How are the Routing Engine and the Packet Forwarding Engine components connected?
They use shared memory access.
They use external breakout cables.
They use an MPLS connection.
They use an internal Ethernet link.
Answer:
Explanation:
The fundamental architecture of Junos OS is built upon the clean separation of the Control Plane (Routing Engine or RE) and the Forwarding Plane (Packet Forwarding Engine or PFE). While these two components perform vastly different tasks, they must maintain a high-speed, reliable communication channel to synchronize the state of the device. This connection is achieved through an internal Ethernet link .
This internal link serves several critical functions. First, it allows the Routing Engine to " push " the distilled forwarding table (FIB) to the PFE, ensuring that the hardware knows exactly how to handle incoming transit traffic at wire speed. Second, it acts as a conduit for exception traffic . If the PFE receives a packet that it cannot handle alone—such as an OSPF hello, a BGP update, or an ICMP " Time Exceeded " message—it sends that packet over the internal Ethernet link to the RE for processing. This link is carefully policed by built-in rate limiters to ensure that a flood of transit-related exception traffic cannot overwhelm the Routing Engine ' s CPU, a mechanism known as control plane protection. By using a standard Ethernet-based internal fabric, Junos ensures a scalable and modular design where the RE can focus on complex protocol calculations while the PFE focuses on the heavy lifting of packet switching.
What are two characteristics of IPv6 addressing? (Choose two.)
The IPv6 address is represented by a 128-bit address.
The IPv6 header automatically includes a checksum.
IPv6 uses ARP to discover neighboring devices.
IPv6 addresses that begin with fe80 are not routable.
Answer:
Explanation:
IPv6 introduces several fundamental shifts in networking architecture compared to its predecessor, IPv4. The most prominent characteristic is the address length; IPv6 utilizes a 128-bit address space, represented in hexadecimal notation across eight groups of 16 bits. This massive expansion from IPv4 ' s 32-bit limit was designed to ensure long-term address availability for the global internet and the growing ecosystem of connected devices.
Another defining characteristic of IPv6 is the concept of address scope, particularly regarding link-local addresses . Any IPv6 address beginning with the fe80::/10 prefix is classified as link-local. These addresses are automatically configured on every IPv6-enabled interface and are strictly not routable beyond the local physical or logical link segment. They are essential for local link operations such as neighbor discovery and routing protocol adjacency formation.
Architecturally, IPv6 also improves performance by streamlining the packet header. Unlike IPv4, the IPv6 header does not include a checksum, as modern link-layer (Layer 2) and transport-layer (Layer 4) protocols perform their own error checking, making a redundant header checksum unnecessary at the network layer. Additionally, IPv6 replaces the broadcast-based Address Resolution Protocol (ARP) with the multicast-based Neighbor Discovery Protocol (NDP). Understanding these core traits—massive address length and non-routable link-local scoping—is critical for managing modern Junos-based network infrastructures.
Which two statements about route preference in Junos OS are correct? (Choose two.)
Higher route preference values indicate higher priority.
Route preference is considered after evaluating the longest prefix match.
Lower route preference values indicate higher priority.
Route preference determines the forwarding table size.
Answer:
Explanation:
In Junos OS, route preference (often referred to as administrative distance in other operating systems) is the mechanism used to select the " best " path when the routing table receives multiple advertisements for the exact same destination prefix from different routing sources. The core rule for preference is that lower values indicate a more preferred or " higher priority " route . For example, a direct route has a default preference of 0, a static route is 5, and OSPF internal routes are 10. If a router learns about the same network from both OSPF and a static entry, it will select the static route because 5 is lower than 10.
Crucially, route preference is only evaluated after the longest prefix match (LPM) has been determined. LPM is the absolute first step in packet forwarding; the router will always choose the most specific route available (e.g., a /28 over a /24). Only if there are multiple entries for that same /28 does the router look at preference to break the tie. It is a common misconception that a lower preference value can override a more specific prefix; in reality, a /32 route with a preference of 170 (BGP) will always win over a /24 route with a preference of 5 (Static). Understanding this hierarchy is vital for network architects when designing redundant paths and predictable failover behaviors.
When troubleshooting a problem, you issue the following commands in sequence:
show chassis alarms
show chassis fpc
show chassis fpc detail
show chassis errors fpc-slot 0
In this scenario, what happens when you press the up arrow key twice at the prompt?
The show chassis fpc command is displayed at the prompt.
The show chassis errors fpc-slot 0 command is displayed at the prompt.
The show chassis alarms command is displayed at the prompt.
The show chassis fpc detail command is displayed at the prompt.
Answer:
Explanation:
The Junos OS Command Line Interface (CLI) utilizes an advanced command-line editing environment influenced by standard Emacs and Unix terminal behaviors. One of the most critical features for operational efficiency is the command history buffer. This buffer automatically records a sequence of previously executed commands, allowing administrators to recall, modify, and re-execute them without manual re-entry.
The navigation of this history buffer is strictly chronological and operates as a stack. When the up arrow key is pressed once, the CLI retrieves the most recent command that was successfully entered—in this scenario, show chassis errors fpc-slot 0. Pressing the up arrow key a second time moves the cursor one step further back into the history stack to the command that preceded the most recent one. Following the provided sequence, the command executed prior to the " errors " check was show chassis fpc detail. Consequently, the second press of the up arrow key will display show chassis fpc detail at the prompt. This mechanism is essential for architects during intensive troubleshooting sessions, enabling them to cycle through relevant diagnostic commands rapidly while maintaining focus on the hardware output rather than syntax repetition. Reference: User Interfaces, CLI Editing Features, Command History.
==========
An administrator wants to set up a remote user authentication service for the many users that access a Juniper security device. In this scenario, what are two supported authentication protocols? (Choose two.)
RADIUS
TACACS+
SHA
IPsec
Answer:
Explanation:
For managing high volumes of administrative users, Junos OS supports externalizing the authentication, authorization, and accounting (AAA) process. The two primary industry-standard protocols supported for this purpose are RADIUS (Remote Authentication Dial-In User Service) and TACACS+ (Terminal Access Controller Access-Control System Plus).
Using these protocols allows an architect to maintain a centralized user database on an external server (like Cisco ACS, FreeRADIUS, or Microsoft NPS) rather than configuring every individual user account locally on every Junos device. When a user attempts to log in via SSH or the console, the Junos device acts as a client, forwarding the credentials to the remote server. RADIUS is often preferred for its broad compatibility and efficiency, while TACACS+ is frequently chosen for its ability to separate authentication from authorization and its support for granular command-level accounting. SHA (Secure Hash Algorithm) is a cryptographic hash function used within these processes but is not an authentication protocol itself. Similarly, IPsec is a suite for securing IP communications (VPNs) and is unrelated to the administrative login AAA sequence.
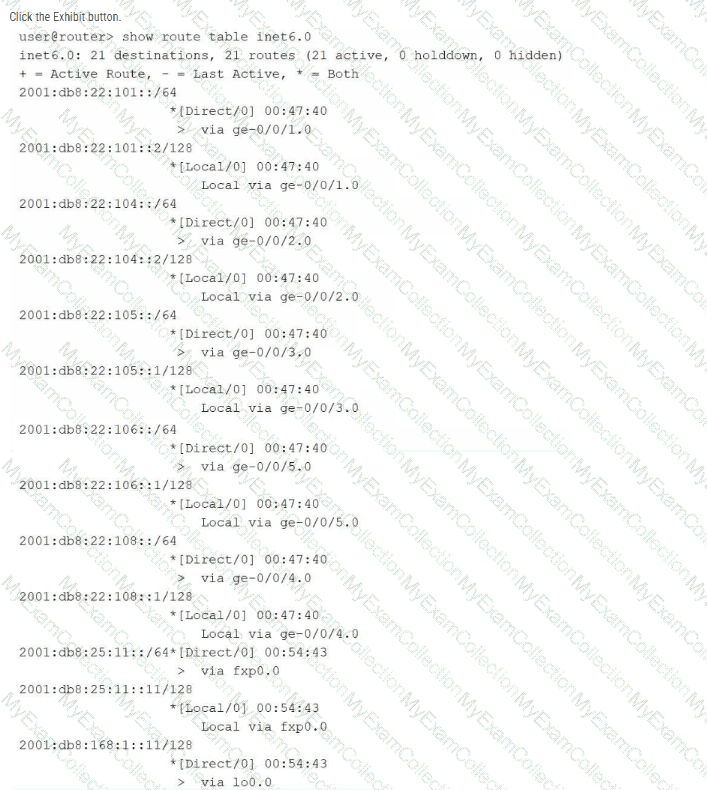
Referring to the exhibit, which two statements about IPv6 routing are correct? (Choose two.)
The router is not learning IPv6 routes from peers.
The router cannot forward traffic to remote IPv6 networks.
Traffic destined for the 2001:db8:22:108::/64 network is forwarded using the ge-0/0/5.0 interface.
The router is connected to the 2001:db8:22:107::/64 network.
Answer:
Explanation:
The provided exhibit displays the output of the show route table inet6.0 command, which represents the master routing table for IPv6 unicast traffic in Junos OS. Analysis of the specific route entries reveals that all listed destinations are categorized as either [Direct/0] or [Local/0] . These route types indicate that the table only contains networks physically connected to the router ' s interfaces and the specific IP addresses assigned to those interfaces.
Because there are no routes identified by dynamic protocols (such as OSPFv3, IS-IS, or BGP) or static entries, it is verified that the router is not learning IPv6 routes from any neighbors or peers. Consequently, the routing table lacks reachability information for any non-local or remote IPv6 segments. Without these routes or a configured default gateway (::/0), the router is unable to forward traffic to remote IPv6 networks. Statements C and D are factually incorrect based on the exhibit: the 2001:db8:22:108::/64 network is associated with interface ge-0/0/4.0 (not ge-0/0/5.0), and the 2001:db8:22:107::/64 network is entirely absent from the displayed routing table.
Which routing table is used for IPv6 unicast routes by default?
inet.0
inet.6
inet.1
inet6.0
Answer:
Explanation:
In Junos OS, routing information is meticulously organized into separate databases known as routing tables, each identified by a specific name corresponding to an address family and its intended operational purpose. The master routing table for IPv4 unicast information is inet.0 . For the IPv6 address family, Junos OS utilizes inet6.0 as the default master routing table for all unicast reachability information. This table stores all IPv6 prefixes learned from directly connected interfaces, static configurations, and dynamic routing protocols such as OSPFv3, IS-IS, or BGP.
It is a core architectural principle in Junos to isolate these families to ensure management clarity and prevent address space collisions. While the system utilizes other specialized tables for specific functions—such as inet.3 for MPLS path information or inet.1 for multicast forwarding caches— inet6.0 remains the primary repository for IPv6-based forwarding decisions. When a Junos device receives an IPv6 packet, the Packet Forwarding Engine (PFE) performs a lookup against the entries derived from this table to determine the appropriate egress interface and next-hop address. Understanding this default table structure is essential for network architects when troubleshooting dual-stack environments or configuring protocol-specific import and export policies.
Exhibit:
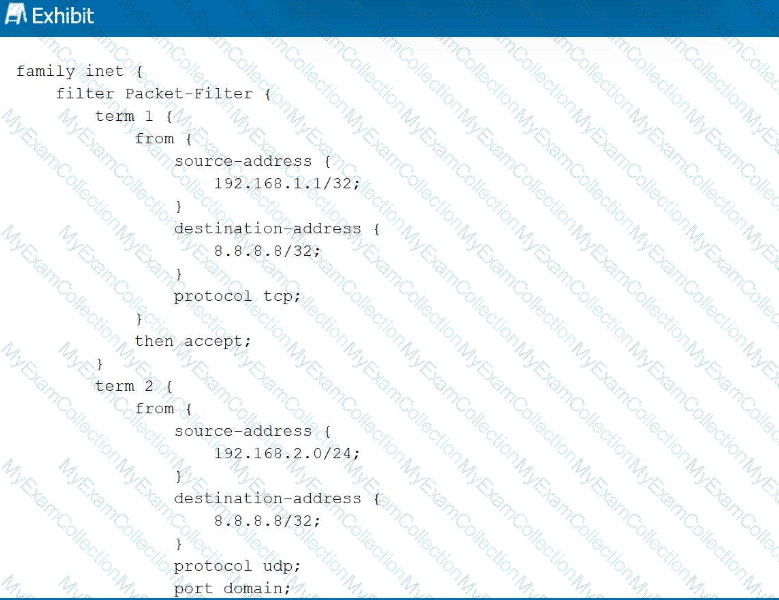
Referring to the exhibit, with firewall filter Packet-Filter attached to an interface, if traffic is sent from 192.168.1.1 to 8.8.8.8 for a UDP DNS query, what will happen to the traffic?
The traffic will match term 1 and be forwarded.
The traffic will match the default last term and be forwarded.
The traffic will match the default last term and be discarded.
The traffic will match term 3 and be forwarded.
Answer:
Explanation:
Junos OS firewall filters operate on a first-match basis, evaluating terms sequentially from top to bottom. In this scenario, a UDP DNS packet (destination port 53) is sent from 192.168.1.1 to 8.8.8.8. Evaluation begins with term 1 , which matches the correct source and destination IP addresses but specifies protocol tcp . Because the actual traffic uses UDP, term 1 is not a match. Evaluation then moves to term 2 . While term 2 correctly identifies protocol udp and port domain (port 53), it requires the source-address to reside within the 192.168.2.0/24 subnet. Since the source is 192.168.1.1 , term 2 also fails to match.
When a packet fails to match any explicitly defined terms in a Junos firewall filter, it is subject to the implicit deny action. This default " last term " is a hardcoded safety mechanism that automatically discards all traffic that has not been explicitly permitted. Consequently, because neither term provides a match for the specific combination of source IP, protocol, and destination port, the DNS query is silently dropped by the Packet Forwarding Engine. This behavior ensures that Junos devices maintain a " deny-by-default " security posture, requiring administrators to define precise permit statements for all required transit or management traffic. Reference: Routing Policy and Firewall Filters, Firewall Filter Evaluation, Implicit Discard.
==========
Which two tasks are performed by the Routing Engine in a Junos device? (Choose two.)
The Routing Engine runs routing protocols.
The Routing Engine evaluates transit traffic against firewall filters.
The Routing Engine manages the device configuration.
The Routing Engine forwards transit traffic.
Answer:
Explanation:
The Routing Engine (RE) functions as the centralized processor and administrative core of any Junos OS-based platform. Its primary responsibility involves the execution and maintenance of the control plane, which includes running all active routing protocols such as OSPF, BGP, and IS-IS. Through these protocols, the RE exchanges topology information with neighboring routers, builds the Routing Information Base (RIB), and calculates the optimal paths for traffic. Once these paths are determined, the RE distributes the resulting Forwarding Information Base (FIB) to the Packet Forwarding Engine (PFE) for hardware-level execution.
In addition to its protocol duties, the Routing Engine manages the device configuration and the overall system environment. This includes providing the user interface (CLI or J-Web), managing the candidate and active configuration databases, and handling the commit process. While the PFE is specifically designed to forward transit traffic and evaluate that traffic against firewall filters at line rate, the RE focuses on the higher-level logic and management tasks. This architectural separation ensures that management functions—such as a complex configuration commit or a protocol re-convergence event—do not degrade the performance of the data plane, allowing the device to continue forwarding user traffic without interruption. Reference: Junos OS Fundamentals, Routing Engine Functions, Management and Control Planes.
==========
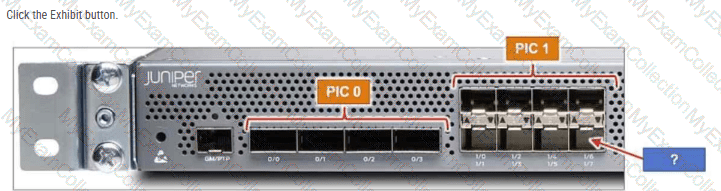
The MX204 has 12 built-in ports. Referring to the exhibit, to which interface does the arrow point?
хе-0/2/7
хе-0/0/7
хе-0/1/7
хе-0/1/6
Answer:
Explanation:
The Juniper MX204 is a fixed-configuration router that utilizes a specific hierarchical naming convention for its physical interfaces: type-fpc/pic/port. In the MX204 architecture, there is a single built-in Flexible PIC Concentrator (FPC), which is always designated as FPC 0 . This FPC is subdivided into two logical Physical Interface Cards (PICs): PIC 0 and PIC 1 .
As shown in the exhibit, PIC 0 contains four high-speed ports (labeled 0/0 through 0/3) that typically support 40GbE or 100GbE speeds. PIC 1 contains eight ports (labeled 1/0 through 1/7) designed for 1GbE or 10GbE connectivity. These ports are arranged in a stacked, $2 \times 4$ grid. The labeling system on the chassis indicates the port numbers for each column. In the fourth column of the PIC 1 block, the top port is identified as 1/6 and the bottom port as 1/7 .
The blue arrow in the exhibit points directly to the bottom-right interface in the PIC 1 section. Correlating this physical location with the chassis labels confirms that the port number is 7. When combined with the FPC and PIC identifiers, the full interface name is xe-0/1/7 (assuming a 10GbE transceiver is installed). Understanding this physical-to-logical mapping is essential for accurate cabling and configuration within the Junos OS, ensuring that administrators apply the correct logical unit and protocol settings to the intended physical hardware.
Which statement describes the purpose of configuring traceoption log files in Junos OS?
The traceoption log files automatically optimize routing decisions based on traffic patterns.
The traceoption log files enable detailed debugging of specific protocols or processes.
The traceoption log files allow permanent storage of all system logs for compliance purposes.
The traceoption log files provide real-time monitoring of interface bandwidth utilization.
Answer:
Explanation:
Traceoptions represent an essential diagnostic facility within Junos OS, primarily used by network engineers for deep-level troubleshooting and protocol analysis. The fundamental purpose of configuring traceoption log files is to enable detailed debugging of specific protocols—such as BGP, OSPF, or IS-IS—or specific system processes like the Routing Protocol Process (rpd). When enabled, the system captures detailed information about the internal operations of the protocol, including the exchange of packets, state machine transitions, and error conditions, writing this data to a dedicated file in the /var/log directory.
Unlike standard system logging (syslog), which captures high-level events and warnings, traceoptions provide a granular, " behind-the-scenes " view of how a protocol is interacting with its neighbors. This is particularly useful for identifying the root cause of complex adjacency issues or route instability that standard show commands may not reveal. However, because tracing can be resource-intensive, it is typically configured with specific flags to limit the output to relevant events and is disabled once the troubleshooting task is complete. Traceoptions do not serve to optimize routing automatically , nor are they intended for permanent compliance storage or simple bandwidth monitoring. Instead, they remain the premier tool for clinical debugging and protocol verification within the Junos environment. Reference: Operational Monitoring and Maintenance, Troubleshooting Tools and Traceoptions.
==========
Which two statements are correct about logical units? (Choose two.)
A physical interface can host multiple logical units.
Logical units can have multiple IP addresses.
Logical units are used only for management interfaces.
A physical interface can host only one logical unit.
Answer:
Explanation:
In the Junos OS architecture, interfaces are strictly divided into physical and logical components. The physical interface represents the actual hardware port (e.g., ge-0/0/0), while logical units (e.g., ge-0/0/0.0) define the protocol-specific parameters and logical segmentation required for traffic processing. A fundamental characteristic of this model is that a single physical interface can host multiple logical units. This is a mandatory requirement for technologies such as 802.1Q VLAN tagging, where each logical unit corresponds to a different VLAN ID on the same physical link, allowing for efficient micro-segmentation of traffic.
Furthermore, Junos OS allows logical units to have multiple IP addresses assigned to them within the same address family or across different families (such as inet and inet6). This flexibility enables a single logical interface to reside on multiple subnets simultaneously, which is essential for complex routing scenarios, multi-homing, or transitional dual-stack environments. It is a common misconception that logical units are reserved for management; in reality, every physical interface must have at least one logical unit (typically unit 0) configured for the device to process any transit or local traffic. Understanding the hierarchical relationship between the physical port and its logical subdivisions is critical for successful interface management and protocol deployment on Junos platforms. Reference: Junos OS Fundamentals, Interface Naming and Hierarchy.
==========
Your routing policy has three terms. A route matches the first term with an accept action. In this scenario, what happens next?
The route is rejected by default.
The route is evaluated by the second term.
The route is sent to the next policy chain.
The route is accepted and no further terms are evaluated.
Answer:
Explanation:
Junos OS routing policies are evaluated using a sequential, " first-match " logic. When a route is compared against a policy, the system evaluates the terms in the order they are defined. Once a route meets all the match criteria (the from statement) in a term, the router executes the associated action (the then statement).
If the action is a terminating action —such as accept or reject—the evaluation of that specific route for that specific policy ends immediately. In this scenario, since the route matched the first term and the action was accept, the route is successfully processed and the policy evaluation is complete. The system will not proceed to evaluate the second or third terms. This behavior is critical for network architects to understand when ordering terms; more specific " exceptions " must be placed at the top of the policy, while broader " catch-all " terms must be placed at the bottom. If the administrator wanted the evaluation to continue to the next term despite a match, they would need to explicitly include the next term action, which is a non-terminating action. Without it, a match on an accept action signifies the final decision for that route within that policy context.
You committed a new configuration on a Junos router, but users report connectivity issues. You must quickly restore the previous working configuration without manually editing the candidate configuration. Which command should you use to load the required configuration into the candidate configuration?
rollback 0
show | compare rollback
rollback 1
load override
Answer:
Explanation:
In Junos OS, the configuration database is designed with a robust versioning system that facilitates rapid recovery from administrative errors. Every time a commit command is successfully executed, the system automatically archives the previous active configuration and assigns it a " rollback " index. The rollback command is used within configuration mode to revert the candidate configuration to a previously saved state.
The indices are zero-based, where rollback 0 represents the currently active configuration that was just committed. To restore the configuration that was functional immediately before the most recent, problematic commit, the administrator must use rollback 1. This command replaces the current candidate configuration with the contents of the last known working state. It is important to note that executing rollback 1 only populates the candidate buffer; to make this previous configuration active and restore connectivity, the administrator must subsequently issue the commit command. This mechanism is a cornerstone of Junos OS ' s commitment to high availability and operational resilience, allowing for nearly instantaneous restoration of services without the need for manual line-by-line configuration edits during a network outage.
According to HPE Juniper Networking, what are two recommended tasks you should perform before upgrading Junos OS on a device? (Choose two.)
Delete all rollback configurations.
Verify available storage space using the show system storage command.
Disable all interfaces to prevent traffic during the upgrade.
Back up the active current configuration.
Answer:
Explanation:
Upgrading the Junos OS is a high-impact operation that requires thorough preparation to minimize risk and potential downtime. According to Juniper ' s best practices, one of the most critical preliminary steps is to verify that the device has sufficient available storage space. Using the show system storage command, an administrator can inspect the /var partition, which is the primary directory where software packages are temporarily stored and expanded during the installation process. If the storage is nearly full, the upgrade may fail midway, potentially leaving the device in an inconsistent state or requiring manual intervention via the boot loader.
The second mandatory task is to back up the active configuration . While Junos automatically maintains rollback files locally, these could be lost if the storage media fails or if a " clean install " (format install) becomes necessary. Having an external backup on a remote server or a local workstation ensures that the device ' s identity, policies, and interface settings can be restored quickly regardless of the upgrade outcome. Other tasks, such as creating a rescue configuration or performing a file system cleanup, are also highly recommended to ensure the " last known good " state is preserved. Disabling interfaces is generally unnecessary as Junos manages the transition gracefully, and deleting rollbacks would counterproductively remove historical recovery points. Ensuring these two pillars—storage availability and off-box backups—provides the safest foundation for a successful software lifecycle management event.
Which statement is correct when Router R1 receives a packet from User A destined for User B as shown in the exhibit?

Router R1 replaces the destination IP address in the packet with the IP address of Router R2.
Router R1 leaves the packet unchanged.
Router R1 replaces the destination MAC address in the packet with the MAC address of Router R2.
Router R1 replaces the destination MAC address in the packet with the MAC address of User B.
Answer:
Explanation:
Comprehensive and Detailed 150 to 250 words of Explanation From: In a routed environment like the one shown in the exhibit, traffic forwarding involves a constant interaction between Layer 3 (Network) and Layer 2 (Data Link) addressing. When User A generates a packet destined for User B, the source and destination IP addresses remain static throughout the entire journey across the network (assuming no Network Address Translation is performed). However, the Layer 2 Ethernet headers must be rewritten at every hop because MAC addresses have only local significance on a physical segment.
As Router R1 receives the packet from User A, it performs a lookup in its Forwarding Information Base (FIB) and identifies that the path to User B requires forwarding the packet to Router R2. R1 decapsulates the incoming frame, stripping away the original Ethernet header that contained User A ' s source MAC and R1 ' s own destination MAC. To forward the packet to the next hop, R1 creates a new Ethernet header. The source MAC address becomes the MAC address of R1’s egress interface, and the destination MAC address is replaced with the MAC address of Router R2 . R1 cannot use User B ' s MAC address at this point because User B is not on a directly connected segment. This hop-by-hop MAC address replacement is essential for the Packet Forwarding Engine to successfully deliver the frame to the next Layer 3 device in the path. Reference: Networking Fundamentals, Packet Forwarding, Layer 2 and Layer 3 Addressing.
Which two statements about prefix lists in Junos are correct? (Choose two.)
Prefix lists can be re-used in multiple routing policies.
Prefix lists can be used in both firewall filters and routing policies.
Prefix lists cannot be used in routing policies.
Prefix lists cannot be used in firewall filters.
Answer:
Explanation:
Prefix lists in Junos OS are named collections of IP addresses or network prefixes defined under the [edit policy-options] hierarchy. One of their most powerful features is their versatility and reusability. Because they are defined as independent objects, a single prefix list can be referenced in multiple different routing policies across the device. This modularity ensures consistency; for instance, if a set of " internal " prefixes changes, an administrator only needs to update the list in one location for those changes to propagate to every policy that utilizes it.
Furthermore, prefix lists are designed to be used across different functional areas of the Junos architecture. They are equally valid for use in routing policies (to control the import or export of routes between protocols like BGP or OSPF) and in firewall filters (to match source or destination addresses for transit or management traffic). When used in a routing policy, the prefix list typically performs an exact match on the prefix length unless modified by a match type like orlonger. In a firewall filter, it acts as a high-speed lookup table for the Packet Forwarding Engine. This dual-purpose capability makes prefix lists a foundational tool for architects seeking to implement scalable, automated security and routing logic within a unified configuration framework.
You are creating a new user account on your Junos device. The user must be able to validate the routing table and interface statistics but should not be able to make any configuration changes. In this scenario, which permission flag would satisfy this requirement?
configure
all
view
network
Answer:
Explanation:
User access control in Junos OS is managed through the application of permission flags within login classes. When an architect needs to define a role that allows for robust monitoring and troubleshooting without granting authority to alter the device ' s operational state, the view permission flag is the appropriate selection. This flag grants the user the ability to execute the majority of show commands in operational mode, which includes viewing the routing table, inspecting interface statistics, and checking hardware status.
The view permission is specifically designed for " read-only " access. It ensures that the user can observe all necessary telemetry data to validate network health—satisfying the requirement to check routing and interface stats—while strictly prohibiting access to configuration mode or any set commands. This contrasts with the configure flag, which allows modification of the candidate configuration, or the network flag, which provides specific permissions related to network-level operational tasks. By assigning a user to a class restricted with the view flag, an administrator maintains a secure environment where support personnel can diagnose issues without the risk of accidental or unauthorized configuration changes. This principle of least privilege is a cornerstone of Junos security management. Reference: User Interfaces, User Management and Access Control.
==========
Click the Exhibit button.
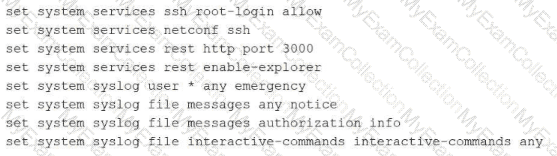
Which command displays the output in the format shown in the exhibit?
show configuration | display inheritance
show configuration | display set
show configuration
show configuration | display detail
Answer:
Explanation:
The exhibit illustrates a Junos configuration rendered as a sequence of flat, executable lines that each begin with the set keyword. This is commonly referred to as the " set format. " By default, Junos OS displays the configuration in a hierarchical, brace-delimited format (often called " staza " or " curly brace " format). While the default format is excellent for visualizing the structural relationship between different configuration objects, the set format is often preferred for documentation, scripting, or copying specific configuration snippets between different devices.
To produce the output seen in the exhibit, an administrator must append the pipe filter | display set to the show configuration command. This filter instructs the CLI parser to flatten the hierarchical structure and prepend the necessary context to every individual leaf statement. These lines are highly functional because they can be pasted directly into the CLI of another device while in configuration mode to recreate the exact settings. In contrast, display inheritance is used to reveal hidden settings applied via configuration groups, and display detail provides additional technical metadata about the objects. Neither of those options would transform the output into the discrete set command lines shown in the exhibit. Understanding how to toggle between these display formats is a fundamental skill for any architect managing Junos infrastructures through the Command Line Interface.
Which two characteristics apply to TCP? (Choose two.)
TCP guarantees fixed latency for application flows.
TCP broadcasts datagrams by default on Ethernet.
TCP uses a three-way handshake to establish a connection.
TCP provides reliable, ordered delivery using sequence numbers.
Answer:
Explanation:
Comprehensive and Detailed 150 to 250 words of Explanation From: The Transmission Control Protocol (TCP) is a core transport-layer protocol within the TCP/IP suite designed to provide a highly reliable, connection-oriented service. Unlike the User Datagram Protocol (UDP), which is connectionless and best-effort, TCP ensures that data is delivered accurately and in the correct order. A defining characteristic of TCP is its use of a three-way handshake to establish a session. This process involves the exchange of SYN, SYN-ACK, and ACK segments, which synchronizes sequence numbers between the two endpoints and ensures both hosts are ready for data transfer.
Furthermore, TCP provides reliable, ordered delivery by utilizing sequence numbers and acknowledgments. Each data segment is assigned a sequence number; the receiving host uses these numbers to reassemble the data in its original order, even if segments arrive out of sequence due to network jitter or multiple paths. If a segment is lost, the lack of a timely acknowledgment triggers a retransmission, guaranteeing that the application receives all data. TCP does not provide fixed latency guarantees, as its error-recovery mechanisms can introduce delays. Additionally, TCP is a unicast-only protocol and does not support broadcasting on Ethernet. Reference: Networking Fundamentals, Transport Layer Protocols, TCP vs. UDP.
==========
Which two statements are correct regarding Layer 2 network switches? (Choose two.)
Switches are susceptible to traffic loops.
Switches flood broadcast traffic.
Switches do not learn MAC addresses.
Switches create a single collision domain.
Answer:
Explanation:
In the Junos OS architecture and general networking standards, Layer 2 switches are designed to increase network efficiency by segmenting collision domains. Unlike legacy hubs, a switch creates a separate collision domain for each of its physical ports. This micro-segmentation allows for full-duplex communication, effectively eliminating the possibility of collisions on individual links. However, while switches segment collision domains, they maintain a single broadcast domain by default.
When a switch receives a broadcast frame, such as an ARP request, it must ensure the frame reaches all possible destinations within the local segment. Consequently, the switch floods the broadcast traffic out of all ports except the one on which it was received. This flooding behavior, while necessary for protocol discovery, makes Layer 2 networks susceptible to traffic loops. If redundant physical paths exist between switches without a loop-prevention mechanism like the Spanning Tree Protocol (STP), broadcast frames can circulate endlessly, leading to a broadcast storm that consumes all available bandwidth and processor resources on the Routing Engine. Furthermore, switches are highly active learners; they populate their Media Access Control (MAC) tables by observing the source addresses of incoming frames to ensure that subsequent unicast traffic is precisely forwarded rather than flooded. Therefore, understanding the management of broadcast domains and the risks of loops is a core competency for any Junos Associate.
Which two statements about firewall filters are correct? (Choose two.)
Firewall filters are stateful.
Firewall filters can match Layer 4 parameters.
Firewall filters can match Layer 7 parameters.
Firewall filters are stateless.
Answer:
Explanation:
In Junos OS, standard firewall filters operate as a primary security and traffic management tool within the forwarding plane. These filters are fundamentally stateless, meaning they evaluate each packet individually and in isolation without maintaining a session table or tracking the state of network connections. This stateless nature allows the Packet Forwarding Engine (PFE) to process filters at hardware speeds, ensuring minimal latency for transit traffic. This distinguishes them from the stateful security policies found on Junos security devices like the SRX Series, which track the entire lifecycle of a flow.
Furthermore, firewall filters are designed to inspect and match header information up to Layer 4 of the OSI model. This capability allows administrators to define terms based on parameters such as source and destination IP addresses (Layer 3) as well as TCP or UDP port numbers and protocol types (Layer 4). While they provide granular control over packet flow, they do not natively inspect Layer 7 application payloads, which is typically reserved for advanced services like Intrusion Detection and Prevention (IDP). By combining stateless execution with Layer 4 matching, Junos firewall filters provide an efficient method for implementing transit protection, rate limiting through policing, and protecting the local Routing Engine through loopback interface filtering. Reference: Routing Policy and Firewall Filters, Firewall Filter Framework.
==========
Which two actions would you perform when you are in the operational mode of the CLI? (Choose two.)
Clear the log files.
Commit the configuration.
Reboot the device.
Configure routing protocols.
Answer:
Explanation:
The Junos Command Line Interface (CLI) is strictly partitioned into operational and configuration modes to maintain a clear boundary between monitoring and administrative changes. Operational mode, identified by the > prompt, is designed for executing commands that monitor device status, troubleshoot network connectivity, and manage the physical system state. One typical administrative task performed here is clearing log files (using the clear log command) to free up storage space or reset diagnostic data during troubleshooting.
Additionally, high-level system requests that do not alter the persistent configuration database, such as rebooting the hardware, are executed in operational mode. The request system reboot command allows the administrator to gracefully restart the device after a software update or as part of a maintenance cycle. In contrast, actions such as configuring routing protocols or committing changes require transitioning to configuration mode (the # prompt). Committing a configuration is the specific act of moving changes from the candidate database to the active database, which is a logic-altering event strictly reserved for configuration mode. Therefore, operational mode remains the dedicated environment for real-time observation and system-level requests that ensure the device operates correctly within its existing parameters. Reference: User Interfaces, CLI Modes, Operational Mode Commands.
==========
Which two statements are correct about a Routing Engine? (Choose two.)
It processes management traffic.
It processes CoS marked traffic.
It forwards transit traffic.
It maintains routing tables.
Answer:
Explanation:
The architecture of a Junos device is bifurcated into two primary functional planes: the Control Plane, managed by the Routing Engine (RE), and the Data Plane, managed by the Packet Forwarding Engine (PFE). The Routing Engine serves as the " brain " of the device. One of its primary responsibilities is the processing of management traffic, which includes handling CLI sessions (SSH, Telnet), SNMP requests, and system logging. Because the RE runs the Junos OS kernel, it provides the environment for all administrative tasks and system management utilities.
Additionally, the Routing Engine is responsible for the intelligence of the network, which involves running routing protocols (such as OSPF, BGP, or IS-IS) and maintaining the master routing tables. It populates the Routing Information Base (RIB) with all learned paths and then calculates the best paths to build the Forwarding Information Base (FIB). This FIB is then pushed to the PFE for hardware-level packet switching. It is a common misconception that the RE handles transit traffic; however, the RE only handles " exception traffic " or traffic destined for the device itself. This separation ensures that the control plane remains stable and responsive even during periods of heavy transit load on the forwarding plane. Reference: Junos OS Fundamentals, Architectural Overview, Control Plane vs. Forwarding Plane.
What does the user@router > clear log ospf-trace command accomplish?
The ospf-trace file is deleted.
Trace parameters are removed from the OSPF protocol configuration.
Logging data into ospf-trace is stopped.
Data in the ospf-trace file is removed and logging continues.
Answer:
Explanation:
The clear log command is a vital operational utility within the Junos OS used to manage the size and relevance of log files without interrupting the system ' s logging processes. When a Senior Architect executes the clear log ospf-trace command, the Junos kernel truncates the specified file, effectively removing all existing text and resetting the file size to zero bytes. Crucially, the file itself is not deleted from the /var/log directory, nor is the underlying traceoptions configuration modified in any way.
Because tracing is often used for real-time debugging of protocol behaviors like OSPF, trace files can rapidly grow to several megabytes, making it difficult to find specific events. By clearing the log, the administrator ensures that any subsequent OSPF events—such as adjacency changes, LSA flooding, or SPF calculations—are recorded at the very beginning of the file, free from historical clutter. The OSPF process (rpd) continues to write to the file immediately after the truncation occurs. This operational behavior distinguishes the clear command from the file delete command, which would remove the file entirely, or the set protocols ospf traceoptions configuration command, which defines which specific events the device should record. Utilizing clear log is a standard best practice during intensive troubleshooting sessions to maintain a clean and chronologically relevant diagnostic environment.

