Upon logging into Prism Central, an administrator notices high cluster latency.
How can the administrator analyze data with the least number of steps or actions?
An Administrator is working on a one-node ROBO cluster configurations
Which statement is true for this configuration?
How should an administrator correct an SSL error when connecting to a Nutanix cluster?
An Administrator has been asked to deploy VMs using a specific image. The image has been configured with settings and applications that will be used by engineering to develop a new product by the company.
The image is not available on the desired cluster, but it is available in other cluster associated with Prism Central.
Why isno’t the image available?
An administrator is adding a node with a higher AOS release to an existing cluster.
What is the most efficient action an administrator should take to ensure it is in a supported state?
Which command should an administrator run from the CLI to view the uplink state of all AHV nodes in the
cluster?
Refer to Exhibit:
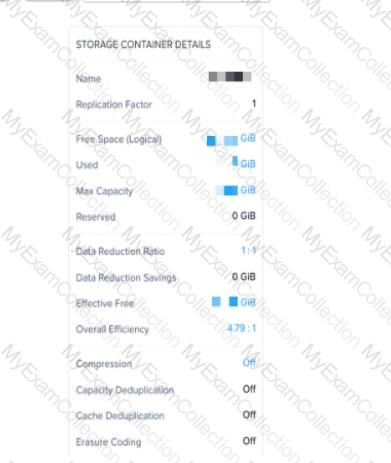
An administrator needs to enable inline deduplication for a pre-existing storage container. When trying to enable deduplication on the storage container. this feature is grayed-out.
What is the reason for this behavior?
When configuring Prism Central, which two log modules are able to forward messages to an external syslog server? (Choose two.
An administrator wants to ensure that data in a container is stored in the most space efficient manner as quickly as possible after being written,
Which space efficiency too meets this requirement?
In Nutanix clusters, which feature ensures VMs can be migrated and restarted on another host in case of failure?
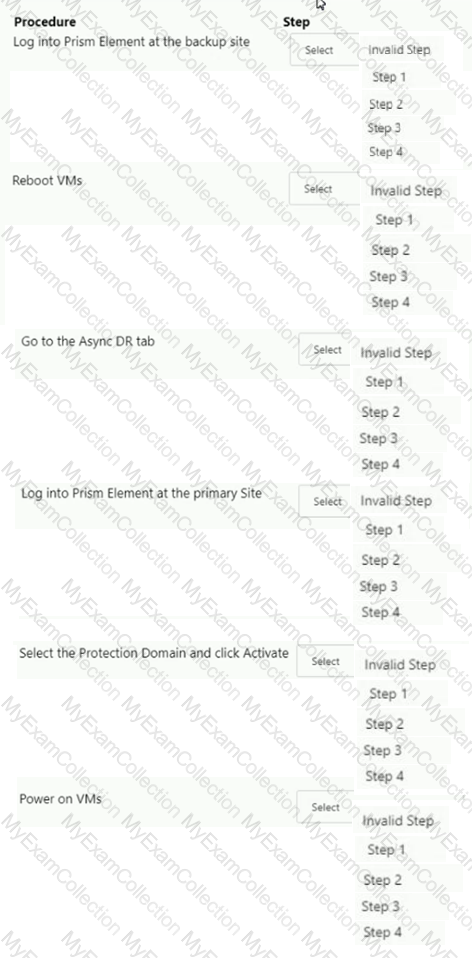
Async DR is configured between two sites. A network outage occurs at the primary site.
Which steps must the administrator perform to bring the VMs back into service at the backup site?
Item instructions: For each procedure, indicate the order in which that procedure must take place to meet the item requirements. Not all procedures are valid. Identify any invalid procedures using the drop-down option.
The administrator wants a container to be displayed and limited to 1TB in the hypervisor.
What advanced container setting must the administrator set?
An administrator logs in to Prism Element goes to the Network view, and sees the output shown in the exhibit.
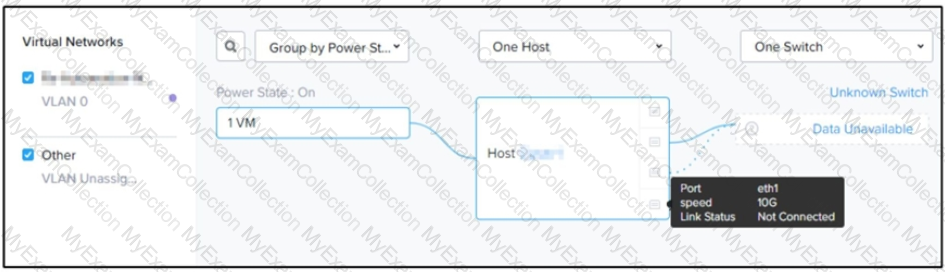
Which three steps must the administrator take to increase throughput to the host? (Choose three.)
A customer has a newly-deployed AHV cluster with nodes that have 2.x 10 GBE and 2.x interface. The customer wants to use all available network interfaces to provide connectivity to the VMs.
Which option should the administrator use to achieve this while remaining consistent with Nutanix recommendations?
A user running a Computer Aided Design (CAD) application is complaining about slow response time within the VM, particular when moving windows or rendering images.
Which VM metric will guide the administrator toward diagnosing the problem?
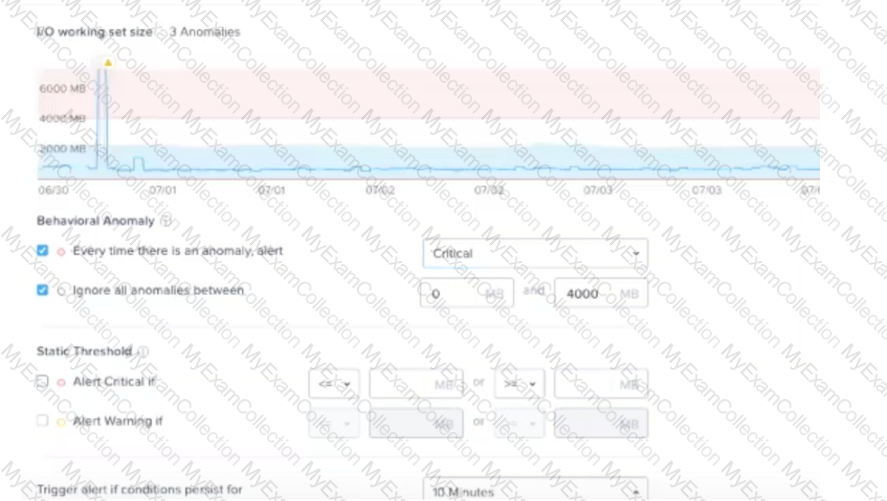
An administrator wants to reduce the largest amount of alert emails received from Prism Central.
Which two settings should the administrator customize to meet this requirement? (Choose two)
A vDisk is read by multiple VMs. The cluster creates immutable copies of the vDisk. What are these vDisk copies called?
Which three cluster operations require an administrator to reclaim licenses?(Choose three)
After running an LCM inventory it is noticed that there are a number of firmware and software updates available. The administrator would like to avoid any host reboots, but would like to apply some of the available updates?
Which two updates can be done while avoiding a host reboot? (Choose two.)
An administrator has set up a local web server accessible to the Nutanix clusters.
Which two steps are required to set up LCM for an environment without Internet access? (Choose two.)
While installing Windows 2019 on a new VM on an AHV cluster, an administrator notices there aren’t any drives listed for the install.
What might the problem be?
A customer has a 24-node cluster with all containers configured with RF3. Two different nodes have incurred a simultaneous HDD failure.
What is the result?
An administrator has been alerted to a VM that has high I/O latency and wants to determine if there are any other factors, such as insufficient network or memory resources that correlate, as part of a troubleshooting process.
Which type of chart should the administrator create to allow all relevant data to be easily exported to CSV for later analysis?
An administrator has been asked to enable block awareness and increase the fault tolerance to FT2 on a Nutanix AHV cluster with the following configuration:
Four blocks
One node per block
Will the administrator be able to accomplish these tasks?
Which two private key types are supported by the Nutanix SSL certificate implementation? (Choose two.)
When a VM is connected to a Nutanix managed network, when is the IP addressed assigned?
Which method can be used to migrate a VM configured for UEFI-boot from a Nutanix Hyper-V cluster to AHV?
Which two capabilities does IPAM provide in a Nutanix networking configuration? (Choose two.)
Microsegmentation was recently enabled in a Nutanix environment. The administrator wants to leverage Prism Central to create a policy that will block all traffic regardless of direction, between two groups of VMs identified by their category.
Which policy should be used to meet this requirement?
An administrator wants to create a trunked interface on a VM on AOS 5.15x.
Which two steps should the administrator take first to achieve this? (Choose two)
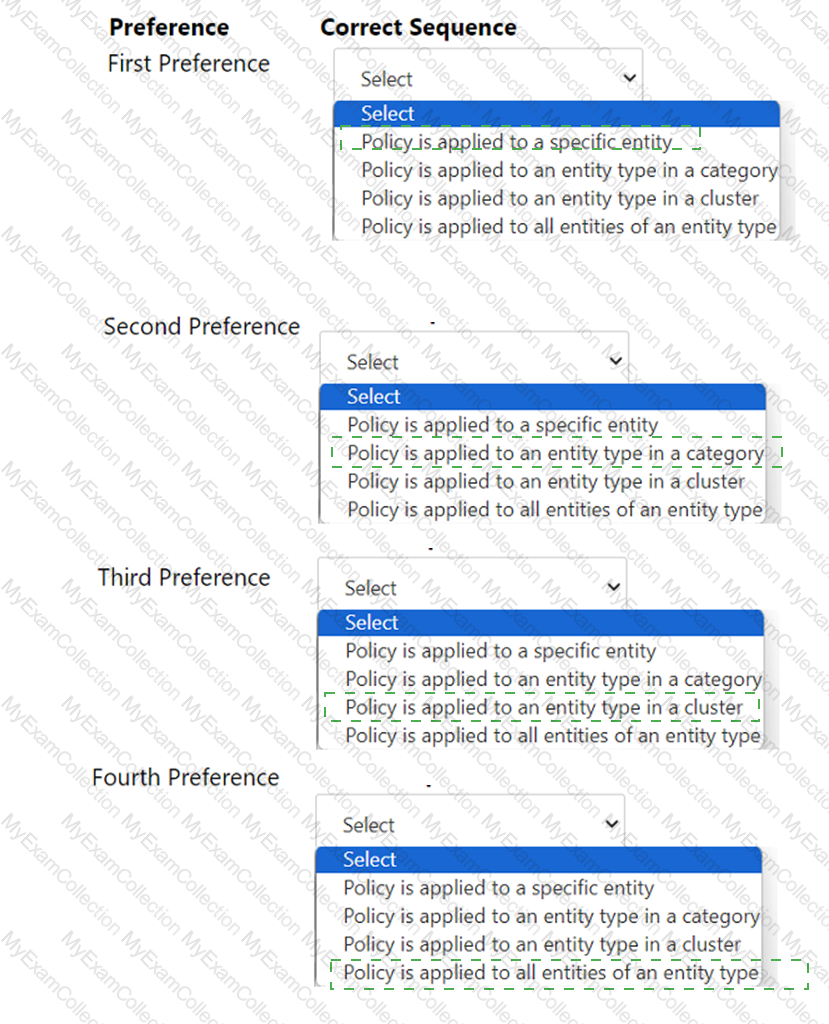
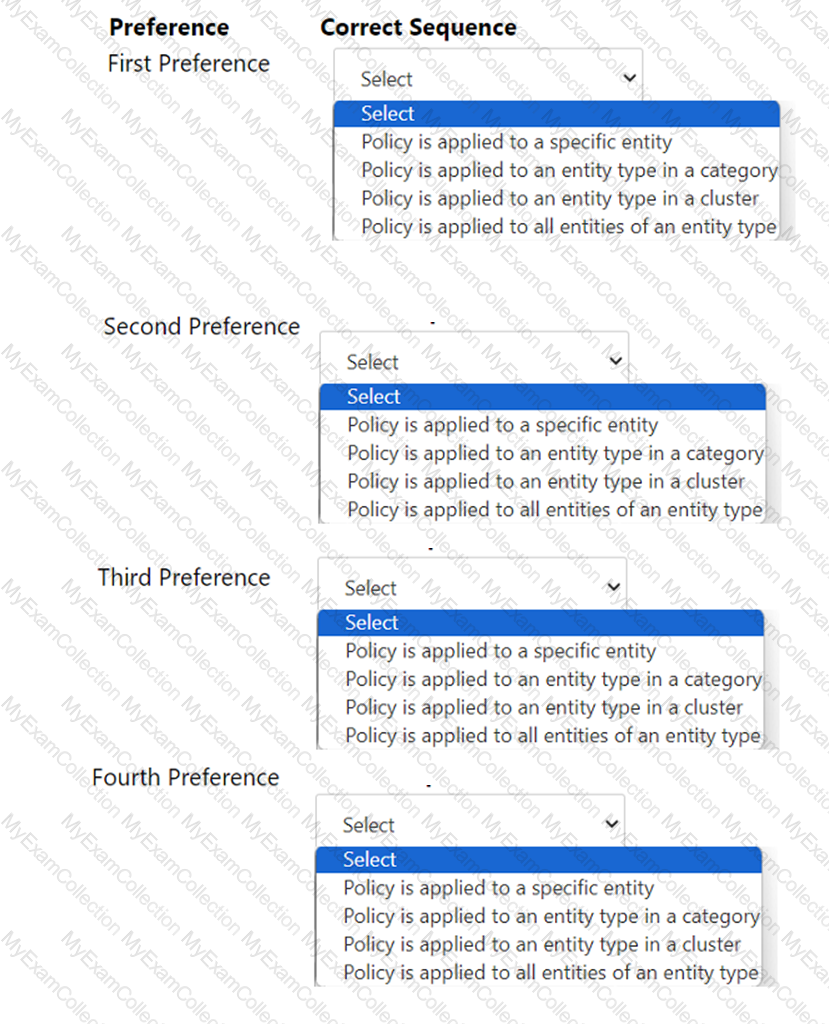
An administrator has created several custom alert policies, which are applied to the same entities. Prism Central displays a message that a similar policy exists.
In what order of precedence are overlapping policies evaluated?
An administrator manages a cluster and notices several failed components shown in the exhibit.

What two options does the administrator have to run all NCC checks manually? (Choose two.)
The administrator recently had a node fail in an AHV Nutanix cluster. All of the VMs restarted on other nodes in the cluster, but they discovered that the VMs that make up a SQL cluster were running on the failed host. The administrator has been asked to take measures to prevent a SQL outage in the future.
What affinity option will prevent the SQL VMs from running on the same hos?
A guest VM should be able to tolerate simultaneous failure of two nodes or drives.
What are the minimum requirements for the Nutanix cluster?
Refer to the exhibit.

Which two initial cluster configuration tasks were missed during the deployment process? (Choose two.)
An administrator is tasked with configuring networking on an AHV cluster and needs to optimize for maximum single VM throughput.
Which bond mode should the administrator select?
An administrator wants to receive an environment summary report when a host failure occurs.
Which action would address the administrator’s need?
An administrator has been tasked with increasing security on Nutanix cluster by disabling password authentication when accessing the CVM and AHV hosts and instead moving to key-based SSH,
What is the easiest way for the administrator to meet these needs?
After configuring Active Directory as the desired authentication service, an administrator is not able to login into Prism Central using privileged account.
Which configuration must be checked first?
An administrator manages an AHV cluster that is dedicated to a dev/test environment. The administrator receiving complaints from users that they are unable to create new VMs on the cluster.
After the reviewing the cluster, the administrator finds that the memory resources are almost fully utilized, with many VMs over-provisioned on memory.
What option is the most efficient resolution to enable additional VMs to be created?
An administrator migrates a VM onto a new Nutanix cluster- After the migration, the administrator observes the following conditions:
• Cluster memory utilization: 64%
• Cluster CPU utilization: 19%
• Cluster storage utilization. 32%
• Average VM CPU utilization: 25%
• Average VM CPU ready%: 24%
• Average VM memory utilization: 60%
Which two changes should the administrator make to improve VM performance? (Choose two.)
An administrator needs to bring down a host in a Nutanix Cluster for maintenance reasons. The administrator puts the host in maintenance mode.
What should the administrator do to perform an orderly shutdown of the CVM?
Which three configuration scenarios are valid for the deployment of Prism Central? (Choose three.)
Which inefficient VM Profile can be used to identify a VM that consumes too many resources and causes other VMs to starve?
Which change can be made on a cluster with software-based Data-at-Rest Encryption enabled?