During an LCM upgrade, the pre-check test_ahv_entering_mm_pinned_vms pre-check fails on an AHV host. The administrator reviews the listed VMs and finds that:
One VM is configured as an Agent VM
Two VMs are running Windows Defender Credential Guard
One VM has a vGPU-enabled
Based on the behavior of this pre-check, which action is required to allow the host to enter maintenance mode and proceed with the LCM upgrade?
An administrator has noticed that a cluster consists of four Full-NVMe nodes. Which expansion path is supported?
An administrator is tasked with using Nutanix Move to migrate a VM from Hyper-V to Nutanix AHV. What must be deployed on the Hyper-V host to facilitate migration?
An administrator wants to run a workload at site A, but replicate it to two clusters with different RPOs. Which replication option fits the needs?
An administrator attempts to provision a VM using remote storage, but the target container does not appear in the dropdown list. What is the most likely explanation?
A Windows VM will be cloned repeatedly and each clone needs OS-level customization during deployment.
What is the most efficient method to accomplish this task?
The administrator observed the following NCC check in a cluster running VDI workloads:
ec_enablement_check:
Node XX.XX.XX.XX:
INFO: Consider enabling erasure coding on container SelfServiceContainer to get 26% space savings.
INFO: Consider enabling erasure coding on container default-container203943 to get 22% space savings.
What is the best course of action?
An administrator has been asked to deploy a single-node Prism Central VM, with the possibility to scale out to increase its capacity. What is the minimum supported Prism Central size?
An administrator needs to protect a set of workloads across three sites (Site A, Site B, Site C) managed by different Prism Central instances. Which is the most efficient way to protect such VMs?
An administrator wants to define a set of conditions and approvers that must be satisfied before a deployment can proceed.
Which component must be enabled?
A VM is protected by a protection policy and the volume group is configured with CHAP authentication. An administrator rotates the VM’s password as part of the monthly routine. What action must the administrator perform to ensure the password is retained in the event of a failover?
An administrator wants to adjust how often the platform checks for security drift without modifying controls that run at fixed intervals.
Which setting should the administrator modify?
An administrator detects suspicious outbound connections from a single VM that hosts a web tier component.
The incident response requirement is to immediately quarantine the VM so it cannot communicate with any other workload, but still allow connectivity from a designated forensic tooling group so investigators can collect evidence.
The organization uses categories for policy scope and wants a change that can be applied quickly during an incident without redesigning existing policies.
Which action best meets the requirement?
An administrator is creating a settings profile in Prism Central to standardize NTP configuration across multiple clusters. The organization ' s security policy requires that all NTP communication must be authenticated.
The administrator adds an NTP server to the profile, but does not see the Key ID and Key Hex fields.
What is the most likely cause?
How many storage pools and storage containers are created during cluster creation?
Refer to Exhibit:
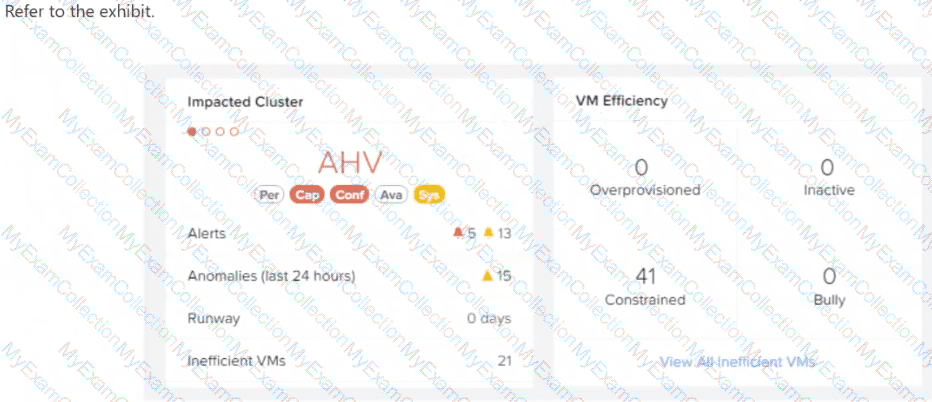
After logging into Prism Central, an administrator observes that there are a large number of constrained VMs.
What does this indicate about those VMs?
A company has purchased Nutanix hardware for multiple remote branch offices. The IT team at headquarters needs to image and deploy all clusters remotely from a central location.
An administrator deploys Foundation Central from the Prism Central Marketplace.
What capability does Foundation Central provide in this scenario?
An administrator added an SSH public key and verified connectivity to CVMs and AHV hosts. What is the recommended next step to reduce interactive access risk?
Refer to Exhibit:
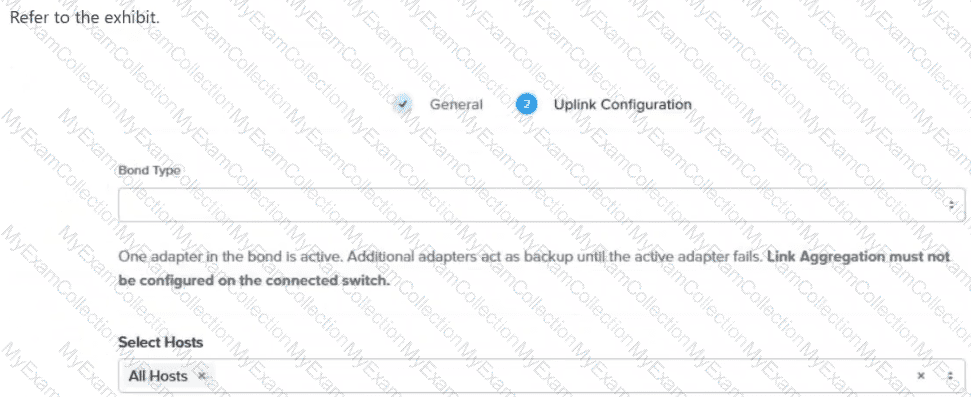
An administrator has been tasked with enabling LACP on an AHV cluster. In the exhibit, which option is the best to select for Bond Type when completing the task?
An administrator supports multiple AHV clusters under Prism Central and uses Intelligent Operations playbooks for remediation.
The organization recently standardized alert policies, but the alert policy names and IDs change between environments due to automated deployments and periodic updates.
The requirement is to trigger a remediation playbook for any alert that matches a defined performance pattern (for example, impact type and severity plus a keyword pattern), regardless of which specific alert policy generated it, while avoiding unrelated non-performance alerts.
Which playbook trigger best meets the requirement?
An administrator needs to migrate an existing VM from a 3-tier ESXi environment to Nutanix AHV.
What should be used to minimize downtime during the migration?
An administrator is tasked with creating a Disaster Recovery plan between two clusters within Prism Central local AZ. To ensure a failover operation is successful, the administrator also needs the ability to test recovery in both directions.
What are the recommended networks required between the two clusters for successfully testing the recovery?
After scaling out Prism Central to improve resiliency, which additional configuration should an administrator complete?
An administrator needs to enable software data-at-rest encryption on a 2-node ROBO cluster. The organization requires that encryption keys are stored on-premises outside of the cluster. Which KMS type should the administrator configure?
An administrator has a large group of VMs for the marketing team that all have the same RPO requirements of a snapshot every hour. A Protection Policy already exists with an hourly snapshot schedule. What is the easiest way to add this group of VMs to the Protection Policy?
An administrator needs an account for automation that can be granted granular permissions and being authenticated without an interactive user password.
Which statement best describes how a Prism Central service account authenticates?
A corporate security policy mandates strict protection against boot-level rootkits and requires the isolation of NTLM password hashes from the running operating system to prevent " pass-the-hash " attacks.
During the initial testing phase, the administrator deploys a test VM using the standard AHV creation workflow. While configuring the guest operating system, administrator attempts to enable Windows Defender Credential Guard via Group Policy. However, the feature fails to start, and the system logs indicate that the underlying virtualization platform does not meet the necessary hardware security requirements.
Which specific configuration change must the administrator apply to the VM to satisfy the security policy requirements?
An administrator ran NCC checks and noticed the following failure:
Node x.x.x.x: FAIL: No NTP servers are configured in the cluster configuration Refer to KB 4519 ...
What is the minimum number of NTP servers that should be configured to be considered a good configuration that will ensure a high degree of accuracy?
Which storage-optimization method is recommended for full clone VDI workloads?

