Which policy mode blocks all traffic that is not explicitly allowed by the policy?
Exhibit:
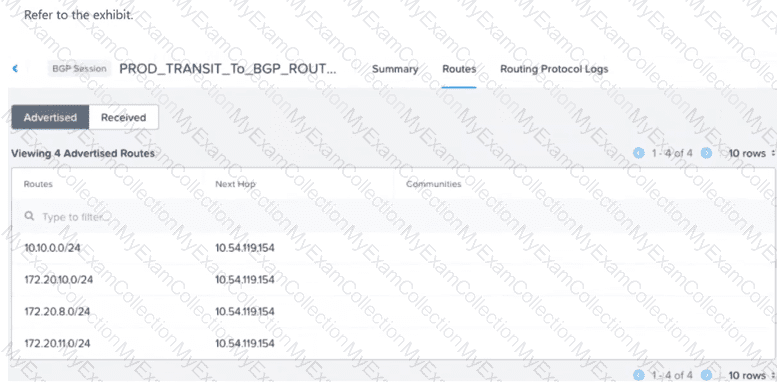
A VM with IP address 172.20.9.5 resides on a subnet with CIDR 172.20.9.0/24. The VPC is successfully peered via BGP with an external router... External networks outside the VPC are unable to reach the VM. What configuration change should be made to enable reachability for the VM?
An administrator is deploying a multi-tier application on a Nutanix AHV cluster. The Web tier needs to be accessible from the internet, the App tier must communicate only with the Web tier and the Database tier, and the Database tier should accept traffic only from the App tier. The administrator must determine the correct configuration to ensure secure, reliable connectivity for the Web tier while maintaining isolation from the Internet for the App and Database tiers. Which connectivity option should the administrator implement to meet the requirements?
Refer to Exhibit:
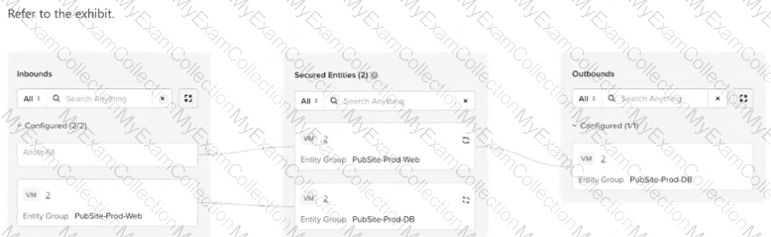
An administrator is tasked with configuring an application policy for a two-tier public website with Web and DB components. The database servers need to communicate with each other for replication, but the web servers should not be able to communicate with each other. The administrator configures the policy... and sets it to Enforce mode. Later testing reveals that the web servers are able to communicate with each other. What should the administrator do to resolve this?
An administrator has created a VPC with the following subnets: 10.1.1.0/24 10.1.2.0/24 10.1.3.0/24 What action must be taken for these networks to be externally routable?
A new multi-tier application is being deployed across several subnets in a Nutanix environment. The security team wants to create a Flow Network Security Policy to restrict traffic between the tiers, but the complete matrix of required network ports and protocols is not fully documented. Which strategy should the team employ first to accurately capture the necessary communication patterns without risking application outage?
Which two options are supported as a Secured Entity in Flow Network Security Application Policies? (Choose two.)
An administrator is deploying a multi-tier (web, app, database) application on a Nutanix cluster using AHV. The administrator needs to allow internal communication between tiers and provide external access to the web tier. How should the administrator satisfy this requirement?
A junior network operator is assigned two predefined roles in Prism Central... Role A: Prism Viewer Role B: VPC Admin The operator reports being able to successfully create, update, and delete Virtual Private Clouds (VPCs). However, the operator is unable to create a VM into the VPC. How does Prism Central determine the operator's effective permissions?
An administrator has been tasked with upgrading the Nutanix cluster to a newer version of AOS. The cluster is running a mix of different versions across nodes... What is the recommended first step when upgrading a Nutanix cluster with different AOS versions across nodes?
An administrator needs to configure a security policy that controls VM-to-VM communication within a category defined as secured entity. Which configuration action should the administrator take to restrict all intra-tier communication between the VMs within a category defined as secured entity?
An administrator manages a four-node cluster Each node has a 4 available 10GB uplinks, and all four are configured as an Active/Active bundle. They want to use Flow Virtual Networking to provide networking to the VMs in the cluster with the following requirements: VMs should be in a single VPC. VMs should be reachable by their real IP addresses. The VPC should have access to the most north/south bandwidth possible. No changes can be made to the physical infrastructure. How can this best be achieved?
What type of policy would be used to block all traffic between VMs in the category Environment:Sandbox and VMs in the category Environment:Production?
An administrator configures a VPN gateway with eBGP for dynamic route exchange. After setup, routes are not advertised to the remote peer. Which configuration is most likely missing?
An administrator has configured a VPC with multiple overlay subnets and attached a VPN gateway using IPSec. After enabling Jumbo Frames on the physical network, VMs are still experiencing packet drops. What is the most likely reason?
An administrator has deployed a microsegmentation policy in Nutanix Flow that allows certain VM traffic based on Active Directory (AD) user group membership. Users in a specific AD group report they are unable to access the VMs, while other users can connect without issues. The administrator suspects the problem is related to identity-based policy mapping. What should the administrator do to troubleshoot and resolve the access issue related to the identity-based policy?
An administrator plans to upgrade a Nutanix cluster running AHV and Prism Central. The current cluster is on AOS 6.10, and the administrator wants to move to AOS 7.3 while ensuring all components remain compatible. What is the correct upgrade order to minimize downtime and maintain cluster functionality?
An administrator creates a VPC named AppVPC1 in Nutanix Cloud Infrastructure (NCI) with separate subnets for the web, app, and database tiers. The database subnet must remain isolated from external networks; however, all tiers need to communicate with each other internally. What should the administrator configure to limit external access to only the web and app subnets?
An administrator is setting up a transit VPC to connect two VPCs and enable both internal (on-prem) and Internet connectivity. Which is the best configuration to meet the requirement?
A VPC admin creates a policy to allow traffic between two IP subnets but forgets to enable reverse direction. What happens in this scenario?
An administrator wants to configure the subnet 10.1.1.0/24 to stretch across two VPCs over a Network Gateway in VXLAN mode. The VMs on this subnet need to communicate with a traffic pattern of size 2000 Bytes. What is the minimum MTU required in the underlay network to ensure communication happens without fragmentation or traffic drops?
An administrator is responsible for managing user access to a Nutanix cluster... configure custom user roles... What is the first step in configuring and managing user roles for a Nutanix cluster?
An administrator finds that App tier VMs cannot connect to the Database tier on port 3306, and Flow logs show the traffic is being denied by a security policy. The Web tier communicates normally. What should the administrator do to allow the App tier to access the Database tier?
What is the first step in preparing a Nutanix cluster for Flow Virtual Networking?
An administrator needs to make a web server VM, which is inside a private VPC overlay subnet, accessible from the external network. The administrator assigns a Floating IP to the VM, but the service is still unreachable from the outside. What is a likely reason for this failure?
An administrator has a requirement to capture application flow data for a policy in Monitor mode and export those events to an external SIEM for correlation with other logs. Which two actions are required to achieve this? (Choose two.)

