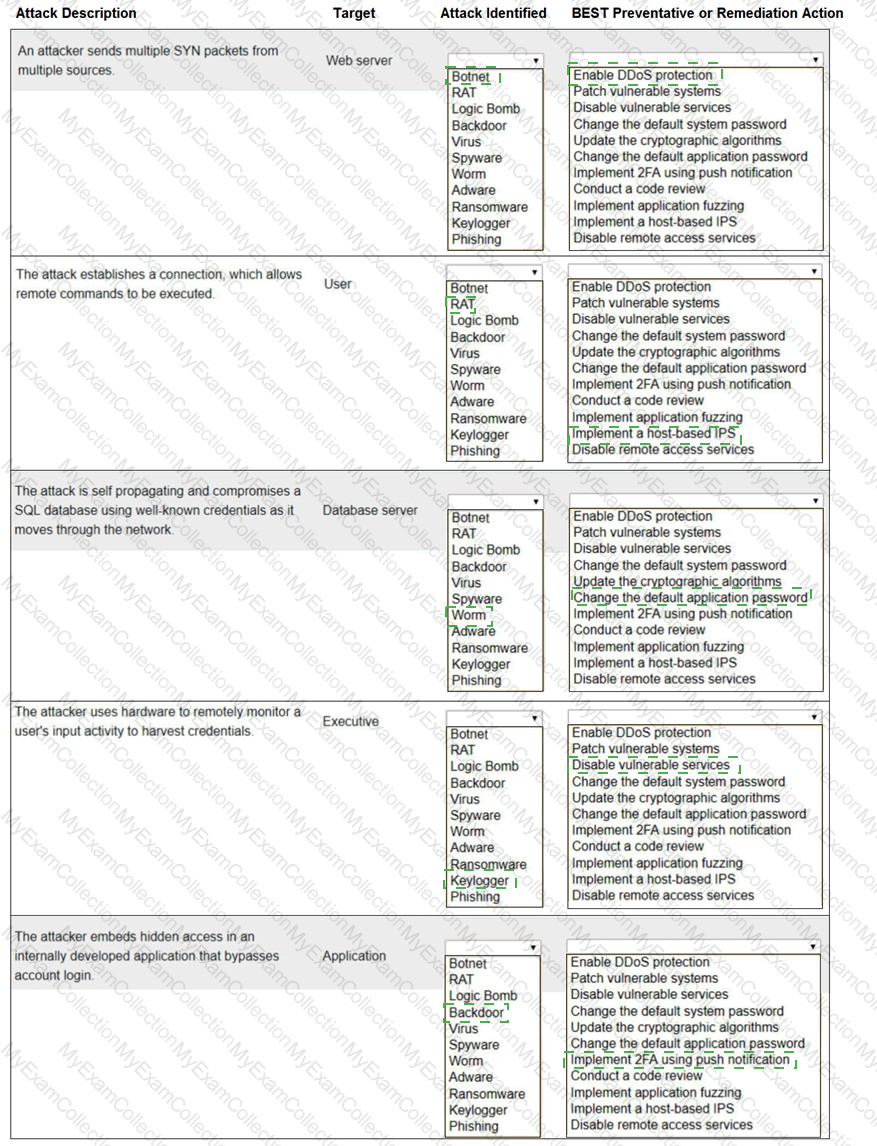
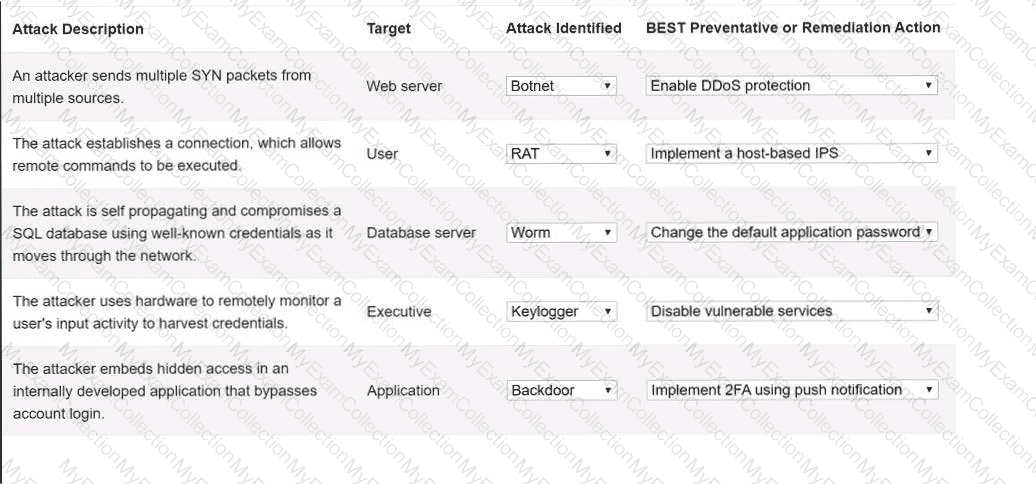
Select the appropriate attack and remediation from each drop-down list to label the corresponding attack with its remediation.
INSTRUCTIONS
Not all attacks and remediation actions will be used.
If at any time you would like to bring back the initial state of the simu-lation, please click the Reset All button.
A company wants to track modifications to the code that is used to build new virtual servers. Which of the following will the company most likely deploy?
A technician wants to improve the situational and environmental awareness of existing users as they transition from remote to in-office work. Which of the following is the best option?
Which of the following would be the best way to handle a critical business application that is running on a legacy server?
Which of the following is a common data removal option for companies that want to wipe sensitive data from hard drives in a repeatable manner but allow the hard drives to be reused?
A company is experiencing issues with employees leaving the company for a competitor and taking customer contact information with them. Which of the following tools will help prevent this from reoccurring?
A company receives an alert that a network device vendor, which is widely used in the enterprise, has been banned by the government.
Which of the following will the company ' s general counsel most likely be concerned with during a hardware refresh of these devices?
A systems administrate wants to implement a backup solution. the solution needs to allow recovery of the entire system, including the operating system, in case of a disaster. Which of the following backup types should the administrator consider?
Which of the following activities is included in the post-incident review phase?
A security report shows that during a two-week test period. 80% of employees unwittingly disclosed their SSO credentials when accessing an external website. The organization purposelycreated the website to simulate a cost-free password complexity test. Which of the following would best help reduce the number of visits to similar websites in the future?
During a penetration test in a hypervisor, the security engineer is able to use a script to inject a malicious payload and access the host filesystem. Which of the following best describes this vulnerability?
A recent penetration test identified that an attacker could flood the MAC address table of network switches. Which of the following would best mitigate this type of attack?
The Chief Information Security Officer of an organization needs to ensure recovery from ransomware would likely occur within the organization ' s agreed-upon RPOs end RTOs. Which of the following backup scenarios would best ensure recovery?
A security engineer needs to quickly identify a signature from a known malicious file. Which of the following analysis methods would the security engineer most likely use?
A security engineer receives reports of unauthorized devices on the organization ' s network. Which of the following best describes a secure and effective way to mitigate the risks?
A systems administrator is concerned users are accessing emails through a duplicate site that is not run by the company. Which of the following is used in this scenario?
A newly appointed board member with cybersecurity knowledge wants the board of directors to receive a quarterly report detailing the number of incidents that impacted the organization. The systems administrator is creating a way to present the data to the board of directors. Which of the following should the systems administrator use?
Which of the following describes the reason for using an MDM solution to prevent jailbreaking?
Which of the following is the most likely reason a security analyst would review SIEM logs?
Which of the following can be used to compromise a system that is running an RTOS?
A bank insists all of its vendors must prevent data loss on stolen laptops. Which of the following strategies is the bank requiring?
A security administrator is deploying a DLP solution to prevent the exfiltration of sensitive customer data. Which of the following should the administrator do first?
A security analyst sees an increase of vulnerabilities on workstations after a deployment of a company group policy. Which of the following vulnerability types will the analyst most likely find on the workstations?
A network manager wants to protect the company ' s VPN by implementing multifactor authentication that uses:
. Something you know
. Something you have
. Something you are
Which of the following would accomplish the manager ' s goal?
During a penetration test in a hypervisor, the security engineer is able to inject a malicious payload and access the host filesystem. Which of the following best describes this vulnerability?
A company wants to get alerts when others are researching and doing reconnaissance on the company One approach would be to host a part of the Infrastructure online with known vulnerabilities that would appear to be company assets. Which of the following describes this approach?
Security controls in a data center are being reviewed to ensure data is properly protected and that human life considerations are included. Which of the following best describes how the controls should be set up?
Which of the following solutions would most likely be used in the financial industry to mask sensitive data?
An administrator is reviewing a single server ' s security logs and discovers the following;
Which of the following best describes the action captured in this log file?
An employee receives a text message that appears to have been sent by the payroll department and is asking for credential verification. Which of the following social engineering techniques are being attempted? (Choose two.)
During an investigation, an incident response team attempts to understand the source of an incident. Which of the following incident response activities describes this process?
A company prepares for an upcoming regulatory audit. The company wants to perform a gap analysis in the most cost-effective way. Which of the following will help the company achieve this goal?
A vendor needs to remotely and securely transfer files from one server to another using the command line. Which of the following protocols should be Implemented to allow for this type of access? (Select two).
A company with a high-availability website is looking to harden its controls at any cost. The company wants to ensure that the site is secure by finding any possible issues. Which of the following would most likely achieve this goal?
Which of the following should be used to ensure that a device is inaccessible to a network-connected resource?
An employee asks a security analyst to scan a suspicious email that contains a link to a file on a file-sharing site. The analyst determines that the file is safe after downloading and scanning the file with antivirus software. When the employee opens the file, their device is infected with ransomware. Which of the following steps should the analyst have taken?
Which of the following security controls are a company implementing by deploying HIPS? (Select two).
Which of the following is the phase in the incident response process when a security analyst reviews roles and responsibilities?
Which of the following organizational documents is most often used to establish and communicate expectations associated with integrity and ethical behavior within an organization?
Which of the following describes the difference between encryption and hashing?
A security analyst estimates that a small security incident will cost $10,000 and will occur twice per year. The analyst recommends a budget of $20,000 for next year. Which of the following does the $10,000 represent?
Which of the following provides the details about the terms of a test with a third-party penetration tester?
Which of the following security threats aims to compromise a website that multiple employees frequently visit?
Which of the following would be the most appropriate way to protect data in transit?
A company installed cameras and added signs to alert visitors that they are being recorded. Which of the following controls did the company implement? (Select two).
A customer reports that software the customer downloaded from a public website has malware in it. However, the company that created the software denies any malware in its software at delivery time. Which of the following techniques will address this concern?
A company wants to reduce the time and expense associated with code deployment. Which of the following technologies should the company utilize?
Which of the following techniques would identify whether data has been modified in transit?
A security analyst investigates an incident in which a PowerShell script was identified as a potential IoC. Which of the following will best help the analyst identify an attempt to compromise the system?
In order to strengthen a password and prevent a hacker from cracking it, a random string of 36 characters was added to the password. Which of the following best describes this technique?
While reviewing a recent compromise, a forensics team discovers that there are hard-coded credentials in the database connection strings. Which of the following assessment types should be performed during software development to prevent this from reoccurring?
A company is developing a business continuity strategy and needs to determine how many staff members would be required to sustain the business in the case of a disruption. Which of the following best describes this step?
During a recent log review, an analyst found evidence of successful injection attacks. Which of the following will best address this issue?
A customer has a contract with a CSP and wants to identify which controls should be implemented in the IaaS enclave. Which of the following is most likely to contain this information?
To which of the following security categories does an EDR solution belong?
A security analyst is investigating a workstation that is suspected of outbound communication to a command-and-control server. During the investigation, the analyst discovered that logs on the endpoint were deleted. Which of the following logs would the analyst most likely look at next?
A penetration tester is testing the security of a building’s alarm system. Which type of penetration test is being conducted?
Which of the following most accurately describes the order in which a security engineer should implement secure baselines?
Which of the following agreements defines response time, escalation points, and performance metrics?
A security team is reviewing the findings in a report that was delivered after a third party performed a penetration test. One of the findings indicated that a web application form field is vulnerable to cross-site scripting. Which of the following application security techniques should the security analyst recommend the developer implement to prevent this vulnerability?
Which of the following must be considered when designing a high-availability network? (Select two).
Which of the following best describes the concept of information being stored outside of its country of origin while still being subject to the laws and requirements of the country of origin?
A systems administrator is auditing all company servers to ensure. They meet the minimum security baseline While auditing a Linux server, the systems administrator observes the /etc/shadow file has permissions beyond the baseline recommendation. Which of the following commands should the systems administrator use to resolve this issue?
Which of the following documents details how to accomplish a technical security task?
A security operations center determines that the malicious activity detected on a server is normal. Which of the following activities describes the act of ignoring detected activity in the future?
An organization recently started hosting a new service that customers access through a web portal. A security engineer needs to add to the existing security devices a new solution to protect this new service. Which of the following is the engineer most likely to deploy?
Which of the following can be used to identify potential attacker activities without affecting production servers?
A company wants to use new Wi-Fi-enabled environmental sensors to automatically collect metrics. Which of the following will the security team most likely do?
A company is expanding its threat surface program and allowing individuals to security test the company’s internet-facing application. The company will compensate researchers based on the vulnerabilities discovered. Which of the following best describes the program the company is setting up?
Which of the following can a security director use to prioritize vulnerability patching within a company ' s IT environment?
Which of the following makes Infrastructure as Code (IaC) a preferred security architecture over traditional infrastructure models?
A business is expanding to a new country and must protect customers from accidental disclosure of specific national identity information. Which of the following should the security engineer update to best meet business requirements?
Which of the following allows an exploit to go undetected by the operating system?
A few weeks after deploying additional email servers, employees complain that messages are being marked as spam. Which needs to be updated?
An organization wants to improve the company ' s security authentication method for remote employees. Given the following requirements:
• Must work across SaaS and internal network applications
• Must be device manufacturer agnostic
• Must have offline capabilities
Which of the following would be the most appropriate authentication method?
A business uses Wi-Fi with content filleting enabled. An employee noticed a coworker accessed a blocked sue from a work computer and repotted the issue. While Investigating the issue, a security administrator found another device providing internet access to certain employees. Which of the following best describes the security risk?
Which of the following is an example of implementing Zero Trust architecture?
A company is concerned about the theft of client data from decommissioned laptops. Which of the following is the most cost-effective method to decrease this risk?
A systems administrator wants to prevent users from being able to access data based on their responsibilities. The administrator also wants to apply the required access structure via a simplified format. Which of the following should the administrator apply to the site recovery resource group?
Which of the following would be most useful in determining whether the long-term cost to transfer a risk is less than the impact of the risk?
Which of the following is the most likely to be included as an element of communication in a security awareness program?
A security manager wants to reduce the number of steps required to identify and contain basic threats. Which of the following will help achieve this goal?
Which of the following security controls would best guard a payroll system against insider manipulation threats?
An administrator learns that users are receiving large quantities of unsolicited messages. The administrator checks the content filter and sees hundreds of messages sent to multiple users. Which of the following best describes this kind of attack?
Which of the following is a key reason to follow data retention policies during asset decommissioning?
Which of the following best describes why me SMS DIP authentication method is more risky to implement than the TOTP method?
An organization has too many variations of a single operating system and needs to standardize the arrangement prior to pushing the system image to users. Which of the following should the organization implement first?
While a user reviews their email, a host gets infected by malware from an external hard drive plugged into the host. The malware steals all the user ' s credentials stored in the browser. Which of the following training topics should the user review to prevent this situation from reoccurring?
A new employee logs in to the email system for the first time and notices a message from human resources about onboarding. The employee hovers over a few of the links within the email and discovers that the links do not correspond to links associated with the company. Which of the following attack vectors is most likely being used?
An organization ' s web servers host an online ordering system. The organization discovers that the servers are vulnerable to a malicious JavaScript injection, which could allow attackers to access customer payment information. Which of the following mitigation strategies would be most effective for preventing an attack on the organization ' s web servers? (Select two).
A company ' s accounting department receives an urgent payment message from the company ' s bank domain with instructions to wire transfer funds. The sender requests that the transfer be completed as soon as possible. Which of the following attacks is described?
Several employees received a fraudulent text message from someone claiming to be the Chief Executive Officer (CEO). The message stated:
“I’m in an airport right now with no access to email. I need you to buy gift cards for employee recognition awards. Please send the gift cards to following email address.â€
Which of the following are the best responses to this situation? (Choose two).
A security analyst determines that a security breach will have a financial impact of $15,000 and is expected to occur twice within a three-year period. Which of the following is the ALE for this risk?
An administrator assists the legal and compliance team with ensuring information about customer transactions is archived for the proper time period. Which of the following data policies is the administrator carrying out?
An organization experiences a compromise in a cloud-hosted solution that contains customer information. Which of the following strategies will help determine the sensitivity level of the breach?
Which of the following should be used to select a label for a file based on the file ' s value, sensitivity, or applicable regulations?
A company is currently utilizing usernames and passwords, and it wants to integrate an MFA method that is seamless, can Integrate easily into a user ' s workflow, and can utilize employee-owned devices. Which of the following will meet these requirements?
An MSSP manages firewalls for hundreds of clients. Which of the following tools would be most helpful to create a standard configuration template in order to improve the efficiency of firewall changes?
An administrator must implement a solution that provides security and network connectivity between two companies. Which of the following infrastructure solutions is the best for this purpose?
Visitors to a secured facility are required to check in with a photo ID and enter the facility through an access control vestibule Which of the following but describes this form of security control?
A security analyst is reviewing the following logs:
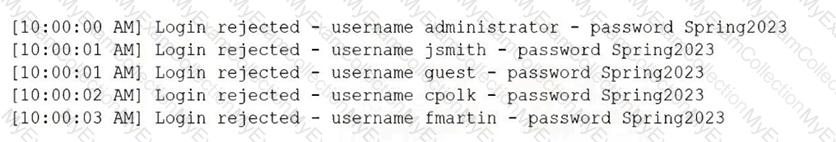
Which of the following attacks is most likely occurring?
A company is in the process of cutting jobs to manage costs. The Chief Information Security Officer is concerned about the increased risk of an insider threat. Which of the following would most likely help the security awareness team address this potential threat?
A healthcare organization wants to provide a web application that allows individuals to digitally report health emergencies.
Which of the following is the most important consideration during development?
A smart lighting system is deployed in an office building. The devices connect to the corporate Wi-Fi and are managed via a cloud portal. Which of the following security techniques reduces risk for these IoT devices?
After a company was compromised, customers initiated a lawsuit. The company ' s attorneys have requested that the security team initiate a legal hold in response to the lawsuit. Which of the following describes the action the security team will most likely be required to take?
Which of the following is used to protect a computer from viruses, malware, and Trojans being installed and moving laterally across the network?
A legal department must maintain a backup from all devices that have been shredded and recycled by a third party. Which of the following best describes this requirement?
Which of the following is a type of vulnerability that involves inserting scripts into web-based applications in order to take control of the client ' s web browser?
A company wants to verify that the software the company is deploying came from the vendor the company purchased the software from. Which of the following is the best way for the company to confirm this information?
A company has yearly engagements with a service provider. The general terms and conditions are the same for all engagements. The company wants to simplify the process and revisit the general terms every three years. Which of the following documents would provide the best way to set the general terms?
A company must ensure sensitive data at rest is rendered unreadable. Which of the following will the company most likely use?
In an effort to reduce costs, a company is implementing a strategy that gives employees access to internal company resources, including email, from personal devices. Which of the following strategies is the company implementing?
 A screenshot of a computer program Description automatically generated with low confidence
A screenshot of a computer program Description automatically generated with low confidence
