What is the primary function of the People Page in the Threat Protection Workbench and TAP Dashboard?
To manage user permissions and access controls.
To configure email filtering rules for specific users.
To track user engagement with phishing simulations.
To help identify and prioritize users affected by threats.
Answer:
Explanation:
The People Page is a user-centric investigation view designed to help analysts quickly identify who is being targeted and who is most at risk/impacted by threats (D). Instead of starting from a single message, responders can pivot from user risk signals—Attack Index, exposure metrics, click behavior, VIP status, and repeated campaign targeting—to build a prioritized queue for investigation. In Proofpoint IR operations, this supports rapid triage during active phishing/BEC waves: analysts identify the highest-risk users first (those with permitted clicks or delivered accessible threats), then perform immediate follow-up actions such as credential resets, session/token revocation, mailbox rule review, and targeted comms. The People Page is not an access control manager and it is not the place to configure granular filtering rules per user (that’s policy/admin territory). It’s also distinct from security awareness simulation dashboards, though it can inform who should receive training based on risky behavior. As part of detection and analysis, the People Page helps convert large-scale threat telemetry into actionable, person-focused response steps, minimizing dwell time and reducing the chance that the most exposed users are missed.
For which two reasons should organizations customize their incident response plans based on NIST SP 800-61 or another incident response standard? (Select two.)
To make it more generic so that it can be used to respond to incidents from new attack vectors.
To document the contact information for each of the security analysts at your managed security services provider.
To change the order of operations in the Incident Response Lifecycle processes to match ISO 12035.
To meet unique requirements relating to the organization’s mission, size, structure, and functions.
To improve incident response effectiveness and efficiency by creating a repeatable process and documented handoffs.
Answer:
Explanation:
Standards like NIST SP 800-61 provide a proven framework, but incident response must be operationalized to the organization’s reality. Customization is required to match mission, size, structure, and functions (D)—for example, whether the organization is regulated (financial/health), globally distributed, heavily supplier-dependent, or cloud-first. These factors determine evidence retention, legal notification triggers, escalation thresholds, and which teams own containment steps (email admin vs SOC vs IAM). Customization also improves effectiveness/efficiency by creating a repeatable process and documented handoffs (E): who triages TAP alerts, who executes TRAP pulls, who updates URL Defense blocklists, who performs account resets/token revocation, and how comms are handled with executives and end users. In Proofpoint-driven IR, handoffs are particularly important because email incidents often cross functional boundaries (SOC ↔ messaging team ↔ IAM ↔ helpdesk ↔ legal). Making plans “more generic†(A) is counterproductive; standards are already generic. Documenting every MSSP analyst contact (B) is fragile; role-based contacts are better, but that’s not the key reason for customizing a standard. Changing lifecycle order (C) is not the objective; improving fit and execution is.
Which two items should be included in an incident report to be discussed during a post-incident debrief? (Select two.)
Software inventory
Speculation about adversary attribution
Product manuals
Incident timeline
Devices and systems involved
Answer:
Explanation:
Post-incident debriefs require evidence-backed documentation that enables learning and control improvements. The two most essential items are the incident timeline (D) and the devices/systems involved (E). The timeline reconstructs key events (first delivery, first click, first alert, containment actions, TRAP pulls, credential resets, policy changes) and supports measurable IR metrics (MTTD, MTTR). The “devices and systems involved†section defines scope and blast radius: which mailboxes were targeted, which users were impacted, what email systems were involved (gateway, cloud mail, endpoints), and which Proofpoint components contributed (TAP verdicts, URL Defense click logs, Smart Search traces, TRAP remediation). This information is the foundation for root cause analysis and for validating that remediation fully covered the environment (no missed recipients, no unremediated copies, no lingering compromised accounts). Software inventories and product manuals are generally not debrief deliverables, and adversary attribution speculation is discouraged unless it is evidence-based and necessary for risk decisions. Proofpoint IR best practice is factual, actionable reporting that directly drives preventive control changes.
Exhibit:

What can be determined by the threat information shown in the exhibit?
Five messages containing this threat were pulled from mailboxes after delivery.
The URLs related to the threat were rewritten after the threat was discovered.
More than 150 messages containing this threat were unclicked or were deleted.
The VIP user clicked on the non-rewritten URL in the threat message.
Answer:
Explanation:
The exhibit’s threat detail indicates that a VIP user clicked and that the click occurred on a non-rewritten URL (D). This determination is significant in Proofpoint IR because non-rewritten clicks can bypass URL Defense’s time-of-click protections and logging, reducing both prevention and visibility. It often happens when a user accesses the link outside the protected path (e.g., copying/pasting the URL into a browser, using a client/app that didn’t preserve rewriting, or receiving the URL through a channel where rewriting wasn’t applied). For responders, this elevates urgency: the VIP user should be prioritized for compromise assessment (credential reset, token/session revocation, MFA verification, mailbox rule/forwarding review, suspicious login checks) because the protective block page may not have been enforced. It also drives containment improvements: ensure URL Defense rewriting is applied broadly (body links), verify supported clients and configurations, and consider additional controls such as isolation or stricter policies for VIP cohorts. The other options (A–C) require explicit remediation or message-count indicators that are not definitively implied by the “VIP clicked non-rewritten URL†exhibit signal.
Exhibit:

Which column indicates the number of users targeted by a malicious campaign or threat?
Highlighted
Intended
At Risk
Impacted
Answer:
Explanation:
In TAP threat and campaign views, the columns typically reflect a funnel of exposure and interaction. “Intended†(B) represents the number of targeted recipients—i.e., how many users the attacker attempted to reach (often including messages that were blocked or not ultimately delivered). “At Risk†usually reflects users who actually received the message (delivered) and were therefore exposed, while “Impacted†reflects users who interacted with the threat (clicks, credential entry, or other measurable engagement depending on the threat type and telemetry). “Highlighted†is a classification/flagging mechanism (not a population count of targets). For IR detection and analysis, “Intended†is crucial for estimating the campaign’s scope and potential blast radius at the earliest stage—before you know how many were delivered or clicked. Analysts use Intended to decide whether to escalate, whether to run broad retroactive searches, and whether to apply preventative blocks (domains/URLs) quickly. Then they pivot to At Risk and Impacted to prioritize immediate containment actions for exposed and interacting users.
Based on the exhibit,
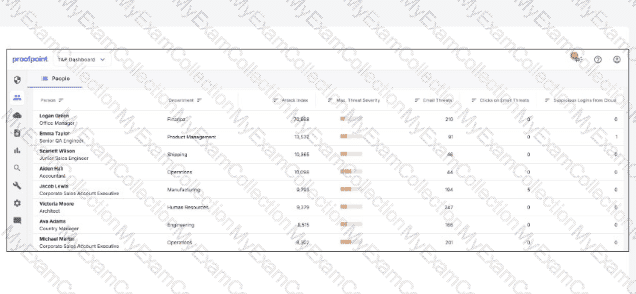
which user would most benefit from attending security awareness training based on their behavior?
Logan Green
Scarlett Wilson
Emma Taylor
Jacob Lewis
Answer:
Explanation:
In Proofpoint user-risk views (People page / user lists), “behavior†signals that drive training prioritization typically include measurable interaction with threats—especially clicks on email threats and repeated exposure patterns. The exhibit indicates that Jacob Lewis stands out behaviorally (e.g., elevated “Clicks on Email Threats†relative to peers and/or meaningful exposure indicators), making them the best candidate for targeted awareness intervention. From an IR preparation standpoint, training is most effective when it is risk-based and individualized: users who click are statistically more likely to become the initial foothold for credential theft and account takeover. Proofpoint programs commonly combine technical controls (URL Defense blocking, attachment detonation, post-delivery quarantine) with human controls (just-in-time coaching, targeted modules, reinforcement after real-world reports). Assigning training to high-click users reduces future incident volume by cutting successful phishing rates, improving reporting via “Report Suspicious,†and increasing early detection. Operationally, analysts also pair training with compensating controls for repeat clickers (stricter URL access policy, heightened monitoring, enforced MFA, mailbox rule audits) to reduce risk while behavior improves.
An analyst has been tasked with providing a report that can be used to prioritise investigations based on a user's Attack Index score. Which report would be most suitable for this purpose?
VIP Activity
Top 10 Recipients
Very Attacked People
Top 10 Clickers
Answer:
Explanation:
Attack Index is a user-level risk/burden metric intended to help SOC teams prioritize which people to investigate first based on the amount and severity/diversity of threat activity directed at them (and often their exposure/interaction, depending on module). The report that directly supports that workflow is “Very Attacked People,†which is designed to surface users with the highest Attack Index and concentration of targeted threats. Operationally, this aligns with IR queue management: instead of treating all alerts equally, analysts use user-centric risk ranking to focus on likely compromise candidates (e.g., frequent recipients of credential phishing, repeated exposure to the same campaign, or elevated threat severity). “Top 10 Recipients†is volume-oriented and may include benign bulk mail; “Top 10 Clickers†is behavior-oriented but does not necessarily reflect overall threat burden; and “VIP Activity†is scoped to a subset (VIPs) rather than the complete organization’s risk ranking. In Proofpoint-led IR best practice, this report is commonly used to drive daily standups, assign investigations, and justify proactive account checks (MFA posture, suspicious logins, mailbox rules) for the highest-risk users.
An analyst is reviewing the Threats page in the TAP Dashboard.
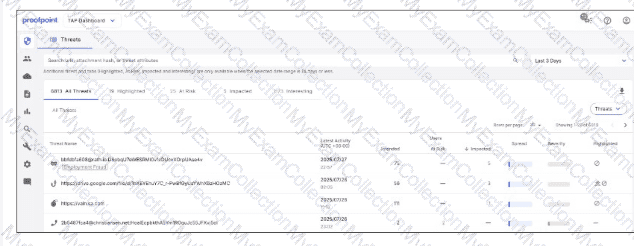
Which of the top four threats seen in the exhibit should be prioritised for investigation?
The Malware Delivery threat
The TOAD (Telephone-Oriented Attack Delivery) threat
The Credential Phishing threat
The BEC (Business Email Compromise) threat
Answer:
Explanation:
In Proofpoint-driven triage, threats are prioritized by likelihood of immediate compromise and blast radius. Credential phishing typically ranks highest because a single successful credential submission can lead to account takeover (ATO), which then enables follow-on attacks: internal phishing, mailbox rule abuse, OAuth consent abuse, wire-fraud/BEC escalation, and data access. Proofpoint TAP surfaces credential phishing with strong indicators (URL defense verdicts, rewritten URL clicks, campaign clustering, and known phishing kits/landing pages), making it actionable for containment. Compared to malware delivery, credential theft often bypasses endpoint controls and produces fewer immediate artifacts, so rapid response is critical: password reset, token revocation, MFA enforcement, and mailbox audit. TOAD and BEC can be high impact, but in many environments they require human interaction outside email controls (phone/social steps) and may not always show definitive technical IOCs early. The TAP “Threats†view is designed for quick pivoting (Intended/At Risk/Impacted) and credential phishing typically correlates strongly with “Impacted†activity (clicks/submissions), which is why it should be investigated first when competing items are present.
Exhibit:
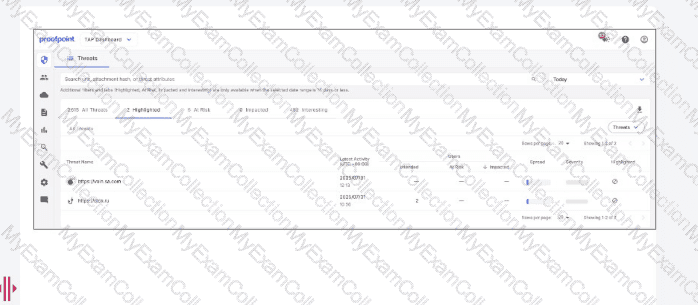
What is indicated by the icon shown in the “Highlighted†column?
The threat has been added to a custom blocklist.
The threat has been reported as a false negative.
The threat has been reported as a false positive.
The threat has been cleared and considered safe.
Answer:
Explanation:
In the TAP Dashboard, the “Highlighted†column is used to surface items that require analyst attention beyond basic volume metrics, including items that have been explicitly flagged for investigation outcomes. The icon shown corresponds to a false positive report (C), meaning the message or threat classification is being contested as benign but incorrectly condemned or prioritized as malicious. In Proofpoint workflows, this matters because false positives can disrupt business operations (legitimate suppliers, customer mail, internal systems) and can also hide real threats if analysts become desensitized to noisy alerting. Handling a highlighted false positive typically involves validating message authentication (SPF/DKIM/DMARC), reviewing TAP verdict drivers (URL/attachment detonation, reputation, MLX scoring where applicable), and confirming business legitimacy (known sender relationship, expected content, and user confirmation). When confirmed, analysts submit false positive feedback through the correct channel to improve future detection fidelity and reduce repeat quarantines. Operationally, false positive handling is part of detection hygiene: it improves signal quality, reduces alert fatigue, and ensures that high-confidence threats rise to the top of the triage queue.
Which two tasks are considered frequent and high-priority when actively reviewing the threat landscape? (Select two.)
Updating user training materials for quarterly phishing simulations.
Scheduling annual penetration tests for system validation.
Monitoring current threats and vulnerabilities affecting systems.
Archiving historical incident reports for long-term compliance.
Reviewing monitoring data to inform risk-based decisions.
Answer:
Explanation:
Active threat landscape review is an operational detection-and-analysis function: it focuses on what is happening now, what is likely to impact the environment, and what telemetry indicates elevated risk. Monitoring current threats and vulnerabilities (C) keeps analysts aligned to emergent campaigns (new phishing kits, BEC lures, malware droppers, supplier compromise patterns) and to exposure shifts (fresh CVEs that enable email-to-endpoint execution chains, new MFA-bypass trends, OAuth consent abuse). Reviewing monitoring data for risk-based decisions (E) is the day-to-day SOC activity that converts signals into priorities: TAP Threats/People views (Intended/At Risk/Impacted, clicks, severity), message traces (Smart Search), and threat response outcomes (quarantines/pulls). These two tasks directly reduce time-to-detect and time-to-contain by ensuring analysts focus on threats with user interaction, VIP targeting, and campaign spread. The other options are valuable but not “frequent and high-priority†in active landscape review: training content updates are periodic program work, pen tests are annual/episodic, and archiving is compliance-driven rather than real-time threat prioritization.
What is the purpose of Smart Search?
Trace and analyze information about files downloaded from a user's computer.
Trace and analyze information about messages processed by the Proofpoint Protection Server.
Trace and analyze information about user clicks on external websites.
Trace and analyze information about firewall breaches.
Answer:
Explanation:
Smart Search is a message-tracing and investigation feature used to query and analyze email messages processed by Proofpoint’s email security pipeline (B). In Proofpoint-focused IR, it functions as a primary evidence source for determining whether a message was accepted, rejected, quarantined, rewritten (URL Defense), modified (banners), or delivered, and which policy/rule triggered the decision. Analysts use Smart Search to pivot on sender/recipient, subject, message IDs, attachment names/hashes, URLs, sending IPs, and disposition outcomes—supporting rapid scoping (who got it, how many, what happened) and timeline creation. This is essential for detection and analysis because it links threat intelligence (from TAP verdicts) to operational mail flow facts (gateway decisions). It is not a host forensics tool (files downloaded), a web click-tracing platform (though TAP provides click telemetry), or a network firewall analysis console. In practice, Smart Search accelerates false positive validation, identifies false negatives (delivered when it should have been blocked), and provides the authoritative audit trail needed for containment actions and post-incident reporting.
What type of threat does the Cloud Security Report help identify in connected environments?
Ransomware
Account Takeover
Malicious Insider
Business Email Compromise
Answer:
Explanation:
The Cloud Security Report is designed to highlight risks and suspicious activity across connected cloud environments, with a strong focus on indicators consistent with account takeover (ATO) (B). In Proofpoint cloud-connected contexts (e.g., cloud email and SaaS integrations), ATO manifests through patterns such as unusual sign-in behavior, suspicious mailbox activity, anomalous sending, unexpected forwarding rules, OAuth application consents, and risky access from new locations/devices. For IR, this is critical because modern phishing frequently targets credentials and sessions rather than delivering executable malware, and compromised cloud identities enable fast lateral movement through internal phishing, invoice fraud, and data access. Proofpoint reporting helps analysts identify which users and accounts show the strongest compromise signals so they can prioritize containment: force password reset, revoke refresh tokens/sessions, remove malicious inbox rules and forwarding, disable suspicious OAuth grants, and validate MFA posture. While ransomware, insider risk, and BEC can be related outcomes, the Cloud Security Report’s connected-environment emphasis is on identity compromise signals and cloud account misuse—core ATO detection and investigation drivers.

