What is the broadcast address of the network that contains a host with IP address 192.168.1.147/28?
When a Huawei network device functions as an FTP server, which of the following are possible causes of an FTP client failing to log in to the FTP server? (Select all that apply)
Secure Shell (SSH) is a protocol that uses encryption and authentication mechanisms to implement network services, such as secure access and file transfer, securely over an insecure network. Which of the following protocols use SSH? (Select all that apply)
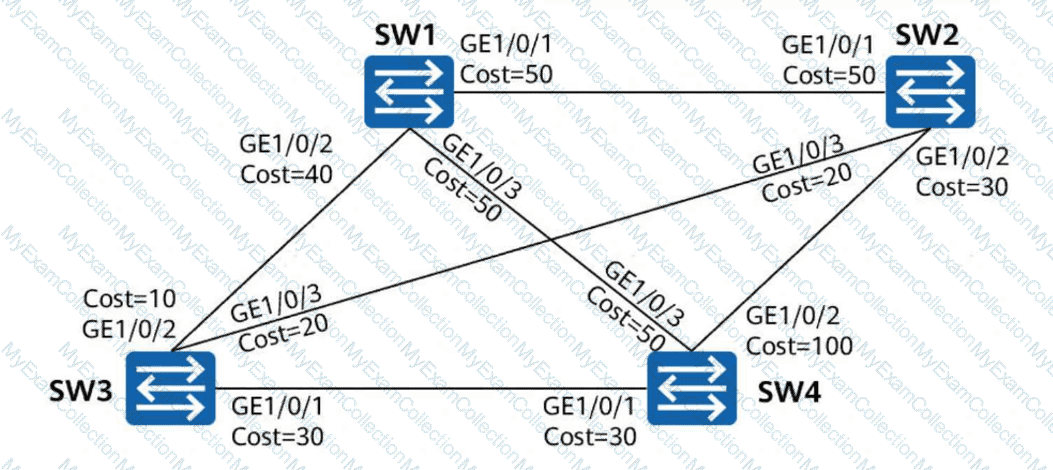
On the network shown in the figure, all switches run STP. All links have a path cost of 20, and SW1 is the root bridge. What is the root path cost (RPC) of SW4?
Both SNMP Trap and Inform Request are used by managed devices to send alarms to the NMS. Inform Request requires an acknowledgment from the NMS, whereas Trap does not.
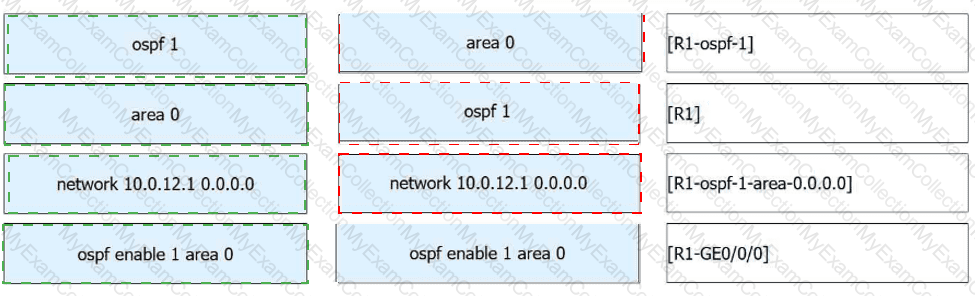
On the switched network shown in the figure, STP is enabled on all devices. SW1 is the root bridge. The port costs are shown in the figure. Other parameters retain the default values. After the network is stable, which of the following paths is used by SW1 to send traffic to SW4?
Which of the following statements are true about the Python code shown below? (Select all that apply)
import paramiko
import time
ssh = paramiko.SSHClient()
ssh.set_missing_host_key_policy(paramiko.AutoAddPolicy())
ssh.connect('192.168.1.254', username='python', password='Huawei@123')
channel = ssh.invoke_shell()
channel.send('screen-length 0 temporary\n')
time.sleep(1)
output = channel.recv(65535).decode('utf-8')
print(output)
ssh.close()
DAD enables a node to detect whether an IPv6 address is already in use by another node before assigning it to an interface. This ensures that duplicate unicast addresses do not exist on a network. Which of the following packets are used for DAD? (Select all that apply)
The traditional Fat AP networking usually applies to WLANs of small and micro stores. For a large-scale WLAN, the WAC + Fit AP networking is typically used. Which of the following statements are true about the WAC + Fit AP networking architecture? (Select all that apply)
Four links between two switches establish an Eth-Trunk in manual mode, and the bandwidth of each link is 1 Gbit/s. One of the links fails. Which of the following statements are true about this scenario? (Select all that apply)
OSPF supports the division of a network into areas, each identified by an area ID that ranges from 0 to 255. Area 0 is designated as the backbone area.
With the continuous development of AI, data center application scenarios are gradually divided into general-purpose computing and intelligent computing scenarios. Data centers need to ensure service continuity of general-purpose computing clusters while unleashing the full potential of intelligent computing clusters, so as to guarantee stable and efficient operation in the AI era. Which of the following statements are true about the service requirements of data center networks in the two scenarios? (Select all that apply)
Which of the following hosts are reachable to the host at 192.168.1.200/27 at Layer 2? (Select all that apply)
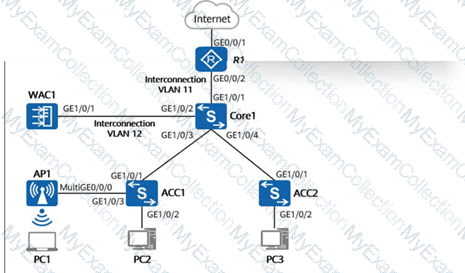
On the campus network shown in the figure below, the core switch Core1 functions as a Layer 3 gateway and as a DHCP server to dynamically assign IP addresses to AP1, PC1, PC2, and PC3. The network below Core1 is a Layer 2 network. WAC1 and R1 are connected to Core1 at Layer 3. AP1 goes online through VLAN 100. The wireless service VLAN is VLAN 101, and the wired service VLANs for PC2 and PC3 are VLAN 102 and VLAN 103, respectively. Additionally, the direct forwarding mode is used for wireless traffic forwarding. If no additional VLANs are allowed on device interfaces, which of the following VLANs must be allowed on GE1/0/1 of ACC1? (Select all that apply)
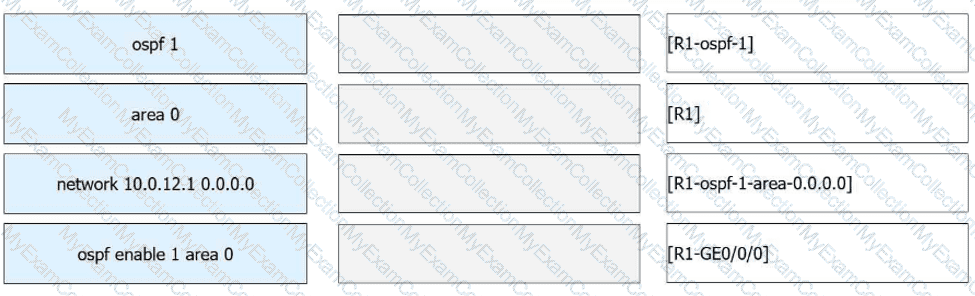
Assume that the IP address of GE0/0/0 on R1 is 10.0.12.1/24. Multiple commands can be used to enable OSPF on this interface. Match the commands with their configuration views.