A network technician is adding a new switch to increase capacity on the network. The technician connects the two switches using a single cable. Several hosts are moved to the new switch, but none of the hosts can access the network or internet. Which of the following should the technician do to resolve the issue?
A small business is choosing between static and dynamic routing for its network. Which of the following is the best reason to use dynamic routing in a growing network?
Users are experiencing significant lag while connecting to a cloud-based application during peak hours. An examination of the network reveals that the bandwidth is being heavily utilized. Further analysis shows that only a few users are using the application at any given time. Which of the following is the most cost-effective solution for this issue?
Which of the following tools uses ICMP to help determine whether a network host is reachable?
Which of the following connection methods allows a network engineer to automate configuration deployment for network devices across the environment?
Which of the following cloud platform technology characteristics would a quantum computing host most likely prioritize?
Which of the following is the most likely reason an insurance brokerage would enforce VPN usage?
A network administrator is planning to implement device monitoring to enhance network visibility. The security that the solution provides authentication and encryption. Which of the following meets these requirements?
Which of the following is the best way to keep devices on during a loss of power?
A network administrator needs to create a way to redirect a network resource that has been on the local network but is now hosted as a SaaS solution. Which of the following records should be used to accomplish the task?
A company is hosting a secure that requires all connections to the server to be encrypted. A junior administrator needs to harded the web server. The following ports on the web server. The following ports on the web server are open:

Which of the following ports should be disabled?
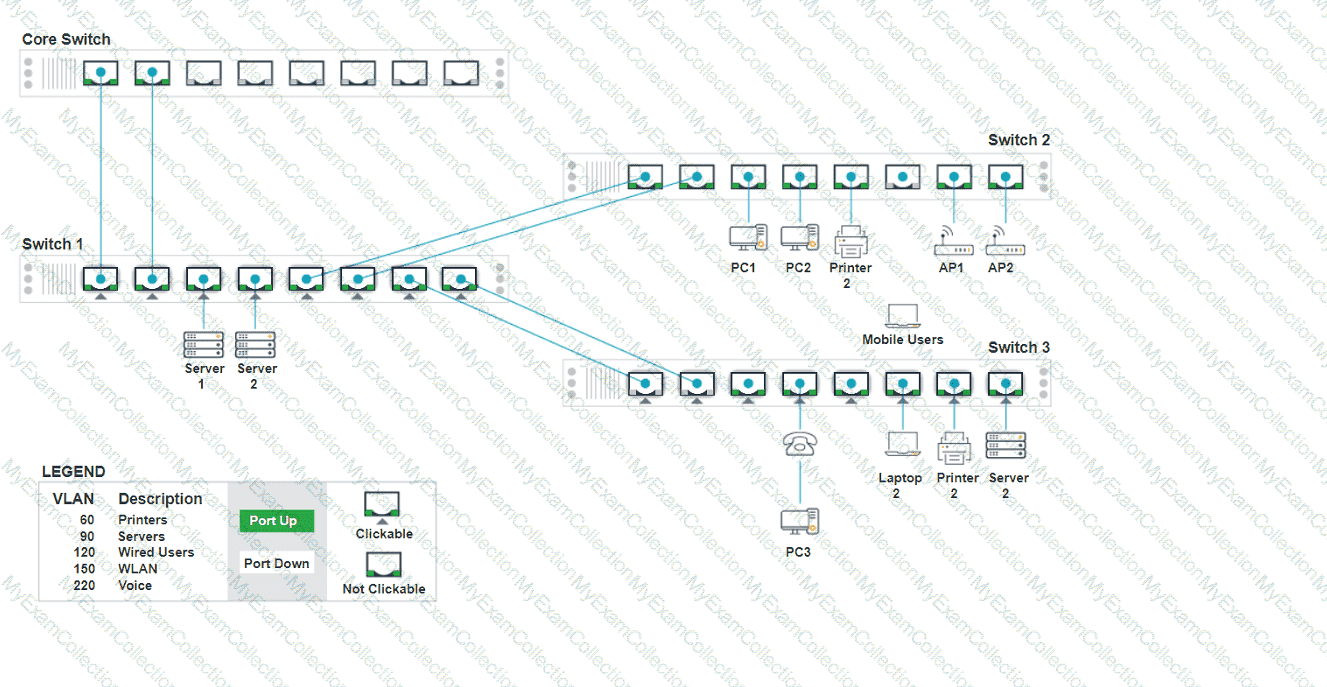
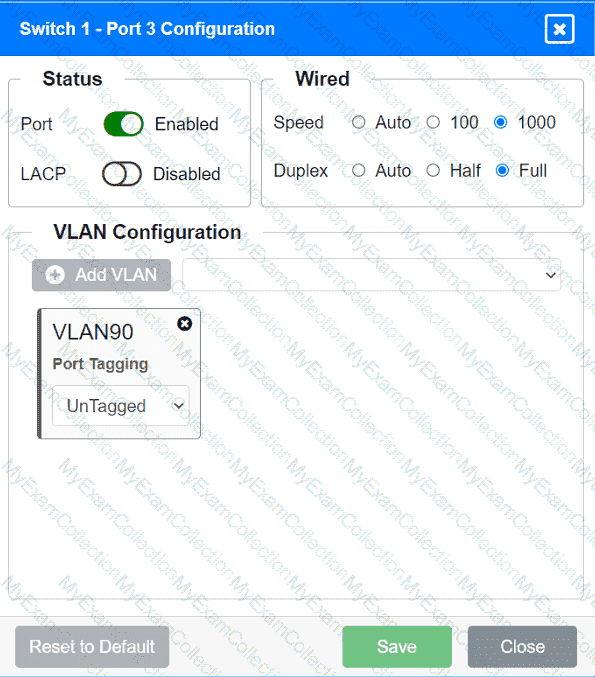
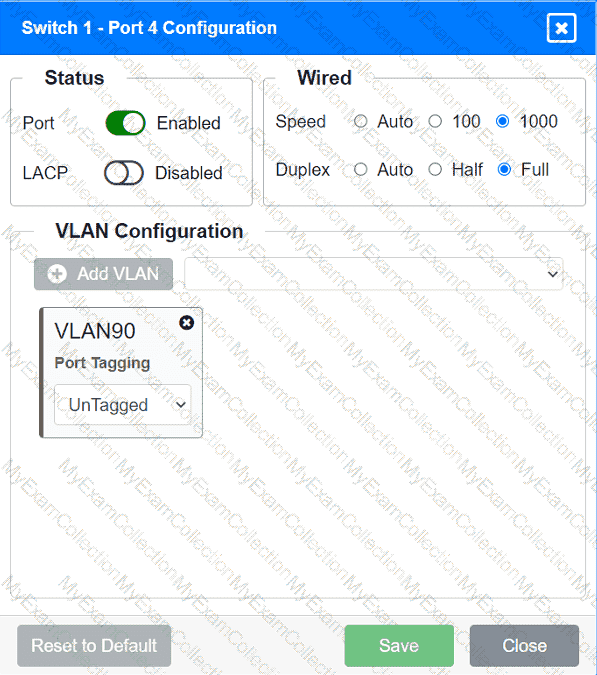
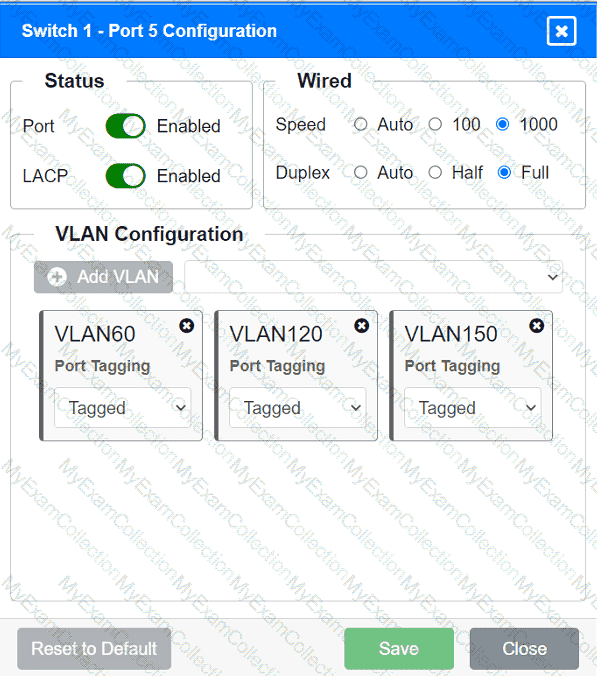
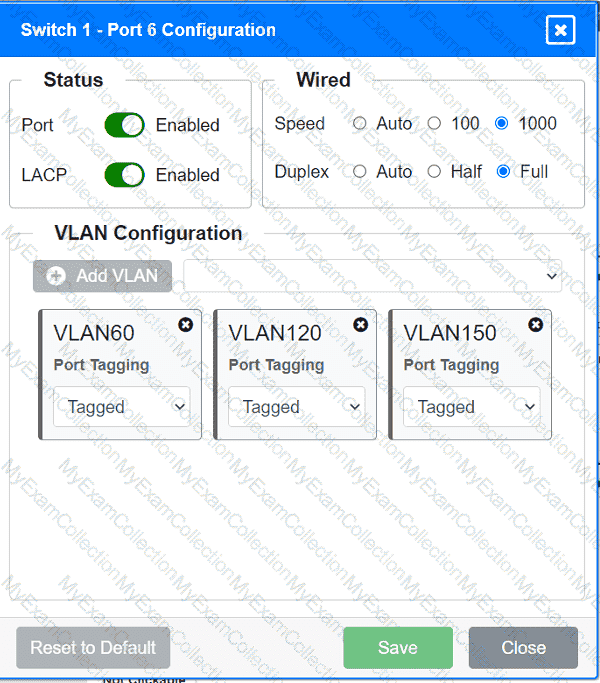
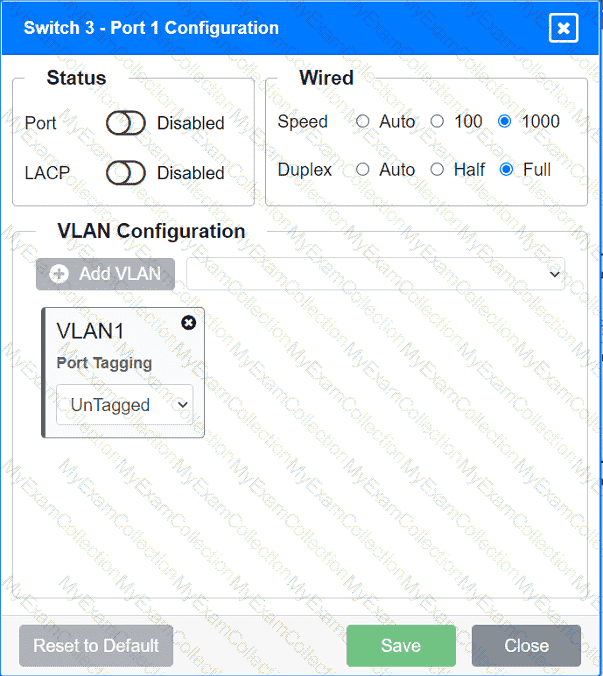
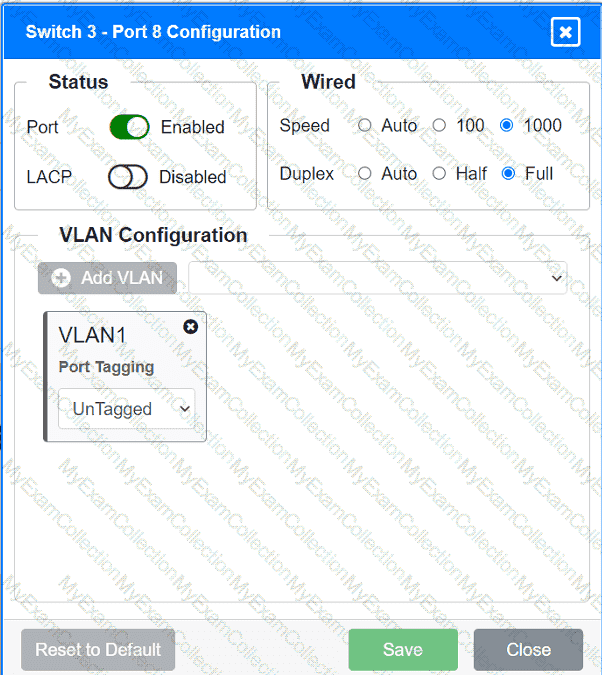
A network technician replaced an access layer switch and needs to reconfigure it to allow the connected devices to connect to the correct networks.
INSTRUCTIONS
Click on the appropriate port(s) on Switch 1 and Switch 3 to verify or reconfigure the
correct settings:
· Ensure each device accesses only its
correctly associated network.
· Disable all unused switchports.
. Require fault-tolerant connections
between the switches.
. Only make necessary changes to
complete the above requirements.
A network engineer is installing new PoE wireless APs. The first five APs deploy successfully, but the sixth one fails to start. Which of the following should the engineer investigate first?
A network administrator needs to configure the core switches where multiple connections between data centers are used. Given the following requirements:
• Fault tolerance and redundancy
• Vendor interoperability
• Increased bandwidth
• Cost effectiveness
• Simplified management
Which of the following should the administrator configure?
Which of the following is associated with avoidance, acceptance, mitigation, and transfer?
A network administrator needs to connect a multimode fiber cable from the MDF to the server room. The administrator connects the cable to Switch 2, but there is no link light. The administrator tests the fiber and finds it does not have any issues. Swapping the connection to Switch 1 in a working port is successful, but the swapped connection does not work on Switch 2. Which of the following should the administrator verify next?
A company is migrating a data center from on premises to the cloud. Which of the following tools will help maintain consistency, reliability, and efficiency of provisioning and management?
Which of the following is used to store and deliver content to clients in a geographically distributed manner using edge servers?
Which of the following is most commonly associated with many systems sharing one IP address in the public IP-addressing space?
A network administrator installs a node that requires a media converter to connect Ethernet to fiber but sees no link light on the node. The administrator notices the following:
Both terminating points are properly seated.
Both the fiber and Ethernet cables have been successfully tested.
The media converter is turned on.
The switchport is configured as half duplex.
Which of the following is the reason the link light is not on?
A network engineer sees traffic going to 224.7.8.99. Which of the following describes this traffic type?
A technician is troubleshooting wireless connectivity near a break room. Whenever a user turns on the microwave, connectivity to the user ' s laptop is lost. Which of the following frequency bands is the laptop most likely using?
Which of the following is the most cost-effective way for a network administrator to establish a persistent, secure connection between two facilities?
Which of the following ports should a network administrator enable for encrypted login to a network switch?
Which of the following is the best networking appliance for interconnecting multiple logical networks and forwarding data packets between them while minimizing latency?
A network administrator needs to divide a Class B network into four equal subnets, each with a host range of 1,000 hosts. Which of the following subnet masks should the administrator use?
A network engineer receives a vendor alert regarding a vulnerability in a router CPU. Which of the following should the engineer do to resolve the issue?
A technician needs to quickly set up a network with five wireless devices. Which of the following network types should the technician configure to accomplish this task?
A company security policy requires all network traffic from remote employees ' corporate laptops to use the company’s VPN. Which of the following network access methods best describes this scenario?
An organization wants better network visibility. The organization ' s requirements include:
Multivendor/OS-monitoring capabilities
Real-time collection
Data correlation
Which of the following meets these requirements?
Early in the morning, an administrator installs a new DHCP server. In the afternoon, some users report they are experiencing network outages. Which of the following is the most likely issue?
A customer calls the help desk to report issues connection to the internet. The customer can reach a local database server. A technician goes to the site and examines the configuration:
Which of the following is causing the user ' s issue?
During a VoIP call, a user notices inconsistent audio and logs an incident ticket. A network administrator notices inconsistent delays in arrival of the RTP packets. Which of the following troubleshooting tools should the network administrator use to determine the issue?
A network administrator is troubleshooting a connectivity issue between two devices on two different subnets. The administrator verifies that both devices can successfully ping other devices on the same subnet. Which of the following is the most likely cause of the connectivity issue?
To reduce costs and increase mobility, a Chief Technology Officer (CTO) wants to adopt cloud services for the organization and its affiliates. To reduce the impact for users, the CTO wants key services to run from the on-site data center and enterprise services to run in the cloud. Which of the following deployment models is the best choice for the organization?
Which of the following best describes a characteristic of a DNS poisoning attack?
After a recent security awareness phishing campaign, the cybersecurity team discovers that additional security measures need to be set up when users access potentially malicious websites. Which of the following security measures will best address this concern?
An organization has a security requirement that all network connections can be traced back to a user. A network administrator needs to identify a solution to implement on the wireless network. Which of the following is the best solution?
A network manager connects two switches together and uses two connecting links. Which of the following configurations will prevent Layer 2 loops?
Which of the following provides simple authentication to access network devices while also providing logging capabilities?
A network technician is configuring the company’s network of 100 Mbps Layer 2 switches. The technician wants increased throughput for the uplinks between switches. The technician connects multiple redundant links between the switches. Which of the following should the technician configure?
A network administrator wants to increase network security by preventing client devices from communicating directly with each other on the same subnet. Which of the following technologies should be implemented?
A network engineer needs to change, update, and control APs remotely, with real-time visibility over HTTPS. Which of the following will best allow these actions?
A junior network administrator is auditing the company network and notices incrementing input errors on a long-range microwave interface. Which of the following is the most likely reason for the errors?
Which of the following allows a user to authenticate to multiple resources without requiring additional passwords?
A network engineer must determine which ports are currently established from a client device. Given the following:
Active Connections
Proto Local Address Foreign Address State
TCP 10.203.10.11:3389 207.141.201.10:65278 ESTABLISHED
TCP 10.203.10.11:49678 168.63.129.16:32526 ESTABLISHED
TCP 10.203.10.11:49688 168.63.129.16:http ESTABLISHED
TCP 10.203.10.11:49701 168.63.129.16:32526 ESTABLISHED
TCP 10.203.10.11:52502 20.190.135.17:https TIME_WAIT
TCP 10.203.10.11:52554 168.63.129.16:http TIME_WAIT
Which of the following commands was used to produce the output?
Which of the following attacks forces a switch to send all traffic out of all ports?
A network administrator needs to connect two routers in a point-to-point configuration and conserve IP space. Which of the following subnets should the administrator use?
Which of the following does a router prioritize first in the route selection process?
Which of the following protocols is used to route traffic on the public internet?
A company implements a video streaming solution that will play on all computers that have joined a particular group, but router ACLs are blocking the traffic. Which of the following is the most appropriate IP address that will be allowed in the ACL?
A network technician is troubleshooting the connection to the company website. The traceroute command produces the following output:
Traceroute towww.mysite.com(8.8.8.8) over a maximum of 30 hops
10.1.1.1 < 1 ms 2. * < 1 ms < 1 ms
k k
k kTraceroute completeWhich of the following should the technician do to identify the path to the server?
A network administrator has been monitoring the company ' s servers to ensure that they are available. Which of the following should the administrator use for this task?
A network engineer discovers network traffic that is sending confidential information to an unauthorized and unknown destination. Which of the following best describes the cause of this network traffic?
Which of the following network traffic type is sent to all nodes on the network?
Which of the following connector types would most likely be used to connect to an external antenna?
In an environment with one router, which of the following will allow a network engineer to communicate between VLANs without purchasing additional hardware?
A network engineer is completing a new VoIP installation, but the phones cannot find the TFTP server to download the configuration files. Which of the following DHCP features would help the phone reach the TFTP server?
A critical infrastructure switch is identified as end-of-support. Which of the following is the best next step to ensure security?
A technician needs to identify a computer on the network that is reportedly downloading unauthorized content. Which of the following should the technician use?
Which of the following uses the longest prefix match to determine an exit interface?
An IT department is considering implementing a SIEM solution to improve network security. The department wants to ensure that the SIEM system is able to ingest and analyze logs from all of the company’s core devices. Which of the following is the most important consideration when selecting a SIEM solution?
A new backup system takes too long to copy files to the new SAN each night. A network administrator makes a simple change to the network and the devices to decrease backup times. Which of the following does the network administrator change?
A network administrator wants to configure a backup route in case the primary route fails. A dynamic routing protocol is not installed on the router. Which of the following routing features should the administrator choose to accomplish this task?
A network engineer is designing an internal network that needs to support both IPv4 and IPv6 routing. Which of the following routing protocols is capable of supporting both IPv4 and IPv6?
Which of the following steps of the troubleshooting methodology comes after testing the theory to determine cause?
A network administrator deploys new network hardware. While configuring the network monitoring server, the server could authenticate but could not determine the specific status of the hardware. Which of the following would the administrator most likely do to resolve the issue?
A customer wants to cache commonly used content to reduce the number of full page downloads from the internet. Which of the following should the network administrator recommend?
A network administrator notices interference with industrial equipment in the 2.4GHz range. Which of the following technologies would most likely mitigate this issue? (Select two).
An attack on an internal server is traced to an isolated guest network. Which of the following best describes the attack?
A company recently implemented a videoconferencing system that utilizes large amounts of bandwidth. Users start reporting slow internet speeds and an overall decrease in network performance. Which of the following are most likely the causes of the network performance issues? (Select two)
Which of the following should an installer orient a port-side exhaust to when installing equipment?
A network administrator recently upgraded a wireless infrastructure with new APs. Users report that when stationary, the wireless connection drops and reconnects every 20 to 30 seconds. While reviewing logs, the administrator notices the APs are changing channels.
Which of the following is the most likely reason for the service interruptions?
Which of the following offers the ability to manage access at the cloud VM instance?
Which of the following layers in the OSI model is responsible for establishing, maintaining, and terminating connections between nodes?
A company is implementing a new internal network in which all devices use IPv6 addresses. Which of the following routing protocols will be best for this setup?
A network administrator is unable to ping a remote server from a newly connected workstation that has been added to the network. Ping to 127.0.0.1 on the workstation is failing. Which of the following should the administrator perform to diagnose the problem?
An administrator wants to find the top destination for traffic across the infrastructure on a specific day. Which of the following should the administrator use?
Which of the following physical installation factors is the most important when a network switch is installed in a sealed enclosure?
A customer recently moved into a new office and notices that some wall plates are not working and are not properly labeled Which of the following tools would be best to identify the proper wiring in the IDF?
A technician is plugging an Ethernet cable into a switch to bring a new device online, but the device is not showing an active network connection. Previously, another technician turned off unused switchports as part of device hardening. Which of the following describes the port status?
Which of the following is a cost-effective advantage of a split-tunnel VPN?
A company recently converted most of the office laptops to connect wirelessly to the corporate network. After a high-traffic malware attack, narrowing the event to a specific user was difficult because of the wireless configuration.
Which of the following actions should the company take?
A network administrator installed a new VLAN to the network after a company added an additional floor to the office. Users are unable to obtain an IP address on the new VLAN, but ports on existing VLANs are working properly. Which of the following configurations should the administrator update?
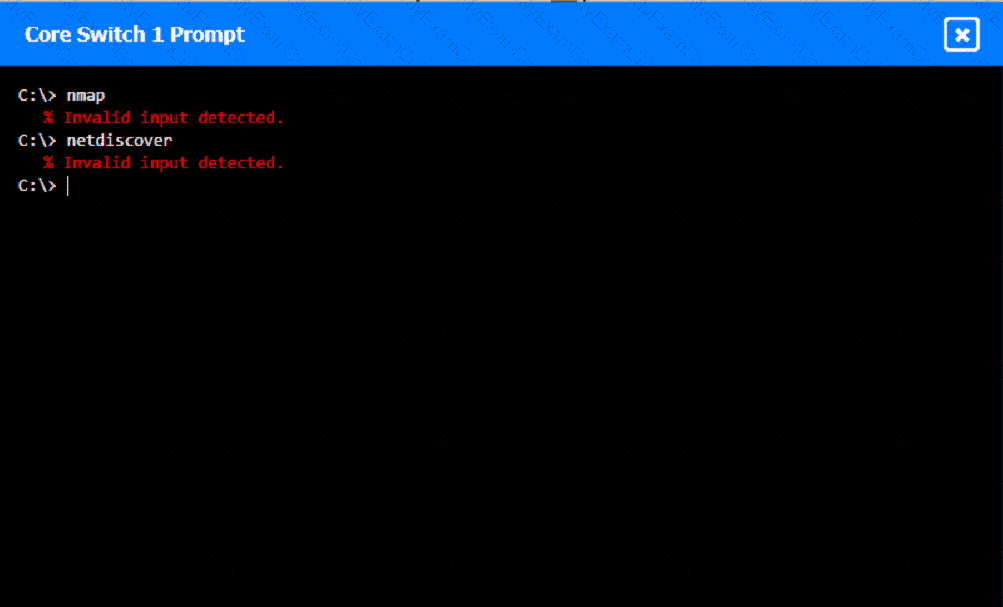
A network technician was recently onboarded to a company. A manager has
tasked the technician with documenting the network and has provided the technician With partial information from previous documentation.
Instructions:
Click on each switch to perform a network discovery by entering commands into the terminal. Fill in the missing information using drop-down menus provided.
Which of the following is used to describe the average duration of an outage for a specific service?
A customer calls the help desk to report that resources are no longer reachable. The resources were available before network changes were made. The technician verifies the report, investigates, and discovers that a new logical layout is segmenting the network using tagging. Which of the following appliances most likely needs to be reviewed to restore the connections?
A detective is investigating an identity theft case in which the target had an RFID-protected payment card issued and compromised in the same day. The only place the target claims to have used the card was at a local convenience store. The detective notices a video camera at the store is placed in such a way that customers ' credentials can be seen when they pay. Which of the following best explains this social engineering technique?
A network administrator is migrating a domain to a different provider. As part of the onboarding process, the new provider requests domain ownership proof. Which of the following records would the administrator most likely need to create?
Which of the following ports creates a secure connection to a directory service?
A technician is planning an equipement installation into a rack in a data center that practices hot aisle/cold aise ventilation. Which of the following directions should the equipement exhaust face when installed in the rack?
Which of the following cloud deployment models is most commonly associated with multitenancy and is generally offered by a service provider?
Which of the following cloud service models most likely requires the greatest up-front expense by the customer when migrating a data center to the cloud?
A network administrator is responding to a request to configure a new IP phone. Which of the following should the network administrator do to allow data and voice traffic to be properly prioritized?
Which of the following will allow secure, remote access to internal applications?
Which of the following is the best example of a networking appliance that connects different network segments and directs allowed traffic between specific segments?
Which of the following attacks would most likely cause duplicate IP addresses in a network?
A company is concerned that the public can use network wall jacks in publicly available conference rooms to access company servers. Which of the following is the best way to mitigate the vulnerability?
A company wants to implement data loss prevention by restricting user access to social media platforms and personal cloud storage on workstations. Which of the following types of filtering should the company deploy to achieve these goals?
A network technician needs to configure IP addressing in a Class C network with eight subnets total:
Three subnets for 60 hosts
Three subnets for 15 hosts
Two subnets for seven hosts
Which of the following solutions should the technician use to accomplish this task?
A new SQL server is identified as allowing FTP access to all users. Which of the following would a systems administrator most likely do to ensure only the required services are allowed?
A network engineer is now in charge of all SNMP management in the organization. The engineer must use a SNMP version that does not utilize plaintext data. Which of the following is the minimum version of SNMP that supports this requirement?
A support agent receives a report that a remote user’s wired devices are constantly disconnecting and have slow speeds. Upon inspection, the support agent sees that the user’s coaxial modern has a signal power of -97dB.
A company reports that their facsimile machine no longer has a dial tone when trying to send a fax. The phone cable is damaged on one end. Which of the following types of connectors should a technician replace?
A network engineer runs ipconfig and notices that the default gateway is 0.0.0.0. Which of the following address types is in use?
Which of the following could provide a lightweight and private connection to a remote box?
Users at an organization report that the wireless network is not working in some areas of the building. Users report that other wireless network SSIDs are visible when searching for the network, but the organization ' s network is not displayed. Which of the following is the most likely cause?
Which of the following would most likely be utilized to implement encryption in transit when using HTTPS?
A user ' s home mesh wireless network is experiencing latency issues. A technician has:
•Performed a speed test.
•Rebooted the devices.
•Performed a site survey.
•Performed a wireless packet capture.
The technician reviews the following information:
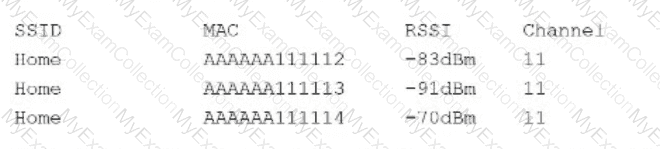
The technician notices in the packet capture that frames were retransmitted. Which of the following is the most likely cause of the user ' s network issue?
An employee in a corporate office clicks on a link in an email that was forwarded to them. The employee is redirected to a splash page that says the page is restricted. Which of the following security solutions is most likely in place?
A network technician is installing a new switch that does not support STP at the access layer of a network. The technician wants a redundant connection to the distribution switch. Which of the following should the technician use?
A network engineer connects a business to a new ISP. A simple ping test to 8.8.8.8 is successful. However, users complain of extreme slowness to any website and periods of no connectivity. Which of the following is the most likely cause?
A government entity wants to implement technology that can block websites based on country code. Which of the following will best enable this requirement?
A company is implementing a wireless solution in a high-density environment. Which of the following 802.11 standards is used when a company is concerned about device saturation and converage?
Which of the following troubleshooting steps provides a change advisory board with the information needed to make a decision?
Which of the following is the most secure way to provide site-to-site connectivity?
Which of the following kinds of targeted attacks uses multiple computers or bots to request the same resource repeatedly?
Which of the following is used most often when implementing a secure VPN?
A network engineer added more APs to improve wireless coverage. However, users now report that the connectivity disconnects and reconnects repeatedly. Which of the following is causing the issue?
Which of the following types of network architecture typically uses leased lines to provide dedicated, private connections between multiple satellite offices and a head office?
A small company has the following IP addressing strategy:
A user is unable to connect to the company fileshare server located at 192.168.10.1. The user’s networking configuration is:
Which of the following will most likely correct the issue?
A network engineer configures an application server so that it automatically adjusts resource allocation as demand changes. This server will host a new application and demand is not predictable. Which of the following concepts does this scenario demonstrate?
Which of the following is a type of NAC that uses a set of policies to allow or deny access to the network based on the user’s identity?
A network administrator performed upgrades on a server and installed a new NIC to improve performance. Following the upgrades, usera are unable to reach the server. Which of the following is the most likely reason.
A medical clinic recently configured a guest wireless network on the existing router. Since then, guests have been changing the music on the speaker system. Which of the following actions should the clinic take to prevent unauthorized access? (Select two).
Which of the following must be implemented to securely connect a company ' s headquarters with a branch location?
A Chief Executive Officer (CEO) of a company purchases a new phone that will be used while traveling to different countries. The CEO needs to be able to place outgoing calls and receive incoming calls on the phone using a SIM card. Which of the following cellular technologies does the CEO ' s phone need?
Which of the following OSI model layers manages the exchange of HTTP information?
Which of the following is used to redistribute traffic between one source and multiple servers that run the same service?
A secure communication link needs to be configured between data centers via the internet. The data centers are located in different regions. Which of the following is the best protocol for the network administrator to use?
A company wants to implement a disaster recovery site or non-critical applicance, which can tolerance a short period of downltime. Which of the followig type of sites should the company impelement to achive this goal?
An IT department asks a newly hired employee to use a personal laptop until the company can provide one. Which of the following policies is most applicable to this situation?
Which of the following technologies is most appropriate for a business that requires high-speed access to frequently used web content, such as images and videos?
Which of the following protocols is used to send networking status messages between clients and servers?
Which of the following VPN configurations forces a remote user to access internet resources through the corporate network?
A VoIP phone is plugged in to a port but cannot receive calls. Which of the following needs to be done on the port to address the issue?
A network administrator is conducting an assessment and finds network devices that do not meet standards. Which of the following configurations is considered a set of rules that devices should adhere to?
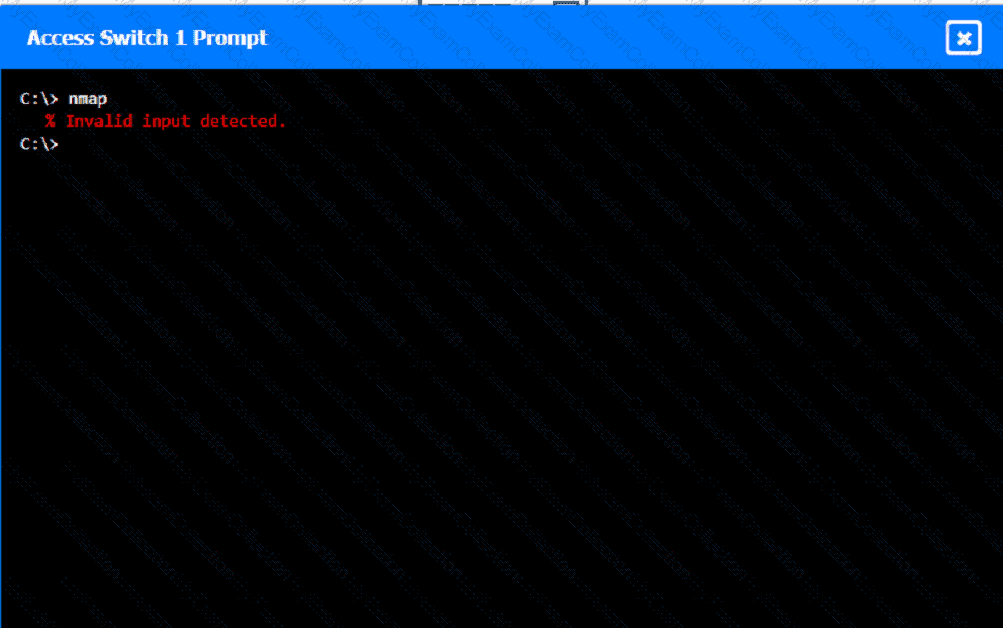
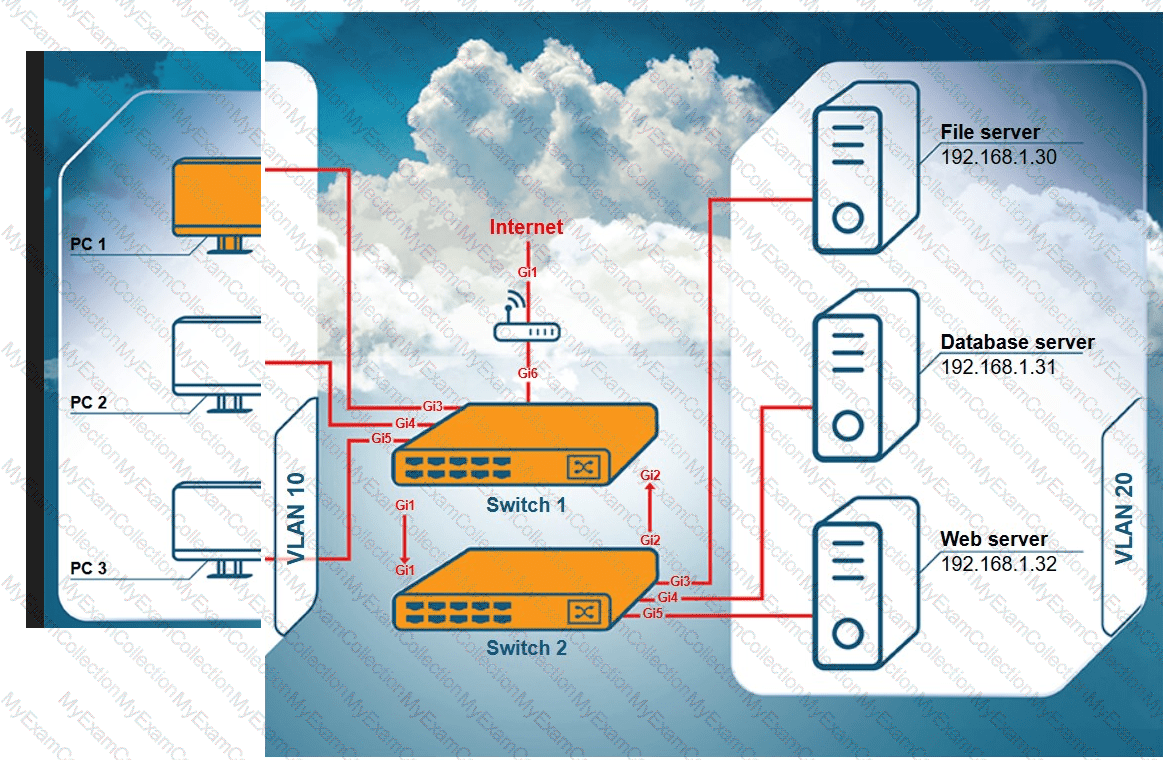
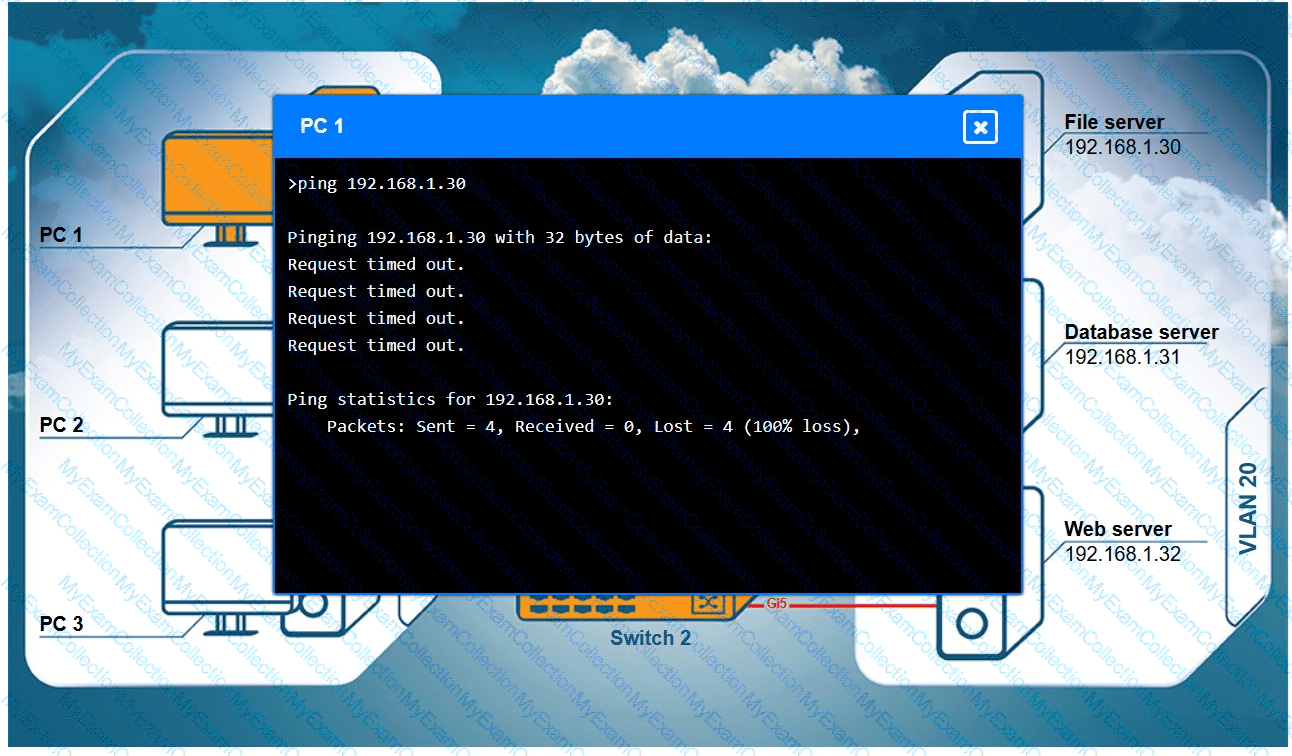
A network technician receives a ticket from an employee who is working on PC 1 but is unable to connect to the database server. The technician pings the database server from PC 1, but the request times out. After reviewing the utilization of Switch 1 and Switch 2, the technician finds high CPU utilization and sees that the MAC table is continuously changing.
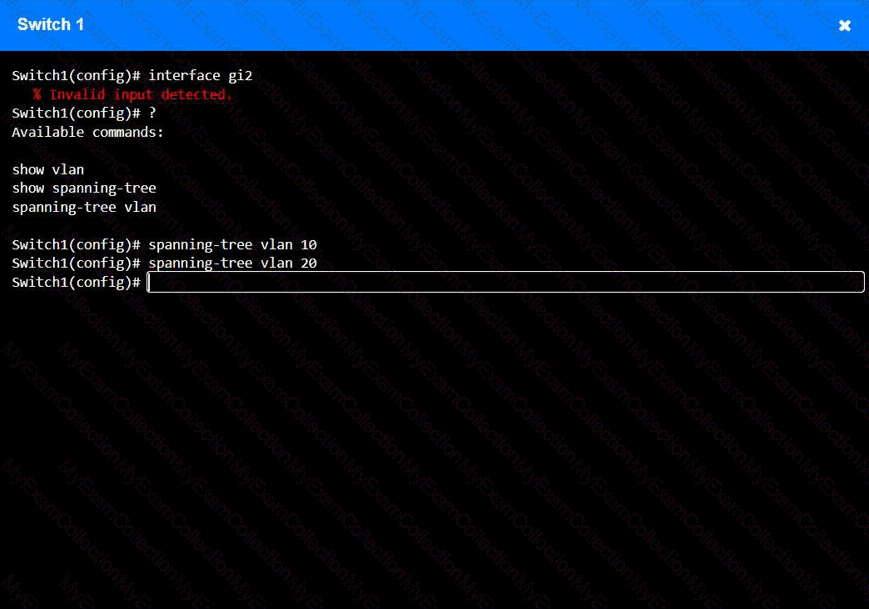
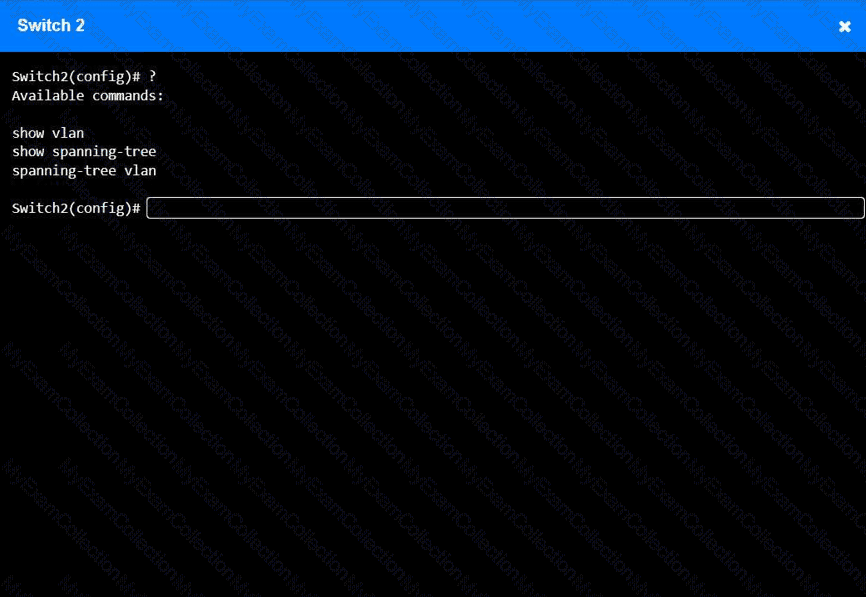
INSTRUCTIONS
Configure Switch 1 and Switch 2 to remediate the employee ' s issue. Then, validate connectivity between PC 1 and the database server.
Switch 1 and Switch 2 are already in configuration mode. Type help to view a list of available commands.
A network technician needs to install patch cords from the UTP patch panel to the access switch for a newly occupied set of offices. The patch panel is not labeled for easy jack identification. Which of the following tools provides the easiest way to identify the appropriate patch panel port?
A company ' s network is experiencing high latency and packet loss during peak hours. Network monitoring tools show increased traffic on a switch. Which of the following should a network technician implement to reduce the network congestion and improve performance?
Which of the following actions should be taken as part of the first step of the troubleshooting methodology?
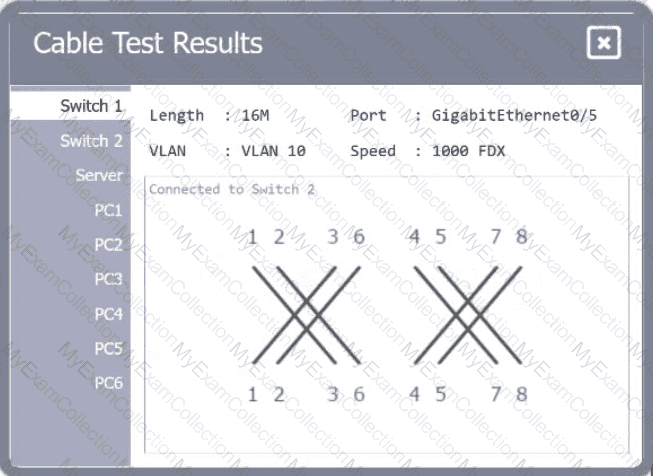
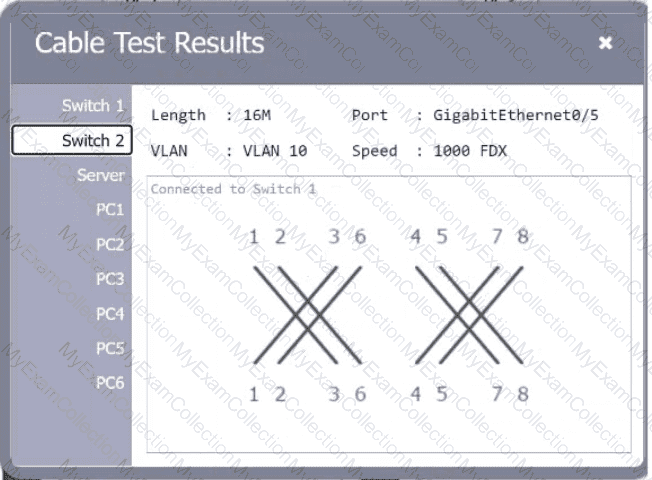
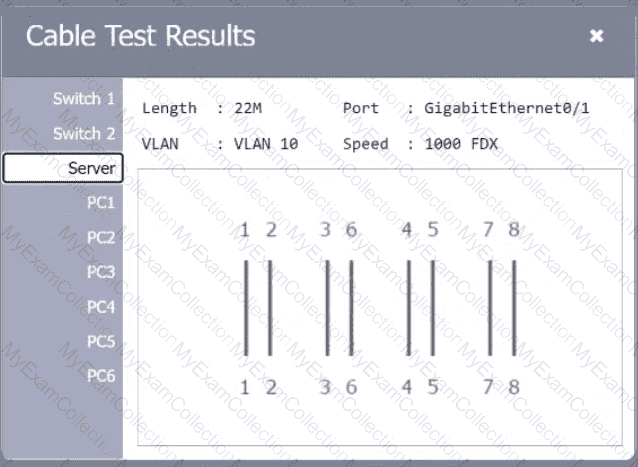
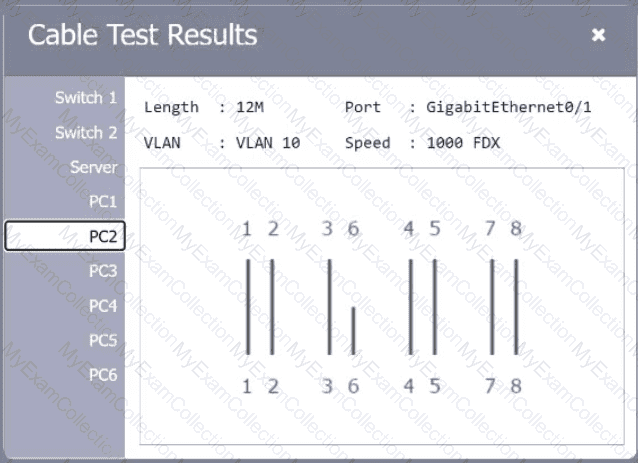
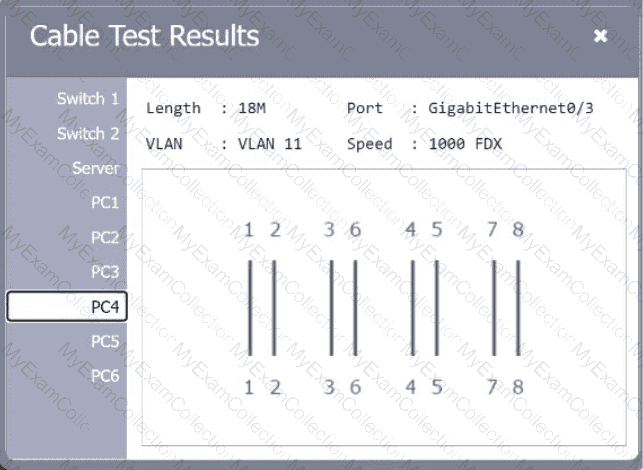
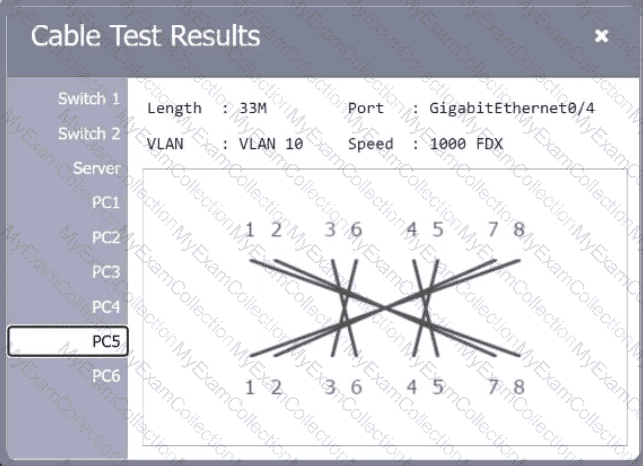
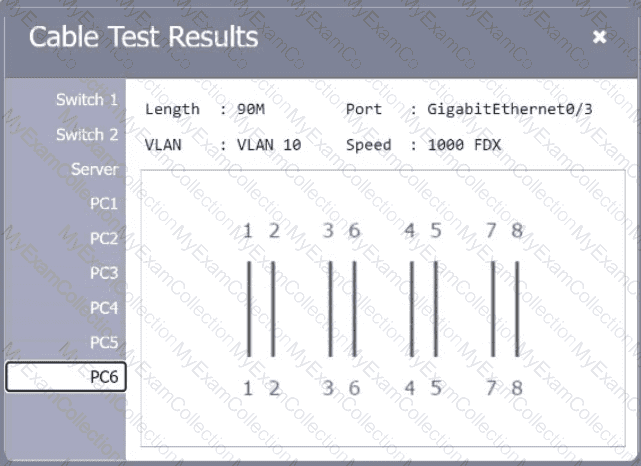
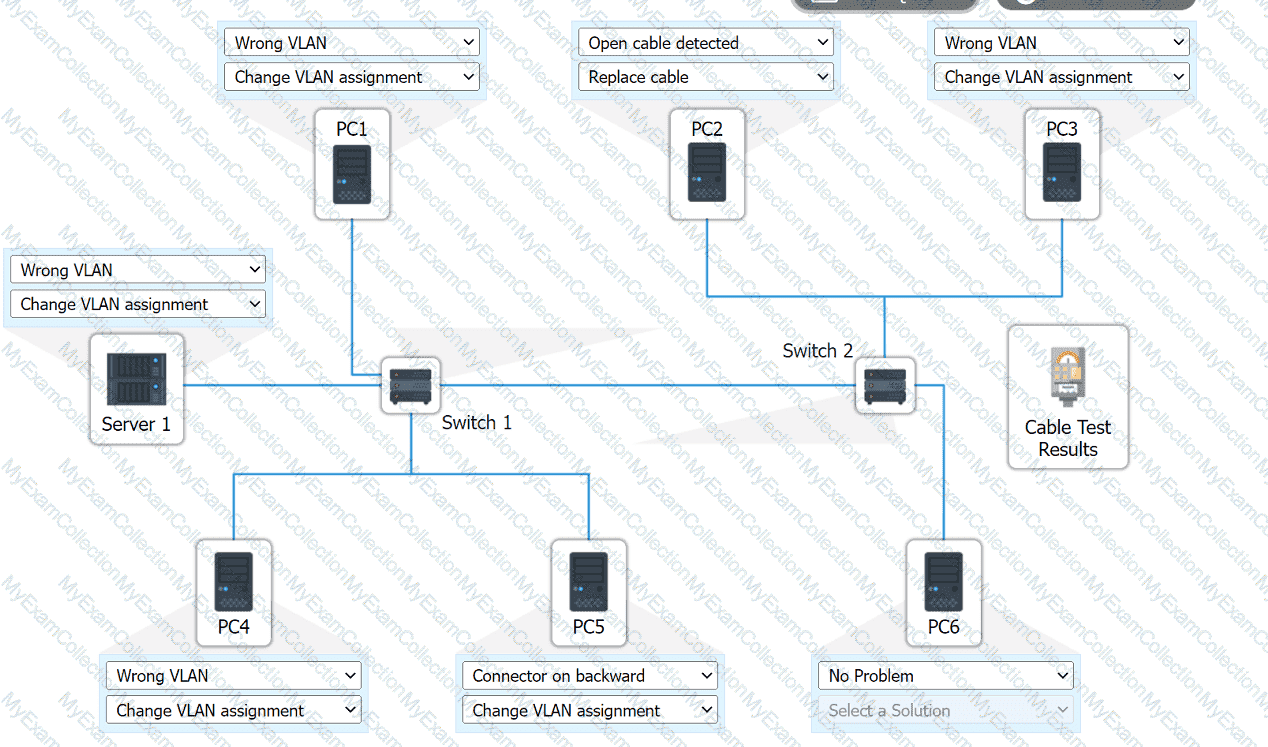
A network technician needs to resolve some issues with a customer ' s SOHO network. The
customer reports that some of the PCs are not connecting to the network, while others
appear to be working as intended.
INSTRUCTIONS
Troubleshoot all the network components.
Review the cable test results first, then diagnose by clicking on the appropriate PC,
server, and Layer 2 switch.
Identify any components with a problem and recommend a solution to correct each
problem.
If at any time you would like to bring back
the initial state of the simulation, please
click the Reset All button.
A network administrator ' s device is experiencing severe Wi-Fi interference within the corporate headquarters causing the device to constantly drop off the network. Which of the following is most likely the cause of the issue?
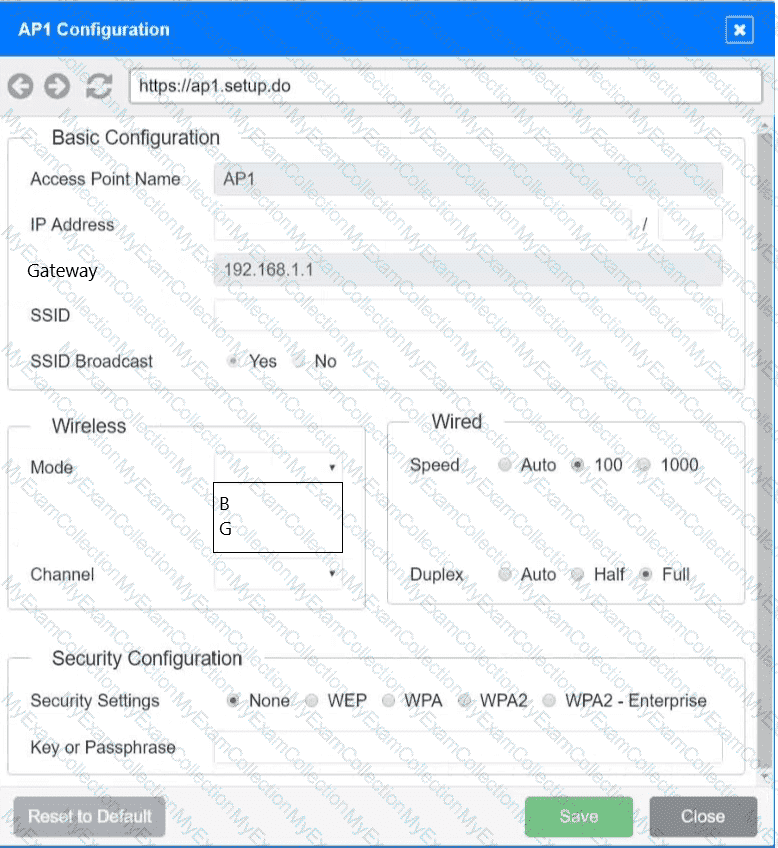
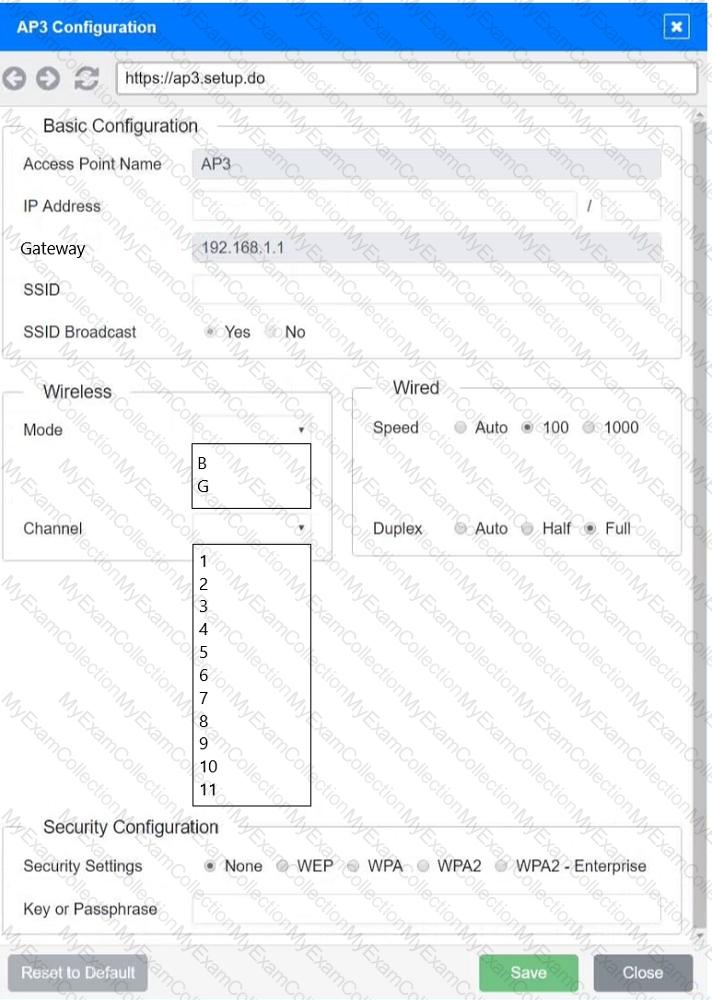
SIMULATION
You have been tasked with setting up a wireless network in an office. The network will consist of 3 Access Points and a single switch. The network must meet the following parameters:
The SSIDs need to be configured as CorpNet with a key of S3cr3t!
The wireless signals should not interfere with each other
The subnet the Access Points and switch are on should only support 30 devices maximum
The Access Points should be configured to only support TKIP clients at a maximum speed
INSTRUCTONS
Click on the wireless devices and review their information and adjust the settings of the access points to meet the given requirements.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A user reports issues accessing a file server on a LAN with the IP address 192.168.50.140 at a large facility with incomplete infrastructure documentation. The following are the results of the ping command:
ping -c 10 192.168.50.140
Packets: Sent = 10, Received = 5, Lost = 5 (50% loss)
Round-trip times: Minimum = 3ms, Maximum = 144ms, Average = 42ms
Which of the following should a technician do next to continue troubleshooting the issue at the switch with minimal impact?
A network administrator needs a solution to isolate and potentially identify any threat actors that are attempting to breach the network. Which of the following should the administrator implement to determine the type of attack used?
A network administrator receives complaints of intermittent network connectivity issues. The administrator investigates and finds that the network design contains potential loop scenarios. Which of the following should the administrator do?
A network technician sets up a computer on the accounting department floor for a user from the marketing department. The user reports that they cannot access the marketing department’s shared drives but can access the internet. Which of the following is the most likely cause of this issue?
Which of the following best explains the role of confidentiality with regard to data at rest?
A network administrator installs new cabling to connect new computers and access points. After deploying the equipment, the administrator notices a few of the devices are not connecting properly. The administrator moves the devices to a different port, but it does not resolve the issue. Which of the following should the administrator verify next?
A laptop user gets an error when trying to access the company’s intranet site. A technician runs ipconfig /all with the following results:
Autoconfiguration IPv4 Address: 169.254.0.5 (Preferred)
Subnet Mask: 255.255.0.0
Default Gateway:
DHCP Server:
Which of the following is most likely causing the issue?
Which of the following steps in the troubleshooting methodology would be next after putting preventive measures in place?
 A computer network diagram with many boxes and text AI-generated content may be incorrect.
A computer network diagram with many boxes and text AI-generated content may be incorrect.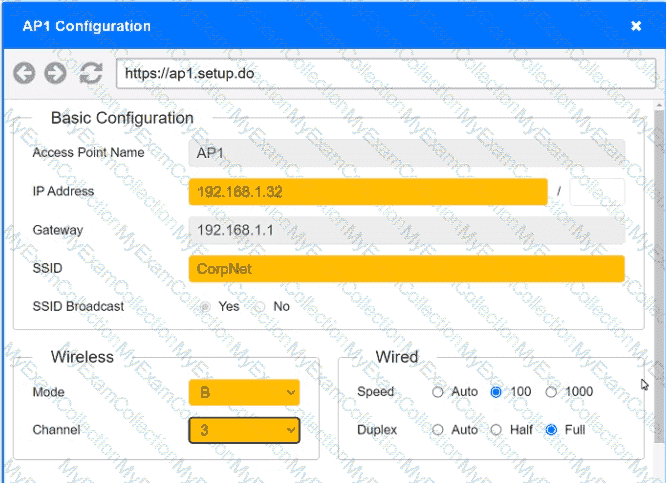 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.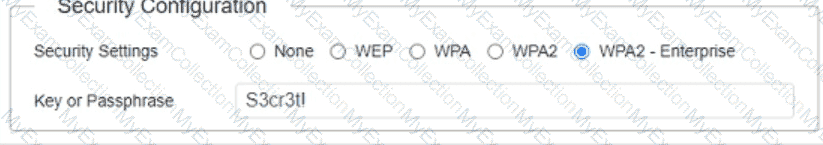 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.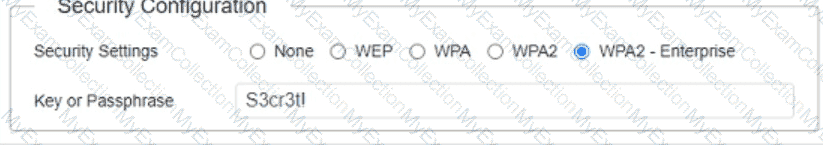 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.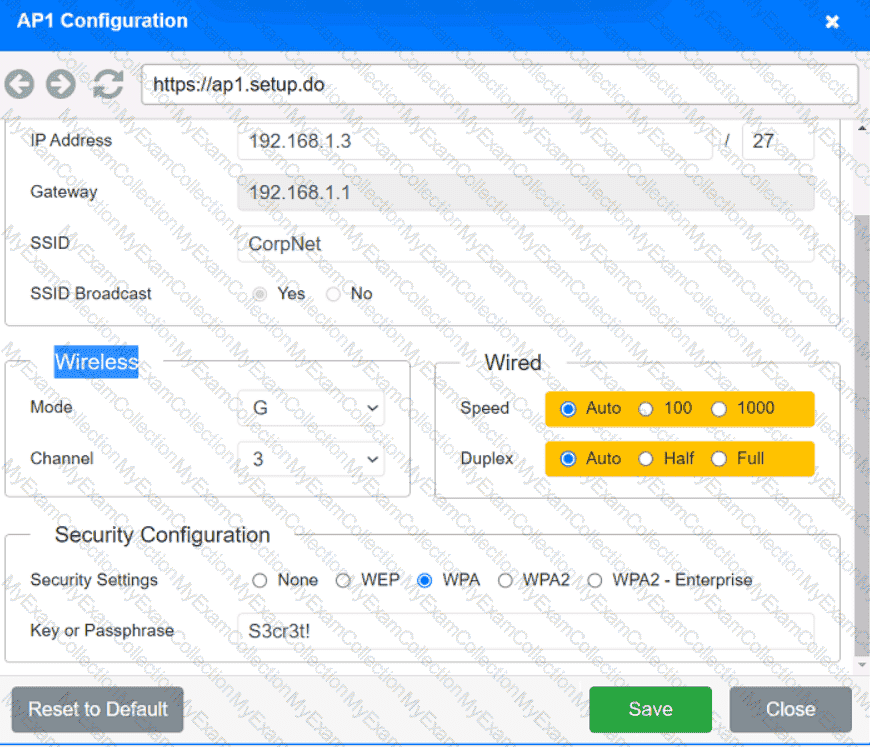 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.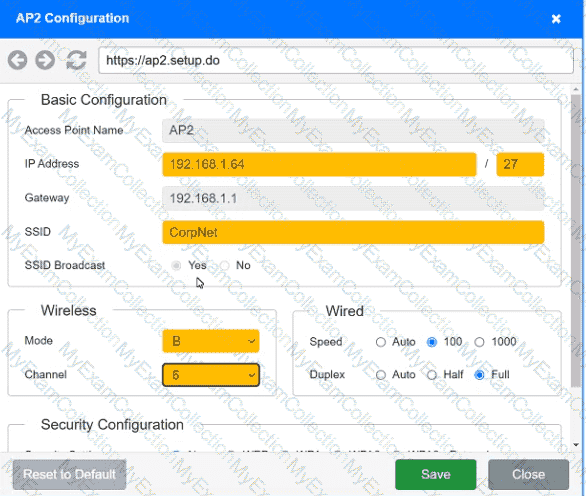 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.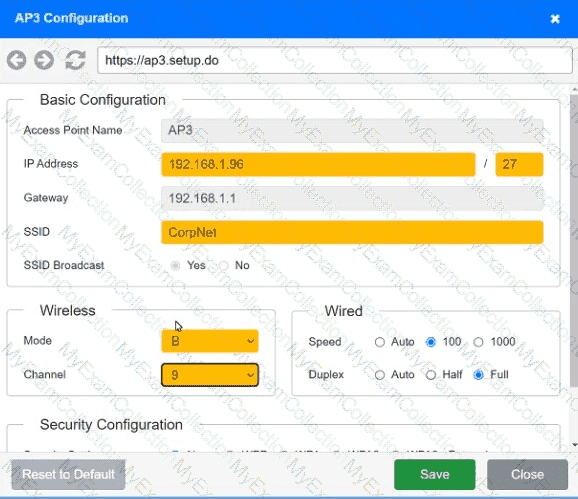 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.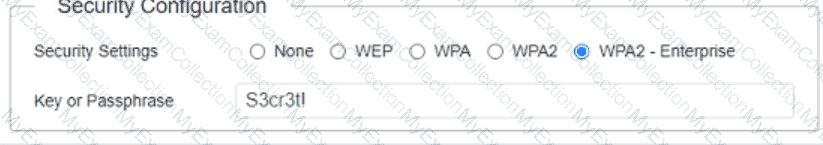 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.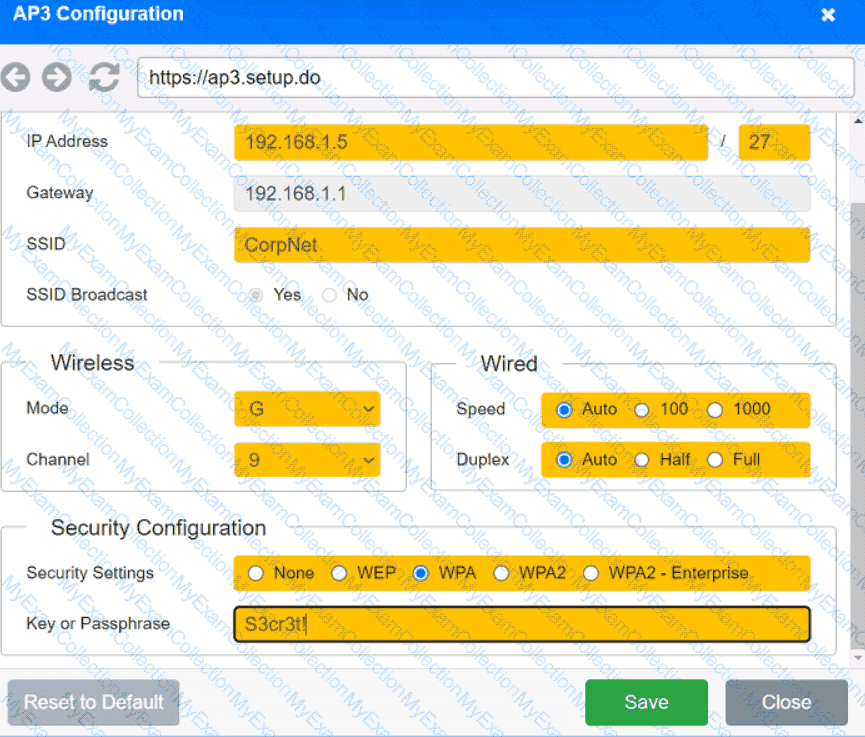 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.
