Which of the following statements is incorrect about information transmission through the heartbeat link between two firewalls that work in hot standby mode?
IKE SA is a one-way logical connection, and only one IKE SA needs to be established between two peers.
____- The goal is to provide a rapid, composed and effective response in emergency situations, thereby enhancing the ability of the business to recover immediately from a disruptive event.[fill in the blank]*
_____ Authentication is to configure user information (including local user's user name, password and various attributes) on the network access server. The advantage is that it is fast.[fill in the blank]*
When IPSec VPN uses tunnel mode to encapsulate packets, which of the following is not within the encryption scope of the ESP security protocol?
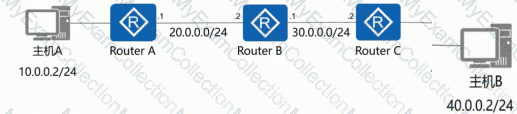
As shown in the figure, the administrator needs to test the network quality of the 20.0.0/24 CIDR block to the 40.0.0/24 CIDR block on Device B, and the device needs to send large packets for a long time to test the network connectivity and stability.
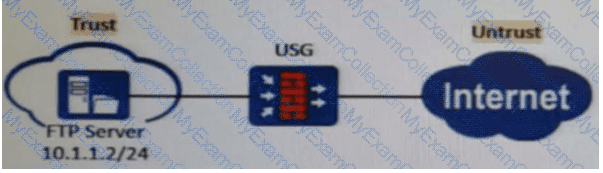
As shown in the figure, nat server global202.106.1.1 inside10.10.1.1 is configured on the firewall. Which of the following is the correct configuration for interzone rules?
Database operation records can be used as ___ evidence to backtrack security events.[fill in the blank]*
Compared with the software architecture of C/S, B/S does not need to install a browser, and users are more flexible and convenient to use.
Which of the following functions help implement IPsec secure transmission of user service data on the Internet by means of encryption and authentication?
Which of the following statements are correct about the PKI system structure?
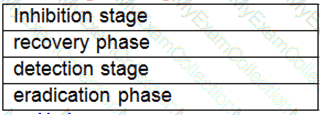
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution.[fill in the blank]*
Which of the following descriptions about the heartbeat interface is wrong ( )?
Which of the following attack methods is to construct special SQL statements and submit sensitive information to exploit program vulnerabilities
WAF can accurately control and manage users' online behavior and user traffic.
The trigger modes of the built-in Portal authentication in the firewall include pre-authentication and ____ authentication[fill in the blank]*
When forwarding a TCP, UDP, or ICMP packet, the firewall needs to query the session table in order to determine the connection to which the packet belongs and take corresponding measures.
The following description of IDS, which items are correct
The IDS cannot be linked to the firewall.
A Web server is deployed in an enterprise intranet to provide Web access services to Internet users, and in order to protect the access security of the server, it should be divided into the _____ area of the firewall.
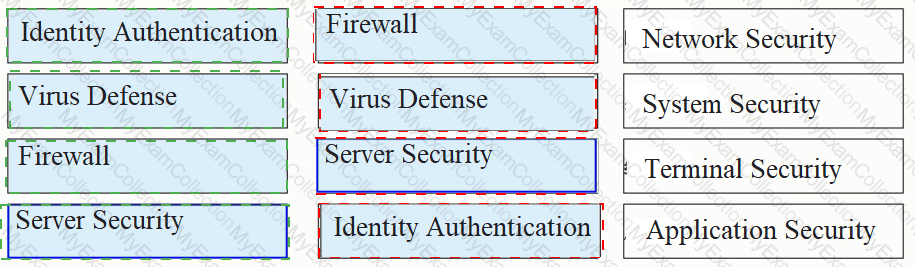
Please classify the following security defenses into the correct classification.

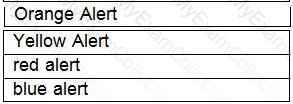
Drag the warning level of the network security emergency response on the left into the box on the right, and arrange it from top to bottom in order of severity.[fill in the blank]*
How frequently should antivirus signature databases be updated to ensure the effectiveness of an antivirus program or software?
Which of the following statements are incorrect about the differences between routers and Layer 2 switches?
Sub-interfaces can be created on GE0/0/1 of a firewall. The sub-interfaces can be added to different VLANs, but cannot be added to security zones.
On a firewall, security policies with the permit action do not need to be configured for traffic between users in the same zone.
Which of the following is not included in the Business Impact Analysis (BIA).
The traffic direction of a firewall is based on the zone priority. The _____ direction refers to the direction from a low-priority zone to a high-priority zone. Capitalize the first letter.
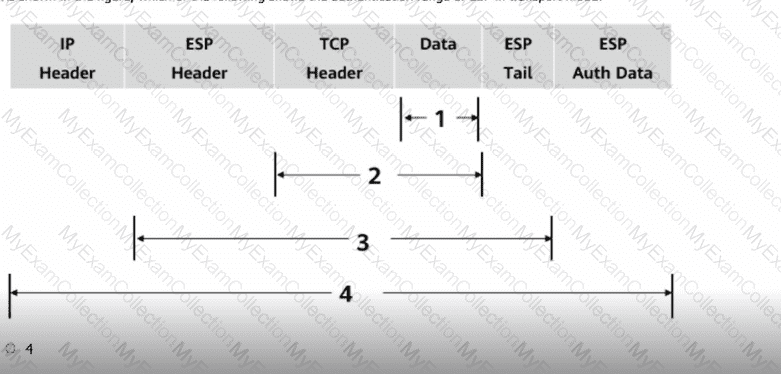
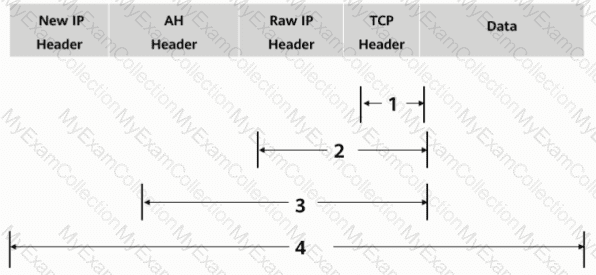
As shown in the figure, what is the authentication range of the AH protocol in tunnel mode?
Sub-interfaces can be created on GE0/0/1 of a firewall. The sub-interfaces can be added to different VLANs, but cannot be added to security zones.
The following description of asymmetric encryption algorithms, which item is wrong?
As shown in the figure, which of the following shows the authentication range of ESP in transport mode?