While troubleshooting a FortiGate web filter issue, users report that they cannot access any websites, even though those sites are not explicitly blocked by any web filter profiles that are applied to firewall policies.
What are the three most likely reasons for this behavior? (Choose three answers)
During which phase of IKEv2 does the Diffie-Helman key exchange take place?
Refer to the exhibit.
The modified output of live routing kemel is shown
Which two statements about the output are (rue? (Choose two.)
Refer to the exhibit, which shows the output of a diagnose command.
What two conclusions can you draw from the output shown in the exhibit? (Choose two answers)
Refer to the exhibit, which shows the modified output of the routing kernel.
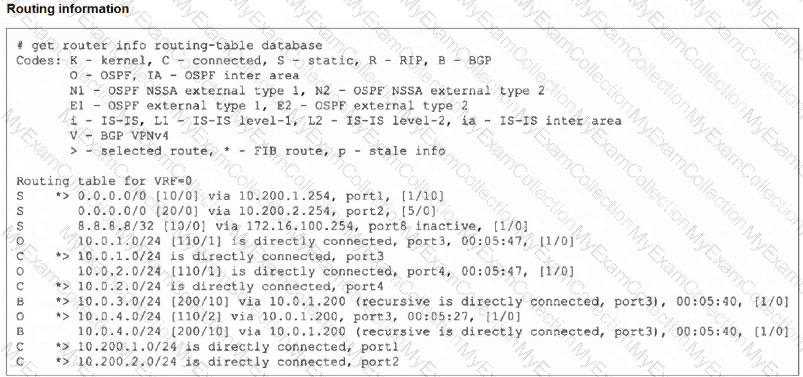
Which statement is true?
What can cause an IKEv2 tunnel to go down after it was initially brought up successfully?
Refer to the exhibit.
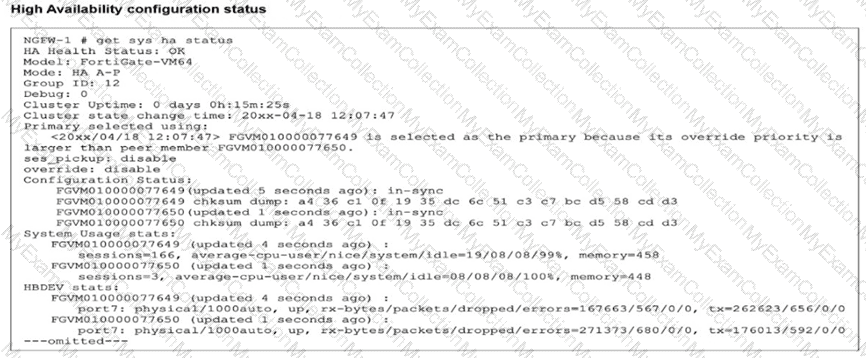
Which two statements about the output are true, considering NGFW-1 and NGFW-2 have been up for a week? (Choose two.)
Refer to the exhibit.
The output of a BGO debug command is shown.
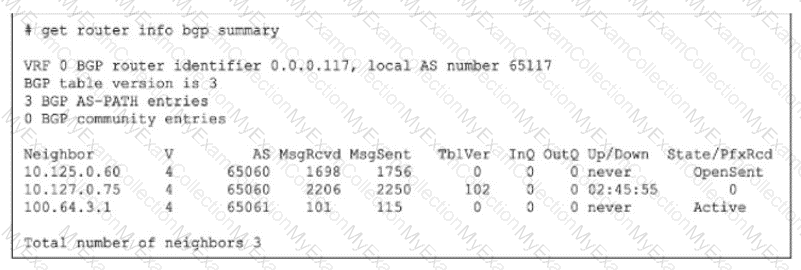
What is the most likely reason that the local FortiGate is not receiving any prefixes from its neighbors?
Refer to the exhibit, which shows the partial output of a diagnose command.
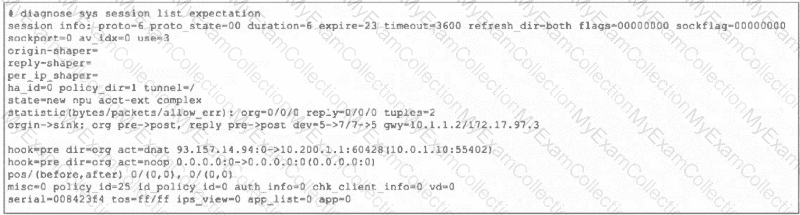
Which two conclusions can you draw from the output shown in the exhibit? (Choose two.)
Refer to the exhibit.
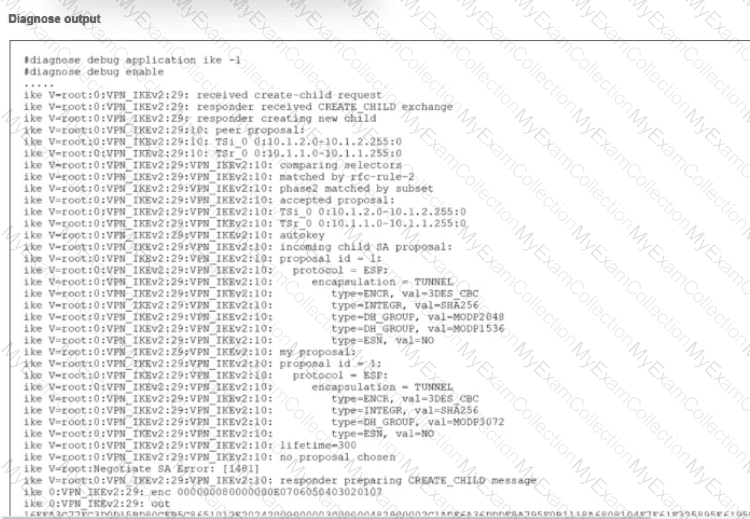
An IPsec VPN tunnel using IKEv2 was brought up successfully, but when the tunnel rekey takes place the tunnel goes down.
The debug command for IKE was enabled and, in the exhibit, you can review the partial output of the debug IKE while attempting to bring the tunnel up.
What is causing. The tunnel to be down?
Refer to the exhibit, which shows the output of get router info bgp summary.
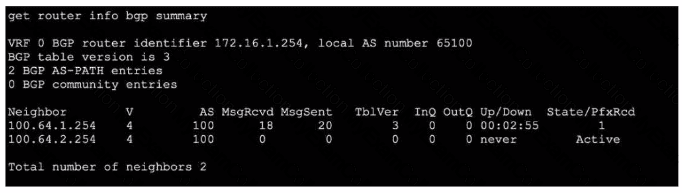
Which two statements are true? (Choose two.)
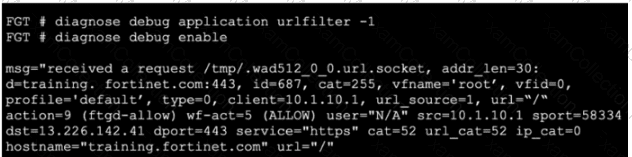
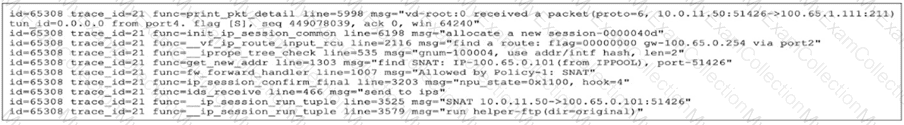
Refer to the exhibit, which shows the output of a real-time debug. Which statement about this output is true? (Choose one answer)
Refer to the exhibit.
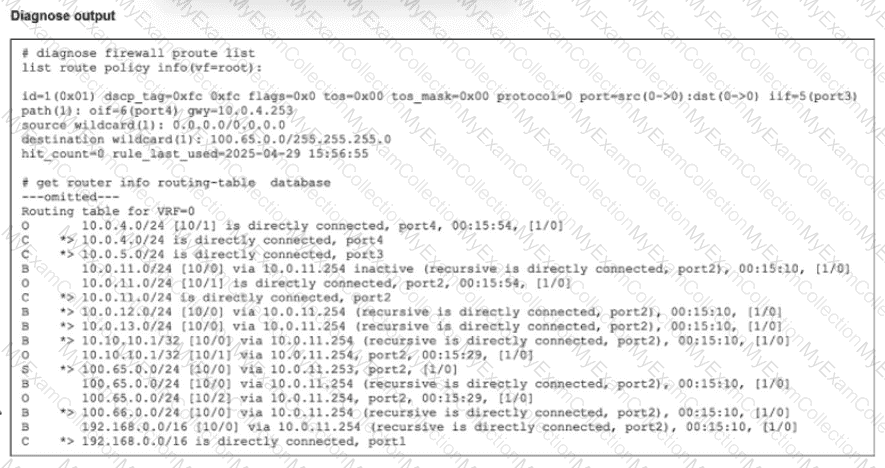
Which route will traffic take to get to the 100.65.0.0/24 network considering the routes are all configured with the same distance?
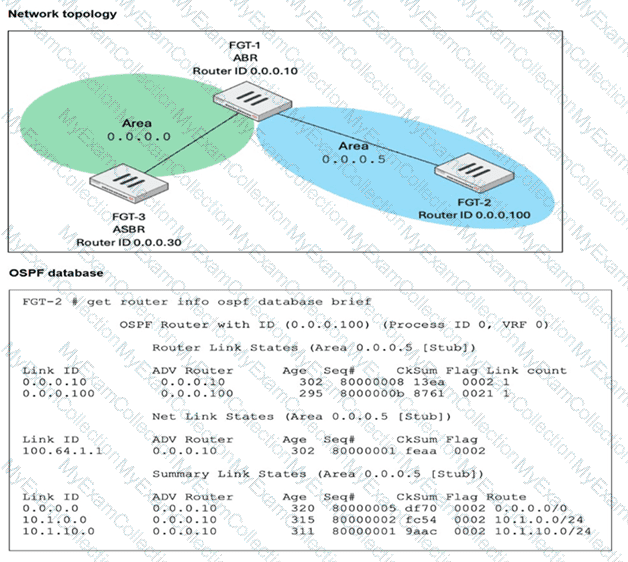
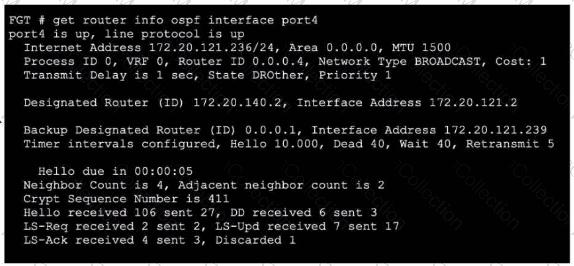
Refer to the exhibits.
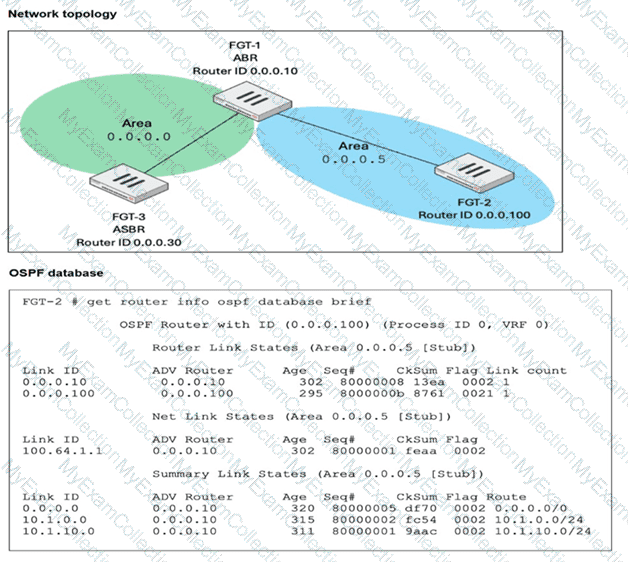
FGT-1 is an area border router (ABR) that has interfaces in OSPF areas 0.0.0.0 and 0.0.0.5. FGT-3 acts as an autonomous system border router (ASBR), importing static routes into OSPF. FGT-2 is an internal router with all its interfaces belonging to area 0.0.0.5. FGT-1 is receiving all advertised routes from FGT-2, however, FGT-3 is not receiving any of the advertised routes from FGT-1. What is the most likely reason for this? (Choose one answer)
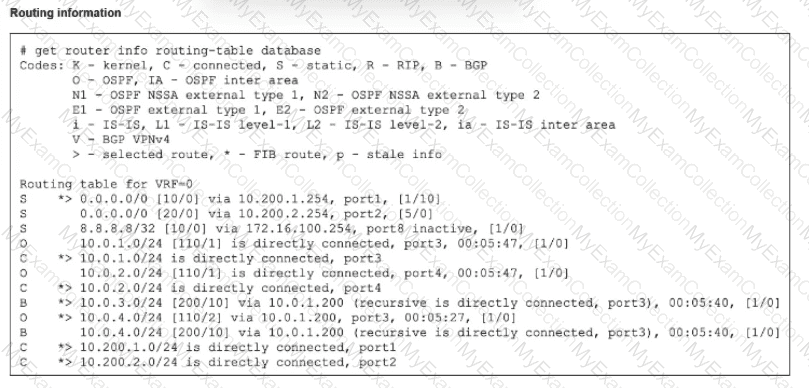
Refer to the exhibit, which shows partial outputs from two routing debug commands.
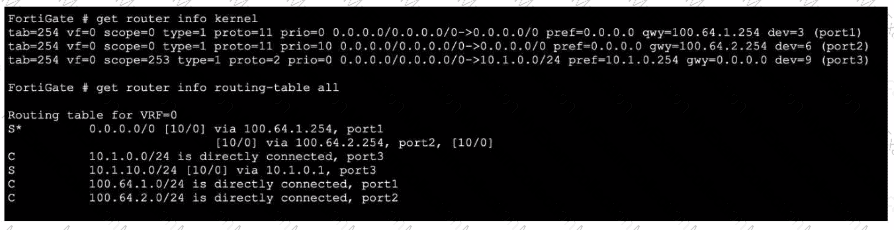
Which change must an administrator make on FortiGate to route web traffic from internal users to the internet, using ECMP?
Refer to the exhibit, which shows the output of a policy route table entry.
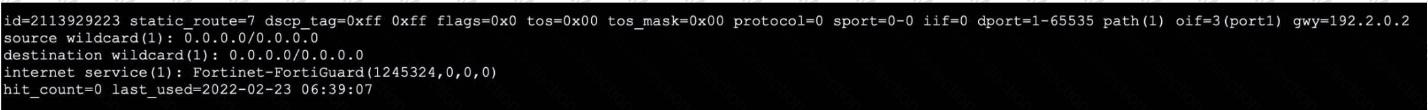
Which type of policy route does the output show?
A VPN tunnel is up. To monitor traffic flow, the administrator enters the following CLI commands on an SSH session on FortiGate:
# diagnose debug enable
# diagnose sniffer packet any ' udp and port 500 ' 4
However, the sniffer does not show any output. Assuming default configuration values, what are two possible reasons there is no output? (Choose two answers)
Exhibit.
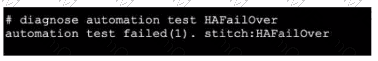
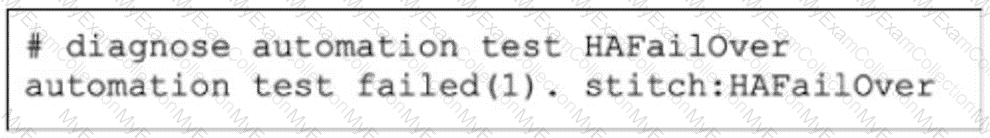
Refer to the exhibit, which shows the output of diagnose automation test.
What can you observe from the output? (Choose two.)
Refer to the exhibit showing a debug output.
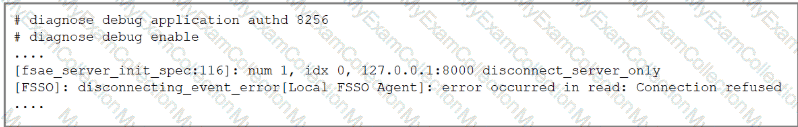
An administrator deployed FSSO in DC Agent Mode but FSSO is failing on FortiGate. Pinging FortiGate from where the collector agent is deployed is successful.
The administrator then produces the debug output shown in the exhibit.
What could be causing this error message?
Consider the scenario where the server name indication (SNI) does not match either the common name (CN) or any of the subject alternative names (SAN) in the server certificate. Which two actions will FortiGate take when using the default settings for SSL certificate inspection? (Choose two answers)
Which three common FortiGate-to-collector-agent connectivity issues can you identify using the FSSO real-time debug? (Choose three.)
Refer to the exhibit.
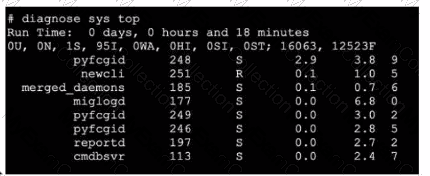
Which three pieces of information does the diagnose sys top command provide? (Choose three.)
Refer to the exhibit, which shows a partial output from the get router info routing-table database command.
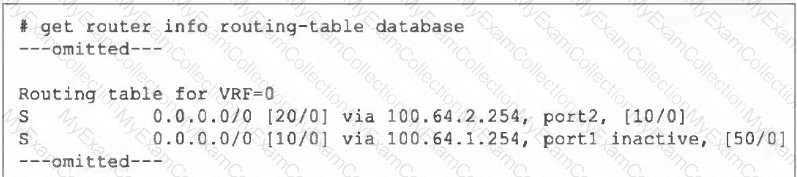
The administrator wants to configure a default static route for port3 and assign a distance of 50 and a priority of 0.
What will happen to the port1 and port2 default static routes after the port3 default static route is created?
Refer to the exhibit.
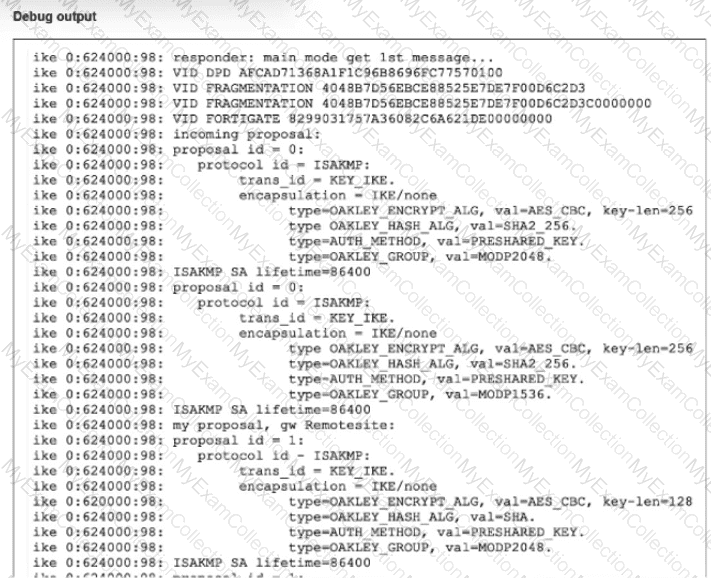
A partial output from an IKE real-time debug is shown
The administrator does not have access to (he remote gateway
Based on the debug output, which two conclusions can you draw? (Choose two.)
Refer to the exhibit.
Partial output of diagnose sys session stat command is shown.
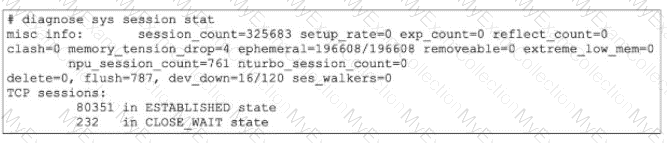
An administrator has noticed unusual behavior from FortiGate. It appears that sessions are randomly removed. Which two reasons could explain this? (Choose two.)
Which three common FortiGate-to-collector-agent connectivity issues can you identify using the FSSO real-time debug? (Choose three.)
Refer to the exhibit.
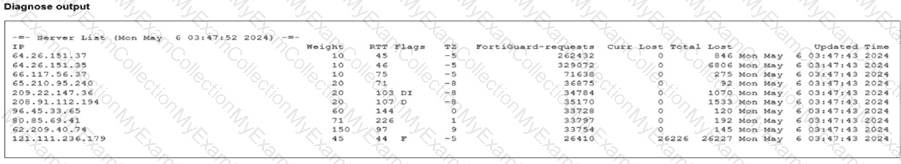
Partial output of command diagnose debug rating is shown. Which FDS server will the FortiGate algorithm choose?
Refer to the exhibit, which shows the output of a debug command.
Which two statements about the output are true? (Choose two.)
Refer to the exhibit, which a network topology and a partial routing table.
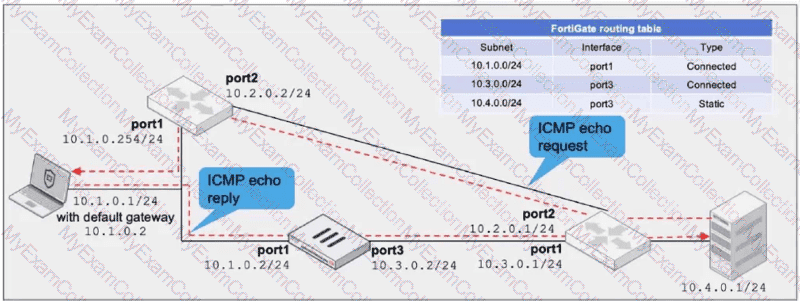
FortiGate has already been configured with a firewall policy that allows all ICMP traffic to flow from port1 to port3.
Which changes must the administrator perform to ensure the server at 10.4.0.1/24 receives the echo reply from the laptop at 10.1.0.1/24?
Refer to the exhibit.
An administrator has configured a firewall policy to use proxy-based inspection mode. What could explain the messages observed in the debug flow output?
What are two reasons that an OSPF router does not have any type 5 tank-state advertisements (LSAs) In its link-stale database (LSD6)? (Choose two.)
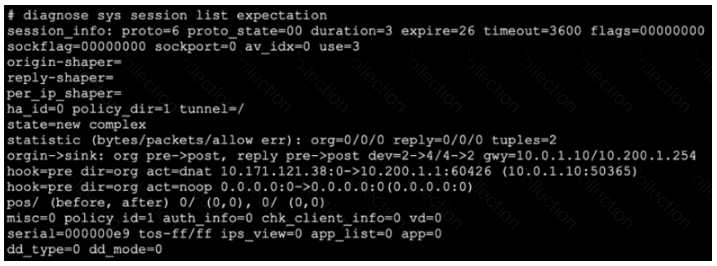
Refer to the exhibit, which shows the output of diagnose sys session list.
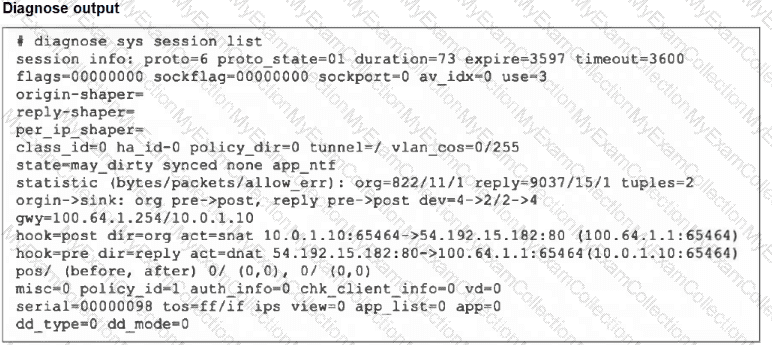
If the HA ID for the primary device is 0, what happens if the primary fails and the secondary becomes the primary?
Refer to the exhibit, which shows the output of a BGP debug command.
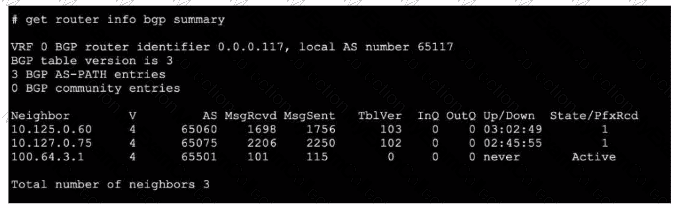
What can you conclude about the router in this scenario?
Refer to the exhibit.
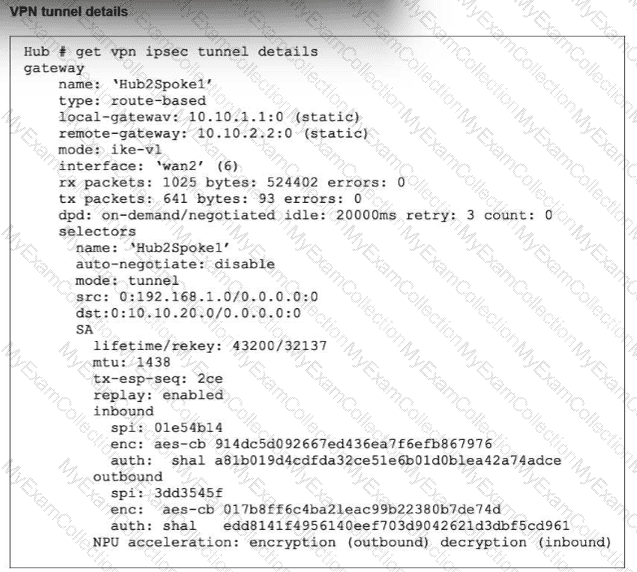
Partial output of the get vpn ipsec tunnel details command is shown. Based on the output, which two statements are correct? (Choose two.)