Which of the following statements about tags is true? (select all that apply.)
Which of the following is one of the pre-configured data models included in the Splunk Common Information Model (CIM) add-on?
Consider the following search:
index=web sourcetype=access_corabined
The log shows several events that share the same jsesszonid value (SD462K101O2F267). View the events as a group.
From the following list, which search groups events by jSSESSIONID?
Which of the following statements are true for this search? (Select all that apply.) SEARCH: sourcetype=access* |fields action productld status
What will you learn from the results of the following search?
sourcetype=cisco_esa | transaction mid, dcid, icid | timechart avg(duration)
Which of the following statements describes the command below (select all that apply)
Sourcetype=access_combined | transaction JSESSIONID
Which of the following statements is true about the root dataset of a data model?
Which of the following is true about a datamodel that has been accelerated?
When using the Field Extractor (FX), which of the following delimiters will work? (select all that apply)
Which of these stats commands will show the total bytes for each unique combination of page and server?
A user wants a table that will show the total revenue made for each product in each sales region. Which would be the correct SPL query to use?
Which of the following can be used with the eval command tostring function (select all that apply)
Which of the following search modes automatically returns all extracted fields in the fields sidebar?
What are the expected search results from executing the following SPL command?
index=network NOT StatusCode=200
Which of the following is the correct way to use the data model command to search field in the data model within the web dataset?
When used with the timechart command, which value of the limit argument returns all values?
Which of the following statements describes the use of the Field Extractor (FX)?
Select this in the fields sidebar to automatically pipe you search results to the rare command
Which syntax will find events where the values for the 1 field match the values for the Renewal-MonthYear field?
When should the regular expression mode of Field Extractor (FX) be used? (select all that apply)
Which of the following is true about the Splunk Common Information Model (CIM)?
Information needed to create a GET workflow action includes which of the following? (select all that apply.)
A POST workflow action will pass which types of arguments to an external website?
When would a user select delimited field extractions using the Field Extractor (FX)?
What does the fillnull command replace null values with, if the value argument is not specified?
Which delimiters can the Field Extractor (FX) detect? (select all that apply)
What other syntax will produce exactly the same results as | chart count over vendor_action by user?
This clause is used to group the output of a stats command by a specific name.
When you mouse over and click to add a search term this (thesE. Boolean operator(s) is(arE. not implied. (Select all that apply).
The Splunk Common Information Model (CIM) is a collection of what type of knowledge object?
which of the following commands are used when creating visualizations(select all that apply.)
There are several ways to access the field extractor. Which option automatically identifies data type, source type, and sample event?
A field alias is created where field1—fieid2 and the Overwrite Field Values checkbox is selected.
What happens if an event only contains values for fieid1?
If a calculated field has the same name as an extracted field, what happens to the extracted field?
Using the export function, you can export search results as __________.( Select all that apply)
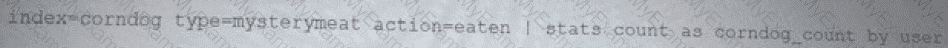
Which of the following describes this search?
New Search
'third_party_outages(EMEA,-24h)'
Which knowledge Object does the Splunk Common Information Model (CIM) use to normalize data. in addition to field aliases, event types, and tags?
When using the timechart command, how can a user group the events into buckets based on time?
Which of the following knowledge objects represents the output of an eval expression?
Which of the following file formats can be extracted using a delimiter field extraction?
Which of the following definitions describes a macro named “samplemacro†that accepts two arguments?
What does the fillnull command do in this search?
index=main sourcetype=http:log | fillnull value="Unknown"
Which of the following are valid options to speed up reports? (Select all the apply.)
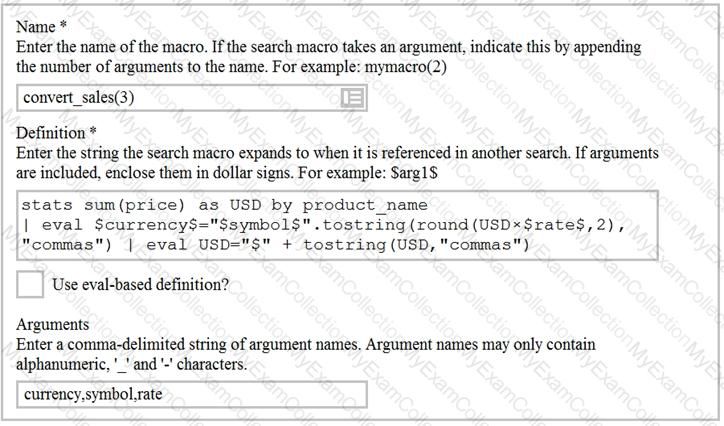
Based on the macro definition shown below, what is the correct way to execute the macro in a search string?
Data model fields can be added using the Auto-Extracted method. Which of the following statements describe Auto-Extracted fields? (select all that apply)
Which search string would only return results for an event type called success ful_purchases?
Data models are composed of one or more of which of the following datasets? (select all that apply)
What are the expected results for a search that contains the command | where A=B?
Which function should you use with the transaction command to set the maximum total time between the earliest and latest events returned?
__________ datasets can be added to root dataset to narrow down the search
The timechart command is an example of which of the following command types?