An internally developed payroll application leverages Platform as a Service (PaaS) infrastructure from the cloud. Who owns the related data confidentiality risk?
Which of the following is the PRIMARY reason to conduct risk assessments at periodic intervals?
Which of the following controls will BEST mitigate risk associated with excessive access privileges?
An organization is considering the adoption of an aggressive business strategy to achieve desired growth From a risk management perspective what should the risk practitioner do NEXT?
Which of the following is the BEST course of action when risk is found to be above the acceptable risk appetite?
Business management is seeking assurance from the CIO that IT has a plan in place for early identification of potential issues that could impact the delivery of a new application Which of the following is the BEST way to increase the chances of a successful delivery ' ?
Which of the following is the BEST way to incorporate continuous monitoring in IT risk policies?
Which of the following is the MAIN reason to continuously monitor IT-related risk?
Which of the following would be a risk practitioner ' s GREATEST concern with the use of a vulnerability scanning tool?
The BEST reason to classify IT assets during a risk assessment is to determine the:
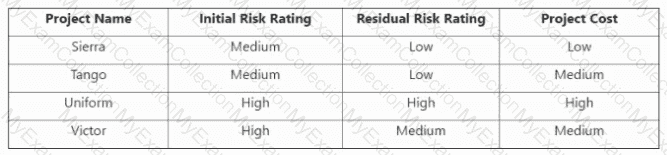
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
Which of the assessments provides the MOST reliable input to evaluate residual risk in the vendor ' s control environment?
Which of the following is the MOST important metric to monitor the performance of the change management process?
Who is BEST suited to provide objective input when updating residual risk to reflect the results of control effectiveness?
Which of the following would MOST effectively reduce risk associated with an increase of online transactions on a retailer website?
Which of the following is MOST important to the effective monitoring of key risk indicators (KRIS)?
Which of the following is a risk practitioner ' s MOST important action to reduce the likelihood of internal fraud?
A business delegates its application data management to the internal IT team. Which of the following is the role of the internal IT team in this situation?
When a risk practitioner is building a key risk indicator (KRI) from aggregated data, it is CRITICAL that the data is derived from:
Which of the following should be done FIRST upon learning that the organization will be affected by a new regulation in its industry?
Which of the following BEST facilitates the development of effective IT risk scenarios?
Which of the following would be the BEST senior management action to influence a strong risk-aware culture within an organization?
Of the following, who is responsible for approval when a change in an application system is ready for release to production?
Which of the following controls would BEST reduce the risk of account compromise?
Which of the following provides the MOST comprehensive information when developing a risk profile for a system?
A risk practitioner notices a risk scenario associated with data loss at the organization ' s cloud provider is assigned to the provider who should the risk scenario be reassigned to.
A risk owner has identified a risk with high impact and very low likelihood. The potential loss is covered by insurance. Which of the following should the risk practitioner do NEXT?
WhichT5f the following is the MOST effective way to promote organization-wide awareness of data security in response to an increase in regulatory penalties for data leakage?
Which of the following provides the MOST important information to facilitate a risk response decision?
Which of the following is the PRIMARY reason for a risk practitioner to report changes and trends in the IT risk profile to senior management?
Which of the following is MOST important information to review when developing plans for using emerging technologies?
Which of the following should be the PRIMARY consideration when implementing controls for monitoring user activity logs?
Which of the following is the MOST important reason to restrict access to the risk register on a need-to-know basis?
Key risk indicators (KRIs) are MOST useful during which of the following risk management phases?
A key performance indicator (KPI) has been established to monitor the number of software changes that fail and must be re-implemented. An increase in the KPI indicates an ineffective:
Using key risk indicators (KRIs) to illustrate changes in the risk profile PRIMARILY helps to:
Which of the following is the MOST useful indicator to measure the efficiency of an identity and access management process?
Which of the following would MOST effectively enable a business operations manager to identify events exceeding risk thresholds?
Which of the following is the MOST important consideration for protecting data assets m a Business application system?
Of the following, whose input is ESSENTIAL when developing risk scenarios for the implementation of a third-party mobile application that stores customer data?
Which of the following is MOST important when creating a program to reduce ethical risk?
Which of the following BEST assists in justifying an investment in automated controls?
Which of the following scenarios is MOST likely to cause a risk practitioner to request a formal risk acceptance sign-off?
To enable effective integration of IT risk scenarios and enterprise risk management (ERM), it is MOST important to have a consistent approach to reporting:
A risk practitioner has been asked to mark an identified control deficiency as remediated, despite concerns that the risk level is still too high. Which of the following is the BEST way to address this concern?
Which of the following provides The BEST information when determining whether to accept residual risk of a critical system to be implemented?
Which of the following should be the PRIMARY input when designing IT controls?
Which of the following should be a risk practitioner ' s NEXT step after learning of an incident that has affected a competitor?
An organization operates in a jurisdiction where heavy fines are imposed for leakage of customer data. Which of the following provides the BEST input to assess the inherent risk impact?
Which of the following will MOST improve stakeholders ' understanding of the effect of a potential threat?
Which of the following is the BEST indication of the effectiveness of a business continuity program?
Which of the following is the PRIMARY role of the second line when an IT risk management framework is adopted?
What is the BEST course of action when the business impact of a risk event is rated high, but the likelihood of risk materialization has decreased?
Which of the following is MOST important to understand when determining an appropriate risk assessment approach?
Which of the following is the BEST indicator of executive management ' s support for IT risk mitigation efforts?
An organization is subject to a new regulation that requires nearly real-time recovery of its services following a disruption. Which of the following is the BEST way to manage the risk in this situation?
An organization has identified a risk exposure due to weak technical controls in a newly implemented HR system. The risk practitioner is documenting the risk in the risk register. The risk should be owned by the:
Which of the following is the PRIMARY reason to perform periodic vendor risk assessments?
Which of the following is the BEST way to assess the effectiveness of an access management process?
Which of the following controls BEST helps to ensure that transaction data reaches its destination?
A recent risk workshop has identified risk owners and responses for newly identified risk scenarios. Which of the following should be the risk practitioner ' s NEXT step?
Which of the following is the BEST indication that an organization ' s IT asset life cycle is poorly managed?
A risk heat map is MOST commonly used as part of an IT risk analysis to facilitate risk:
Within the three lines of defense model, the PRIMARY responsibility for ensuring risk mitigation controls are properly configured belongs with:
Which of the following should be the FIRST step when a company is made aware of new regulatory requirements impacting IT?
A risk practitioner has identified that the agreed recovery time objective (RTO) with a Software as a Service (SaaS) provider is longer than the business expectation. Which ot the following is the risk practitioner ' s BEST course of action?
An organization ' s financial analysis department uses an in-house forecasting application for business projections. Who is responsible for defining access roles to protect the sensitive data within this application?
Which of the following BEST enables a risk practitioner to plan a vulnerability assessment that aligns to detailed organizational requirements?
Which of the following changes would be reflected in an organization ' s risk profile after the failure of a critical patch implementation?
A small organization finds it difficult to implement separation of duties necessary to mitigate the likelihood of system misuse. Which of the following would be the BEST compensating control?
When developing risk treatment alternatives for a Business case, it is MOST helpful to show risk reduction based on:
An organization has implemented immutable backups to prevent successful ransomware attacks. Which of the following is the MOST effective control for the risk practitioner to review?
A risk practitioner has become aware of production data being used in a test environment. Which of the following should be the practitioner ' s PRIMARY concern?
Which of the following describes the relationship between Key risk indicators (KRIs) and key control indicators (KCIS)?
During a data loss incident, which role in the RACI chart would be aligned to the risk practitioner?
Which of the following is the PRIMARY concern for a risk practitioner regarding an organization ' s adoption of innovative big data analytics capabilities?
Which of the following presents the GREATEST risk to change control in business application development over the complete life cycle?
Which of the following is the MOST important consideration when developing an organization ' s risk taxonomy?
Which organization is implementing a project to automate the purchasing process, including the modification of approval controls. Which of the following tasks is lie responsibility of the risk practitioner*?
Which of the following is the MOST important benefit of reporting risk assessment results to senior management?
Which of the following is MOST important to consider when determining a recovery time objective (RTO)?
Which of the following is the MOST effective way to mitigate identified risk scenarios?
Which of the following should be determined FIRST when a new security vulnerability is made public?
Which of the following is MOST likely to be identified from an information systems audit report?
Which of the following is necessary to enable an IT risk register to be consolidated with the rest of the organization’s risk register?
Identifying which of the following would BEST help an organization define an IT asset ' s criticality?
Which of the following is the BEST key control indicator (KCI) for measuring the security of a blockchain network?
A business unit has decided to accept the risk of implementing an off-the-shelf, commercial software package that uses weak password controls. The BEST course of action would be to:
Which of the following is the GREATEST risk associated with the use of data analytics?
Which of the following could BEST detect an in-house developer inserting malicious functions into a web-based application?
Which of the following outcomes of disaster recovery planning is MOST important to enable the initiation of necessary actions during a disaster?
Which of the following would MOST likely cause management to unknowingly accept excessive risk?
An organization is moving its critical assets to the cloud. Which of the following is the MOST important key performance indicator (KPI) to include in the service level agreement (SLA)?
Which of the following is the BEST way to identify changes in the risk profile of an organization?
Which of the following is the MOST important consideration when establishing a recovery point objective (RPO)?
Which of the following is a business asset for an organization that runs only in a Software as a Service (SaaS) cloud computing environment?
Mitigating technology risk to acceptable levels should be based PRIMARILY upon:
Of the following, who should be responsible for determining the inherent risk rating of an application?
An organization ' s stakeholders are unable to agree on appropriate risk responses. Which of the following would be the BEST course of action?
Which of the following is the ULTIMATE goal of conducting a privacy impact analysis (PIA)?
Which of the following is the PRIMARY factor in determining a recovery time objective (RTO)?
After migrating a key financial system to a new provider, it was discovered that a developer could gain access to the production environment. Which of the following is the BEST way to mitigate the risk in this situation?
An organization ' s Internet-facing server was successfully attacked because the server did not have the latest security patches. The risk associated with poor patch management had been documented in the risk register and accepted. Who should be accountable for any related losses to the organization?
Which of the following is the PRIMARY benefit of using an entry in the risk register to track the aggregate risk associated with server failure?
Who should be responsible for approving the cost of controls to be implemented for mitigating risk?
Who should be responsible for determining which stakeholders need to be involved in the development of a risk scenario?
When evaluating a number of potential controls for treating risk, it is MOST important to consider:
Of the following, who is BEST suited to assist a risk practitioner in developing a relevant set of risk scenarios?
Which of the following is the MOST effective way to minimize the impact associated with the loss of key employees?
Which of the following is the GREATEST benefit of reviewing security trends reported by a log monitoring system?
An organization has outsourced its IT security operations to a third party. Who is ULTIMATELY accountable for the risk associated with the outsourced operations?
Which of the following is the MOST important concern when assigning multiple risk owners for an identified risk?
Which of the following would require updates to an organization ' s IT risk register?
Which of the following presents the GREATEST challenge for an IT risk practitioner who wants to report on trends in historical IT risk levels?
Which of the following would BEST assist in reconstructing the sequence of events following a security incident across multiple IT systems in the organization ' s network?
Read " rights to application files in a controlled server environment should be approved by the:
Which of the following events is MOST likely to trigger the need to conduct a risk assessment?
Which of the following is the MOST effective way for a large and diversified organization to minimize risk associated with unauthorized software on company devices?
A global organization is considering the transfer of its customer information systems to an overseas cloud service provider in the event of a disaster. Which of the following should be the MOST important risk consideration?
A risk practitioner is performing a risk assessment of recent external advancements in quantum computing. Which of the following would pose the GREATEST concern for the risk practitioner?
During the control evaluation phase of a risk assessment, it is noted that multiple controls are ineffective. Which of the following should be the risk practitioner ' s FIRST course of action?
Which of the following is MOST important for a risk practitioner to verify when periodically reviewing risk response action plans?
Which of the following is the MOST important key performance indicator (KPI) to monitor the effectiveness of disaster recovery processes?
Which of the following approaches to bring your own device (BYOD) service delivery provides the BEST protection from data loss?
Which of the following BEST indicates effective information security incident management?
Improvements in the design and implementation of a control will MOST likely result in an update to:
Which of the following is the BEST way to ensure adequate resources will be allocated to manage identified risk?
Which of the following would BEST help to address the risk associated with malicious outsiders modifying application data?
Which of the following should be the PRIMARY concern when changes to firewall rules do not follow change management requirements?
Which of the following is the PRIMARY purpose for ensuring senior management understands the organization’s risk universe in relation to the IT risk management program?
A large organization recently restructured the IT department and has decided to outsource certain functions. What action should the control owners in the IT department take?
A key risk indicator (KRI) indicates a reduction in the percentage of appropriately patched servers. Which of the following is the risk practitioner ' s BEST course of action?
A service organization is preparing to adopt an IT control framework to comply with the contractual requirements of a new client. Which of the following would be MOST helpful to the risk practitioner?
Which of the following is the MOST effective way to help ensure future risk levels do not exceed the organization ' s risk appetite?
When reviewing a risk response strategy, senior management ' s PRIMARY focus should be placed on the:
The PRIMARY advantage of involving end users in continuity planning is that they:
Which of the following is the PRIMARY concern related to using pseudonymization for the protection of an organization’s processed privacy data?
Which of the following provides the MOST useful information when measuring the progress of risk response action plans?
A risk practitioner identifies an increasing trend of employees copying company information unrelated to their job functions to USB drives. Which of the following elements of the risk register should be updated to reflect this observation?
Which of the following is the BEST course of action to help reduce the probability of an incident recurring?
An organization is measuring the effectiveness of its change management program to reduce the number of unplanned production changes. Which of the following would be the BEST metric to determine if the program is performing as expected?
Which of the following is the GREATEST benefit of incorporating IT risk scenarios into the corporate risk register?
Which of the following would BEST facilitate the implementation of data classification requirements?
Which of the following is the BEST approach for performing a business impact analysis (BIA) of a supply-chain management application?
The PRIMARY objective of the board of directors periodically reviewing the risk profile is to help ensure:
An organization ' s risk management team wants to develop IT risk scenarios to show the impact of collecting and storing credit card information. Which of the following is the MOST comprehensive approach to capture this scenario?
Which of the following is the BEST way to validate privileged access to database accounts?
Which of the following BEST facilitates the identification of appropriate key performance indicators (KPIs) for a risk management program?
Risk mitigation is MOST effective when which of the following is optimized?
To reduce costs, an organization is combining the second and third tines of defense in a new department that reports to a recently appointed C-level executive. Which of the following is the GREATEST concern with this situation?
Which of the following should be the PRIMARY objective of a risk awareness training program?
While evaluating control costs, management discovers that the annual cost exceeds the annual loss expectancy (ALE) of the risk. This indicates the:
Which of the following BEST indicates that additional or improved controls ate needed m the environment?
A risk practitioner is utilizing a risk heat map during a risk assessment. Risk events that are coded with the same color will have a similar:
The BEST key performance indicator (KPI) to measure the effectiveness of a vulnerability remediation program is the number of:
Which of the following would be MOST helpful when communicating roles associated with the IT risk management process?
Which of the following BEST enables an organization to address risk associated with technical complexity?
An organization is planning to implement a Zero Trust model. From a cybersecunty perspective, which of the following is MOST important to ensure successful alignment with the overall inten Zero Trust?
Which of the following is the BEST approach when a risk treatment plan cannot be completed on time?
Which of the following is the MOST important consideration for effectively maintaining a risk register?
Which of the following is the FIRST step when developing a business case to drive the adoption of a risk remediation project by senior management?
A key risk indicator (KRI) for technology operations has been above risk thresholds for the last three reporting periods. What is the BEST way for a risk practitioner to address this concern?
When of the following provides the MOST tenable evidence that a business process control is effective?
Which of the following BEST indicates that an organization has implemented IT performance requirements?
Which of the following would qualify as a key performance indicator (KPI)?
Which of the following is a risk practitioner ' s BEST course of action if a risk assessment identifies a risk that is extremely unlikely but would have a severe impact should it occur?
Which of the following should a risk practitioner recommend FIRST when an increasing trend of risk events and subsequent losses has been identified?
An organization has just implemented changes to close an identified vulnerability that impacted a critical business process. What should be the NEXT course of action?
During a risk assessment, the risk practitioner finds a new risk scenario without controls has been entered into the risk register. Which of the following is the MOST appropriate action?
Which of the following would be the BEST justification to invest in the development of a governance, risk, and compliance (GRC) solution?
Which of the following is the PRIMARY objective of providing an aggregated view of IT risk to business management?
A vendor ' s planned maintenance schedule will cause a critical application to temporarily lose failover capabilities. Of the following, who should approve this proposed schedule?
An organization ' s recovery team is attempting to recover critical data backups following a major flood in its data center. However, key team members do not know exactly what steps should be taken to address this crisis. Which of the following is the MOST likely cause of this situation?
A company has located its computer center on a moderate earthquake fault. Which of the following is the MOST important consideration when establishing a contingency plan and an alternate processing site?
Which of the following cloud service models is MOST appropriate for client organizations that want to maximize their control over management of the data life cycle?
Which of the following is the MOST effective way to help ensure an organization ' s current risk scenarios are relevant?
Which of the following is the MOST important requirement for monitoring key risk indicators (KRls) using log analysis?
An organization maintains independent departmental risk registers that are not automatically aggregated. Which of the following is the GREATEST concern?
The effectiveness of a control has decreased. What is the MOST likely effect on the associated risk?
An organization has decided to implement a new Internet of Things (loT) solution. Which of the following should be done FIRST when addressing security concerns associated with this new technology?
Which of the following is the BEST indicator of the effectiveness of a control?
Which of the following is MOST important to consider when selecting and designing key control indicators (KCIs)?
A PRIMARY advantage of involving business management in evaluating and managing risk is that management:
Which of the following is the MOST important data attribute of key risk indicators (KRIs)?
A risk practitioner learns of an urgent threat intelligence alert to patch a critical vulnerability identified in the organization ' s operating system. Which of the following should the risk practitioner do FIRST?
In a DevOps environment, a container does not pass dynamic application security testing (DAST). How should this situation be categorized?
From a business perspective, which of the following is the MOST important objective of a disaster recovery test?
When determining which control deficiencies are most significant, which of the following would provide the MOST useful information?
Which of the following deficiencies identified during a review of an organization ' s cybersecurity policy should be of MOST concern?
Which of the following is the BEST key performance indicator (KPI) to measure the effectiveness of an antivirus program?
A risk practitioner has been notified that an employee sent an email in error containing customers ' personally identifiable information (Pll). Which of the following is the risk practitioner ' s BEST course of action?
Which of the following is the MOST essential characteristic of a good IT risk scenario?
Which of the following is the BEST approach to mitigate the risk associated with outsourcing network management to an external vendor who will have access to sensitive information assets?
To help ensure all applicable risk scenarios are incorporated into the risk register, it is MOST important to review the:
Which of the following BEST describes the role of the IT risk profile in strategic IT-related decisions?
Which of the following is MOST important for an organization to update following a change in legislation requiring notification to individuals impacted by data breaches?
An organization has recently updated its disaster recovery plan (DRP). Which of the following would be the GREATEST risk if the new plan is not tested?
An organization has restructured its business processes, and the business continuity plan (BCP) needs to be revised accordingly. Which of the following should be identified FIRST?
A risk practitioner recently discovered that personal information from the production environment is required for testing purposes in non-production environments. Which of the following is the BEST recommendation to address this situation?
An organization uses a vendor to destroy hard drives. Which of the following would BEST reduce the risk of data leakage?
An organization has opened a subsidiary in a foreign country. Which of the following would be the BEST way to measure the effectiveness of the subsidiary ' s IT systems controls?
Which of the following is MOST important to include when reporting the effectiveness of risk management to senior management?
Which of the following would BEST mitigate the risk associated with reputational damage from inappropriate use of social media sites by employees?
Which of the following criteria associated with key risk indicators (KRIs) BEST enables effective risk monitoring?
An organization has engaged a third party to provide an Internet gateway encryption service that protects sensitive data uploaded to a cloud service. This is an example of risk:
Which of the following is a risk practitioner ' s MOST important responsibility in managing risk acceptance that exceeds risk tolerance?
Which of the following tasks should be completed prior to creating a disaster recovery plan (DRP)?
The MOST important reason for implementing change control procedures is to ensure:
The PRIMARY reason for tracking the status of risk mitigation plans is to ensure:
An organization has outsourced its backup and recovery procedures to a third-party cloud provider. Which of the following should be the risk practitioner ' s NEXT course of action?
A risk practitioner learns that a risk owner has been accepting gifts from a supplier of IT products. Some of these IT products are used to implement controls and to mitigate risk to acceptable levels. Which of the following should the risk practitioner do FIRST?
Who should be responsible for implementing and maintaining security controls?
Which of the following is a risk practitioner ' s BEST course of action after identifying risk scenarios related to noncompliance with new industry regulations?
When of the following is the BEST key control indicator (KCI) to determine the effectiveness of en intrusion prevention system (IPS)?
A recently purchased IT application does not meet project requirements. Of the following, who is accountable for the potential impact?
A risk assessment has identified increased losses associated with an IT risk scenario. It is MOST important for the risk practitioner to:
when developing IT risk scenarios associated with a new line of business, which of the following would be MOST helpful to review?
Which of the following is the MOST effective way to validate organizational awareness of cybersecurity risk?
What is the BEST recommendation to reduce the risk associated with potential system compromise when a vendor stops releasing security patches and updates for a business-critical legacy system?
Which of the following BEST supports ethical IT risk management practices?
Which of the following is the GREATEST concern when an organization uses a managed security service provider as a firewall administrator?
Which of the following is the MOST important consideration for prioritizing risk treatment plans when faced with budget limitations?
Recent changes in an organization ' s business strategy requires an application to increase its recovery point objective (RPO). Which of the following MUST be updated?
Which of the following BEST enables a risk practitioner to enhance understanding of risk among stakeholders?
Which of the following is the MOST comprehensive resource for prioritizing the implementation of information systems controls?
When reporting on the performance of an organization ' s control environment including which of the following would BEST inform stakeholders risk decision-making?
Which of the following would be the BEST way to help ensure the effectiveness of a data loss prevention (DLP) control that has been implemented to prevent the loss of credit card data?
Which of the following approaches will BEST help to ensure the effectiveness of risk awareness training?
When determining the accuracy of a key risk indicator (KRI), it is MOST important that the indicator:
Which of the following is MOST important for a risk practitioner to consider when evaluating plans for changes to IT services?
Which of the following BEST supports the communication of risk assessment results to stakeholders?
Which of the following would be of GREATEST concern regarding an organization ' s asset management?
A risk practitioner discovers that an IT operations team manager bypassed web filtering controls by using a mobile device, in violation of the network security policy. Which of the following should the risk practitioner do FIRST?
An organization does not have a defined process to revoke IT access of staff members who have changed roles within the organization. Which of the following is the GREATEST concern associated with this deficiency?
A risk practitioner wants to identify potential risk events that affect the continuity of a critical business process. Which of the following should the risk practitioner do FIRST?
Which of the following provides the BEST evidence that a selected risk treatment plan is effective?
Which of the following is the BEST measure of the effectiveness of an employee deprovisioning process?
Which of the following is the PRIMARY reason to compare the business impact analysis (BIA) against the organization ' s business continuity plan (BCP)?
Which of We following is the MOST effective control to address the risk associated with compromising data privacy within the cloud?
Which of the following would provide the MOST helpful input to develop risk scenarios associated with hosting an organization ' s key IT applications in a cloud environment?
Which of the following is the PRIMARY reason to obtain independent reviews of risk assessment and response mechanisms?
To drive effective risk management, it is MOST important that an organization ' s policy framework is:
Real-time monitoring of security cameras implemented within a retail store is an example of which type of control?
An organization is unable to implement a multi-factor authentication requirement until the next fiscal year due to budget constraints. Consequently, a policy exception must be submitted. Which of the following is MOST important to include in the analysis of the exception?
Which of the following is the PRIMARY risk management responsibility of the third line of defense?
A risk assessment has identified that departments have installed their own WiFi access points on the enterprise network. Which of the following would be MOST important to include in a report to senior management?
Which of the following BEST indicates the condition of a risk management program?
Reviewing historical risk events is MOST useful for which of the following processes within the risk management life cycle?
Which of the following should be the PRIMARY focus of an IT risk awareness program?
Which of the following should be the PRIMARY driver for an organization on a multi-year cloud implementation to publish a cloud security policy?
Which of the following is MOST important to consider when selecting risk indicators (KRIs)? The ability to:
Which of the following BEST enables a proactive approach to minimizing the potential impact of unauthorized data disclosure?
A hospital recently implemented a new technology to allow virtual patient appointments. Which of the following should be the risk practitioner ' s FIRST course of action?
Which of the following BEST enables risk-based decision making in support of a business continuity plan (BCP)?
Which of the following is the MOST important benefit of implementing a data classification program?
A risk practitioner is collaborating with key stakeholders to prioritize a large number of IT risk scenarios. Which scenarios should receive the PRIMARY focus?
Which of the following observations would be the GREATEST concern to a risk practitioner evaluating an organization ' s risk management practices?
Which of the following is the MOST critical element to maximize the potential for a successful security implementation?
Which of the following would cause the GREATEST concern for a risk practitioner reviewing the IT risk scenarios recorded in an organization’s IT risk register?
An organization practices the principle of least privilege. To ensure access remains appropriate, application owners should be required to review user access rights on a regular basis by obtaining:
Which of the following is MOST important to address for an organization looking to improve its IT asset management processes?
Which of the following will BEST quantify the risk associated with malicious users in an organization?
The risk associated with an asset before controls are applied can be expressed as:
Which of these documents is MOST important to request from a cloud service
provider during a vendor risk assessment?
An IT department has organized training sessions to improve user awareness of organizational information security policies. Which of the following is the BEST key performance indicator (KPI) to reflect effectiveness of the training?
Which of the following is the BEST approach for an organization in a heavily regulated industry to comprehensively test application functionality?
Which of the following IT key risk indicators (KRIs) provides management with the BEST feedback on IT capacity?
Which of the following should be the FIRST course of action if the risk associated with a new technology is found to be increasing?
The GREATEST benefit of including low-probability, high-impact events in a risk assessment is the ability to:
The PRIMARY reason for communicating risk assessment results to data owners is to enable the:
An organization has granted a vendor access to its data in order to analyze customer behavior. Which of the following would be the MOST effective control to mitigate the risk of customer data leakage?
An organization learns of a new ransomware attack affecting organizations worldwide. Which of the following should be done FIRST to reduce the likelihood of infection from the attack?
Which of the following is the MOST effective way to determine if a risk factor exceeds risk tolerance?
Which of the following should a risk practitioner do NEXT after learning that Internet of Things (IoT) devices installed in the production environment lack appropriate security controls for sensitive data?
Which of the following is the BEST way to determine the value of information assets for risk management purposes?
What is the MOST important consideration when selecting key performance indicators (KPIs) for control monitoring?
Which of the following is the BEST course of action to reduce risk impact?
Which of the following methods is the BEST way to measure the effectiveness of automated information security controls prior to going live?
Which of the following is the MOST important reason to report on changes or trends related to an organization ' s IT risk profile?
Which of the following is the MOST important topic to cover in a risk awareness training program for all staff?
Which of the following is the MOST effective way to validate organizational awareness of cybersecurity risk?
Which of the following is the BEST reason to use qualitative measures to express residual risk levels related to emerging threats?
Which of the following should be considered FIRST when creating a comprehensive IT risk register?
Which of the following should be a risk practitioner ' s NEXT step upon learning the impact of an organization ' s noncompliance with a specific legal regulation?
Which of the following is the MOST effective control to maintain the integrity of system configuration files?
A risk practitioner implemented a process to notify management of emergency changes that may not be approved. Which of the following is the BEST way to provide this information to management?
Which of the following trends would cause the GREATEST concern regarding the effectiveness of an organization ' s user access control processes? An increase in the:
From an IT risk perspective, which of the following has the GREATEST impact on organizational strategy?
An organization striving to be on the leading edge in regard to risk monitoring would MOST likely implement:
An organization has used generic risk scenarios to populate its risk register. Which of the following presents the GREATEST challenge to assigning of the associated risk entries?
Which of the following is the BEST metric to measure employee adherence to organizational security policies?
Which of the following is the FIRST step in managing the security risk associated with wearable technology in the workplace?
Which of the following is the MOST important consideration when developing risk strategies?
An organization has identified the need to implement an asset tiering model to establish the appropriate level of impact. Which of the following is the MOST effective risk assessment methodology for a risk practitioner to use for this initiative?
Which of the following is the MOST important information to cover in a business continuity awareness training program for all employees of the organization?
A financial institution has identified high risk of fraud in several business applications. Which of the following controls will BEST help reduce the risk of fraudulent internal transactions?
A recent audit identified high-risk issues in a business unit though a previous control self-assessment (CSA) had good results. Which of the following is the MOST likely reason for the difference?
Which of the following controls BEST enables an organization to ensure a complete and accurate IT asset inventory?
What is the PRIMARY reason to periodically review key performance indicators (KPIs)?
Which of the following is the GREATEST benefit of involving business owners in risk scenario development?
An organization plans to migrate sensitive information to a public cloud infrastructure. Which of the following is the GREATEST security risk in this scenario?
When collecting information to identify IT-related risk, a risk practitioner should FIRST focus on IT:
After undertaking a risk assessment of a production system, the MOST appropriate action is fcr the risk manager to
An organization delegates its data processing to the internal IT team to manage information through its applications. Which of the following is the role of the internal IT team in this situation?
The operational risk associated with attacks on a web application should be owned by the individual in charge of:
A risk practitioner is organizing risk awareness training for senior management. Which of the following is the MOST important topic to cover in the training session?
Implementing which of the following controls would BEST reduce the impact of a vulnerability that has been exploited?
Which of the following would be MOST helpful in assessing the risk associated with data loss due to human vulnerabilities?
One of an organization ' s key IT systems cannot be patched because the patches interfere with critical business application functionalities. Which of the following would be the risk practitioner ' s BEST recommendation?
A risk practitioner shares the results of a vulnerability assessment for a critical business application with the business manager. Which of the following is the NEXT step?
Which of the following risk management practices BEST facilitates the incorporation of IT risk scenarios into the enterprise-wide risk register?
Which of the following is MOST important to consider when determining risk appetite?
Which of the following shortcomings of perimeter security does Zero Trust aim to resolve?
Which of the following is the BEST method for determining an enterprise ' s current appetite for risk?
Senior management is deciding whether to share confidential data with the organization ' s business partners. The BEST course of action for a risk practitioner would be to submit a report to senior management containing the:
Which of the following is the MOST important reason for a risk practitioner to identify stakeholders for each IT risk scenario?
Which of the following is the BEST way to ensure ongoing control effectiveness?
Which of the following activities is a responsibility of the second line of defense?
The PRIMARY reason for establishing various Threshold levels for a set of key risk indicators (KRIs) is to:
An organization has been notified that a disgruntled, terminated IT administrator has tried to break into the corporate network. Which of the following discoveries should be of GREATEST concern to the organization?
Which of me following is MOST helpful to mitigate the risk associated with an application under development not meeting business objectives?
An organization recently implemented a cybersecurity awareness program that includes phishing simul-ation exercises for all employees. What type of control is being utilized?
Which of the following should be a risk practitioner ' s NEXT action after identifying a high probability of data loss in a system?
Which of the following BEST enables an organization to determine whether risk management is aligned with its goals and objectives?
Which of the following is the MOST appropriate role to determine risk appetite and tolerance?
Which of the following is MOST important to promoting a risk-aware culture?
Which of the following scenarios is MOST important to communicate to senior management?
The following is the snapshot of a recently approved IT risk register maintained by an organization ' s information security department.
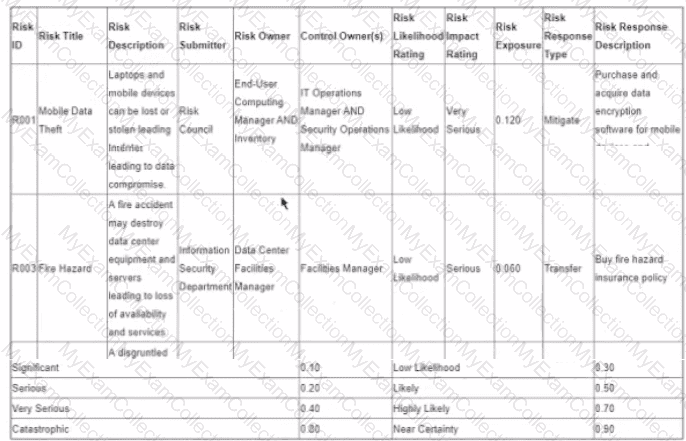
After implementing countermeasures listed in ‘’Risk Response Descriptions’’ for each of the Risk IDs, which of the following component of the register MUST change?
During implementation of an intrusion detection system (IDS) to monitor network traffic, a high number of alerts is reported. The risk practitioner should recommend to:
Which of the following would provide the MOST comprehensive information for communicating current levels of IT-related risk to executive management?
Which of the following would be of MOST concern to a risk practitioner reviewing risk action plans for documented IT risk scenarios?
Which of the following BEST supports the management of identified risk scenarios?
When reporting to senior management on changes in trends related to IT risk, which of the following is MOST important?
Which of the following is the PRIMARY reason for a risk practitioner to examine a post-implementation review report for a control automation tool?
To enable effective risk governance, it is MOST important for senior management to:
An assessment of information security controls has identified ineffective controls. Which of the following should be the risk practitioner ' s FIRST course of action?
Which of the following should a risk practitioner do NEXT after learning that Internet of Things (loT) devices installed in the production environment lack appropriate security controls for
sensitive data?
A global organization is planning to collect customer behavior data through social media advertising. Which of the following is the MOST important business risk to be considered?
Which of the following would offer the MOST insight with regard to an organization ' s risk culture?
Which of the following should be management ' s PRIMARY focus when key risk indicators (KRIs) begin to rapidly approach defined thresholds?
Which of the following is the MOST important reason to validate that risk responses have been executed as outlined in the risk response plan ' '
A recent internal risk review reveals the majority of core IT application recovery time objectives (RTOs) have exceeded the maximum time defined by the business application owners. Which of the following is MOST likely to change as a result?
Which of the following key risk indicators (KRIs) provides the BEST insight into the risk associated with IT systems being unable to meet the required availability service level in the future?
Which of the following is MOST effective in continuous risk management process improvement?
Which of the following is the GREATEST concern associated with redundant data in an organization ' s inventory system?
Which of the following is the MOST important consideration when sharing risk management updates with executive management?
Which of the following should be a risk practitioner’s MOST important consideration when developing IT risk scenarios?
Which of the following is the BEST recommendation to senior management when the results of a risk and control assessment indicate a risk scenario can only be partially mitigated?
Which of the following is MOST important to include in a Software as a Service (SaaS) vendor agreement?
An organization outsources the processing of us payroll data A risk practitioner identifies a control weakness at the third party trial exposes the payroll data. Who should own this risk?
A vendor ' s planned maintenance schedule will cause a critical application to temporarily lose failover capabilities. Of the following, who should approve this proposed schedule?
Which strategy employed by risk management would BEST help to prevent internal fraud?
A risk practitioner has been notified of a social engineering attack using artificial intelligence (Al) technology to impersonate senior management personnel. Which of the following would BEST mitigate the impact of such attacks?
Which of the following would be MOST helpful to a risk practitioner when preparing a summary of current IT risk for senior management review?
Which of the following is the FIRST step when conducting a business impact analysis (BIA)?
An organization that has been the subject of multiple social engineering attacks is developing a risk awareness program. The PRIMARY goal of this program should be to:
To implement the MOST effective monitoring of key risk indicators (KRIs), which of the following needs to be in place?
A risk practitioner ' s BEST guidance to help an organization develop relevant risk scenarios is to ensure the scenarios are:
Which of the following resources is MOST helpful to a risk practitioner when updating the likelihood rating in the risk register?
Which of the following is the PRIMARY reason to perform ongoing risk assessments?
Which of the following is MOST important for the organization to consider before implementing a new in-house developed artificial intelligence (Al) solution?
Which of the following provides the BEST assurance of the effectiveness of vendor security controls?
Which of the following provides the BEST protection for Internet of Things (loT) devices that are accessed within an organization?
Which organizational role should be accountable for ensuring information assets are appropriately classified?
Which of the following is MOST likely to introduce risk for financial institutions that use blockchain?
What should a risk practitioner do FIRST when an assessment reveals a control is not operating as intended?
Due to a change in business processes, an identified risk scenario no longer requires mitigation. Which of the following is the MOST important reason the risk should remain in the risk register?
Which of the following facilitates a completely independent review of test results for evaluating control effectiveness?
In order to determining a risk is under-controlled the risk practitioner will need to
A bank recently incorporated Blockchain technology with the potential to impact known risk within the organization. Which of the following is the risk practitioner’s BEST course of action?
An organization retains footage from its data center security camera for 30 days when the policy requires 90-day retention The business owner challenges whether the situation is worth remediating Which of the following is the risk manager s BEST response '
Which of the following would MOST likely require a risk practitioner to update the risk register?
Which of the following is the BEST source for identifying key control indicators (KCIs)?
An organization recently invested in an identity and access management (IAM) solution to manage user activities across corporate mobile devices. Which of the following is MOST important to update in the risk register?
Which of the following is the MOST important key risk indicator (KRI) to protect personal information on corporate mobile endpoints?
A risk practitioner notices that a particular key risk indicator (KRI) has remained below its established trigger point for an extended period of time. Which of the following should be done FIRST?
From a governance perspective, which of the following is MOST important to ensure when risk management policies are being updated to facilitate the pursuit of new opportunities?
A risk practitioner has established that a particular control is working as desired, but the annual cost of maintenance has increased and now exceeds the expected annual loss exposure. The result is that the control is:
Which of the following is the BEST approach when a risk practitioner has been asked by a business unit manager to exclude an in-scope system from a risk assessment?
Which of the following should be the PRIMARY consideration for a startup organization that has decided to adopt externally-sourced security policies?
The MOST effective way to increase the likelihood that risk responses will be implemented is to:
Which of the following activities is MOST likely to be assigned to the second line in the three lines model?
As part of an overall IT risk management plan, an IT risk register BEST helps management:
Which of the following is the BEST indication that key risk indicators (KRls) should be revised?
Which of the following BEST indicates the effectiveness of anti-malware software?
Which of the following is the BEST risk management approach for the strategic IT planning process?
Which of the following helps ensure compliance with a nonrepudiation policy requirement for electronic transactions?
Which of the following is the BEST key performance indicator (KPI) to measure how effectively risk management practices are embedded in the project management office (PMO)?
An organization is considering outsourcing user administration controls tor a critical system. The potential vendor has offered to perform quarterly sett-audits of its controls instead of having annual independent audits. Which of the following should be of GREATEST concern to me risk practitioner?
Which of the following is the GREATEST concern associated with insufficient focus on addressing blockchain interoperability in the SDLC?
The head of a business operations department asks to review the entire IT risk register. Which of the following would be the risk manager s BEST approach to this request before sharing the register?
To define the risk management strategy which of the following MUST be set by the board of directors?
Which of the following provides the BEST evidence of the effectiveness of an organization ' s account provisioning process?
Which of the following is the PRIMARY responsibility of the first line of defense related to computer-enabled fraud?
Which of the following is MOST helpful to understand the consequences of an IT risk event?
Which of the following is the GREATEST benefit of having a mature enterprise architecture (EA) in place?
Which of the following presents the GREATEST challenge to managing an organization ' s end-user devices?
Which of the following is MOST important for a risk practitioner to consider when determining the control requirements for data privacy arising from emerging technologies?
A global organization is considering the acquisition of a competitor. Senior management has requested a review of the overall risk profile from the targeted organization. Which of the following components of this review would provide the MOST useful information?
Which of the following is the BEST metric to demonstrate the effectiveness of an organization’s software testing program?
Which of the following is the MOST important reason to revisit a previously accepted risk?
An IT risk practitioner has been tasked to engage key stakeholders to assess risk for key IT risk scenarios. Which of the following is the PRIMARY benefit of this activity?
What are the MOST important criteria to consider when developing a data classification scheme to facilitate risk assessment and the prioritization of risk mitigation activities?
An unauthorized individual has socially engineered entry into an organization ' s secured physical premises. Which of the following is the BEST way to prevent future occurrences?
Print jobs containing confidential information are sent to a shared network printer located in a secure room. Which of the following is the BEST control to prevent the inappropriate disclosure of confidential information?
Which of the following is MOST important to add to the risk register for a remediated risk scenario?
Which of the following is MOST important to the effectiveness of key performance indicators (KPIs)?
In addition to the risk exposure, which of the following is MOST important for senior management to understand prior to approving the use of artificial intelligence (Al) solutions?
While conducting an organization-wide risk assessment, it is noted that many of the information security policies have not changed in the past three years. The BEST course of action is to:
Which of the following should be the HIGHEST priority when developing a risk response?
Which of the following should be the PRIMARY recipient of reports showing the
progress of a current IT risk mitigation project?
A robotic process automation (RPA) project has implemented new robots to enhance the efficiency of a sales business process. Which of the following provides the BEST evidence that the new controls have been implemented successfully?
Which of the following activities should only be performed by the third line of defense?
When developing a new risk register, a risk practitioner should focus on which of the following risk management activities?
A risk practitioner has identified that the organization ' s secondary data center does not provide redundancy for a critical application. Who should have the authority to accept the associated risk?
Which of the following should be the PRIMARY consideration when prioritizing limited resources needed to implement overdue corrective actions arising from a recent internal audit?
Once a risk owner has decided to implement a control to mitigate risk, it is MOST important to develop:
Which of the following should be the FIRST consideration when establishing a new risk governance program?
To effectively address ethical risk within an organization, who MUST ensure the ethics policy is enforced and equally applied to all levels of authority ' ?
Which of the following is the MOST important consideration when communicating the risk associated with technology end-of-life to business owners?
When an organization is having new software implemented under contract, which of the following is key to controlling escalating costs?
An organization is developing a risk awareness program for contractors and consultants. Which of the following is MOST important for the organization to keep confidential?
Sensitive data has been lost after an employee inadvertently removed a file from the premises, in violation of organizational policy. Which of the following controls MOST likely failed?
Which of the following stakeholders are typically included as part of a line of defense within the three lines of defense model?
Which of the following is MOST important to ensure when reviewing an organization ' s risk register?
Which of the following is the BEST indicator of the effectiveness of IT risk management processes?
When reviewing a business continuity plan (BCP). which of the following would be the MOST significant deficiency?
After conducting a risk assessment for regulatory compliance, an organization has identified only one possible mitigating control. The cost of the control has been determined to be higher than the penalty of noncompliance. Which of the following would be the risk practitioner ' s BEST recommendation?
Which of the following presents the GREATEST security risk associated with Internet of Things (IoT) technology?
An organization is implementing robotic process automation (RPA) to streamline business processes. Given that implementation of this technology is expected to impact existing controls, which of the following is the risk practitioner ' s BEST course of action?
In order to efficiently execute a risk response action plan, it is MOST important for the emergency response team members to understand:
Which of the following will BEST ensure that controls adequately support business goals and objectives?
An IT department has provided a shared drive for personnel to store information to which all employees have access. Which of the following parties is accountable for the risk of potential loss of confidential information?
Which of the following is the BEST way to promote adherence to the risk tolerance level set by management?
After the announcement of a new IT regulatory requirement, it is MOST important for a risk practitioner to;
An organization has established workflows in its service desk to support employee reports of security-related concerns. Which of the following is the MOST efficient approach to analyze these concerns?
In response to the threat of ransomware, an organization has implemented cybersecurity awareness activities. The risk practitioner ' s BEST recommendation to further reduce the impact of ransomware attacks would be to implement:
Which of the following is the BEST response when a potential IT control deficiency has been identified?
The risk to an organization ' s reputation due to a recent cybersecurity breach is PRIMARILY considered to be:
The MOST important consideration when selecting a control to mitigate an identified risk is whether:
An IT risk practitioner has been asked to regularly report on the overall status and effectiveness of the IT risk management program. Which of the following is MOST useful for this purpose?
A risk practitioner notices a trend of noncompliance with an IT-related control. Which of the following would BEST assist in making a recommendation to management?
An organization has been made aware of a newly discovered critical vulnerability in a regulatory reporting system. Which of the following is the risk practitioner ' s BEST course of action?
A recent regulatory requirement has the potential to affect an organization’s use of a third party to supply outsourced business services. Which of the following is the BEST course of action?
A risk practitioner is asked to present the results of the most recent technology risk assessment to executive management in a concise manner. Which of the following is MOST important to include in the presentation?
Which of the following is the GREATEST concern when using a generic set of IT risk scenarios for risk analysis?
A business unit is updating a risk register with assessment results for a key project. Which of the following is MOST important to capture in the register?
Which of the following provides the MOST helpful reference point when communicating the results of a risk assessment to stakeholders?
Which of the following is the FIRST step when conducting a business impact analysis (BIA)?
Which of the following is MOST useful when performing a quantitative risk assessment?
A risk practitioner finds that data has been misclassified. Which of the following is the GREATEST concern?
Which of the following would provide executive management with the BEST information to make risk decisions as a result of a risk assessment?
A risk practitioner recently discovered that sensitive data from the production environment is required for testing purposes in non-production environments. Which of the following i the BEST recommendation to address this situation?
Which of the following management actions will MOST likely change the likelihood rating of a risk scenario related to remote network access?
Which of the following should an organization perform to forecast the effects of a disaster?
When reporting risk assessment results to senior management, which of the following is MOST important to include to enable risk-based decision making?
What should a risk practitioner do FIRST upon learning a risk treatment owner has implemented a different control than what was specified in the IT risk action plan?
Which of the following BEST helps to mitigate risk associated with users inputting incorrect data into a system?
Which of the following should be an element of the risk appetite of an organization?
Which of the following is the BEST indication that an organization ' s risk management program has not reached the desired maturity level?
Which of the following is PRIMARILY a risk management responsibly of the first line of defense?
Which of the following would be MOST useful to senior management when determining an appropriate risk response?
The MOST essential content to include in an IT risk awareness program is how to:
Which of the following is the BEST metric to demonstrate the effectiveness of an organization ' s patch management process?
Which of the following is the MAIN benefit of involving stakeholders in the selection of key risk indicators (KRIs)?
Which of the following BEST indicates the effective implementation of a risk treatment plan?
Which of the following would BEST facilitate the implementation of data classification requirements?
An organization has introduced risk ownership to establish clear accountability for each process. To ensure effective risk ownership, it is MOST important that:
Who should be accountable for monitoring the control environment to ensure controls are effective?
Prior to selecting key performance indicators (KPIs), itis MOST important to ensure:
It was discovered that a service provider ' s administrator was accessing sensitive information without the approval of the customer in an Infrastructure as a Service (laaS) model. Which of the following would BEST protect against a future recurrence?
Which of the following is the PRIMARY role of the first line of defense with respect to information security policies?
Which of the following BEST reduces the risk associated with the theft of a laptop containing sensitive information?
Which of the following would present the GREATEST challenge when assigning accountability for control ownership?
An organization is participating in an industry benchmarking study that involves providing customer transaction records for analysis Which of the following is the MOST important control to ensure the privacy of customer information?
Which of the following is the MOST important element of a successful risk awareness training program?
Which of the following is the GREATEST benefit when enterprise risk management (ERM) provides oversight of IT risk management?
Which of the following potential scenarios associated with the implementation of a new database technology presents the GREATEST risk to an organization?
Which of the following would provide the BEST guidance when selecting an appropriate risk treatment plan?
Which of the following BEST indicates whether security awareness training is effective?
An organization recently experienced a cyber attack that resulted in the loss of confidential customer data. Which of the following is the risk practitioner ' s BEST recommendation after recovery steps have been completed?
What are the MOST essential attributes of an effective Key control indicator (KCI)?
Which of the following is the BEST indication of an enhanced risk-aware culture?
As part of an aggressive new marketing strategy, an organization has decided to implement an emerging technology in a critical business system. Which of the following is the BEST course of action to address the risk associated with this new technology?
Which of the following BEST indicates that an organization ' s risk management processes are mature?
Which of the following would BEST help to ensure that suspicious network activity is identified?
Which of the following BEST facilities the alignment of IT risk management with enterprise risk management (ERM)?
When developing risk scenario using a list of generic scenarios based on industry best practices, it is MOST imported to:
Which of the following is MOST helpful to ensure effective security controls for a cloud service provider?
Which of the following should management consider when selecting a risk mitigation option?
What is the PRIMARY role of the application owner when changes are being introduced into an existing environment?
An organization has outsourced its customer management database to an external service provider. Of the following, who should be accountable for ensuring customer data privacy?
Which of the following is the BEST key performance indicator (KPI) to measure the effectiveness of a disaster recovery test of critical business processes?
An information system for a key business operation is being moved from an in-house application to a Software as a Service (SaaS) vendor. Which of the following will have the GREATEST impact on the ability to monitor risk?
Which of the following is BEST measured by key control indicators (KCIs)?
Which of the following should be the FIRST consideration when a business unit wants to use personal information for a purpose other than for which it was originally collected?
Which of the following would be MOST effective in monitoring changes in an organization ' s IT risk environment?
Key control indicators (KCls) help to assess the effectiveness of the internal control environment PRIMARILY by:
A cote data center went offline abruptly for several hours affecting many transactions across multiple locations. Which of the to " owing would provide the MOST useful information to determine mitigating controls?
Which of the following risk register updates is MOST important for senior management to review?
Because of a potential data breach, an organization has decided to temporarily shut down its online sales order system until sufficient controls can be implemented. Which risk treatment has been selected?
Which of the following is the MOST important objective of regularly presenting the project risk register to the project steering committee?
An audit reveals that there are changes in the environment that are not reflected in the risk profile. Which of the following is the BEST course of action?
A highly regulated organization acquired a medical technology startup company that processes sensitive personal information with weak data protection controls. Which of the following is the BEST way for the acquiring company to reduce its risk while still enabling the flexibility needed by the startup company?
A business impact analysis (BIA) has documented the duration of maximum allowable outage for each of an organization ' s applications. Which of the following MUST be aligned with the maximum allowable outage?
Which of the following BEST measures the efficiency of an incident response process?
Within the three lines of defense model, the responsibility for managing risk and controls resides with:
A recent risk workshop has identified risk owners and responses for newly identified risk scenarios. Which of the following should be the risk practitioner s NEXT step? r
Which of the following is the PRIMARY reason to use administrative controls in conjunction with technical controls?
Which of the following BEST enables senior management to make risk treatment decisions in line with the organization ' s risk appetite?
The risk associated with inadvertent disclosure of database records from a public cloud service provider (CSP) would MOST effectively be reduced by:
IT stakeholders have asked a risk practitioner for IT risk profile reports associated with specific departments to allocate resources for risk mitigation. The BEST way to address this request would be to use:
Concerned about system load capabilities during the month-end close process, management requires monitoring of the average time to complete tasks and monthly reporting of the findings. What type of measure has been established?
Which of the following is a risk practitioner ' s MOST appropriate course of action upon learning that an organization is not compliant with its patch management policy?
Which of the following is the BEST indication of an effective risk management program?
Which of the following is the MOST important data source for monitoring key risk indicators (KRIs)?
During a routine check, a system administrator identifies unusual activity indicating an intruder within a firewall. Which of the following controls has MOST likely been compromised?
Which of the following should be the MAIN consideration when validating an organization ' s risk appetite?
An organization has contracted with a cloud service provider to support the deployment of a new product. Of the following, who should own the associated risk?
Which of the following is the GREATEST concern when using artificial intelligence (AI) language models?
An organization is increasingly concerned about loss of sensitive data and asks the risk practitioner to assess the current risk level. Which of the following should the risk practitioner do FIRST?
Which of the following will BEST help to ensure that information system controls are effective?
Which of the following would prompt changes in key risk indicator {KRI) thresholds?
The PRIMARY benefit associated with key risk indicators (KRls) is that they:
Which of the following should be the PRIMARY basis for establishing a priority sequence when restoring business processes after a disruption?
Which of the following is the GREATEST concern associated with the use of artificial intelligence (AI) language models?
Which of the following is the BEST key performance indicator (KPI) for a server patch management process?
A public online information security training course is available to an organization ' s staff. The online course contains free-form discussion fields. Which of the following should be of MOST concern to the organization ' s risk practitioner?
An organization is outsourcing a key database to be hosted by an external service provider. Who is BEST suited to assess the impact of potential data loss?
When developing a risk awareness training program, which of the following is the BEST way to promote a risk-aware culture?
Who is PRIMARILY accountable for identifying risk on a daily basis and ensuring adherence to the organization ' s policies?
Which of the following is a risk practitioner ' s BEST recommendation regarding disaster recovery management (DRM) for Software as a Service (SaaS) providers?
Which of the following is MOST critical to the design of relevant risk scenarios?
After entering a large number of low-risk scenarios into the risk register, it is MOST important for the risk practitioner to:
Which of the following is a risk practitioner ' s BEST course of action upon learning that a control under internal review may no longer be necessary?
Following a significant change to a business process, a risk practitioner believes the associated risk has been reduced. The risk practitioner should advise the risk owner to FIRST
A zero-day vulnerability has been discovered in a globally used brand of hardware server that allows hackers to gain
access to affected IT systems. Which of the following is MOST likely to change as a result of this situation?
When an organization ' s business continuity plan (BCP) states that it cannot afford to lose more than three hours of a critical application ' s data, the three hours is considered the application’s:
Which of the following is the MOST effective way 10 identify an application backdoor prior to implementation ' ?
Which of the following should be the PRIMARY focus of a risk owner once a decision is made to mitigate a risk?
When outsourcing a business process to a cloud service provider, it is MOST important to understand that:
Which of the following provides the MOST reliable evidence to support conclusions after completing an information systems controls assessment?
A data center has recently been migrated to a jurisdiction where heavy fines will be imposed should leakage of customer personal data occur. Assuming no other changes to the operating environment, which factor should be updated to reflect this situation as an input to scenario development for this particular risk event?