Which serverless cloud provider is covered by the "overly permissive service access" compliance check?
Which three OWASP protections are part of Prisma Cloud Web-Application and API Security (WAAS) rule? (Choose three.)
A customer is reviewing Container audits, and an audit has identified a cryptominer attack. Which three options could have generated this audit? (Choose three.)
An administrator for Prisma Cloud needs to obtain a graphical view to monitor all connections, including connections across hosts and connections to any configured network objects.
Which setting does the administrator enable or configure to accomplish this task?
When would a policy apply if the policy is set under Defend > Vulnerability > Images > Deployed?
Which statement is true about obtaining Console images for Prisma Cloud Compute Edition?
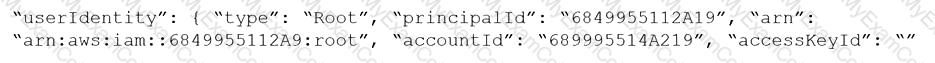
Given the following RQL:
Which audit event snippet is identified by the RQL?
A)
B)
C)
D)
Which IAM RQL query would correctly generate an output to view users who enabled console access with both access keys and passwords?
Which three options are selectable in a CI policy for image scanning with Jenkins or twistcli? (Choose three.)
Which two services require external notifications to be enabled for policy violations in the Prisma Cloud environment? (Choose two.)
What is the behavior of Defenders when the Console is unreachable during upgrades?
Which IAM Azure RQL query would correctly generate an output to view users who have sufficient permissions to create security groups within Azure AD and create applications?
What should be used to associate Prisma Cloud policies with compliance frameworks?
Which two CI/CD plugins are supported by Prisma Cloud as part of its Code Security? (Choose two.)
A customer has a requirement to terminate any Container from image topSecret:latest when a process named ransomWare is executed.
How should the administrator configure Prisma Cloud Compute to satisfy this requirement?
An administrator has deployed Console into a Kubernetes cluster running in AWS. The administrator also has configured a load balancer in TCP passthrough mode to listen on the same ports as the default Prisma Compute Console configuration.
In the build pipeline, the administrator wants twistcli to talk to Console over HTTPS. Which port will twistcli need to use to access the Prisma Compute APIs?
Given the following information, which twistcli command should be run if an administrator were to exec into a running container and scan it from within using an access token for authentication?
• Console is located at https://prisma-console.mydomain.local
• Token is: TOKEN_VALUE
• Report ID is: REPORTJD
• Container image running is: myimage:latest
One of the resources on the network has triggered an alert for a Default Config policy.
Given the following resource JSON snippet:
Which RQL detected the vulnerability?
A)
B)
C)
D)
A customer has a large environment that needs to upgrade Console without upgrading all Defenders at one time.
What are two prerequisites prior to performing a rolling upgrade of Defenders? (Choose two.)
Which two integrated development environment (IDE) plugins are supported by Prisma Cloud as part of its Code Security? (Choose two.)
An administrator sees that a runtime audit has been generated for a host. The audit message is:
“Service postfix attempted to obtain capability SHELL by executing /bin/sh /usr/libexec/postfix/postfix- script.stop. Low severity audit, event is automatically added to the runtime modelâ€
Which runtime host policy rule is the root cause for this runtime audit?
A customer wants to be notified about port scanning network activities in their environment. Which policy type detects this behavior?
A security team notices a number of anomalies under Monitor > Events. The incident response team works with the developers to determine that these anomalies are false positives.
What will be the effect if the security team chooses to Relearn on this image?
What is the purpose of Incident Explorer in Prisma Cloud Compute under the "Monitor" section?
Which two elements are included in the audit trail section of the asset detail view? (Choose two).
Which two bot categories belong to unknown bots under Web-Application and API Security (WAAS) bot protection? (Choose two.)
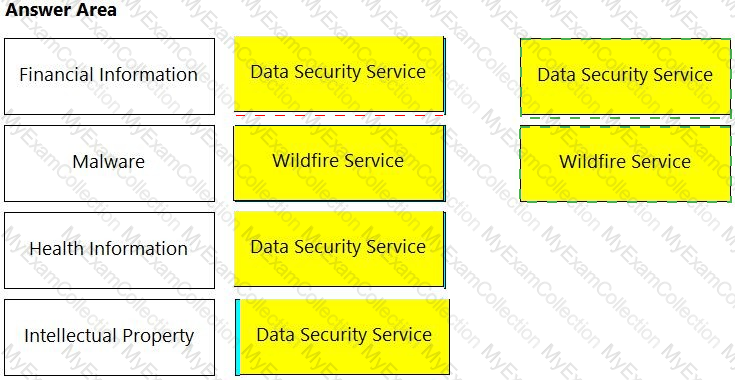
Match the service on the right that evaluates each exposure type on the left.
(Select your answer from the pull-down list. Answers may be used more than once or not at all.)
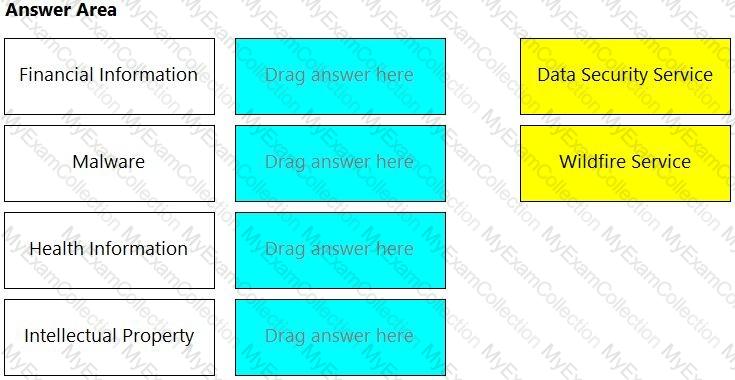
Which two information types cannot be seen in the data security dashboard? (Choose two).
The security auditors need to ensure that given compliance checks are being run on the host. Which option is a valid host compliance policy?
In WAAS Access control file upload controls, which three file types are supported out of the box? (Choose three.)
Which two required request headers interface with Prisma Cloud API? (Choose two.)
A container and image compliance rule has been configured by enabling all checks; however, upon review, the container's compliance view reveals only the entries in the image below.
What is the appropriate action to take next?
A customer has a requirement to automatically protect all Lambda functions with runtime protection. What is the process to automatically protect all the Lambda functions?
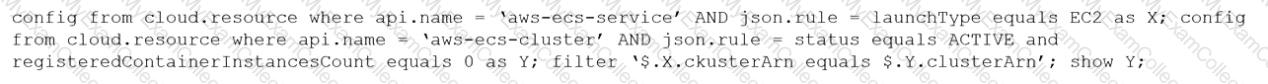
An S3 bucket within AWS has generated an alert by violating the Prisma Cloud Default policy “AWS S3 buckets are accessible to publicâ€. The policy definition follows:
config where cloud.type = 'aws' AND api.name='aws-s3api-get-bucket-acl' AND json.rule="((((acl.grants[? (@.grantee=='AllUsers')] size > 0) or policyStatus.isPublic is true) and publicAccessBlockConfiguration does not exist) or ((acl.grants[?(@.grantee=='AllUsers')] size > 0) and publicAccessBlockConfiguration.ignorePublicAcis is false) or (policyStatus.isPublic is true and publicAccessBlockConfiguration.restrictPublicBuckets is false)) and websiteConfiguration does not exist"
Why did this alert get generated?
Which two of the following are required to be entered on the IdP side when setting up SSO in Prisma Cloud? (Choose two.)
A customer has multiple violations in the environment including:
User namespace is enabled
An LDAP server is enabled
SSH root is enabled
Which section of Console should the administrator use to review these findings?
A Prisma Cloud Administrator needs to enable a Registry Scanning for a registry that stores Windows images. Which of the following statement is correct regarding this process?
Which resource and policy type are used to calculate AWS Net Effective Permissions? (Choose two.)
Which “kind†of Kubernetes object is configured to ensure that Defender is acting as the admission controller?
Which command should be used in the Prisma Cloud twistcli tool to scan the nginx:latest image for vulnerabilities and compliance issues?
A)
B)
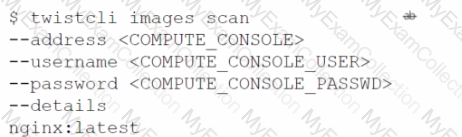
C)
D)
What are the two ways to scope a CI policy for image scanning? (Choose two.)
Which report includes an executive summary and a list of policy violations, including a page with details for each policy?
What is the function of the external ID when onboarding a new Amazon Web Services (AWS) account in Prisma Cloud?
Which two statements explain differences between build and run config policies? (Choose two.)
The compliance team needs to associate Prisma Cloud policies with compliance frameworks. Which option should the team select to perform this task?
Web-Application and API Security (WAAS) provides protection for which two protocols? (Choose two.)
In Prisma Cloud for Azure Net Effective Permissions Calculation, the following Azure permission levels are supported by which three permissions? (Choose three).
A customer has a development environment with 50 connected Defenders. A maintenance window is set for Monday to upgrade 30 stand-alone Defenders in the development environment, but there is no maintenance window available until Sunday to upgrade the remaining 20 stand-alone Defenders.
Which recommended action manages this situation?
In which Console menu would an administrator verify whether a custom compliance check is failing or passing?
Which two IDE plugins are supported by Prisma Cloud as part of its DevOps Security? (Choose two.)
During an initial deployment of Prisma Cloud Compute, the customer sees vulnerabilities in their environment.
Which statement correctly describes the default vulnerability policy?
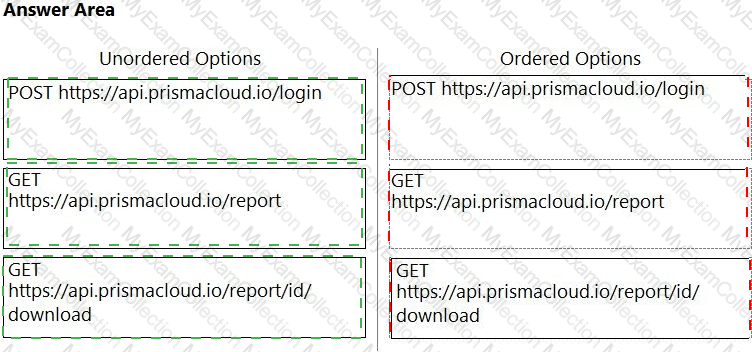
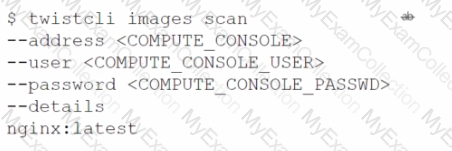
An administrator has been tasked with creating a custom service that will download any existing compliance report from a Prisma Cloud Enterprise tenant.
In which order will the APIs be executed for this service?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
The Unusual protocol activity (Internal) network anomaly is generating too many alerts. An administrator has been asked to tune it to the option that will generate the least number of events without disabling it entirely.
Which strategy should the administrator use to achieve this goal?
In Azure, what permissions need to be added to Management Groups to allow Prisma Cloud to calculate net effective permissions?
An administrator has a requirement to ingest all Console and Defender logs to Splunk.
Which option will satisfy this requirement in Prisma Cloud Compute?
How does assigning an account group to an administrative user on Prisma Cloud help restrict access to resources?
A security team has a requirement to ensure the environment is scanned for vulnerabilities. What are three options for configuring vulnerability policies? (Choose three.)
Which two fields are required to configure SSO in Prisma Cloud? (Choose two.)