Which of the following is not a direct benefit of control self-assessment (CSA)?
Senior management requested that the internal audit activity perform a consulting project to assist in making a decision on a new software system. Which of the following would be used to determine the engagement objectives?
Which type of engagement would be the most appropriate to assess the maturity and rigor of the organizationwide risk management process of a target entity that
management is considering acquiring?
An internal auditor reviewed bank reconciliations prepared by management of the area under review. The auditor noted that the bank statements attached did not have the
bank heading, logo, or address. Which of the following statements is true regarding this situation?
The internal audit activity is responsible for which of the following actions related to an organization’s internal controls9
An internal auditor is conducting a review of the procurement function and uncovers a potential conflict of interest between the chief operating officer and a significant supplier of IT software development services. Which of the following actions is most appropriate for the internal auditor to take?
A chief audit executive (CAE) following up on action plans from previously completed audits identifies that management has determined that certain action plans are no longer necessary If the CAE disagrees with managements decision, which of the following is the most appropriate next step for the CAE to take?
Which statement best describes the benefit of using workpapers from recent internal audit engagements of the area under review to plan new engagements?
The internal audit activity plans to assess the effectiveness of management's self-assessment activities regarding the risk management process. Which of the following procedures would be most appropriate to accomplish this objective?
A corporate merger decision prompts the chief audit executive (CAE) lo propose interim changes to the existing annual audit plan to account for emerging risks Which of the following is the most appropriate action for the CAE to take regarding the changes made to the audit plan''
The internal audit function is performing an assurance engagement on the organization’s environmental, social, and governance (ESG) program. The engagement objective is to determine whether the ESG program’s activities are meeting the program’s established goals. The internal audit function has completed a risk and control assessment of the ESG program's activities. What is the appropriate next step?
The internal audit activity of an insurance company is reviewing six of the company’s 11 branches. During the review of the fourth branch that was selected, the internal audit team discovered control breaches that could result in regulatory sanctions if not addressed. How should the internal audit team proceed?
According to IIA guidance, which of the following procedures would be least effective in managing the risk of payroll fraud?
Which of the following statements accurately describes the Standards requirement for ret internal audit records?
Acceding to IIA guidance, when of the Mowing is an assurance service commonly performed by the internal audit activity?
When reviewing workpapers, engagement supervisors may ask for additional evidence or clarification via review notes. According to IIA guidance, which of the following statements is true regarding the engagement supervisor’s review notes?
According to IIA guidance, organizations have the most influence on which element of fraud?
An internal auditor wanted to determine whether the organization's 200 employees are charging their work hours accurately to the correct project. The internal auditor selected a sample of 30 employee time reports for testing. Based on the testing, the internal auditor determined the following:
- 5 Time reports were incorrect.
- 21 Time reports were correct.
- 4 Time reports were not supported.
An internal auditor suspects that a program contains unauthorized code or errors. Which of the following would assist the internal auditor in this regard?
An internal auditor e assessing the design of a control and has identified a potential significant weakness. The auditor shared his concern with management however management does not agree that the weakness is significant. What should the internet auditor do next?
Which of the following computerized audit tools or techniques should be used if the internal auditor wants to extract specific files and records in the database?
Which of the following is most appropriate for internal auditors to do during the internal audit recommendations monitoring process?
According to IIA guidance, which of the following statements is true regarding engagement planning?
The internal audit manager has been delegated the task of preparing the annual internal audit plan for the forthcoming fiscal year All engagements should be appropriately categorized and presented to the chief audit executive for review Which of the following would most likely be classified as a consulting engagement?
An internal auditor is preparing for an auditor of newly implemented software that is used by 3,000 employees in South America and Europe. What would be the best way for the auditor to gather relevant feedback?
To which of the following aspects should the chief audit executive give the most consideration while communicating an identified unacceptable risk to management?
During the planning phase of an assurance engagement, which of the following would an internal auditor use to assess and present the severity of the impact of identified risks?
Which of the following would most likely form part of the engagement scope?
A team of internal auditors is assigned to audit the employee relations process in an organization, which includes employee conduct and disciplinary hearings. Which of the following audit approaches would provide the auditors with the best evidence to determine the degree to which disciplinary decisions are complying with documented policy?
An internal auditor finds inconsistencies in a risk area that needs immediate attention. Which of the following actions is most appropriate for the auditor?
Flowcharts are useful during audit planning because they contain information that may help internal auditors with which of the following?
Which of the following is true regarding the monitoring of internal audit activities?
During the planning process for a human resources audit, an internal auditor obtains an organizational chart. The auditor observes a flat organizational structure. Which of the below risks should the auditor consider for this engagement?
Which of the following actions should the chief audit executive take when senior management decides to accept risks by choosing to do business with a questionable vendor?
During an audit of the accounts payable process, an internal auditor was assigned to confirm the quantity of goods received on receiving documents to invoices for those goods and subsequent postings in the accounting system. Which of the following procedures would be most appropriate for this test?
Which of the following best describes why an internal audit activity would consider sending written preliminary observations to the audit client?
According to IIA guidance, which of the following statements is true regarding due professional care?
An internal auditor is conducting a preliminary survey of the investments area, and sends an internal control questionnaire to the management of the function. (An extract of the survey is provided below).
1. Are there any restrictions for any company's investments?
2. Are there any written policies and procedures that document the flow of investment processing?
3. Are investment purchases recorded in the general ledger on the date traded?
4. Is the documentation easily accessible to an persons who need in to perform their job?
Which of the following is a drawback of testing methods like this?
A regional entertainment organization is in the process of developing a corporate social responsibility (CSR) policy. Management invites ideas from employees when developing the CSR policy Which of the following is the most appropriate idea to include?
An internal auditor wants to determine if employees spend more than their approved daily stipend for meals. Which technique would be most appropriate to identify meal expenses that exceed the approved threshold?
Which of the following is most likely to impair the organizational independence of the internal audit activity?
An internal auditor is assessing whether a vendor onboarding procedure is being followed in all business units. The procedure has been centrally designed and depicts activities and validations that must be performed at every step. Which of the following is the most suitable way to compile an internal control questionnaire?
An internal auditor uses a data query tool in the purchasing process to review the vendor master file for authorizations Which of the following describes the control objective likely being tested?
In preparing the engagement work program, which of the following is generally true with respect to secondary controls?
In which of the following situations would it be most appropriate for an internal audit function to issue an interim report or memo?
Where should internal auditor focus their attention when identify and assessing key risks during the planning stage of an assurance engagement?
Which of the following is an advantage of nonstatistical sampling over statistical sampling?
Which of the following resources would be most effective for an organization that would like to improve how it informs stakeholders of its social responsibility performance?
Which of the following is the advantage of using internal control questionnaires (ICQs) as part of a preliminary survey for an engagement?
Two internal auditors are conducting an audit engagement concerning derivatives. The auditors meet with the organization's head of accounting. The head of accounting later complains to the chief audit executive (CAE) that it took hours for the auditors to understand basic derivatives concepts and how derivatives are typically recorded in bookkeeping. What should the CAE have considered more thoroughly?
Which of the following is an advantage of utilizing an external fraud specialist in a suspected fraud investigation?
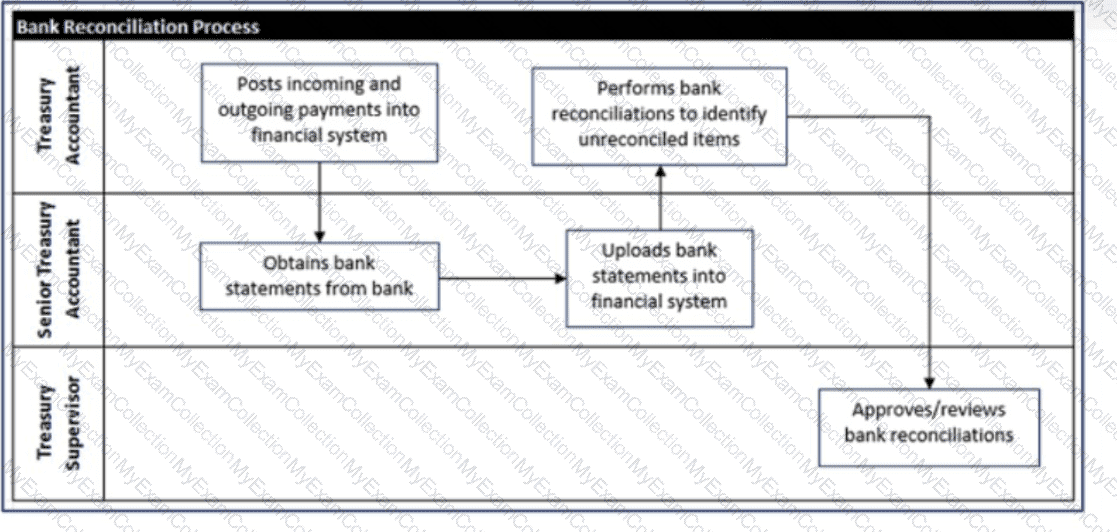
Below is a flowchart detailing an organization's bank reconciliation process. Which of the following conclusions can be drawn from the flowchart?
Which of the following best demonstrates internal auditors performing their work with proficiency?
An internal auditor wants to compare performance information from one quarter to another. Which analytics procedure would the auditor use?
According to IIA guidance, which of the following activities are typically primary objectives of engagement supervision?
Which of the following should an internal auditor document to support an assurance engagement’s conclusions?
Some lime after the final audit report was issued, the engagement supervisor teamed that several internal control deficiencies were not remedied, despite management's previous agreement to remedy them According to IIA guidance, which of the following is the most appropriate response'5
A corporate merger decision prompts the chief audit executive (CAE) to propose interm changes to the existing annual audit plan to account for emerging risks Which of the following Is the most appropriate action for the CAE to take regarding the changes made to the audit plan?
Which of the following statements concerning workpapers is the most accurate?
An internal auditor discovered that equipment used to monitor air quality was not maintained according to the established maintenance schedule. If the issue is not addressed, the equipment may not provide accurate information on pollutant levels, which could result in regulatory sanctions and reputational damage. The auditor discussed the issue with both the manager in charge and the CEO, who explained that they understand the risk, but it has become too expensive to maintain the equipment as scheduled. In this situation, what should the chief audit executive do?
Which of the following processes does the board manage to ensure adequate governance?
Which method of examining entity-level controls involves gathering information from work groups that represent different levels in an organization?
According to IIA guidance, which of the following statements about analytical procedures is true?
With regard to project management, which of the following statements about project crashing is true?
The internal audit activity is asked to review the effectiveness of controls around the disposal of chemical waste. However, the internal auditors on staff lack the necessary skills to conduct this review Which of the following would be the most appropriate approach?
An organization's board would like to establish a formal risk management function and has asked the chief audit executive (CAE) to be involved in the process. According to IIA guidance, which of the following roles should the CAE not undertake?
Which of the following statements is true regarding the final assurance engagement report issued to management?
Which of the following is true regarding the communication of engagement results with stakeholders?
Which of the following is applicable to both a job order cost system and a process cost system'?
Which of the following internal control attributes should internal auditors consider testing during a review of the board of directors?
Which of the following is one of the five attributes that internal auditors include when documenting a deficiency?
According to the IIA guidance, which of the following foes the engagement work test in a review in a review of an organization al process?
In which of the following situations has an internal audit of obtained physical evidence?
Which of the following is an example of a compliance assurance engagement?
An organization is expanding into a new line of business selling natural gas. The internal auditor is planning an engagement and wants to obtain a general understanding of the natural gas market the market share that the organization wants to win, and the competitive advantage that the organization may have. Which of the following would be the best source of such information?
Which of the following is the best option for the chief audit executive to consider for effective coordination of assurance coverage?
Which of the following represents a ratio that measures short term debt-paying ability?
Which of the following statements about including consulting engagements in the annual internal audit plan is true?
Which of the following is an inherent risk of issuing an opinion on the overall effectiveness of internal control?
When setting the scope for the identification and assessment of key risks and controls in a process, which of the following would be the least appropriate approach?
Evidence discovered during the course of an engagement suggests that multiple incidents of fraud have occurred. There do not appear to be sufficient controls in place to prevent reoccurrence. Which of the following is the internal auditor's most appropriate next step?
Which of the following conditions are necessary for successful change management?
1. Decisions and necessary actions are taken promptly.
2. The traditions of the organization are respected.
3. Changes result in improvement or reform.
4. Internal and external communications are controlled.
During a previous audit engagement, an internal auditor recommended that management implement a whistleblowing process. During follow-up, the auditor discovered that the process has been outsourced. Which of the following is the most appropriate response for the internal auditor?
Which of the following is the next step in understanding a business process once an internal auditor has identified the process?
Which of the following evaluation criteria would be the most useful to help the chief audit executive determine whether an external service provider possesses the knowledge, skills, and other competencies needed to perform a review?
Which type of assurance engagement is conducted to determine whether a process or area is performing as intended, accomplishing its objectives, and doing so in an efficient and economical way?
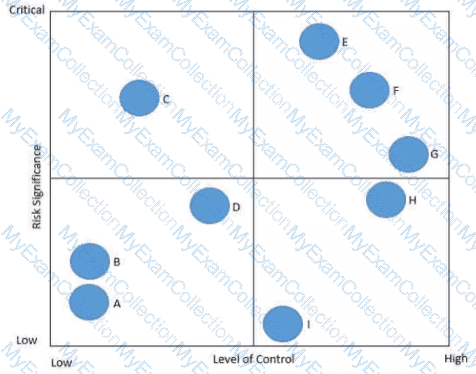
In the following risk control map risks have been categorized based on the level of significance and the associated level of control. Which of the following statements is true regarding Risk C?
An audit reveals that a manager's spouse is receiving paychecks, but is not employed by the organization. According to IIA guidance, which of the following actions should the internal auditor take?
Which of the following is the primary purpose of implementing a program whereby employees are rotated from other parts of the organization into the internal audit activity?
Which of the following best describes the risk contained in an initial public offering for a new stock?
Which of the following is the most important determinant of the objectives and scope of assurance engagements?
The organizational chart, business objectives, and policies and procedures of the area to be reviewed
The only internal auditor, who was part of a larger team of individuals trained in the testing and reading of the organization’s quality control equipment, has resigned. With a scheduled audit of the quality department not yet completed for this year, what alternative approach should the internal audit function take in this scenario?
According to IIA guidance, which of the following activities are typically primary objectives of engagement supervision?
Internal audit staff lacks the expertise to perform a fraud investigation engagement stemming from a whistleblowing incident. Which of the following is the most appropriate
option for the chief audit executive?
Which of the following would help the internal audit activity assess compliance with the organization's standard operating procedures for bank deposits during a preliminary survey?
Upon concluding the engagement fieldwork an internal auditor discusses the audit findings with operational management There is a greater likelihood that the auditor will obtain a responsive action plan from management when both parties agree on which of the following attributes of the audit finding?
An internal auditor is conducting a financial audit. Which of the following audit procedures is most appropriate when existing internal controls are weak?
While conducting a review of the logistics department the internal audit team identified a crucial control weakness. The chief audit executive (CAE) decided to prepare an audit memorandum for management of the logistics department followed by an informal meeting What is the most likely reason the CAE decided to prepare the audit memorandum?
According to IIA guidance, which of the following actions might place the independence of the internal audit function in jeopardy?
At a conference an internal auditor presented a new computer-assisted audit technique developed by his organization The presentation included sample data derived from performing audit engagements for the organization. Travel costs were paid by the conference organizers and the trip was approved by the chief audit executive (CAE). However, neither management nor the CAE was aware that the internal auditor would be making a presentation based on work completed for the organization According to IIA guidance, which of the following statements is most relevant regarding the actions of the auditor?
According to IIA guidance, which of the following statements best justifies a chief audit executive's request for external consultants to complement internal audit activity (IAA) resources?
What is the primary purpose of issuing a preliminary communication to management of the area under review?
Which procedure should an internal auditor perform to determine the audit objective?
The internal audit team judgmentally selected 60 of the 600 employee timesheets that were processed during the previous month to determine whether supervisors were properly approving timesheets in accordance with the organization's policies. The internal audit team found three exceptions. Based on the audit test, which of the following is most appropriate for the internal audit team to conclude?
An audit observation noted that annual inventory counts of biofuel was not being performed appropriately Fuel yards were not visited and physical amounts of biofuel were not reconciled with accounting data Management of the division understood the issue and promised to resolve the problem When should the internal auditor schedule a follow-up review?
Which of the following statements is true regarding the use of internal control questionnaires (ICOs)?
Which of the following offers the best explanation of why the auditor in charge would assign a junior auditor to complete a complex part of the audit engagement?
If the skills and competencies are not present within the internal audit activity to complete an ad-hoc assurance engagement, which of the following is an acceptable resolution?
An internal auditor wants to obtain management's evaluation of the organizational risk culture. Because there are more than 30 geographically dispersed managers, one-to-one interviews are not possible. Which of the following is the most efficient option for the auditor to adopt?
An internal audit intends to create a risk and control matrix to better understand the organization's complex manufacturing process. With which of the following approaches would the auditor most likely start?
The chief audit executive (CAE) determined that the internal audit activity lacks the resources needed to complete the internal audit plan Which of the following would be the most appropriate action tor the CAE to take?
Which of the following statements best explains why an internal auditor should pay attention to retained earnings of an organization?
During an organization’s management meetings, employees who report bad news and significant risks are treated as if they were to blame for those circumstances. As a result, employees tend to postpone delivering bad news to management for as long as possible. Which of the following should be addressed to improve this culture?
The chief audit executive (CAE) should determine whether the internal audit activity has confirmed the status of all of management's corrective actions Doing so would help the CAE assess which of the following?
Which of the following information is most appropriate for the chief audit executive to share when coordinating audit plans with other internal and external assurance providers?
Which of the following is an advantage of utilizing an external fraud specialist in a suspected fraud investigation?
According to IIA guidance which of the following statements is true regarding heat maps?
An internal auditor is performing an assessment in a vehicle brake manufacturing company. The auditor learned that the product quality test conditions are aligned with the company’s written test procedures. However, the test conditions are not similar to conditions experienced by vehicles in the real world. Documentation shows that a significant percentage of products fail the quality tests. Products that fail the tests are discarded. Which perspective is appropriate?
According to HA guidance, which of the following statements regarding audit workpapers is true?
According to IIA guidance, which of the following reflects a characteristic of sufficient and reliable information?
The chief audit executive of an international organization is planning an audit of the treasury function located at the organization's headquarters. The current internal audit team at headquarters lacks expertise in the area of financial markets which is needed tor the engagement When of the following would be the most approbate solution considering the time constraint?
As part of the preliminary survey, an internal auditor sent an internal control questionnaire to the accounts payable function Based on the questionnaire responses, the auditor determines that there is no established procedure for adding and approving new vendors. What would the auditor do next?
An internal auditor was assigned to review controls in the accounts payable function. Most of tie accounts payable processes are performed by a third-party service provider. The auditor included in the audit report a number of control deficiencies involving processes performed by the service provider. The service provider requested a copy of the report Which of Vie following would be the most appropriate response from the chief audit executive (CAE)?
During audit engagement planning, an internal auditor is determining the best approach for leveraging computer-assisted audit techniques (CAATs). Which of the following approaches maximizes the use of CAATs and why?
According to IIA guidance, which of the following objectives was most likely formulated for a non-assurance engagement?
Senior IT management requests the internal audit activity to perform an audit of a complex IT area. The chief audit executive (CAE) knows that the internal audit activity lacks the expertise to perform the engagement. Which of the following is the most appropriate action for the CAE to take?
According to the Standards, which of the following is true regarding the auditor's inclusion of management's satisfactory performance in the final audit report?
Which of the following factors should be considered when determining the staff requirements for an audit engagement?
The internal audit activity's time constraints.
The nature and complexity of the area to be audited.
The period of time since the area was last audited.
The auditors’ preference to audit the area.
The results of a preliminary risk assessment of the activity under review.
Which of the following is an appropriate activity when supervising engagements?
An internal auditor s examination of accounts receivable generates the following results:
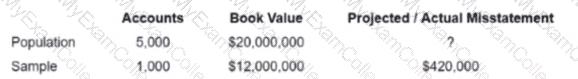
What is the projected misstatement for the population if ratio estimation is used?
An internal auditor is reviewing the accuracy of commission payments by recalculating 100% of the commissions and comparing them to the amount paid. According to IIA guidance, which of the following actions is most appropriate for identified variances?
Which of the following statements is false regarding roles and responsibilities pertaining to risk management and control?
What is the primary objective of an engagement supervisor's review of key activities performed during the engagement?
Which of the following has the greatest effect on the efficiency of an audit?
According to an internal audit observation, the organization’s rules of record management require all contracts to be registered and stored in a specific electronic system. One subsidiary has thousands of client contracts on paper, which are kept in the office because there are not enough assistants to scan the contracts into the system. Which of the following component should be added to this observation?
An internal auditor receives a document displaying all the steps of a process and the path taken as transactions flow between each step of the process How is the internal auditor most likely to use This document during the engagement?
Which of the following statements is true regarding internal auditors and other assurance providers?
The audit engagement objective is to identify vendors who might be involved in money laundering processes or tax evasion schemes. How would the internal auditor use data analytics to fulfill this objective?
Which of the following structures would best suit a maintenance organization that needs to adapt quickly to rapidly changing technology?
An internal auditor discovered that a new employee was granted inappropriate access to the payroll system Apparently the IT specialist had made a mistake and granted access to the wrong new employee. Which of the following management actions would be most effective to prevent a similar issue from occurring again?
Which of the following is a disadvantage of using flowcharts during a risk assessment?
According to IIA guidance,which of the following is true about the supervising internal auditor's review notes?
• They are discussed with management prior to finalizing the audit.
• They may be discarded after working papers are amended as appropriate.
• They are created by the auditor to support her fieldwork in case of questions.
• They are not required to support observations issued in the audit report.
A bakery chain has a statistical model that can be used to predict daily sales at individual stores based on a direct relationship to the cost of ingredients used and an inverse relationship to rainy days What conditions would an auditor look for as an Indicator of employee theft of food from a specific store?
An employee in the sales department completes a purchase requisition and forwards it to the purchaser. The purchaser places competitive bids and orders the requested items using approved purchase orders. When the employee receives the ordered items, she forwards the packing slips to the accounts payable department. The invoice for the ordered items is sent directly to the sales department, and an administrative assistant in the sales department forwards the invoices to the accounts payable department for payment. Which of the following audit steps best addresses the risk of fraud in the cash receipts process?
Which of the following best describes the engagement objective in a banking compliance audit?
An internal auditor performed a review that focused on the organization’s process for vetting vendors. The internal auditor’s testing identified that 120 out of 130 vendors had a business relationship with the organization’s procurement manager that violated conflict-of-interest policies. Which of the following conclusions could the internal auditor draw from these results?
Which of The following best describes a risk that is deemed "unacceptable" to the organization?
An internal auditor wants to examine the intensity of correlation between electricity price and wind speed. Which of the following analytical approaches would be most appropriate for this purpose?
The chief audit executive (CAE) is developing a workpaper preparation policy for a new internal audit activity. The CAE wants to ensure that all workpapers relate directly to the engagement objectives. Which of the following statements should be included in the policy specifically to address this concern?
Which phase of an audit engagement is typically the most effective time for an internal auditor to develop a risk and control matrix?
Which informal ion- gathering method would be most efficient for an internal auditor to determine whether specified control procedures are in place?
Which of the following best describes how an internal auditor would use a flowchart during engagement planning?
During a review of the organization's waste management processes, the internal auditor discovered that wastewater is being disposed of inappropriately. The auditor's recommendations, suggested to mitigate the risk of regulatory sanctions and reputational damages, were accepted and timelines for implementation were agreed. However, during the internal audit activity's periodic follow-up exercise, management indicated that the recommendation was too expensive to implement and the current disposal method has been cost-effective. What should the chief audit executive do in this case?
The external auditor has identified a number of production process control deficiencies involving several departments. As a result, senior management has asked the internal audit activity to complete internal control training for all related staff. According to IIA guidance, which of the following would be the most appropriate course of action for the chief audit executive to follow?
The human resources (HR) department was last reviewed three years ago and is due for an assurance engagement after undergoing recent process changes. Which of the following would the most effective option identify the HR department's risks and controls?
A new internal auditor is overwhelmed by the number of tasks they need to complete at the engagement planning stage. Which of the following could support the auditor’s organization and delivery of planned work?
An internal auditor observes a double payment transaction on a supplier invoice during an accounts payable engagement. Which of the following steps would be the most effective in helping the auditor determine whether fraud exists?
While reviewing the organization’s financial year-end processes, an internal auditor discovered an erroneous journal entry. If the error is not addressed, it will result in a material misstatement of the financial records. The internal auditor needs an additional four weeks to complete the audit engagement. How should the auditor communicate this finding?
An internal control questionnaire would be most appropriate in which of the following situations?
According to IIA guidance which of the following statements is true regarding the annual audit plan?
After concluding a preliminary assessment, the engagement supervisor prepared a draft work program According to HA guidance which of the following would be tested by this program?
A snow removal company is conducting a scenario planning exercise where participating employees consider the potential impacts of a significant reduction in annual snowfall for the coming winter. Which of the following best describes this type of risk?
Which of the following technologies will best reduce human processing errors and enable seamless exchange of business transactions among business partners?
As part of an audit engagement, an internal auditor verifies whether raw material is regularly delivered to the organization's warehouse in a timely manner. What type of objective does this exemplify?
A code of business conduct should include which of the following to increase its deterrent effect?
1. Appropriate descriptions of penalties for misconduct.
2. A notification that code of conduct violations may lead to criminal prosecution.
3. A description of violations that injure the interests of the employer.
4. A list of employees covered by the code of conduct.
An internal auditor determined that the organization's accounting system was designed to reject duplicate invoices if they were issued with identical invoice numbers. However, if an invoice number was changed by at least one digit, the system would accept the duplicate invoice as new. Which of the following would be the most appropriate criteria to refer to in the audit observation?
Which of the following activities Is most likely to require a fraud specialist to supplement the knowledge and skills of the internal audit activity?
Management would like to self-assess the overall effectiveness of the controls in place for its 200-person manufacturing department Which of the following client-facilitated approaches is likely to be the most efficient way to accomplish this objective?
An engagement work program o of greatest value to audit management when which of the following is true?
An internal auditor wants to determine whether employees are complying with the information security policy, which prohibits leaving sensitive information on employee desks overnight. The auditor checked a sample of 90 desks and found eight that contained sensitive information. How should this observation be reported, if the organization tolerates 4 percent noncompliance?
Which of the following statements is true regarding the reporting of tangible and intangible assets?
Which of the following audit steps would an internal auditor perform when reviewing cash disbursements to satisfy IIA guidance on due professional care?
An internal auditor for a regional bank suspects that the head of commercial lending has been granting loans without the required collateral Which of the following sampling techniques will be most effective for investigating the auditor's suspicion?
An internal auditor has been asked to join a project team to help design controls in a software application to address specific risks that have been identified by the team Which of the following actions is most appropriate for the internal auditor to perform?
The internal audit activity is currently working on several engagements, including a consulting engagement on the management process in the human resources department. Which of the following actions should the chief audit executive take to most efficiently and effectively ensure the quality of the engagement?
Which of the following is not a primary purpose for conducting a walk-through during the initial stages of an assurance engagement?
As part of internal audit's assistance with an annual external audit, the internal auditors are required to do a preliminary analytical review of an bank account balances. This involves verifying the current year end balances as web as comparing the current year end balances with previous year end balances to highlight significant changes. Which of the following is the most reliable source for verification of the current year end bank balances?
The engagement supervisor would like lo change the audit program's scope poor to beginning fieldwork According to IIA guidance before any change is implemented what is the most important action that should be undertaken?
According to the International Professional Practices Framework, which of the following is an appropriate reason for issuing an interim report?
To keep management informed of audit progress when audit engagements extend over a long period of time.
To provide an alternative to a final report for limited-scope audit engagements.
To communicate a change in engagement scope for the activity under review.
During an assurance engagement an internal auditor uses benchmarking research to support preparation of a report to stakeholders that contains significant findings about control deficiencies. Which of the following skills did the auditor demonstrate?
Which of the following is the primary reason an internal auditor would issue an interim report during an engagement?
Which of the following best describes the guideline for preparing audit engagement workpapers?
Which of the following represents the best method for confirming that vendor invoices were for authorized purchases?
An electric utility provider measures working time spent on processing grid connection applications, response time for electricity outages, and the call center queuing time. Which of the following criteria would better suit a customer-oriented provider for measurement?
Which of the following engagement techniques would be best to meet the objective of denting a personal conflict -of -interest situation affecting an organization’s procurement function?
A rapidly expanding retail organization continues to be tightly controlled by its original small management team. Which of the following is a potential risk in this vertically centralized organization?
Which of the following is most likely the subject of a periodic report from the chief audit executive to the board?
According to IIA guidance, which of the following is the most appropriate action to be taken by the chief executive (CAE) if management refuses to accept audit recommendations and implement corrective actions, Even after escalation to senior management?
An internal auditor is asked to determine why the production line for a large manufacturing organization has been experiencing shutdowns due to unavailable parts The auditor learns that production data used for generating automatic purchases via electronic interchange is collected on personal computers connected by a local area network (LAN) Purchases are made from authorized vendors based on both the production plans for the next month and an authorized materials requirements plan (MRP) that identifies the parts needed per unit of production. The auditor suspects the shutdowns are occurring because purchasing requirements have not been updated for changes in production techniques. Which of the following audit procedures should be used to test the auditor's theory?
Which of the following parties is accountable for ensuring adequate support for conclusions and opinions readied by the internal audit activity while relying on external auditors' work?
The chief audit executive (CAF) determined that the residual risk identified in an assurance engagement is acceptable. When should this be communicated to senior management?
In which of the following situations would an internal auditor consider the need to outsource competencies and skills9
According to IIA guidance, which of the following are the most important objectives for helping to ensure the appropriate completion of an engagement?
1. Coordinate audit team members to ensure the efficient execution of all engagement procedures.
2. Confirm engagement workpapers properly support the observations, recommendations, and conclusions.
3. Provide structured learning opportunities for engagement auditors when possible.
4. Ensure engagement objectives are reviewed for satisfactory achievement and are documented properly.
Senior management wants assurance that third-party contractors are following procedures as agreed with the organization. Which type of audit would be most appropriate
to achieve this objective?
An investor has acquired an organization that has a dominant position in a mature, slow-growth industry and consistently creates positive financial income Which of the following terms would the investor most likely label this investment in her portfolio?
When creating the internal audit plan, the chief audit executive should prioritize engagements based primarily on which of the following?
An internal auditor collected several employee testimonials Which of the following is the best action for the internal auditor to take before drawing a conclusion?
Which of the following factors would be the most critical in determining which engagements should be included in the annual internal audit plan?
An organization's internal audit plan includes a recurring assurance review of the human resources (HR) department. Which of the following statements is true regarding preliminary communication between the auditor in charge (AIC) and the HR department?
1. The AIC should notify HR management when the draft audit plan is being developed, as a courtesy.
2. The AIC should notify HR management before the planning stage begins.
3. The AIC should schedule formal status meetings with HR management at the start of the engagement.
4. The AIC should finalize the scope of the engagement before communicating with HR management.
An internal audit manager assigns an audit team to test purchase transactions by selecting a sample from transactions processed by each of the three procurement officers.
Which of the following techniques will help the audit team achieve this sampling objective?
During follow-up, the chief audit executive (CAE) is having a discussion with management about the internal audit team's recommendations related to a significant issue Management accepted the issue but took no remedial action What is the next step for the CAE?
Which of the following is most likely the subject of a periodic report from the chief audit executive to the board?
According to IIA guidance, which of the following is least likely to be a key financial control in an organization's accounts payable process?
Which of the following should the chief audit executive do when evaluating the possibility of relying on external auditors' work?
During the planning phase of an assurance engagement, an internal auditor seeks to gam an understanding of now when the area under review is accomplishing its objectives When of the
Following information-gathering techniques is the auditor most likely to use?
An organization recently acquired a subsidiary in a new industry, and management asked the chief audit executive (CAE) to perform a comprehensive audit of the subsidiary prior to recommencing operations The CAE is unsure her team has the necessary skills and knowledge to accept the engagement According to IIAguidance, which of the following responses by the CAE would be most appropriate?
According to IIA guidance, which of the following best describes the purpose of a planning memorandum for an audit engagement?
A chief audit executive (CAE) is determining which engagements to include on the annual audit plan. She would like to consider the organization's attitude toward risk and the degree of difficulty in achieving objectives. Which of the following resources should the CAE consult?
Which of the following statements is true regarding the audit objective for an assurance engagement?
The internal auditors available to perform the engagement do not have sufficient skills related to the area under review. Which of the following iss an appropriate action for the chief audit executive to take?
Which of the following activities demonstrates an example of the chief audit executive performing residual risk assessment?
In which of following scenarios is the internal auditor performing benchmarking?
An internal auditor is performing a review of an organization's vendor for any possible conflicts of interest. Which of the following would provide the greatest assistance to the auditor in meeting this objective?

