What is part of the 5 GHz band?
Channel 12 and 13
U-NII 5
Channels 149 to 161
Channel 14
Answer:
Explanation:
 The 5 GHz band is a radio frequency band used for Wi-Fi communications. It has a higherdata bandwidth than the 2.4 GHz band, but a shorter range and less penetration through walls. The 5 GHz band is divided into several sub-bands, each with a different set of channels. One of these sub-bands is the U-NII-3 band, which covers the frequency range from 5725 MHz to 5850 MHz. This sub-band contains 24 non-overlapping channels, numbered from 149 to 172. Channels 149 to 161 are part of the 5 GHz band and can be used for Wi-Fi communications. Channels 165 and 169 are restricted to indoor use only, and channel 173 is not allowed in some regions. Channels 12, 13, and 14 are not part of the 5 GHz band, but belong to the 2.4 GHz band, which has a different set of channels and regulations. U-NII-5 is not a valid sub-band name, but a proposed extension of the 5 GHz band to include the frequency range from 5925 MHz to 7125 MHz. This extension is not yet approved or implemented, and therefore not part of the 5 GHz band. References: List of WLAN channels, What’s the Difference Between 2.4 and 5 GHz Wi-Fi (and Which Should I Use)?, What is the difference between 2.4 GHz, 5 GHz, and 6 GHz wireless frequencies?
Which organization is in charge of determining the International Standards?
Institute of Electrical and Electronics Engineers
Wi-Fi Alliance
Federal Communications Commission
Internet Engineering Task Force
Answer:
Explanation:
The Institute of Electrical and Electronics Engineers (IEEE) is an organization that develops and publishes international standards for various fields of engineering, including electrical, electronic, computer, software, and telecommunications. IEEE standards are widely used and recognized by the industry, academia, and governments. IEEE standards cover topics such as wireless networking, Ethernet, power systems, smart grid, cybersecurity, robotics, biomedical engineering, and more. IEEE standards are developed by consensus among experts from different sectors and regions, and are reviewed and updated regularly to reflect the latest technologies and best practices. IEEE standards aim to promote innovation, interoperability, safety, reliability, and efficiency in engineering applications. References: IEEE Standards Association, IEEE - Wikipedia, IEEE Standards - Creative Safety Supply
Refer to Exhibit.
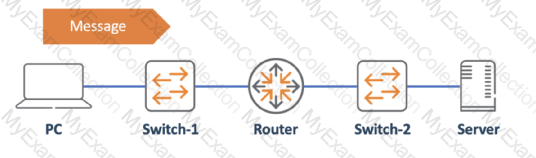
The PC is sending a message to the server. Which devices have performed Layer 2 encapsulation by the time the message arrives at the server? (Select two.)
PC
Server
Router
switch-2
Switch-1
Answer:
Explanation:
Layer 2 encapsulation is the process of adding a header and a trailer to the data coming from the upper layer (Layer 3) before sending it over the physical medium. The header and the trailer contain information such as source and destination MAC addresses, error detection, and protocol type. The devices that perform Layer 2 encapsulation are usually switches, bridges, or network interface cards (NICs). In the given network diagram, the PC is sending a message to the server. The PC first adds a Layer 2 header and trailer to the data and sends it to Switch-1. Switch-1 performs Layer 2 encapsulation again before forwarding it to the router. The router operates at Layer 3 and does not perform Layer 2 encapsulation. It only removes the Layer 2 header and trailer, checks the destination IP address, and forwards the packet to the next hop. The packet then reaches Switch-2, where Layer 2 encapsulation occurs again before it is sent to the server. The server also performs Layer 2 de-encapsulation by removing the header and trailer and passing the data to the upper layer. Therefore, the devices that have performed Layer 2 encapsulation by the time the message arrives at the server are Switch-1 and Switch-2. References: Understanding Data Link Layer Encapsulation, How Data Encapsulation & De-encapsulation Works?, HDLC Protocol and Encapsulation method Explained
Refer to Exhibit.
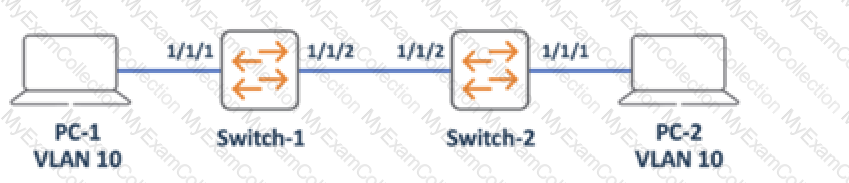
PC-1 and PC-2 are connected to Interfaces configured as access ports on VLAN 10. All other ports on Switch-1 and Switch-2 are in default settings. Which configuration is required on Doth switches to allow inter-PC communication in the same Broadcast domain?
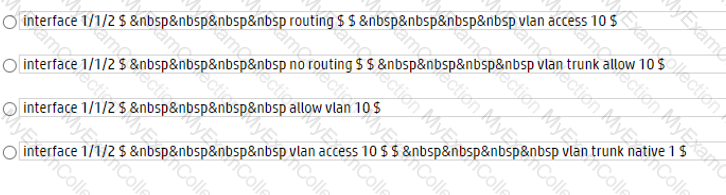
Option A
Option B
Option C
Option D
Answer:
Explanation:
In order to allow inter-PC communication in the same broadcast domain, both switches need to have the same VLAN configured on the ports that connect to the PCs and the trunk port that connects to each other. Option B shows the correct configuration for both switches, as follows:
- On Switch-1, interface 0/1 is configured as an access port on VLAN 10, which matches the VLAN of PC-1. Interface 0/2 is configured as a trunk port, which allows VLAN 10 traffic to pass through to Switch-2.
- On Switch-2, interface 0/1 is configured as an access port on VLAN 10, which matches the VLAN of PC-2. Interface 0/2 is also configured as a trunk port, which allows VLAN 10 traffic to pass through from Switch-1.
Option A is incorrect because it does not configure the trunk port on Switch-2, which prevents VLAN 10 traffic from reaching Switch-1. Option C is incorrect because it configures the trunk port on Switch-1 with the wrong encapsulation mode (ISL instead of dot1q), which causes a mismatch with Switch-2. Option D is incorrect because it configures the access ports on Switch-2 with the wrong VLAN (20 instead of 10), which isolates PC-2 from PC-1.
References:
1: Layer 2 VLAN Configuration on a Cisco Switch (with Example) - Networks Training 2: VLAN Configuration Commands Step by Step Explained - Computer Networking Notes 3: How To Configure VLANs On the Catalyst Switches - Cisco Community 4: Configure VLAN on Cisco Switch Using Cisco Packet Tracer - TECHNIG
Which protocol provides logical addressing used for routing messages across the network towards their destination?
Internet Protocol
Transmission Control Protocol
Wired Ethernet
Link Layer Discovery Protocol
Answer:
Explanation:
 The protocol that provides logical addressing used for routing messages across the network towards their destination is the Internet Protocol (IP). IP is a network layer protocol that assigns a unique numerical identifier to each device on a network, called an IP address. IP addresses are used to identify the source and destination of data packets, and to determine the best path to deliver them. IP is a connectionless and best-effort protocol, meaning that it does not guarantee the delivery, order, or integrity of the packets. IP relies on other protocols, such as TCP, to provide reliable and orderly data transfer.
The other options are incorrect because:
B. Transmission Control Protocol (TCP) is a transport layer protocol that provides reliable and orderly data delivery by establishing a connection between devices and providing error-checking and retransmission mechanisms. TCP does not provide logical addressing or routing functions, but it uses IP addresses to identify the endpoints of a connection.
C. Wired Ethernet is a data link layer protocol that defines the physical and logical characteristics of a wired network, such as cable types, frame formats, and MAC addresses. MAC addresses are used to identify the physical devices on a network segment, but they are not used for routing messages across the network. Ethernet does not provide logical addressing or routing functions, but it relies on IP to do so.
D. Link Layer Discovery Protocol (LLDP) is a data link layer protocol that allows devices to discover and advertise information about themselves and their neighbors on a network, such as device type, capabilities, port configuration, and VLAN membership. LLDP does not provide logical addressing or routing functions, but it can help network administrators to troubleshoot and optimize the network topology. References:
- Aruba Certified Network Technician (ACNT) | HPE Aruba Networking
- Network Layer Protocols - GeeksforGeeks
- Network protocols and layers A Level Resources - Teach Computer Science
Which table must clients populate to remember the L2 addressing of their neighbors?
MAC Table
ARP Table
Routing Table
Ethernet Table
Answer:
Explanation:
The table that clients must populate to remember the L2 addressing of their neighbors is the ARP table. ARP stands for Address Resolution Protocol, which is a protocol that maps an IP address to a MAC address1. A MAC address is a unique identifier for a network interface card (NIC) that operates at the data link layer (layer two) of the OSI model2. An IPaddress is a logical identifier for a device that operates at the network layer (layer three) of the OSI model3. When a client wants to communicate with another device on the same network, it needs to know the MAC address of the destination device. To do this, the client sends an ARP request, which is a broadcast message that asks “Who has this IP address?†The device that has the matching IP address replies with an ARP reply, which contains its MAC address. The client then stores this information in its ARP table, which is a cache of IP-to-MAC mappings. Therefore, statement B is correct. Statements A, C, and D are incorrect because they describe different types of tables. A MAC table is a table that a switch uses to store MAC addresses and the corresponding ports that they are connected to. A routing table is a table that a router uses to store the destination networks and the next-hop addresses that they are reachable through. An ethernet table is not a valid term in networking. References: 1: Aruba Certified Network Technician (ACNT) Study Guide, page 342: Aruba Certified Network Technician (ACNT) Study Guide, page 283: Aruba Certified Network Technician (ACNT) Study Guide, page 29. : Aruba Certified Network Technician (ACNT) Study Guide, page 35. : Aruba Certified Network Technician (ACNT) Study Guide, page 30. : Aruba Certified Network Technician (ACNT) Study Guide, page 31.
What are the differences between Local-based and Server-based management? (Select two.)
server-based management cannot talk to the device's control plane, local-based can
in local-based, the managed device is a client, while in server-based it is a server
local-based management can use the device's console port, server-based cannot
local-based management requires an on-premises network management appliance
server-based management can monitor multiple devices at once, local-based cannot
Answer:
Explanation:
Local-based management refers to managing a network device directly from the device itself, using tools such as console port, web interface, or command-line interface. Server-based management refers to managing a network device remotely from a centralized server, using tools such as Windows Admin Center, System Center, or Azure Arc123. The differences between these two types of management are:
- Local-based management can use the device’s console port, which is a physical connection that allows access to the device even when the network is down or the device is not configured. Server-based management cannot use the console port, as it relies on network connectivity and protocols4.
- Server-based management can monitor multiple devices at once, using a single dashboard or interface that shows the status, performance, and configuration of all the devices in the network. Local-based management can only monitor one device at a time, using the device’s own tools123.
References:
1: Cloud vs Server: Learn the Key Differences and Benefits - Parallels 2: Windows Server management overview | Microsoft Learn 4: 5 Benefits of Server-Based Local Access Networks for Small … - Versatech 3: What is Windows Admin Center | Microsoft Learn
What are characteristics of Aruba Central? (Select two.)
It must be deployed as an on-premises server.
It manages networking equipment using SNMP.
It manages networking equipment using HTTPs.
It can manage third-party networking equipment.
It is considered cloud-based network management.
Answer:
Explanation:
 Aruba Central is a cloud-based networking solution that offers simplicity, security, and scalability for managing Aruba network infrastructure. It uses HTTPs to communicate with networking equipment such as wireless, wired, VPN, and SD-WAN devices. It also provides AI-powered insights, workflow automation, and advanced security features to unifyoperations across campus, branch, data center, and remote work environments. Aruba Central does not require an on-premises server, nor does it use SNMP for management. It also does not support third-party networking equipment, as it is designed for Aruba ESP (Edge Services Platform). References: Aruba Central for Cloud-managed networking, About Aruba Central, Aruba Central data sheet
What is the binary equivalent of the decimal number of 233?
11010101
11101001
11100101
11110001
Answer:
Explanation:
The binary equivalent of the decimal number of 233 is 11101001. To find this, we can use the following method:
- Divide 233 by 2 and write down the remainder. The remainder is either 0 or 1.
- Divide the quotient by 2 and write down the new remainder.
- Repeat this process until the quotient is 0.
- Write the remainders from the bottom to the top. This is the binary equivalent.
For example:
Table
Quotient
Remainder
233 / 2
1
116 / 2
0
58 / 2
0
29 / 2
1
14 / 2
0
7 / 2
1
3 / 2
1
1 / 2
1
0 / 2
0
The remainders from the bottom to the top are 11101001, which is the binary equivalent of 233.
References:
1: Decimal to Binary Converter - RapidTables 2: How to Convert Decimal to Binary - wikiHow 3: Decimal to Binary Conversion Methods - GeeksforGeeks
On which connection type are collisions more likely to happen?
Dark Fiber
Fiber
Copper
Wi-Fi
Answer:
Explanation:
 A collision occurs when two or more devices try to transmit data at the same time on a shared medium, such as a cable or a wireless channel. Collisions result in corrupted or lost data, and reduce the efficiency of the network. Different connection types have different susceptibility to collisions, depending on how they handle data transmission and collision detection.
Dark fiber and fiber are optical connections that use light to transmit data. They are immune to electromagnetic interference and have very high bandwidth. They also use full-duplex communication, which means that data can be sent and received simultaneously on separate fibers. Therefore, collisions are very unlikely to happen on dark fiber and fiber connections.
Copper is an electrical connection that uses metal wires to transmit data. It is prone to electromagnetic interference and has lower bandwidth than optical connections. It can use either half-duplex or full-duplex communication, depending on the device and the protocol. Half-duplex communication means that data can only be sent or received at a time on the same wire. Therefore, collisions are more likely to happen on copper connections that use half-duplex communication, such as Ethernet hubs.
Wi-Fi is a wireless connection that uses radio waves to transmit data. It is also prone to electromagnetic interference and has lower bandwidth than optical connections. It uses half-duplex communication, which means that data can only be sent or received at a time on the same channel. Therefore, collisions are very likely to happen on Wi-Fi connections, especially when there are many devices using the same channel or frequency.
References:
- Types of Collisions
- What are elastic and inelastic collisions?
- Why is a switch port a collision domain?
Which Wi-Fi technology assists with data privacy on open networks?
Simultaneous Authentications of Equals (SAE)
Opportunistic Wireless Encryption (OWE)
Commercial National Security Algorithm (CNSA)
Wi-Fi Protected Access 2 (WPA2)
Answer:
Explanation:
OWE is a Wi-Fi technology that assists with data privacy on open networks by providing unauthenticated data encryption. OWE is based on the standard defined in RFC 8110, which specifies an extension to IEEE 802.11 that uses a cryptographic handshake to encrypt the devices connecting to open network access points. OWE reduces the risk of data exposure or theft when using an open Wi-Fi network, without adding complexity or scalability burdens. OWE is part of the Wi-Fi CERTIFIED Enhanced Open™ program, which is a new certification for Wi-Fi devices that support this technology123 References:
- Wi-Fi CERTIFIED Enhanced Open™: Transparent Wi-Fi … - Wi-Fi Alliance
- Debunking Wi-Fi® Security Myths: Cellular Networks are … - TechSpective
- 10. Use adequate security to send or receive health information over …
Which represents a valid Basic Service Set Identifier (BSSID)?
the radio and all its associated clients
the name of the wireless network
a group of radios and all its WLAN clients
a radio's MAC address assigned to a WLAN
Answer:
Explanation:
A BSSID is a 48-bit label that identifies a basic service set (BSS) within a wireless network. A BSS is a subgroup of devices that share physical-layer medium access characteristics, such as radio frequency, modulation scheme, and security settings. A BSSID is usually the MAC address of the access point (AP) that creates the BSS, or a randomly generated value in an ad hoc network. A BSSID is different from an SSID, which is the name of the wireless network that users see and connect to. An SSID can have multiple BSSIDs associated with it, depending on the number and location of the APs. A BSSID is used to differentiate between different BSSs and to facilitate roaming and load balancing among them. References: https://internetspeedtest.world/wiki/bssid
https://www.minthaik.com/bssid-basic-service-set-identifier/
Why do clients run the Address Resolution Protocol (ARP)?
To discover the destination address of the Layer 3 header of IP packets.
To discover the source address of the Layer 3 header of IP packets.
To discover the destination address of the Layer z header that encapsulates IP packets.
To discover the source address of the Layer z header that encapsulates IP packets.
Answer:
Explanation:
ARP is a protocol that maps an IP address to a MAC address, which is the physical address of a device on a network. ARP is necessary because the software address (IP address) of the host or computer connected to the network needs to be translated to a hardware address (MAC address). Without ARP, a host would not be able to figure out the hardware address of another host. ARP works by sending a broadcast message to all devices on the network, asking for the MAC address of the device that has a specific IP address. The device that has that IP address replies with its MAC address, and the sender stores this information in its ARP cache for future use. The sender then uses the MAC address as the destination address of the Layer 2 header that encapsulates the IP packet. The Layer 2 header is also known as the data link layer header, which is responsible for delivering the packet to the correct device on the same network. The Layer 3 header is also known as the network layer header, which is responsible for routing the packet to the correct network. Therefore, the correct answer is C, because ARP is used to discover the destination address of the Layer 2 header that encapsulates IP packets1234 References: What Is Address Resolution Protocol (ARP)? - Fortinet, Address Resolution Protocol - Wikipedia, ARP (Address Resolution Protocol) explained - Study-CCNA, Aruba Certified Network Technician Exam HPE3-U01 Actual Questions
Which organization provides certifications that ensure interoperability between WLAN vendors?
Institute of Electrical and Electronics Engineers
Federal Communications Commission
Wi-Fi Alliance
Internet Engineering Task Force
Answer:
Explanation:
The Wi-Fi Alliance is an organization that promotes interoperability among WLAN device manufacturers. The Wi-Fi Alliance is an important organization for the advancement of wireless LAN (WLAN) technology. It develops certification programs and technologies that deliver quality Wi-Fi experiences. Members have completed more than 80,000 certifications. Through industry-developed comprehensive testing, Wi-Fi Alliance certification programs ensure that Wi-Fi products from multiple manufacturers work well together. These certification programs are foundational to the rapid adoption and proliferation of Wi-Fi products in home, office, and public access locations around the world and underpin the success of Wi-Fi technology proliferation. Only Wi-Fi CERTIFIED™ products have been tested to deliver interoperability with the latest technologies, and industry-standard security protections. The Wi-Fi CERTIFIED logo gives consumersconfidence that the Wi-Fi devices purchased deliver a positive user experience, regardless of brand. For retailers, vendors, and service providers, the Wi-Fi CERTIFIED seal of approval means consistent performance and better user experience. A company must be a member of Wi-Fi Alliance ® and achieve certification to use the Wi-Fi CERTIFIED logo and Wi-Fi CERTIFIED certification marks. The Wi-Fi Alliance certification programs cover the following categories: Connectivity, Security, Mobility, Coexistence, and Performance123. References: Certification | Wi-Fi Alliance, Programs | Wi-Fi Alliance, Aruba Certified Network Technician Exam HPE3-U01 Actual Questions, Why Wi-Fi Certification Really Matters | Aruba Blogs
Before routers forward unicast packets, what information is compared with the unicast routing table entries?
The source address of the IP header.
The destination address of the Ethernet header.
The destination address of the IP header.
The source address of the Ethernet header.
The inbound port the packet is received in.
Answer:
Explanation:
Before routers forward unicast packets, they compare the destination address of the IP header with the unicast routing table entries. This is because routers use the destination IP address to determine the next hop or outgoing interface for the packet. Routers do not care about the source address of the IP header or the Ethernet header, as they are not relevant for forwarding decisions. The inbound port the packet is received in is also not important, as routers use the routing table to make forwarding decisions, not the interface information. Therefore, the correct answer is C. Referenceshttps://networklessons.com/cisco/ccie-routing-switching/unicast-reverse-path-forwarding-urpf
https://www.killtest.com/news_Aruba_Certified_Network_Technician_Exam_ACNT_HPE3-U01_Exam_Questions_Released_2022_659.html

