Which Network Prevent action has taken place when a Network incident snapshot indicates the message has been “Modified�
Which server target uses the “Automated Incident Remediation Tracking†feature in Symantec DLP?
A DLP administrator created a new agent configuration for an Endpoint server. However, the endpoint agents fail to receive the new configuration.
What is one possible reason that the agent fails to receive the new configuration?
Which two (2) detection technology options run ONLY on detection servers and NOT on endpoint agents? (Choose two.)
Which tool must a DLP administrator run to certify the database prior to upgrading DLP?
What is the correct order for data in motion when a customer has integrated their CloudSOC and DLP solutions?
Which two detection technology options run on the DLP agent? (Choose two.)
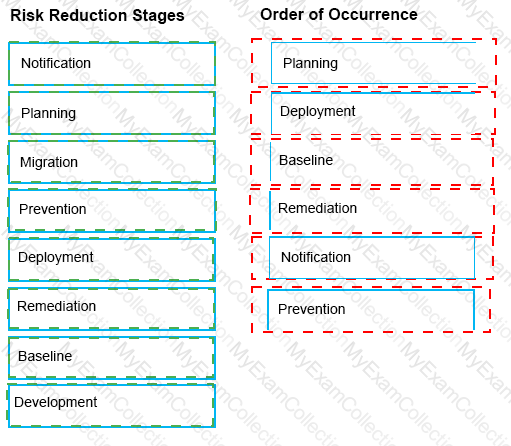
The Symantec Data Loss risk reduction approach has six stages.
Drag and drop the six correct risk reduction stages in the proper order of Occurrence column.
How should a DLP administrator change a policy so that it retains the original file when an endpoint incident has detected a “cope to USB device†operation?
Which two (2) DLP products support Optical Character Recognition (OCR)? (Choose two.)
A customer needs to integrate information form DLP incidents into external Governance, Risk, and Compliance dashboards.
Which feature should a third-party component integrate with to provide dynamic reporting, create custom incident remediation processes, or support business processes?
Which option correctly describes the two-tier installation type for Symantec DLP?
Under the “System Overview†in the Enforce management console, the status of a Network Monitor detection server is shown as “Running Selected.†The Network Monitor server’s event logs indicate that the packet capture and filereader processes are crashing.
What is a possible cause for the Network Monitor server being in this state?
What is the default fallback option for the Endpoint Prevent Encrypt response rule?
A DLP administrator is checking the System Overview in the Enforce management console, and all of the detection servers are showing as “unknownâ€. The Vontu services are up and running on the detection servers. Thousands of .IDC files are building up in the Incidents directory on the detection servers. There is good network connectivity between the detection servers and the Enforce server when testing with the telnet command.
How should the administrator bring the detection servers to a running state in the Enforce management console?
Which two (2) actions are available for a “Network Prevent: Remove HTTP/HTTPS content†response rule when the content is unable to be removed? (Choose two.)
When Symantec DLP is integrated with Microsoft Purview Information Protection (MPIP, also previously known as MIP), to which content types can the Mac DLP Agent apply MPIP labels (classification tags)?
Which option correctly describes the two-tier installation type for Symantec DLP?
A company needs to implement Data Owner Exception so that incidents when employees send or receive their own personal information.
What detection method should the company use?
What should an incident responder select in the Enforce management console to remediate multiple incidents simultaneously?
Which two detection servers are available as virtual appliances? (Choose two.)
What detection server is used for Network Discover, Network Protect, and Cloud Storage?
Which detection server is available from Symantec as a hardware appliance?
Which two (2) detection technology options run on the DLP agent? (Choose two.)
Which statement accurately describes where Optical Character Recognition (OCR) On-Premises DLP Core components must be installed?