A cloud architect is designing the VPCs for a new hybrid cloud deployment. The business requires the following:
High availability
Horizontal auto-scaling
60 nodes peak capacity per region
Five reserved network IP addresses per subnet
/24 range
Which of the following would BEST meet the above requirements?
A cloud engineer, who manages workloads in a public cloud environment, uses autoscaling to maintain availability of a critical application. During a recent burst in demands, the engineer received the following error alert:
LimitedlnstanceCapacity
Which of the following is MOST likely cause of the error?
A storage administrator is reviewing the storage consumption of a SAN appliance that is running a VDI environment. Which of the following features should the administrator implement to BEST reduce the storage consumption of the SAN?
A startup online gaming company is designing the optimal graphical user experience for multiplayer scenarios. However, online players have reported latency issues. Which of the following should the company configure as a remediation?
A piece of software applies licensing fees on a socket-based model. Which of the following is the MOST important consideration when attempting to calculate the licensing costs for this software?
An organization has a public-facing API that is hosted on a cloud provider. The API performs slowly at times. Which of the following technologies should the cloud administrator apply to provide speed acceleration and a secure connection?
A security analyst is investigating incidents in which attackers are able to access sensitive data from a corporate application's database. The attacks occur periodically and usually
after the release of a new application's version. The following log confirms the compromise:
The following actions are made after every incident occurrence:
• Validation of firewall rules
• Scripted rebuild of the database and web instances
• Application deployment from a cloud code repository
Which of the following actions will MOST likely prevent future compromises?
A web-application company recently released some new marketing promotions without notifying the IT staff. The systems administrator has since been noticing twice the normal traffic consumption every two hours for the last three hours in the container environment. Which of the following should the company implement to accommodate the new traffic?
After initial stress testing showed that a platform performed well with the specification of a single 32 vCPU node, which of the following will provide the desired service with the LOWEST cost and downtime?
While investigating network traffic, a cloud administrator discovers the monthly billing has increased substantially. Upon further review, it appears the servers have been compromised, and sensitive files have been exfiltrated. Which of the following can be implemented to maintain data confidentiality?
A systems administrator received an email from a cloud provider stating that storage is 80% full on the volume that stores VDI desktops. Which of the following is the MOST efficient way to mitigate the situation?
A company wants to move to a multicloud environment and utilize the technology that provides the most portability. Which of the following technology solutions would BEST meet the company's needs?
A systems administrator is deploying a new virtualized environment. The setup is a three-server cluster with 12 VMs running on each server. While executing a vertical-scaling test of the vCPU on the VMs, the administrator gets an error. Which of the following issues is MOST likely occurring?
A company is performing a DR drill and is looking to validate its documentation. Which of the following metrics will determine the service recovery duration?
A cloud administrator needs to establish a secure connection between two different locations. Which of the following is the BEST option to implement the secure connection?
A cloud architect is deploying a web application that contains many large images and will be accessed on two continents. Which of the following will MOST improve the user experience while keeping costs low?
A company is migrating workloads from on premises to the cloud and would like to establish a connection between the entire data center and the cloud environment. Which of the following VPN configurations would accomplish this task?
A systems administrator is helping to develop a disaster recovery solution. The solution must ensure all production capabilities are available within two hours. Which of the following will BEST meet this requirement?
A systems administrator wants to restrict access to a set of sensitive files to a specific group of users. Which of the following will achieve the objective?
Due to a policy change, a few of a customer’s application VMs have been migrated to synchronously replicated storage. The customer now reports that performance is lower. The systems administrator checks the resource usage and discovers CPU utilization is at 60% and available memory is at 30%.
Which of the following is the MOST likely cause?
A cloud administrator is designing a multiregion network within an IaaS provider. The business requirements for configuring the network are as follows:
Use private networking in and between the multisites for data replication.
Use low latency to avoid performance issues.
Which of the following solutions should the network administrator use within the IaaS provider to connect multiregions?
A systems administrator recently upgraded the processors in a web application host. Upon the next login, the administrator sees a new alert regarding the license being out of compliance.
Which of the following licensing models is the application MOST likely using?
A SaaS provider wants to maintain maximum availability for its service.
Which of the following should be implemented to attain the maximum SLA?
A developer is no longer able to access a public cloud API deployment, which was working ten minutes prior.
Which of the following is MOST likely the cause?
An organization is required to set a custom registry key on the guest operating system.
Which of the following should the organization implement to facilitate this requirement?
A marketing team is using a SaaS-based service to send emails to large groups of potential customers. The internally managed CRM system is configured to generate a list of target customers automatically on a weekly basis, and then use that list to send emails to each customer as part of a marketing campaign. Last week, the first email campaign sent emails successfully to 3,000 potential customers. This week, the email campaign
attempted to send out 50,000 emails, but only 10,000 were sent.
Which of the following is the MOST likely reason for not sending all the emails?
A company has developed a cloud-ready application. Before deployment, an administrator needs to select a deployment technology that provides a high level of portability and is lightweight in terms of footprint and resource requirements.
Which of the following solutions will be BEST to help the administrator achieve the requirements?
A web server has been deployed in a public IaaS provider and has been assigned the public IP address of 72.135.10.100. Users are now reporting that when they browse to the website, they receive a message indicating the service is unavailable. The cloud administrator logs into the server, runs a netstat command,
and notices the following relevant output:
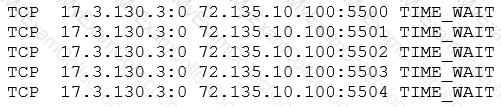
Which of the following actions should the cloud administrator take to resolve the issue?
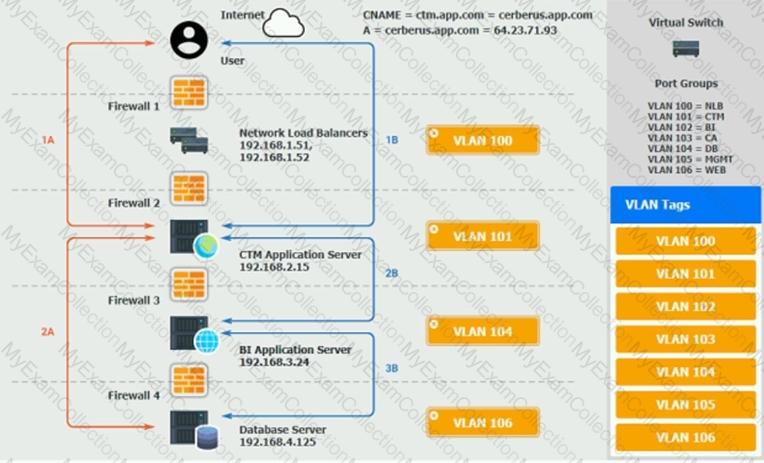
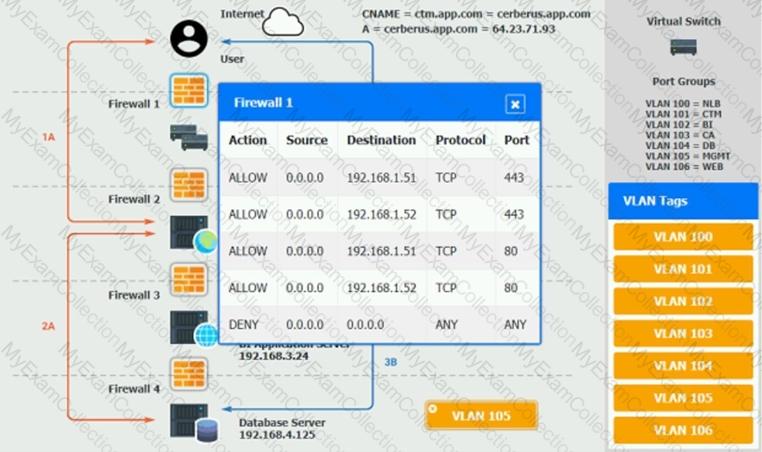
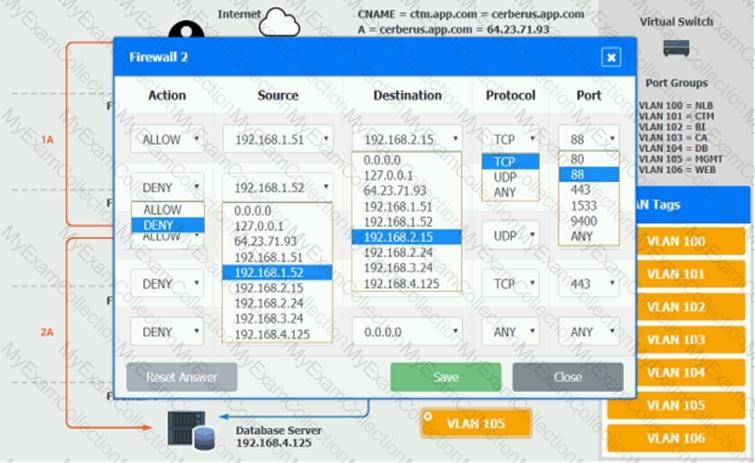
The QA team is testing a newly implemented clinical trial management (CTM) SaaS application that uses a business intelligence application for reporting. The UAT users were instructed to use HTTP and HTTPS.
Refer to the application dataflow:
1A – The end user accesses the application through a web browser to enter and view clinical data.
2A – The CTM application server reads/writes data to/from the database server.
1B – The end user accesses the application through a web browser to run reports on clinical data.
2B – The CTM application server makes a SOAP call on a non-privileged port to the BI application server.
3B – The BI application server gets the data from the database server and presents it to the CTM application server.
When UAT users try to access the application using https://ctm.app.com or http://ctm.app.com, they get a message stating: “Browser cannot display the webpage.†The QA team has raised a ticket to troubleshoot the issue.
INSTRUCTIONS
You are a cloud engineer who is tasked with reviewing the firewall rules as well as virtual network settings.
You should ensure the firewall rules are allowing only the traffic based on the dataflow.
You have already verified the external DNS resolution and NAT are working.
Verify and appropriately configure the VLAN assignments and ACLs. Drag and drop the appropriate VLANs to each tier from the VLAN Tags table. Click on each Firewall to change ACLs as needed.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.

A cloud administrator is reviewing a new application implementation document. The administrator needs to make sure all the known bugs and fixes are applied, and unwanted ports and services are disabled.
Which of the following techniques would BEST help the administrator assess these business requirements?
A company developed a product using a cloud provider’s PaaS platform and many of the platform-based components within the application environment.
Which of the following would the company MOST likely be concerned about when utilizing a multicloud strategy or migrating to another cloud provider?
A systems administrator wants the VMs on the hypervisor to share CPU resources on the same core when feasible.
Which of the following will BEST achieve this goal?
A cloud administrator has built a new private cloud environment and needs to monitor all computer, storage, and network components of the environment.
Which of the following protocols would be MOST useful for this task?
Lateral-moving malware has infected the server infrastructure.
Which of the following network changes would MOST effectively prevent lateral movement in the future?
A company wants to implement business continuity, and the cloud solution architect needs to design the correct solution.
Which of the following will provide the data to measure business continuity? (Choose two.)
An organization is hosting a DNS domain with private and public IP ranges.
Which of the following should be implemented to achieve ease of management?
A systems administrator is concerned about having two virtual database servers on the same host. Which of the following should be configured?
A company is planning its cloud architecture and wants to use a VPC for each of its three products per environment in two regions, totaling 18 VPCs. The products have interdependences, consuming services between VPCs. Which of the following should the cloud architect use to connect all the VPCs?
An engineer is responsible for configuring a new firewall solution that will be deployed in a new public cloud environment. All traffic must pass through the firewall. The SLA for the firewall is 99.999%. Which of the following should be deployed?
A company needs to migrate the storage system and batch jobs from the local storage system to a public cloud provider. Which of the following accounts will MOST likely be created to run the batch processes?
A DevOps administrator is designing a new machine-learning platform. The application needs to be portable between public and private clouds and should be kept as small as possible. Which of the following approaches would BEST meet these requirements?
A systems administrator has migrated a web application to the cloud with a synchronous uplink speed of 100Mbps. After the migration, the administrator receives reports of slow connectivity to the web application. The administrator logs into the firewall and notices the WAN port is transmitting at a constant 12.5MBps. Which of the following BEST explains the reason for the issue?
A company is planning to migrate applications to a public cloud, and the Chief Information Officer (CIO) would like to know the cost per business unit for the applications in the cloud. Before the migration, which of the following should the administrator implement FIRST to assist with reporting the cost for each business unit?
A cloud administrator has been using a custom VM deployment script. After three months of use, the script no longer joins the LDAP domain. The cloud administrator verifies the account has the correct permissions. Which of the following is the MOST likely cause of the failure?
A database analyst reports it takes two hours to perform a scheduled job after onboarding 10,000 new users to the system. The analyst made no changes to the scheduled job before or after onboarding the users. The database is hosted in an IaaS instance on a cloud provider. Which of the following should the cloud administrator evaluate to troubleshoot the performance of the job?
A company is currently running a website on site. However, because of a business requirement to reduce current RTO from 12 hours to one hour, and the RPO from one day to eight hours, the company is considering operating in a hybrid environment. The website uses mostly static files and a small relational database. Which of the following should the cloud architect implement to achieve the objective at the LOWEST cost possible?
An organization is using multiple SaaS-based business applications, and the systems administrator is unable to monitor and control the use of these subscriptions. The administrator needs to implement a solution that will help the organization apply security policies and monitor each individual SaaS subscription. Which of the following should be deployed to achieve these requirements?
An administrator has been informed that some requests are taking a longer time to respond than other requests of the same type. The cloud consumer is using multiple network service providers and is performing link load balancing for bandwidth aggregation. Which of the following commands will help the administrator understand the possible latency issues?
A systems administrator has received an email from the virtualized environment's alarms indicating the memory was reaching full utilization. When logging in, the administrator notices that one out of a five-host cluster has a utilization of 500GB out of 512GB of RAM. The baseline utilization has been 300GB for that host. Which of the following should the administrator check NEXT?
Which of the following service models would be used for a database in the cloud?
A company had a system compromise, and the engineering team resolved the issue after 12 hours. Which of the following information will MOST likely be requested by the Chief Information Officer (CIO) to understand the issue and its resolution?
A company has an in-house-developed application. The administrator wants to utilize cloud services for additional peak usage workloads. The application has a very unique stack of dependencies.
Which of the following cloud service subscription types would BEST meet these requirements?
A cloud solutions architect needs to determine the best strategy to deploy an application environment in production, given the following requirements:
No downtime
Instant switch to a new version using traffic control for all users
Which of the following deployment strategies would be the BEST solution?
An update is being deployed to a web application, and a systems administrator notices the cloud SQL database has stopped running. The VM is responding to pings, and there were not any configuration changes scheduled for the VM. Which of the following should the administrator check NEXT?
A cloud engineer is responsible for managing a public cloud environment. There is currently one virtual network that is used to host the servers in the cloud environment. The environment is rapidly growing, and the network does not have any more available IP addresses. Which of the following should the engineer do to accommodate additional servers in this environment?
Users of an enterprise application, which is configured to use SSO, are experiencing slow connection times. Which of the following should be done to troubleshoot the issue?
A company is considering consolidating a number of physical machines into a virtual infrastructure that will be located at its main office. The company has the following requirements:
High-performance VMs
More secure
Has system independence
Which of the following is the BEST platform for the company to use?
A systems administrator is performing an OS upgrade on a production VM. Which of the following actions should the administrator take before the upgrade to ensure the FASTEST recovery of the system in case the upgrade fails in an unrecoverable way?
A cloud engineer needs to perform a database migration. The database has a restricted SLA and cannot be offline for more than ten minutes per month. The database stores 800GB of data, and the network bandwidth to the CSP is 100MBps Which of the following is the best option to perform the migration?
A systems administrator is working within a private cloud environment. Over time. random 4K read/write speeds on all VMS in the environment slow down until the VMS are completely unusable, with disk speeds of less than 1MBps. The administrator has gathered the information below:
• There is no correlation between the slowdown and VM/hypervisor resource utilization.
• The network is rated to 40Gbps and utilization is between 1—5%.
• The hypervisors use hundreds of NFSv3 mounts to the same storage appliance, one per VM.
• The VMS on each hypervisor become unresponsive after two weeks of uptime.
• The unresponsiveness is resolved by moving slow VMS onto a rebooted hypervisor.
Which of the following solutions will MOST likely resolve this issue?
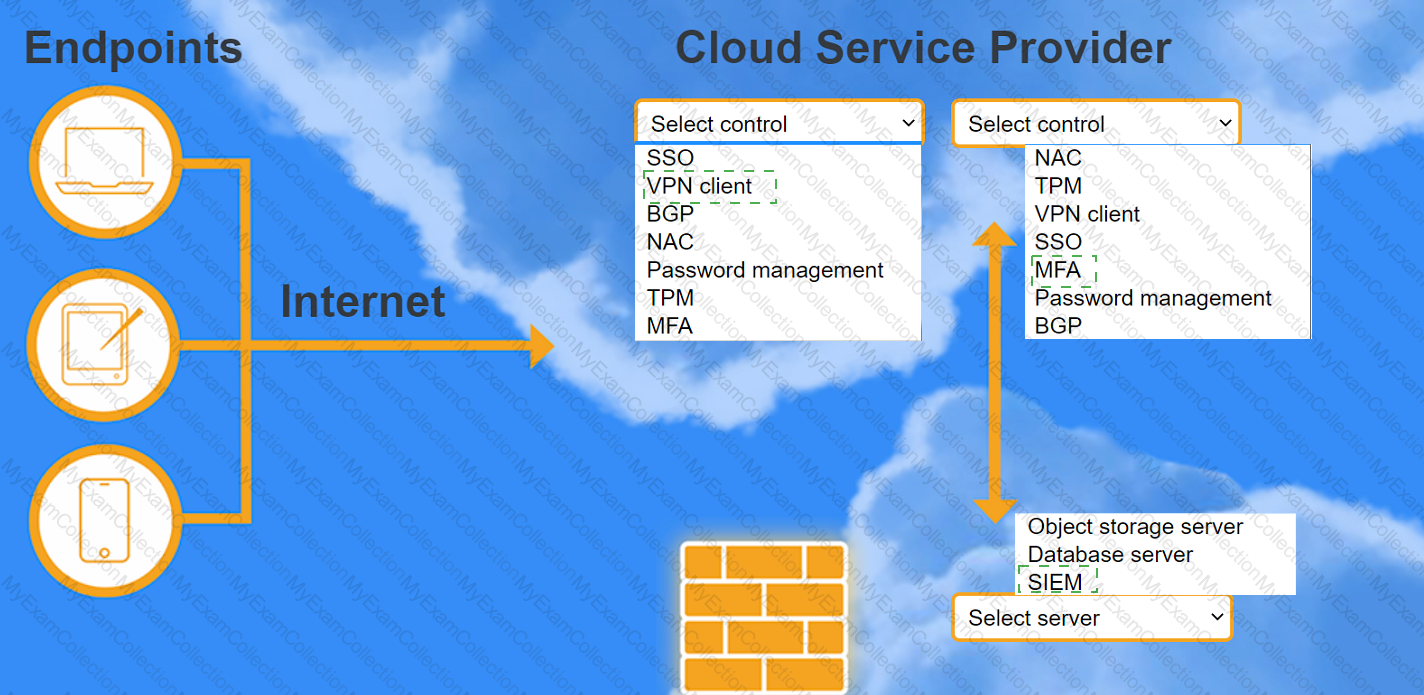
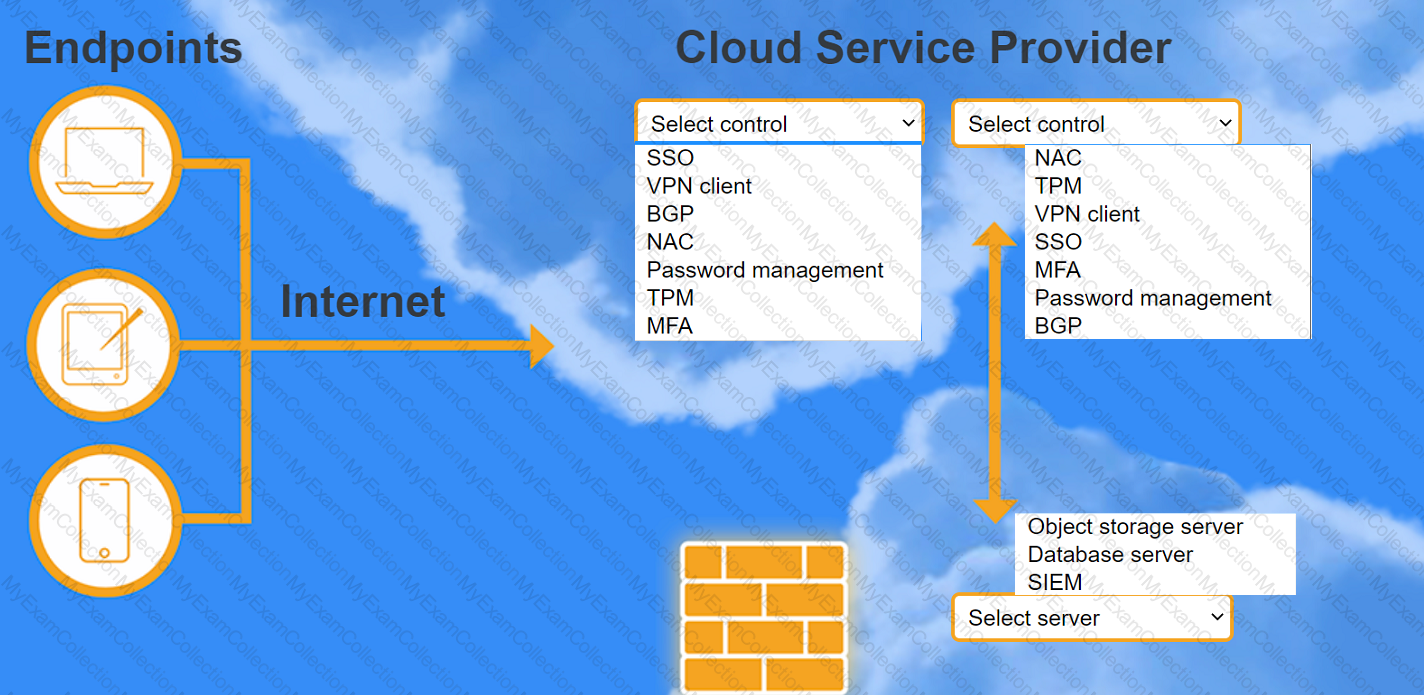
A highly regulated business is required to work remotely, and the risk tolerance is very low. You are tasked with providing an identity solution to the company cloud that includes the following:
secure connectivity that minimizes user login
tracks user activity and monitors for anomalous activity
requires secondary authentication
INSTRUCTIONS
Select controls and servers for the proper control points.
A company is using a hybrid cloud environment. The private cloud is hosting the business applications, and the cloud services are being used to replicate for availability purposes.
The cloud services are also being used to accommodate the additional resource requirements to provide continued services. Which of the following scalability models is the company utilizing?
A systems administrator has verified that a physical switchport that is connected to a virtualization host is using all available bandwidth. Which of the following would best address this issue?
A systems administrator wants to repurpose and implement a legacy tool that has been used in the past as a multicloud monitoring system. Which of the following will be the most probable challenges in the future caused by this implementation? (Select two).
An organization’s web server farm, which is hosted in the cloud with DNS load balancing, is experiencing a spike in network traffic. This has caused an outage of the organization’s web server infrastructure.
Which of the following should be implemented to prevent this in the future as a mitigation method?
An organization is running a database application on a SATA disk, and a customer is experiencing slow performance most of the time.
Which of the following should be implemented to improve application performance?
A cloud administrator checked out the deployment scripts used to deploy the sandbox environment to a public cloud provider. The administrator modified the script to add an application load balancer in front of the web- based front-end application. The administrator next used the script to recreate a new sandbox environment successfully, and the application was then using the new load balancer.
The following week, a new update was required to add more front-end servers to the sandbox environment. A second administrator made the necessary changes and checked out the deployment scripts. The second administrator then ran the script, but the application load balancer was missing from the new deployment.
Which of the following is the MOST likely reason for this issue?
Which of the following cloud deployment models allows a company to have full control over its IT infrastructure?
An organization has the following requirements that need to be met when implementing cloud services:
SSO to cloud infrastructure
On-premises directory service
RBAC for IT staff
Which of the following cloud models would meet these requirements?
A company needs to rehost its ERP system to complete a datacenter migration to the public cloud. The company has already migrated other systems and configured VPN connections.
Which of the following MOST likely needs to be analyzed before rehosting the ERP?
A systems administrator needs to configure monitoring for a private cloud environment. The administrator has decided to use SNMP for this task.
Which of the following ports should the administrator open on the monitoring server’s firewall?
A systems administrator is provisioning VMs in a cloud environment and has been told to select an OS build with the furthest end-of-life date.
Which of the following OS builds would be BEST for the systems administrator to use?
A systems administrator is reviewing two CPU models for a cloud deployment. Both CPUs have the same number of cores/threads and run at the same clock speed.
Which of the following will BEST identify the CPU with more computational power?
A VDI administrator has received reports of poor application performance.
Which of the following should the administrator troubleshoot FIRST?
A systems administrator is deploying a new storage array for backups. The array provides 1PB of raw disk space and uses 14TB nearline SAS drives. The solution must tolerate at least two failed drives in a single RAID set.
Which of the following RAID levels satisfies this requirement?
A systems administrator is deploying a solution that requires a virtual network in a private cloud environment. The solution design requires the virtual network to transport multiple payload types.
Which of the following network virtualization options would BEST satisfy the requirement?
Company A has acquired Company B and is in the process of integrating their cloud resources. Company B needs access to Company A’s cloud resources while retaining its IAM solution.
Which of the following should be implemented?
A cloud administrator set up a link between the private and public cloud through a VPN tunnel. As part of the migration, a large set of files will be copied. Which of the following network ports are required from a security perspective?
A systems administrator wants to ensure two VMs remain together on the same host. Which of the following must be set up to enable this functionality?
A support engineer wants to prevent users from running malware on several IaaS compute instances. Which of the following will BEST achieve this objective?
A company is concerned about the security of its data repository that contains customer PII. A systems administrator is asked to deploy a security control that will prevent the exfiltration of such data. Which of the following should the systems administrator implement?
Which of the following definitions of serverless computing BEST explains how it is different from using VMs?
A company wants to move its environment from on premises to the cloud without vendor lock-in. Which of the following would BEST meet this requirement?
An organization suffered a critical failure of its primary datacenter and made the decision to switch to the DR site. After one week of using the DR site, the primary datacenter is now ready to resume operations.
Which of the following is the MOST efficient way to bring the block storage in the primary datacenter up to date with the DR site?
An administrator recently provisioned a file server in the cloud. Based on financial considerations, the administrator has a limited amount of disk space. Which of the following will help control the amount of space that is being used?
A cloud administrator needs to reduce the cost of cloud services by using the company's off-peak period. Which of the following would be the BEST way to achieve this with minimal effort?
Users of a public website that is hosted on a cloud platform are receiving a message indicating the connection is not secure when landing on the website. The administrator has found that only a single protocol is opened to the service and accessed through the URL https://www.comptiasite.com. Which of the following would MOST likely resolve the issue?
After a few new web servers were deployed, the storage team began receiving incidents in their queue about the web servers. The storage administrator wants to verify the incident tickets that should have gone to the web server team. Which of the following is the MOST likely cause of the issue?
A cloud provider wants to make sure consumers are utilizing its IaaS platform but prevent them from installing a hypervisor on the server. Which of the following will help the cloud provider secure the environment and limit consumers’ activity?
A VDI administrator has received reports from the drafting department that rendering is slower than normal. Which of the following should the administrator check FIRST to optimize the performance of the VDI infrastructure?
A cloud administrator is managing an organization's infrastructure in a public cloud. All servers are currently located in a single virtual network with a single firewall that all traffic must pass through. Per security requirements, production, QA, and development servers should not be able to communicate directly with each other. Which of the following should an administrator perform to comply with the security requirement?
A user reports a poor-quality remote VDI session. Which of the following should the help desk technician do FIRST to troubleshoot the issue?
A VDI provider suspects users are installing prohibited software on the instances. Which of the following must be implemented to prevent the issue?
A cloud administrator is reviewing the current private cloud and public laaS environment, and is building an optimization plan. Portability is of great concern for the administrator so resources can be easily moved from one environment to another.
Which of the following should the administrator implement?
A web consultancy group currently works in an isolated development environment. The group uses this environment for the creation of the final solution, but also for showcasing it to customers, before commissioning the sites in production. Recently, customers of newly commissioned sites have reported they are not receiving the final product shown by the group, and
the website is performing in unexpected ways. Which of the following additional environments should the group adopt and include in its process?
A cloud administrator is looking at the company's cloud services bill for the previous month. The administrator notices on the billing dashboard that certain resources are not being billed to any particular department. Which of the following actions will help correct this billing issue?
The Chief Information Officer of a financial services company wants to ensure stringent security measures are maintained while migrating customer financial information from a private cloud to the public cloud. The cloud engineer must deploy automated validation and verification checks to prevent unauthorized disclosure of financial information. Which of the following should be configured during the migration?
A cloud administrator notices an e-commerce website was recently warned that the connection is not private. Which of the following is most likely the cause?
A cloud engineer receives an alert that a newly provisioned server is running a non-supported Linux version. The automation scripts are performing as expected on the server. Which of the following should the engineer check first?
A cloud solutions architect has an environment that must only be accessed during work hours. Which of the following processes should be automated to BEST reduce cost?
A company migrated its entire retail marketplace system to the cloud. The company is currently running a three-tier architecture on a Virtual Private Cloud (VPC) with web, database, and application servers on separate segments using virtual servers as compute resources. After the migration, users reported the following issues:
Slow-loading web pages
Connection timeouts that are resolved after retries
Given the following statistics:
[root@ApplicationServer]* traceroute DBserver
traceroute to DBserver (192.168.10.2), 30 hops max, 60 by packets
1 gateway (192.168.11.1) 2.341 ms 3.77 ms 3.716 ms
2 nexthop (192.168.10.1) 2.5 ms 2.80 ms 2.36 ms
...
3 nexthop (192.168.10.2) 95 ms 97 ms 98 ms
Which of the following is the best explanation for these issues?
After analyzing a web server’s logs, a systems administrator sees that users are connecting to the company’s application through HTTP instead of HTTPS. The administrator then configures a redirect from HTTP to HTTPS on the web server, and the application responds with a connection time-out message.
Which of the following should the administrator verify NEXT?
A cloud administrator receives a billing report and notices the IT department billing has been the same for the last few months, despite the deployment of ten new instances for the SIEM solution. Which of the following is the most likely cause of the issue?
As a result of an IT audit, a customer has decided to move some applications from an old legacy system to a private cloud. The current server location is remote with low bandwidth. Which of the following is the best migration strategy to use for this deployment?
A cloud service provider is designing an online streaming service that requires an uptime of 99.9%. Which of the following will best meet the uptime requirement?
A systems administrator is implementing a new file storage service that has been deployed in the company's private cloud instance. The key requirement is fast read/write times for the targeted users, and the budget for this project is not a concern. Which of the following storage types should the administrator deploy?
Based on the shared responsibility model, which of the following solutions passes the responsibility of patching the OS to the customer?
An IaaS provider has numerous devices and services that are commissioned and decommissioned automatically on an ongoing basis. The cloud administrator needs to implement a solution that will help reduce administrative overhead.
Which of the following will accomplish this task?
A systems administrator is creating a playbook to run tasks against a server on a set schedule.
Which of the following authentication techniques should the systems administrator use within the playbook?
A systems administrator is planning a penetration test for company resources that are hosted in a public cloud. Which of the following must the systems administrator do FIRST?
A cloud administrator has created a new asynchronous workflow lo deploy VMs to the cloud in bulk. When the workflow is tested for a single VM, it completes successfully. However, if the workflow is used to create 50 VMs at once, the job fails. Which of the following is the MOST likely cause of the issue? (Choose two.)
A local bank has all of its infrastructure in the cloud. An update was applied to the main database server at 5:00 a.m. on Monday morning, and the database was then corrupted and unusable. It had to be restored from backup. The last backup was taken the night before at 10:00 p.m. The database was then restored successfully, but seven hours' worth of data was lost, which is deemed unacceptable. Which of the following needs to be updated in the DR plan?
A cloud administrator would like to maintain file integrity checks through hashing on a cloud object store. Which of the following is MOST suitable from a performance perspective?
A web application has been configured to use autoscaling for provisioning and deprovisioning more VMs according to the workload. The systems administrator deployed a new CI/CD tool to automate new releases of the web application. During the night, a script was deployed and configured to be executed by the VMs during bootstrapping. Now. the autoscaling configuration is creating a new VM ever\ five minutes. Which of the following actions will MOS I like y resolve the issue?
An administrator needs to back up all the data from each VM daily while also saving space. Which of the following backup types will BEST fit this scenario?
An enterprise recently upgraded the memory of its on-premises VMs from 8GB to 16GB. However, users are not experiencing any performance benefit. Which of the following is the MOST likely reason?
A cloud administrator is reviewing the annual contracts for all hosted solutions. Upon review of the contract for the hosted mail solution, the administrator notes the monthly subscription rate has increased every year. The provider has been in place for ten years, and there is a large amount of data being hosted. Which of the following is a barrier to switching providers?
A cloud administrator received a request to provision a set of cloud resources in an effort to switch to infrastructure as code to automate and optimize operations. The administrator decides to try to run some tests with the following definition:
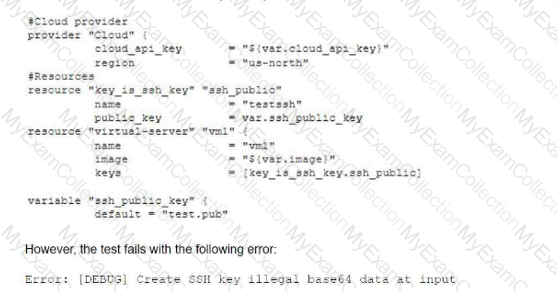
Which of the following is the most likely cause of the issue?
A newly deployed public cloud tenant has been billed five times the forecasted amount. Which of the following is the most likely cause of the issue?
A production engineer is configuring a new application, which is running in containers, that requires access to a database. Which of the following methods will allow the application to authenticate to the database in the MOST secure way?
A company that requires full administrative control at the OS level is considering the use of public cloud services. Which of the following service models would BEST fit the company's requirements?
A cloud engineer is migrating a customer's web servers from a hypervisor platform to a CSP environment. The engineer needs to decouple the infrastructure and components during the migration to reduce the single points of failure. Which of the following storage options should the cloud engineer migrate the content to in order to improve availability?
A cloud administrator recently misconfigured the permission policy on a credential vault by granting public access to it. Which of the following should the administrator do? (Select two).
A systems administrator is trying to connect to a remote KVM host. The command line appears as follows:
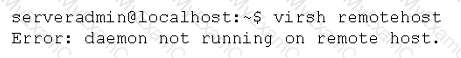
After logging in to the remote server, the administrator verifies the daemon is running. Which of the following should the administrator try NEXT?
An environment has a dual-stack infrastructure in an active-active configuration in two separate data centers. Which of the following best describes replication between the two sites?
A DevOps engineer needs to make application deployments more efficient. The current process to deploy and scale the application is very manual, with hours spent configuring servers from scratch each time. The application has many platform-based dependencies but is highly portable and can run on multiple platforms. Which of the following is most likely to reduce deployment time and improve efficiencies?
A cloud administrator for a retail business identified a significant month-to-month increase in the cost of storage. The current IaaS instances are hosting the organization's ERP solution. Which of the following is the most likely cause for the cost increase?
A company is migrating a large fleet of on-premises servers into the public cloud. The number of servers is estimated to be between 800 and 900. The systems administrator is doing the network planning. Which of the following subnets should the administrator use? (Select two).
An organization's executives would like to allow access to devices that meet the corporate security compliance levels. Which of the following criteria are most important for the organization to consider? (Select two).
During a security incident on an laaS platform, which of the following actions will a systems administrator most likely take as part of the containment procedure?