Regarding the mail content filtering configuration of Huawei USG6000 products, which of the following statements is wrong?.
If the regular expression is "abc. de", which of the following will not match the regular expression?
Which of the following options does not belong to the security risk of the application layer of the TCP/IP protocol stack?
For full encryption registered mobile storage devices must be formatted to normal use in not installed NAC client terminal host.
The core technology of content security lies in anomaly detection, and the concept of defense lies in continuous monitoring and analysis.
Among the following options, which attack is a malformed packet attack based on the TCR protocol?
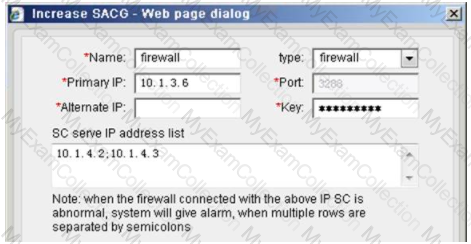
The following is a hardware SACG increase firewall configuration, which statement below is true?
When using the misuse check technology, if the normal user behavior is successfully matched with the intrusion feature knowledge base, it will be falsely reported.
The network-based intrusion detection system is mainly used to monitor the information of the critical path of the network in real time, listen to all packets on the network, collect data, and divide
Analyze the suspicious object, which of the following options are its main features? (multiple choices)
Which of the following behaviors is a false positive of the intrusion detection system?
Which of the following options is not a defense against HTTP Flood attacks?
In order to protect the security of data transmission, more and more websites or companies choose to use SSL to encrypt transmissions in the stream. About using Huawei NIP6000
The product performs threat detection on (SSL stream boy, which of the following statements is correct?
After enabling the IP policy, some services are found to be unavailable. Which of the following may be caused by? (multiple choice)
Which of the following options is wrong for the description of the cleaning center?
IPS is an intelligent intrusion detection and defense product. It can not only detect the occurrence of intrusions, but also can respond in real time through certain response methods.
Stop the occurrence and development of intrusions, and protect the information system from substantial attacks in real time. According to the description of PS, the following items are wrong?
Regarding the enhanced mode in HTTP Flood source authentication, which of the following descriptions are correct? Multiple choices
With regard to APT attacks, the attacker often lurks for a long time and launches a formal attack on the enterprise at the key point of the incident.
Generally, APT attacks can be summarized into four stages:
1. Collecting Information & Intrusion
2. Long-term lurking & mining
3. Data breach
4. Remote control and penetration
Regarding the order of these four stages, which of the following options is correct?
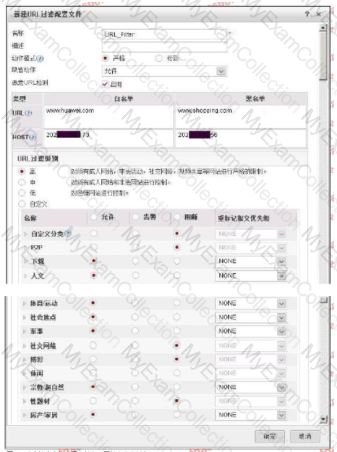
The following figure shows the configuration of the URL filtering configuration file. Regarding the configuration, which of the following statements is correct?
Which of the following descriptions about the black and white lists in spam filtering is wrong? c
Huawei NIP6000 products have zero-setting network parameters and plug-and-play functions, because the interfaces and interface pairs only work on layer 2 without
Set the IP address.
A True
B. False
Which of the following options is correct for the sequence of the flow-by-stream detection of AntiDDoS?
1. The Netflow analysis device samples the current network flow;
2. Send a drainage command to the cleaning center;
3. Discover the DDoS attack stream;
4.Netior: analysis equipment sends alarms to ATIC management center
5. The abnormal flow is diverted to the cleaning center for further inspection and cleaning;
6. The cleaning center sends the host route of the attacked target IF address server to the router to achieve drainage
7. The cleaning log is sent to the management center to generate a report;
8. The cleaned traffic is sent to the original destination server.
Regarding worms and viruses, which of the following statements is correct?
Which of the following descriptions about viruses and Trojans are correct? (multiple choices)

